Solid State Drives And Encryption, A No-Go?
Modern Solid State Drives are faster than their platter-driven brethren. They do have additional advantages like being completely silent when operating and better shock proof. The disadvantages are the high price per Gigabyte of storage space and unreliability when it comes to erasing or deleting data from the storage media. Especially the latter point can have severe security implications.
A recent study of the Department of Computer Science and Engineering at the University of California came to the conclusion that individual file sanitizing techniques were ineffective on SSDs and that built-in disk sanitizing techniques were effective if implemented correctly which was not always the case.
But this article is about encryption and Solid State Drives, read on how the findings impact encryption as well.
The makers of the open source encryption software True Crypt for instance recommend that "TrueCrypt volumes are not created/stored on devices (or in file systems) that utilize a wear-leveling mechanism (and that TrueCrypt is not used to encrypt any portions of such devices or filesystems)".
They basically ask their users to use True Crypt on conventional hard drives only and not on Solid State Drives and other Flash storage devices.
Why are they recommending that? For that, we need to take a look at how data is saved to SSDs.
Solid state drives use a technology called wear leveling to extend the lifetime of the device. Storage sectors on Flash drives have limited write-cycles which means that they cannot be written to anymore eventually. Wear leveling is used to avoid heavy use of specific sectors. With Solid State Drives it's not possible to save data to a specific sector of the drive. The wear leveling mechanism makes sure that the data is evenly distributed on the drive.
This means that it is theoretically possible that data is stored multiple times on the drive. If you change the TrueCrypt volume header for instance it can be that the old header is still accessible on the drive as it is not possible to overwrite it individually. Attackers could exploit this if they have found the old header. A basic example. Lets say you have encrypted your SSD and found out that a trojan recorded the password or keyfile that you use to access the encrypted data.
All you need to do on conventional hard drives is to create a new password or keyfile to resolve the issue and protect the data from access. On solid state drives however it may still be possible to extract the old header and use it to access the data with the stolen password or keyfile.
But what if the drive is empty before you use it? What if you plan to erase it securely if it is compromised?
Even this may not be sufficient. First, we already established that some "secure erase" tools offered by manufacturers of SSDs implement the technology incorrectly which means that the data may still be accessible after the operation.
TrueCrypt recommends the following precautions prior to encryption a blank Solid State Drive.
Before you run TrueCrypt to set up pre-boot authentication, disable the paging files and restart the operating system (you can enable the paging files after the system partition/drive has been fully encrypted). Hibernation must be prevented during the period between the moment when you start TrueCrypt to set up pre-boot authentication and the moment when the system partition/drive has been fully encrypted.
Even then the makers do not guarantee that this "will prevent data leaks and that sensitive data on the device will be securely encrypted".
What's the conclusion then? It depends. The security implications are probably nothing that home users need to worry about as it requires some technical background and equipment to attack encrypted drives. If you run a business, are a government official or an individual with data that needs to be protected at all costs, then you need to avoid drives with wear leveling for now.
Have a different opinion? Let me know in the comments.
