Apple's cybersecurity notifications are on the rise

In recent years, there has been a growing number of state-sponsored attacks on iPhones. These attacks are typically carried out by well-funded and sophisticated adversaries who are targeting specific individuals or groups.
Apple is known for its commitment to security, and its alert system is a key part of its efforts to protect its users from state-sponsored attacks. These attacks are typically carried out by well-funded and sophisticated adversaries, and they can be very difficult to detect and prevent.
Apple cyber attack alert system can help to protect users by identifying and notifying them of potential attacks. And recently, there have been reports that many Indian government officials have received this warning as mentioned in Twitter/X user @riazgold's post below.
Apple has sent 'HACK/COMPROMISE ALERT' emails to 8 opposition leaders and 3 senior journalists claiming "State-sponsored attackers may be targeting your iPhone”. This is happening just before elections, are we leaving in free country? pic.twitter.com/1E9hGdqT6S
— Riaz ????? (@riazgold) October 31, 2023
How does Apple cyber attack alert system work?
Apple cyber attack alert system is based on a combination of threat intelligence and device telemetry. Threat intelligence is information about known and potential threats, and it is collected from a variety of sources, including security researchers, government agencies, and other companies. Device telemetry is data that is collected from Apple devices, such as information about the apps that are installed, the websites that are visited, and the files that are opened.
Whenever Apple cyber attack alert system monitors suspicious activity, a message that reads ''State-sponsored attackers may be targeting your iPhone'' is sent to users.
Apple uses threat intelligence and device telemetry to identify patterns of activity that may be indicative of a state-sponsored attack. For example, if Apple detects that a group of devices are all accessing the same malicious website, or if they are all being targeted by the same type of malware, this may be a sign that they are being attacked.
If Apple believes that a user's device may be compromised, it will send the user an alert. The alert will typically provide information about the potential attack, such as the type of attack and the date and time that it was detected. The alert will also include recommendations for how the user can protect their device, such as changing their passwords or updating their software.
Read also: Microsoft says Chinese state-sponsored hackers penetrate critical U.S. infrastructure.
Who is at risk of state-sponsored attacks?
State-sponsored attacks are typically targeted at high-profile individuals and organizations, such as government officials, journalists, and activists.
However, anyone can be targeted by a state-sponsored attack, and it is important to be aware of the risks.

What can you do to protect yourself from state-sponsored attacks?
There are a number of things that you can do to protect yourself from state-sponsored attacks, including:
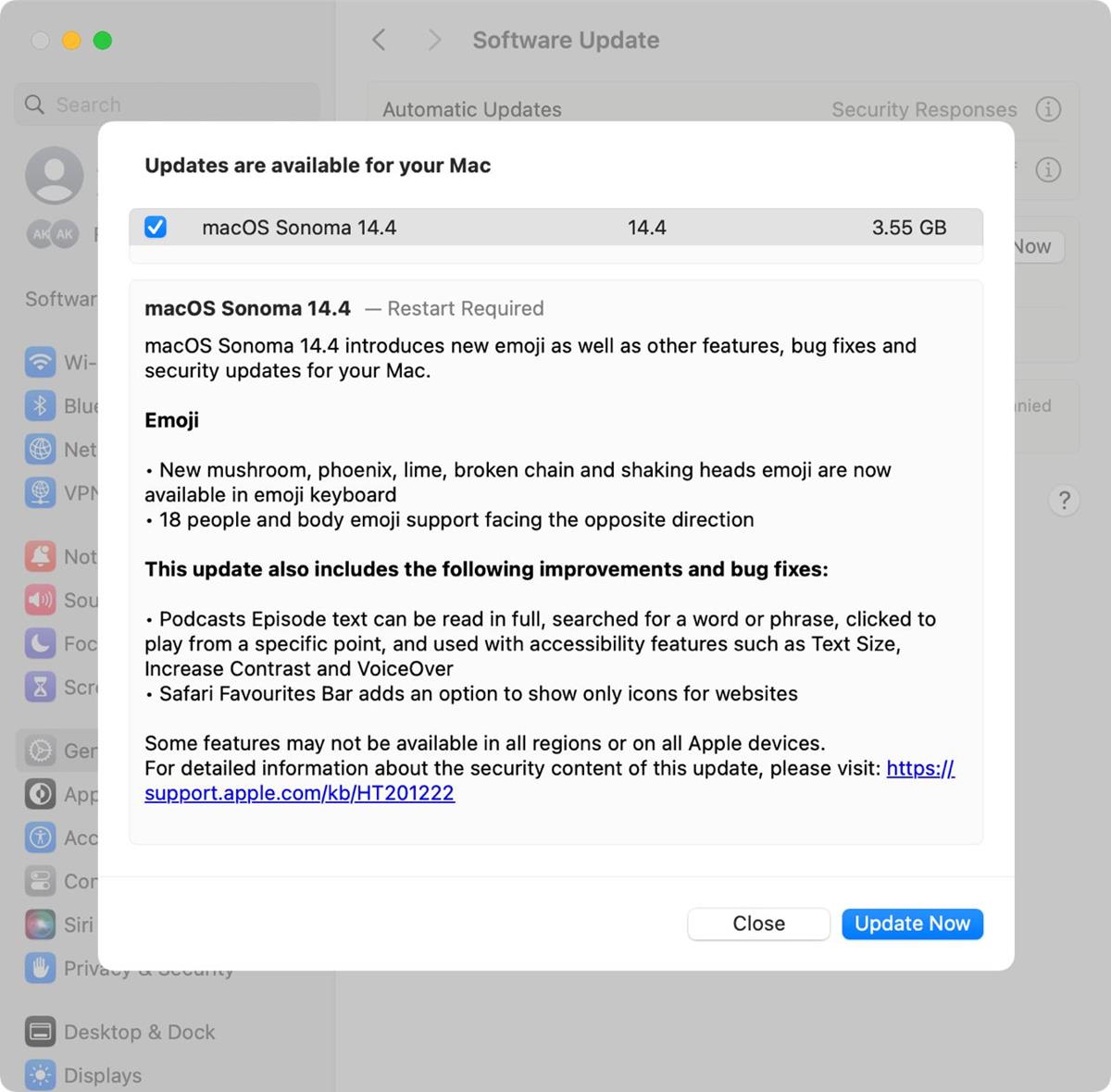
- Keep your software up to date. Software updates often include security patches that can help to protect you from known vulnerabilities
- Be careful about what apps you install. Only install apps from trusted sources, such as the App Store
- Be careful about what links you click on and what attachments you open: Phishing emails are a common way for attackers to gain access to devices
- Use a strong password manager to create and manage strong passwords for all of your online accounts
- Enable two-factor authentication whenever possible. Two-factor authentication adds an extra layer of security to your accounts by requiring you to enter a code from your phone in addition to your password
If you receive an alert from Apple about a potential state-sponsored attack, it is important to take it seriously. Follow the recommendations in the alert to protect your device and your data.
Advertisement


















Apple seems to have become more of a target now that all its hardware basically runs with similar ARM systems. Yes, some differences of course exist, but I can see a well engineered malware attacking all of Apple’s platforms.