Anti-Phishing Tips
Phishing is a popular attack form that is used to steal data on the Internet. It is often associated with emails as the majority of phishing attacks are conducted via email, but there are other forms as well.
Phishing attacks usually look as if they are coming from a legitimate source, PayPal, Amazon, a financial institute or even the government. This is done to make the email look legit so that users are more likely to believe what the attackers are trying to make them do.
This usually involves clicking on a link in an email but may sometimes also involve loading an attachment or other tasks.
I worked for a large bank in the past where phishing support requests were handled regularly on a daily basis. Users usually believed the "phishing story" and provided attackers with account information and sometimes even transaction numbers. At other times, they may have executed attachments that they thought were security updates or financial reports.
The websites that attacked users may be directed to look like the real website more often than not. This is again done to get users to believe that this is all a legit process and that they have nothing to worry about. Data that is entered on those sites on the other hand is usually saved on remote servers and used by the attackers to steal money, take over accounts, spam or perform other malicious activities.
Phishing tips:
- Phishing only works if you click on a link that leads to a website that looks similar to the one you want to visit. If you do not click a link in the email but enter the url of the company directly in your browser window you are save. This is the best tip to prevent phishing at all. Do not follow email links.
- If you receive an email asking you to call a company compare the phone numbers and use the ones that you know and not the ones mentioned in emails. Social Engineering is a rising threat as well. Most users do not know that phishing can also happen by phone. Check the phone numbers in emails.
- You receive an email stating that you are the highest bidder for a golden ring on eBay or that your phone bill is incredibly high and that you can verify the bill by clicking on the document attached. Use your brain. You know that you are not the highest bidder and that the phone bill can't be real as well. To check the first type in the url of eBay in your browser, you will see there is no such auction. Call your phone company in the second one and they will verify that this is a phishing attempt.
- Attachments can contain viruses or other malicious code. If you do not expect a document, do not open it. Even if you do, scan it first. You can usually right-click on an attachment and save it to the computer to scan it first.
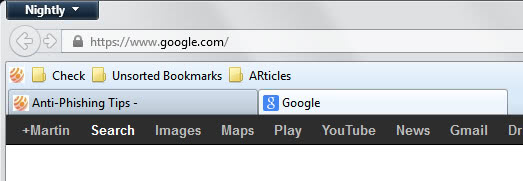
- Always verify that you are at the right website before entering data. Firefox and Internet Explorer have anti-phishing tools on board but it is always a good idea to verify this for yourself. Look at the url, is it the right one? It should normally be a https:// website which can be verified by looking at the yellow padlock in the status bar. If you click it you will see the certificate and you can compare the certificate to the one of the company that you want to visit. (some company's store the certificate information on their webservers, some don´t, call them and you will receive this information.)
To sum it all up. Tech savvy users may detect the majority of phishing attempts and fake websites right away. Inexperienced users on the other hand find it more difficult and that's where guides like this one comes in handy. This is not only a trust issue as some may assume. If something looks real, it must be real, right? It is also important that users get a basic understanding of the technical possibilities, that email addresses can be faked and that it is easy to replicate official emails and websites.
Advertisement















Interesting read Luke, thanks for that link. I personaly think that phishing success would be minimal if users would know what it was and how it worked.
One of my collegues actually did a scientific study on pishing, and the effect of user education about pishing. He presented it at the ITiCSE 06 conference.
You can download the actual paper, and powerpoint slides from here.
Missed one tip. Make sure your host file was not changed. You can specify the IP of a url in that host file which will override the Nameservers. Means you could add an entry like 85.10.210.166 http://www.ebay.com
This would mean that if you type http://www.ebay.com in your browser you would be directed to my webserver..