Advertisement


















Martin –
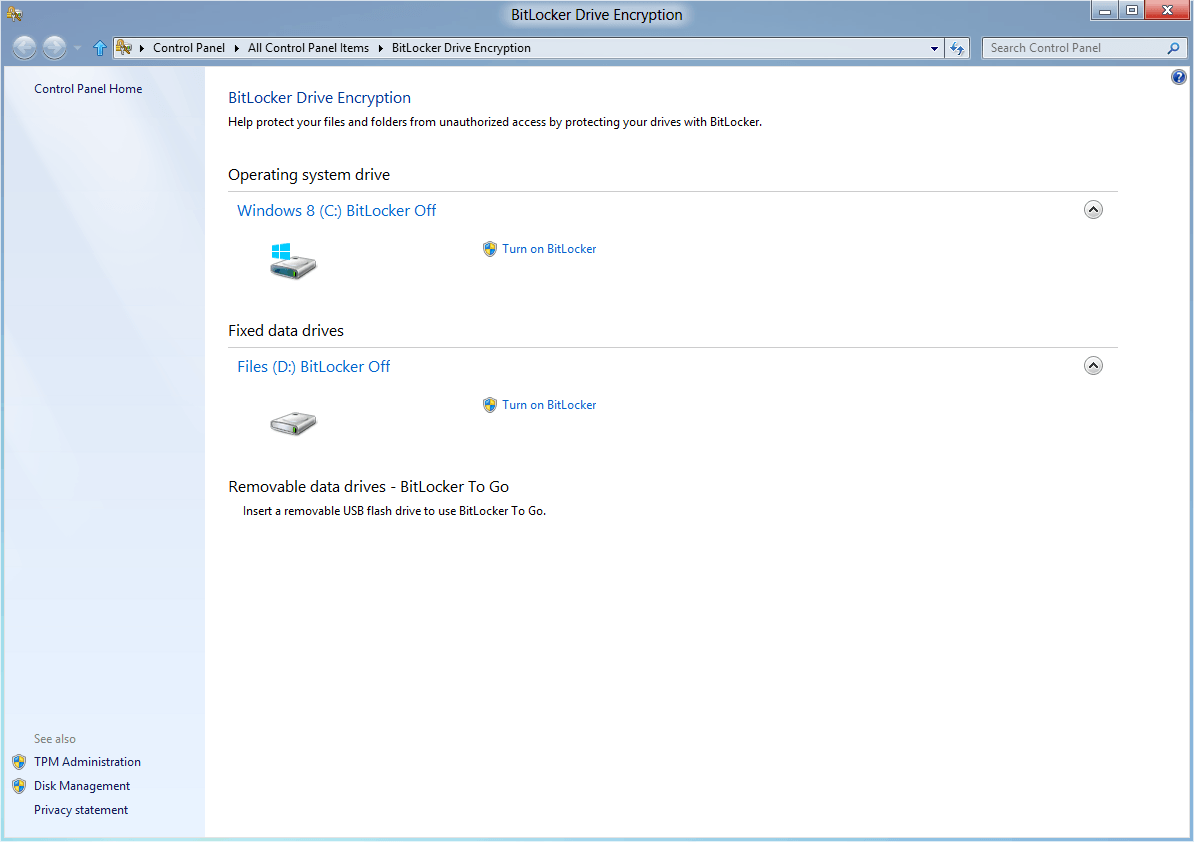
The emerging yet preferred method of encrypting drives, both hard drives and SSDs, is Self-Encrypting Drives (SED), standardized by the Trusted Computing Group and produced by all the major drive manufacturers. SEDs have an on-board encryption engine in HARDWARE; negligible performance impact. The encryption key is generated in the factory by an on-board random generator and never externalized (thus, no encryption key management is needed). By simply deleting/replacing the on-board encryption key, the drive is instantly sanitized; the old data is not readable, but the drive can continue to function with the new key. This “Crypto Erase” technique is soon to be an officially sanctioned drive erasure technique. SEDs are superior to software-based encryption in every respect: ease of management. life-cycle costs, performance, robustness, transparency, user acceptance, etc. As your references have shown, standard hard-drive erasure techniques cannot be applied reliably to SSDs, but SEDs with Crypto Erase do completely and reliably erase an SSD.
Thanks for the good description of the issue – I’m wondering now that it;s been a year since you wrote this, if anything new has developed on this front? Is it even possible these days to but a USB stick without wear-leveling?
Hello,
very interesting article.
What about disk consumption (i.e. damage prone)?
If you consider that I can replace my SSD with a new one every (max) 4-5 years, is there some risk to get the disk damaged very early if I use a disk encryption?
Note that I use Linux and I encrypt my /home directory (I use cryptsetup, as well as Truecrypt).
I can confirm that a degausser does not work. I have one set up on each PC I deemed sensitive. At the push of a button, everything is wiped. I tried one out on a USB stick and an SSD drive. Can still see data :(
A few typos:
“sanititing”
“is it” instead of “it is”
Thanks, corrected.