Google Chrome 114 security update fixes 4 vulnerabilities

Google released a security update for its Google Chrome 114 web browser that addresses four different security issues in the browser. The desktop and Android versions of Google Chrome are affected by the issue, as are third-party web browsers that use Chromium as their core.
The security update is available already and most Chrome installations will receive the update over the course of the coming days and weeks.
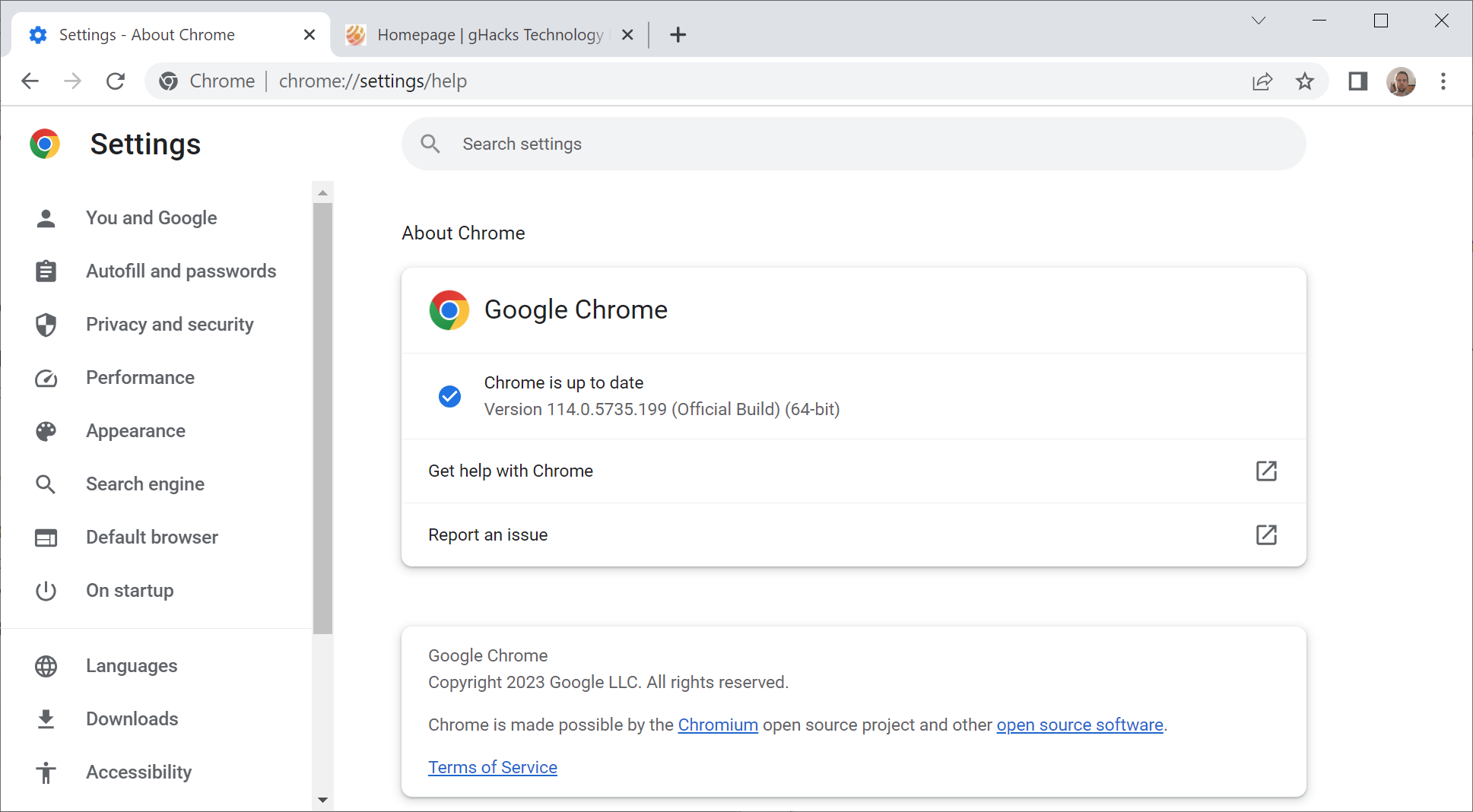
Chrome users on desktop systems may speed up the installation of the update in the following way:
- Select Menu > Help > About Google Chrome, or, load chrome://settings/help directly in the browser's address bar.
