0Patch releases patch for Internet Explorer vulnerability (also for Windows 7)
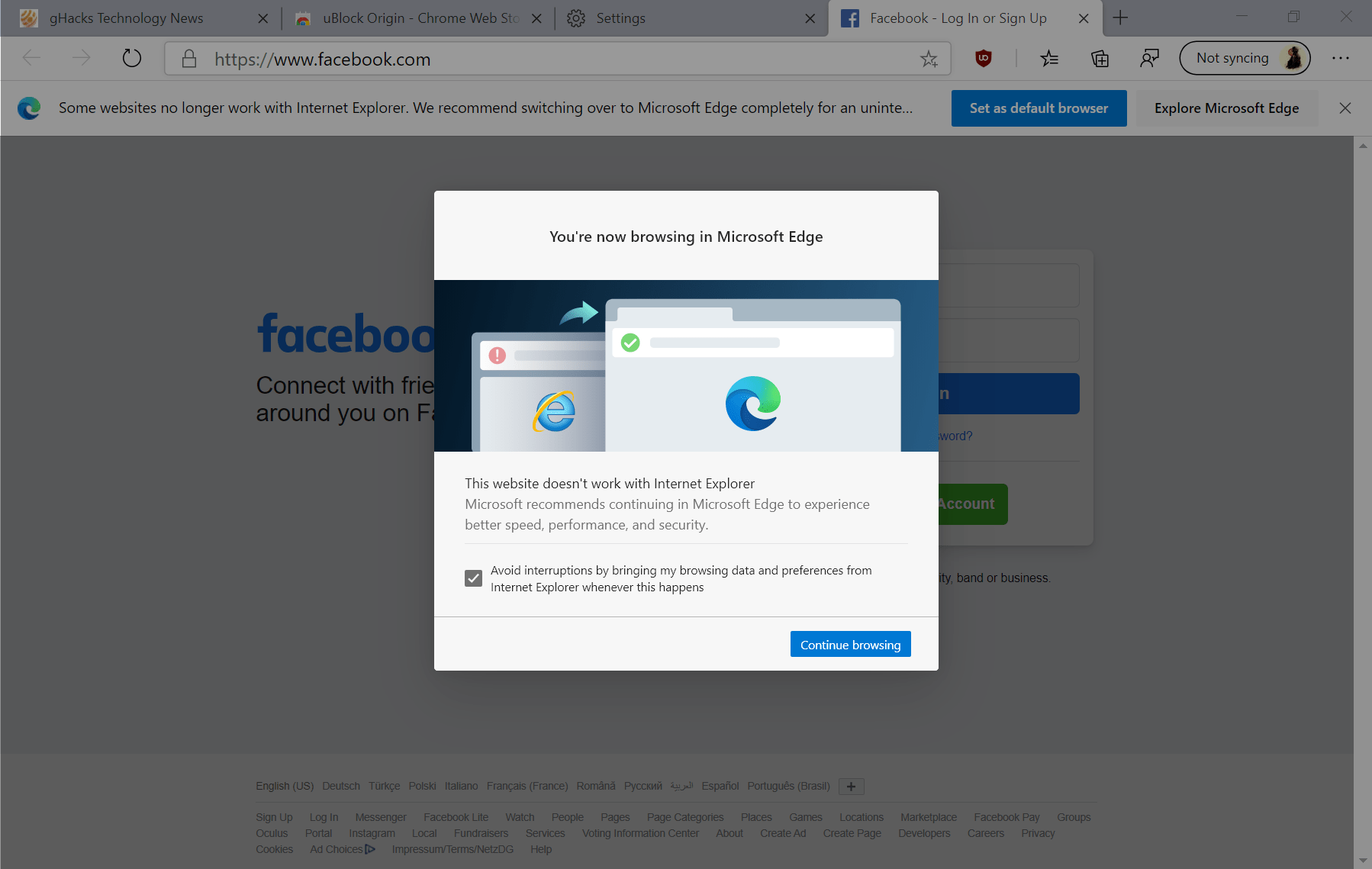
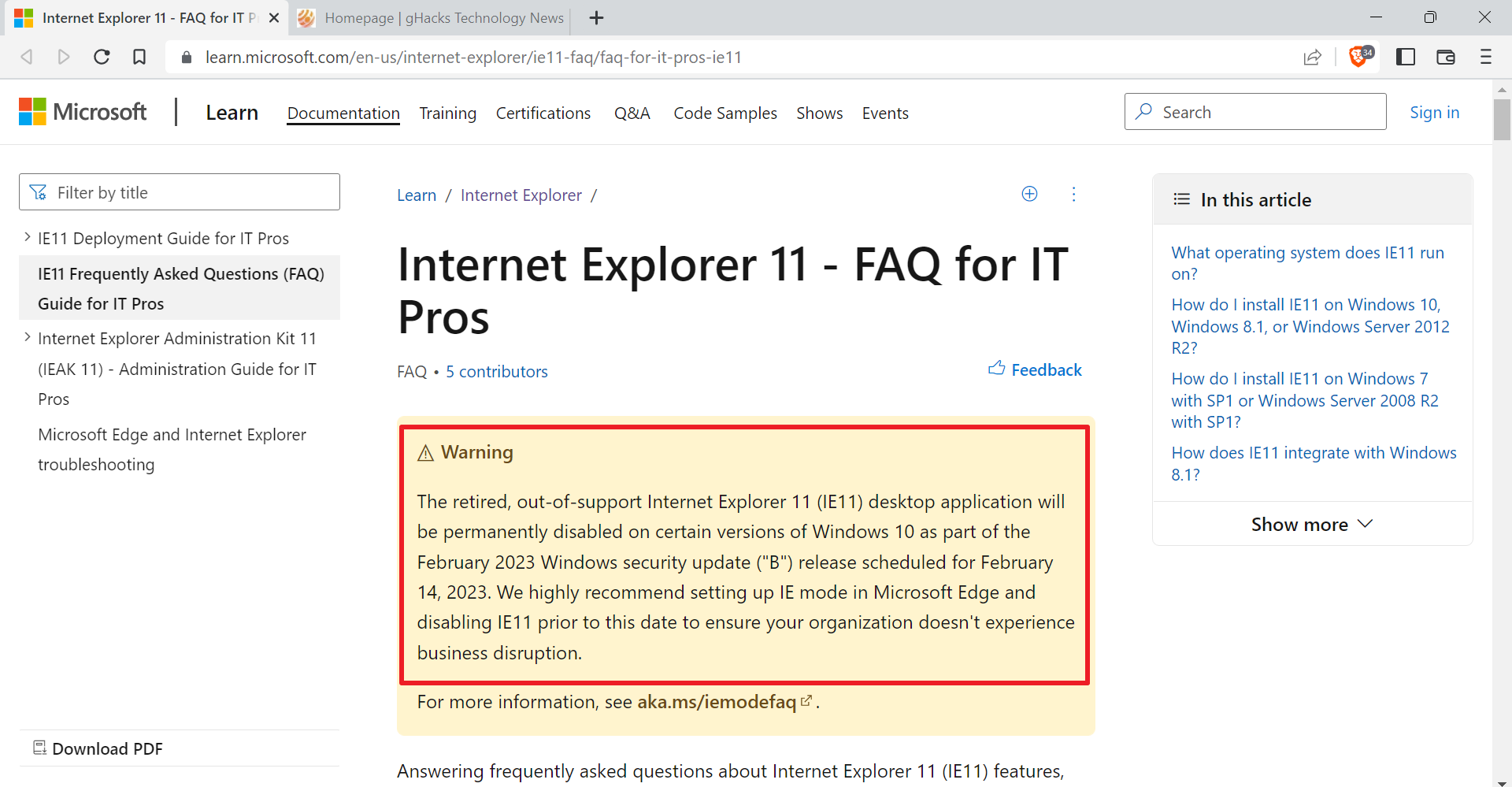
Microsoft ended support for the company's Windows 7 operating system on January 14, 2020 and revealed a day later that it would not support Internet Explorer 11 on Windows 7 either anymore. The timing was as bad as it could be considering that a vulnerability that affected Internet Explorer was discovered after support end that Microsoft rated critical (the highest severity rating).
