How to secure your Yahoo Mail account properly
Yahoo released a statement yesterday in which it notified users of its mail service Yahoo Mail that it noticed a coordinated "effort to gain unauthorized access to Yahoo Mail accounts".
According to Yahoo's preliminary analysis, it does not appear as if the data was dumped from Yahoo servers directly. The company assumes that the data has been collected from third-party databases instead.
The attack used a list of username and password combinations to try and gain access to Yahoo Mail accounts.
It appears that the information the attackers were after were names and email addresses of the most recent sent emails from affected accounts.
Yahoo has reset email passwords of affected accounts as a consequence, and is using sign-in verification to enable affected users to secure their accounts.
How to secure a Yahoo Mail account
The password is the most important part of the equation. If it is weak, it can be easily guessed or brute-forced. Weak in this case means that it has a low character count, may include a dictionary word or names, and does not use general password security suggestions:
- A password should have a lot of characters. My suggestion would be to pick at least 16, but the more the better.
- It should contain a mixture of upper- and lower case letters, numbers and special characters.
- It should not contain dictionary words or names.
- It should not be a sequence that you find on your keyboard, such as qwerty or 123456
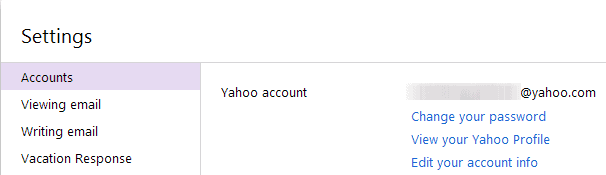
You can change your Yahoo Mail password under Settings > Accounts > change password. To get to the settings, click on the menu button next to your username in the top right corner of the Yahoo Mail website.
Once you have set a secure password, you may want to explore additional security options that are provided by Yahoo.
You can for instance set up sign-in verification for your account on this page.
Sign-in verification adds a second layer of protection to your account. Even if a hacker or thief manages to get your account password, access is only granted if the second-sign in verification code is also known to them.
Note: This works only if you link a mobile device capable of receiving SMS to your account.
Sign-in verification kicks in whenever Yahoo recognizes a login attempt from a device or location that is unknown to the service (meaning that it was not used before).
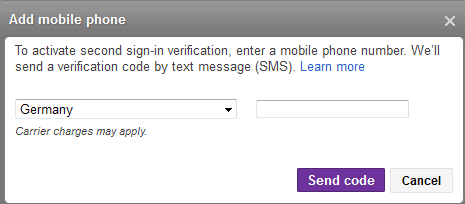
To set up sign-in verification, do the following:
- Once you are on the page linked above, click on "Set up your second sign-in verification" under Sign-in and Security".
- You will be asked for the account password again.
- Click on the get started link here.
- If you have not added a mobile to your account yet, you are asked to do so. Select the country you reside in and enter your mobile phone number.
- You will receive a verification SMS.
- Once done, you have two options: Use either security questions or a supported mobile number for verification, or use only your mobile number for verification.
Additional information about setting up Second sign-in verification on Yahoo are available on Yahoo's help pages.
Note: If you have set up the feature, you may need to create so called app passwords for select applications and devices, as not all may support sign-in verification.
Other Tips
You can create a sign-in seal which is displayed to you during sign in. The idea here is that it will allow you to spot fake Yahoo sign in forms as the custom image or text that you have selected won't be displayed on those. It protects against phishing attacks mostly though.
The recent login activity page can also be useful. You can check and see the locations and devices used to sign in to your Yahoo account. If you spot a sign in from a location you never been to for instance, you should change your account password immediately.
You may also want to check the app and website connections page regularly. This page lists all apps or websites that you have linked to your account. You find the permissions that these apps have listed underneath each app. It is recommended to remove any app or website that you do not use anymore from here by clicking on the remove link next to it.
Those are just the precautionary measures that you can do on Yahoo directly. It goes without saying that you should also take care of your system's security by installing proper antivirus software, using a firewall, and common sense when on the Internet.
Advertisement


















A good password is one step for protection, but everyone is forgetting that they are not using a https connection which encrypts the data being sent from one device to yahoo. This is what makes gmail and outlook more superior. This is also why it is easier to hack yahoo, aol as well, and easier to get the information.
Martin, your comment regarding Yahoo passwords:
“…It should contain a mixture of upper- and lower case letters, numbers and special characters.”
Yahoo limits special characters to “_” and “-“.
My yahoo pwd includes a ” * ” character. But for my (primary) EarthLink account only standard upper-lower case letters and numerals are permitted with an unbelievable 8 character limit.
That’s not much, but still better than nothing I assume.
It seems that we the users can use all of the 100 word passwords,virus protections,firewall,etc in the world but until Yahoo,Google etc stop focusing on how many ad’s and commercials they can cram onto their sites we will always be screwed. They are too focused on how much money they can make to be concerned about safety and consumer protection.
Yahoo Mail will continue to be easy to hack until Yahoo allows more than 32 characters in passwords. If Gmail has a limit I haven’t found it yet.
I don’t think that a 32 character password limit has anything to do with hacking an email service. Yes, I agree that the limit shouldn’t exist in order to accommodate more security conscious users, but most people barely have a 10 characters long password, so raising the limit by itself doesn’t improve security too much.
In the case of the current attack however, it seems that the passwords were collected somewhere else, so the whole argument about the limit doesn’t apply in this particular situation.
What could help is raise the minimum character limit ;) Then again, you’d probably scare away quite a few users in the process.
I have a one step much simpler tip. Get a Gmail account.
Which is no more secure than Yahoo! and requires the same amount of steps to properly secure… So I would say that choosing between Yahoo! and GMail is a matter of personal choice.