- Chrome checks for updates and will download the new version automatically.
- Restart the browser.
The About page displays the installed version whenever it is opened.
The following versions of Google Chrome are protected from potential attacks that target the vulnerabilities:
- Google Chrome for Mac: 114.0.5735.198
- Google Chrome for Linux: 114.0.5735.198
- Google Chrome for Windows: 114.0.5735.198 or 114.0.5735.199
- Google Chrome for Android: 114.0.5735.196
The security issues in Chrome 114
Google lists only three of the four security issues that it patched in the latest Chrome update. The company does not reveal information about security issues that it discovered internally.
The three security issues listed on the official Chrome Releases blog have a severity rating of high, which is second only to critical:
- [$20000][1452137] High CVE-2023-3420: Type Confusion in V8. Reported by Man Yue Mo of GitHub Security Lab on 2023-06-07
- [$10000][1447568] High CVE-2023-3421: Use after free in Media. Reported by Piotr Bania of Cisco Talos on 2023-05-22
- [$5000][1450397] High CVE-2023-3422: Use after free in Guest View. Reported by asnine on 2023-06-01
They address user after free and type confusion vulnerabilities in the components V8, Media and Guest View. Google makes no mention of exploits in the wild.
Chrome users may still want to update the browser as soon as possible to protect it from potential attacks. Third-party Chromium-based browsers such as Microsoft Edge, Brave, Vivaldi or Opera are affected as well and will be updated accordingly, usually in a matter of days.
Closing Words
This is the third point update for Chrome 114. Google released Chrome 114 on May 31, 2023. It fixed 16 security issues in the browser. On June 7, Google released an update for a critical security issue in Chrome that Google confirmed to be exploited in the wild, and another security update a week later to address a critical security issue in Chrome.
Chrome 115 is scheduled for a July 12, 2023 release.
Now You: when do you update your browsers?



















@Tinarse–“Personally, I don’t stress about installing updates immediately.” Nor I, and I usually postpone all Windows updates. But, I run Patch My PC or Winget UI once a week and, “click, click” have programs update. Such a non-issue in this day and age.
Once upon a time, the ease, finesse, and sophistication of updating wasn’t so simple.
Now, users complain because of “click, click, update.”
Personally, I don’t stress about installing updates immediately. The odds of getting hit are tiny (when was the last time your anti-malware software found a real threat?), and usually require stupidity from the wetware (d/l-ing, installing or clicking on something they shouldn’t).
And my set-up is significantly more hardened than most. So if I leave updates for a few days to let the rest of the world do the de-bugging (see especially: Windows Patch Tuesday updates; I give those a week before I’ll touch them), I’m doing myself a favor.
That’s for me personally. For my clients (see: comment about the wetware), I install updates asap.
@tinarse > “(see especially: Windows Patch Tuesday updates; I give those a week before I’ll touch them)”
About Patch Tuesday updates, I can sure you that waiting an entire week does not make the difference. The crude fact is that every new Windows update may have unexpected effects. Indeed I can’t barely remember a single update without issues since W8, that was my first OS. ;S
@John G., I agree that Win updates often have issues, but most of the time those are mitigated – or at least identified – in the few days after Patch Tuesday, as tens of millions of users do the “gamma” testing that it would have been nice if MS had done in the first place. I’m comfortable installing most of those updates by the following weekend.
My first OS was a little earlier than yours: IBM 360 running APL. ;-)
@tinarse > “My first OS was a little earlier than yours: IBM 360 running APL. ;-)”
Amazing! :S
Why are you guys advertising CCleaner after all the negative articles? It says on that post you’re always looking for good products for your users and that’s the best you can come up with? Commenting here since you can’t there.
@Al, CCleaner Pro has the best driver updating tool IMHO. No single problem here since three years. :S
>”$20000 … Type Confusion in V8 … $10000 … Use after free in Media … $5000 … Use after free in Guest View …”
I should polish up my skills in finding user-after-free and type-confusion errors by Google developers. There’s a vast fortune to be made, and no end to the vulnerabilities to be found.
