Mozilla and Microsoft distrust TrustCor root certificates in their browsers
Mozilla and Microsoft have taken action against three root certificates by TrustCor. These root certificates are now distrusted by the browsers.
Mozilla set the distrust date to November 30, 2022, while Microsoft sets the date to November 1, 2022. Other browser makers, including Google and Apple may follow.
Concerns about TrustCor were raised on Mozilla's Dev Security discussion forum in early November by Joel Reardon, a professor at the University of Calgary, and others.
The main claim leveled against TrustCor was that it appeared to be tied to Measurement Systems, which "distributed an SDK containing spyware to Android" users. The following evidence was presented:
- Measurement Systems and TrustCor had their domains registered by Vostrom Holdings.
- The two entities have identical corporate officers.
- TrustCor operates the email encryption product MsgSafe. One beta version of MsgSafe contained the "only known unobfuscated version of the spyware SDK" by Measurement Systems.
New information came to light during the course of the discussion on the security group. A representative of TrustCor provided information.
In the end, it was clear that there were ties between Measurement Systems and TrustCor, at least until 2021, and that one developer hired by TrustCor had access to an unobfuscated version of the source code of the Measurement System malware SDK. However, there no evidence of the mis-issuing of certificates was presented.
Mozilla decided to distrust TrustCor certificates from November 30, 2022 that are included in the Mozilla root store. The certificates will be removed from the root store when they expire. The certificates may be removed at an earlier point if "evidence is found that the CA has mis-used certificates or the CA backdates certificates to bypass the distrust-after settings".
Microsoft did not provide a statement to the discussion group, but it set the distrust date to November 1, 2022.
You find the full discussion, evidence and commentary by the TrustCor representative here.
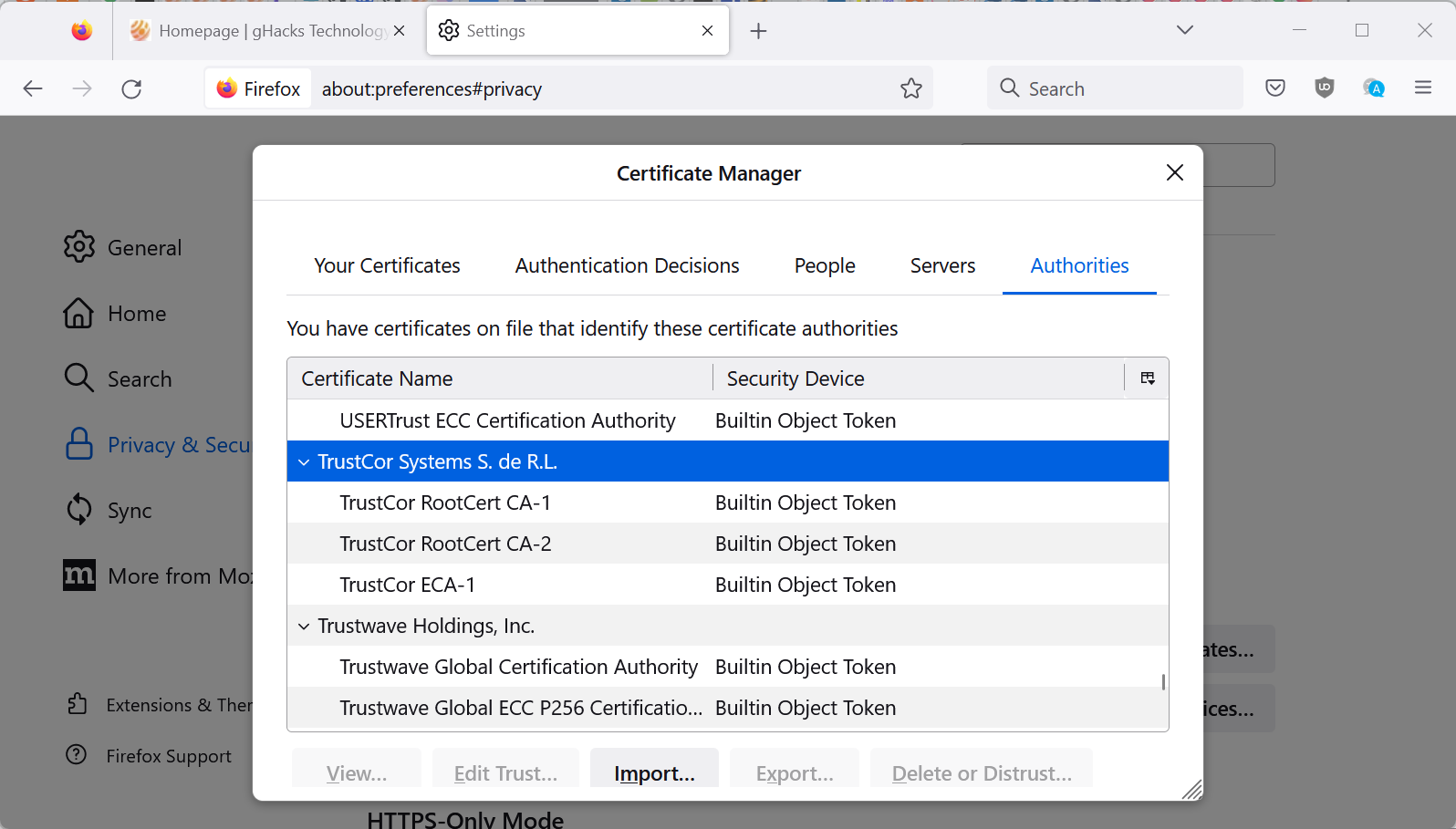
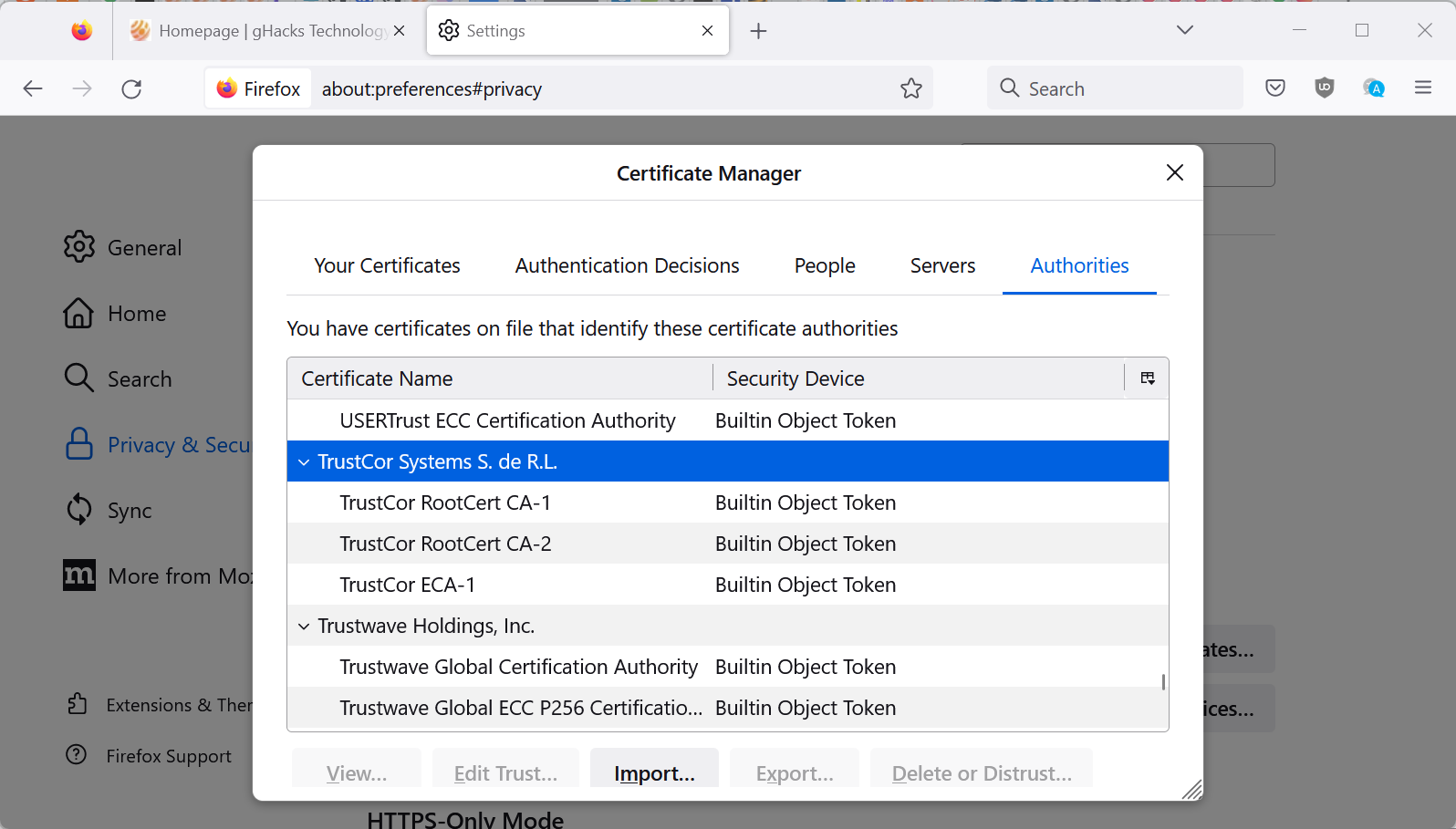
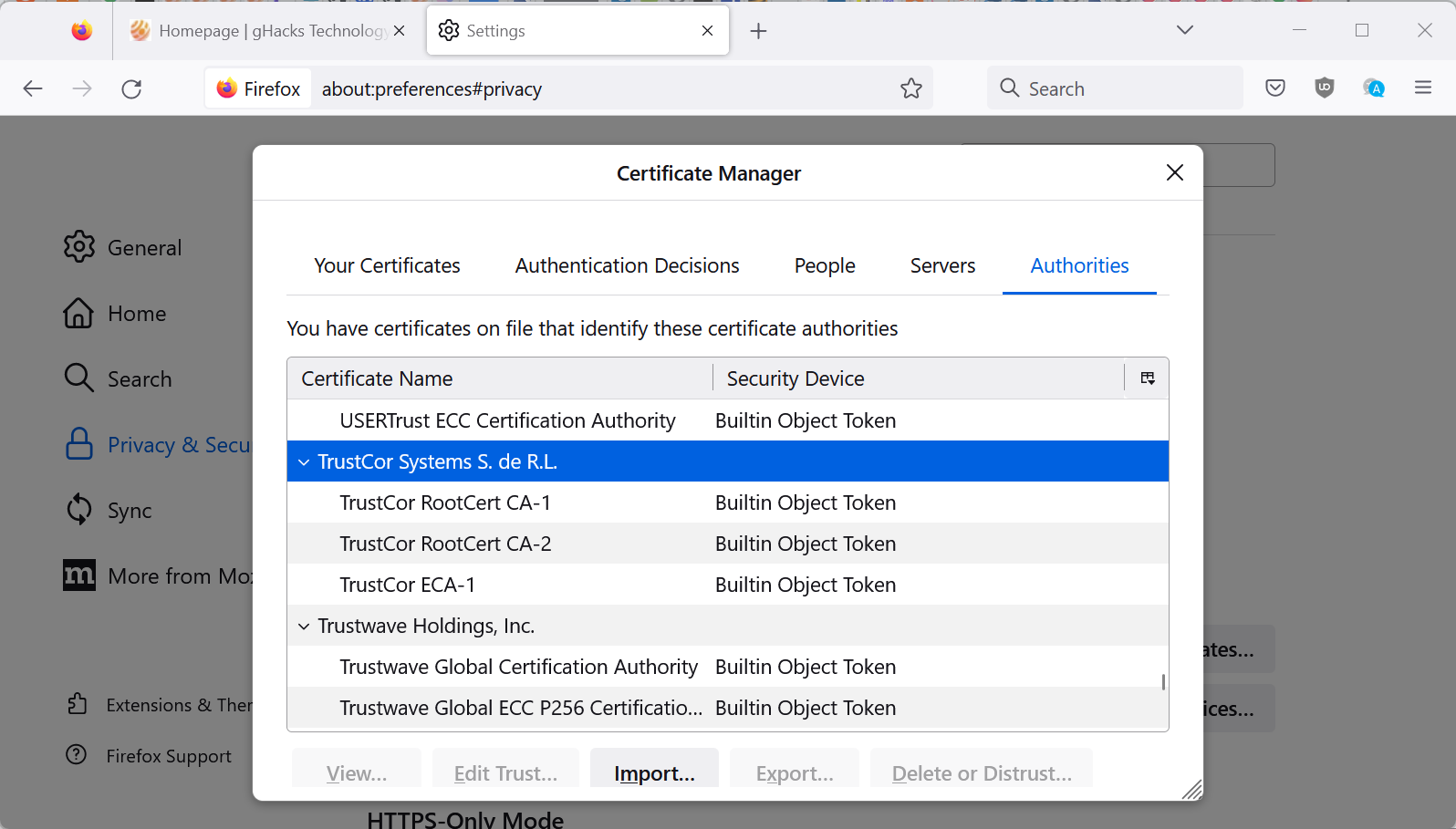
Firefox users may delete TrustCor certificates immediately in the browser.