Microsoft confirmed that it was aware of limited attacks targeting the vulnerability and that administrators should expect a patch to arrive on the second Tuesday of February, the company's monthly Patch Tuesday.
Administrators may apply a workaround on systems to protect against attacks.
Microsoft will provide the patch for Enterprise customers and businesses that are subscribed to the Extended Security Updates program. Home users on the other hand cannot join the program to extend support for Windows 7 by up to three years.
While it is still up for debate whether Microsoft will release a patch for Internet Explorer 11 on Windows 7, security company 0Patch stepped in as promised and released a micropatch that fixes the vulnerability based on a workaround that Microsoft suggested.
The company announced in late 2019 that it would create and release security updates for Windows 7 and Windows Server 2008 R2 after the official support end of both products in January 2020.
A blog post on the official 0Patch website provides details on the micropatch and how it can be applied to affected systems. According to the information, the patch is available for Windows 7, Windows 10 version 1709, 1803 and 1809, Windows Server 2008 R2, and Windows Server 2019.
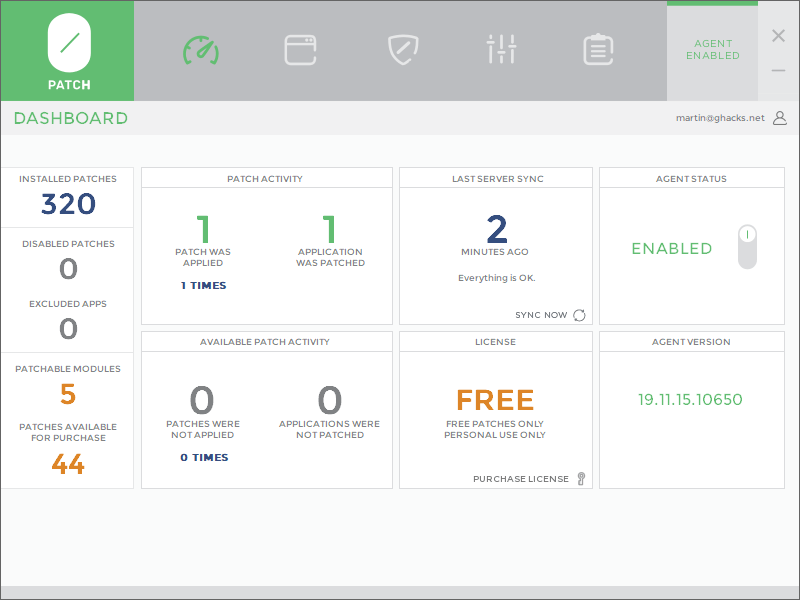
Administrators who want to install the micropatch on supported devices need to download the 0Patch Agent from the company's website to get started. It is a free program that can be installed on Windows devices.
Note that it is necessary to register a free account as you need to sign-in to the application. Once you are signed in data is synced between the local system and the server to determine the patch state of the system. The program lists patches that are available for free and for purchase in the interface; all it takes is to get the Internet Explorer 11 patch installed for the system to protect it against attacks that target the vulnerability.
0Patch states that its patch does not cause the side-effects that Microsoft's workaround is causing (web applications that make use of jscript.dll will not work anymore).
Administrators who run the 0Patch Agent software on their devices may toggle patches on or off in the interface.
Closing Words
It will be interesting to see if Microsoft will release the patch for unsupported versions of Windows 7 or Windows Server 2008 R2. If you still use Windows 7 or Windows Server 2008 R2, you may want to consider using the micropatch instead to protect systems against attacks.
Now You: do you think that Microsoft will release a patch for unsupported versions of Windows?













The patches for Enterprise customers and businesses will end up in the wild we will still get them in the end just like XP !
I have access and I’m more than happy to share them :)
“Internet Explorer 7” This was a little confusing, in the first paragraph.
“Now You: do you think that Microsoft will release a patch for unsupported versions of Windows?”
It doesn’t matter what we thing. All that matters is what Microsoft thinks. I suspect most ghacks readers are educated enough not to be big IE users in any case.
Why did 0Patch stopped at Windows 10 1809 ? What about patching 1903, 1909 ?
Microsoft’s workaround breaks SFC…
Because they are still supported by MS?