Use after free shouldn’t even happen when programming according to standards and best practice.
the more, the better!
The better, the more! :D
> “Now You: when do you update your browsers?”
ASAP. It’s very important to update them to the latest version.
“ASAP. It’s very important to update them to the latest version.”
This just isn’t true, is it? Have you ever tried not updating something – I’ll bet actually you might answer “no”, you strike me as that kind of person. Well I’ll tell you what happens: nothing.
If you don’t apply a certain windows, browser update, etc, immediately, or ever, literally nothing happens.
You have to be a combination of very unfortunate and very foolish to have any kind of problems due to a missing or skipped update.
well .. leaving known vulnerabilities unpatched is kind of dumb right ?
On the other hand is not closing a published exploitable vulnerability on average not leading to an immediate compromise, UNLESS one is targeted, in that case it becomes deadly.
Also do patches of course introduce new vulnerabilities, that may or may not be exploitable, but are (at least at the moment of release) unknown to everybody (incl. the bad guys). Patches are further often insufficiently tested and may lead in special configurations and the worst cases even to production downtimes, which might be worse, than a successful attack. The risk of this happening decreases over time, meaning the risk declines when patching later, than earlier.
This means the answer is not a clear straight forward YES or NO, but depends to some degree on the individuals attack surface, system use, system criticality and the threat level the entity is exposed to.
In principle timely patching a known vulnerability is a pretty smart idea. In case you are not specifically targeted, that’s less essential, than when you are, nonetheless it is kind of smart, albeit, if you are targeted by a truly capable threat actor, they’ll probably have zer0-days at hand and immediate patching won’t help either, as you are f*cked up anyhow.
So yeah, you may not be immediately compromised by not patching, but the risk of a compromise continuously increases over time. This means patching timely does make sense to minimize the overall risk.
I’ve had my device so f%#k%d up ever since and probably before the end of pandemic…I’ve spent 1000″s of hrs. and 100″s of resets trying to beat off the powers that be off this device…to no avail…I don’t know why I even waisted all the time and effort thinking there was a way a chance of getting local,state and yes big bro”s off this device.Every time I turned an Apps permission off ,put a setting this way or that way,tried to do anything to limit access to this device I finally realized I was beating my head against a wall…Apps permissions were fixed so I couldn’t/still can’t even check or uncheck them,categories will even say like two are deleted ,can’t turn notifications on or off on some apps,some apps are listed but can not figure for the life of me where to find them believe me as I said I’ve spent/waisted that much time on this b.s..The more I try the more [they] add for apps,cancel my options/setting choices/ I get redirects/error 401’s/sites aren’t private,right now I have phone different phone apps with same little picture …..So frustrating these organizations are good especially with help of the Tele co.and tech co.Anyway zero days are here to stay at least on this device….I hope I frustrated the powers 10% of the frustration they’re causing me….There’s nothing like my camera taking selfies and pics whenever it wants and the green microphone light coming on sneakily for a few seconds then disappearing….Yeah I tried new phones but of course they become inoperable with a pass code all of a sudden not working or when I press a zero a 9 pops up instead of the pressed zero…which makes things a little frustrating.I can go on and on and on but I have Zero time left ….so I make do the best I can with tape over cams and over mics putting device I. a Tupperware container when not in use…of course I forget the Tupperware sometimes and the tape is pain in ass….unfortunately sometimes I forget to not talk in front of these mega=phone(s)but when THEIR MICROSCOPE COMES OUT ITS NOT JUST THE PHONES ITS THE T.V AND ANY SERVICE / DEVICE ONE HAS TO USE.FOR LIVING IN THE 21ST CENTURY….Anyone want to use my phone …..
@Anonymous, that’s what I meant, the problem is not an exploitation bug but the cumulative number of fixed bugs that you’re not updating. First you have one, then two, then three and when you take care you have dozens of non updated bugs. The more time without updating, the more risks you will have. :S
@muh updates, that’s what a hacker would say, more or less like “please, don’t update, exploitation issues are not important at all”. Security updates are very important.
I’m sorry but you are simply not living in reality, instead, living in fear. I am not even against updates, security or otherwise – but this is just borderline delusion.