Note: removing certificates may prevent access to certain sites on the Internet. You may use the "export" feature to save them to the local system, so that you get an option to restore them using the import option.
Here is how that is done:
- Load about:preferences#privacy in the web browser's address bar.
- Scroll down to the Certificates section.
- Activate the "view certificates" button.
- Scroll down to TrustCor. The list is sorted alphabetically.
- Select each of the TrustCor certificates, then Delete or Distrust, and confirm; this removes the certificates from the browser.
















You can delete them, but on Browser restart they are listed again, not really sure how to remove them permanently.
Cyber-ages ago, I gave up on the notion of managing Windows certificates when I first opened certmgr.msc and brain scream became overwhelming after about a minute of drilling the console entries.
For Mozilla, though, I often wondered why one couldn’t OPT-IN to start off (or wipe and start over) without any certificates and suffer through a while of surfing our daily habitual sites and dealing with alerts to allow them and then block what we want, or “this session only.” You know, an old school “learn” function.
Of course, whether or not opt’d in or out, the about:preferences#privacy Certificates section would remain as is but with necessary security.nocertdb augmentation when opt’d in.)
The Qt5 WebKit QuiteRSS client, having its own crt file, has exactly that function. The bundled crt file hasn’t been updated since 7/10/21 and in the meantime I’ve had to allow three feeds, each now having a crt file in QRSS’s certificates root folder. (This is just an FYI; I don’t need any hints, tips or opinions about QuiteRSS certificatations. Thank you.)
I see also “Google Trust Services LLC” in the Firefox trusted authorities. Are they not well known for distributing android spyware too ?
Trust me, distrust Truscorp.
What a funny word game.
A while back there was an article here to distrust QuoVadis, we still doing that?
@1337,
Yes, I recall that episode myself. At the time, I was forced to re-enable QuoVadis because the Dutch Post Office site at https://www.postnl.nl/ uses their certificates and blocking them meant the P.O. site became unusable.
Can’t delete the TrustCor items (they keep showing up after my deleting action).
If I look into the My Certificates section, I see my VPN provider -> NordVPN.
Be pref(“security.nocertdb”) set to “true” or to “false” (Default=false) I cannot delete the 3 TrustCor root certificates but I can disable them : we disable all 3.
Exit Firefox – I notice that my cert9.db has been modified.
Restart Firefox : the 3 TrustCor root certificates appear :
as disabled if pref(“security.nocertdb”) = “false” (Default) : OK
as enabled if pref(“security.nocertdb”) = “true” : NOT OK
Toggled “true” / “false” and restart several times : always same results
No idea from there on if the 3 TrustCor root certificates are considered by Firefox as disabled only if pref(“security.nocertdb”) is set to “false” (Default). I’m missing something.
// About pref(“security.nocertdb”)
// [NOTE 1] This affects login/cert/key dbs. The effect is all credentials are session-only. Saved logins and passwords are not available. Reset the pref and restart to return them.
// [NOTE 2] “this is not a fingerprinting issue but a first party isolation and super cookie problem” [https://bugzilla.mozilla.org/show_bug.cgi?id=1334485#a6198890_474980]
I don’t use Firefox’s Login Manager (disabled) but the ‘Bitwarden” extension.
I’m keeping pref(“security.nocertdb”) = true (Default=false).
Puzzled.
Mozilla explains how Firefox handles this on this page: https://wiki.mozilla.org/CA/Changing_Trust_Settings#Changing_Root_Certificate_Trust_Settings
Basically, what happens is that trust is removed from the selected certificate when you select the delete option, but it is still shown.
“If you delete a cert in your database that is also in the built-in list, it may appear to be completely gone, until you restart your program, at which point it will reappear, because it never left the built-in root list. However, the trust bits will be turned off for the root.”
The same with my Firefox and LibreWolf. CANNOT DELETE TrustCor certificates. They come back after deletion.
What’s about removing certificate authority from sources you don’t trust personally? For instance, those from countries which are not democraty (China…). To be done in browsers and the OS directly.
Remove everything in your home and on your body which are Made in China, RIGHT NOW! They will kill you in next 10 seconds.
[https://en.wikipedia.org/wiki/Democracy_Index]
You will have to remove a lot of countries. Many are not even real democracies but flawed.
Are you asking what the implications are if you remove those certs? You get a big fat warning each time you visit a website using their certificates. That will be real fun!