Mozilla disables TLS 1.0 and 1.1 in Firefox Nightly in preparation of deprecation
Firefox maker Mozilla disabled support for the protocols TLS 1.0 and TLS 1.1 in recent versions of the Firefox Nightly web browser.
Major browser makers such as Mozilla and Google announced in 2018 that support for the decade-old standards would be dropped in 2020 to improve the security and performance of Internet connections. Back then it was revealed that TLS 1.1 was used by 0.1% of all Internet connections; the number has likely gone done in the meantime.
Transport Layer Security (TLS) is a security protocol used to encrypt Internet traffic; TLS 1.3 Final was published in 2018 and companies started to integrate the final version into browsers shortly thereafter.
Mozilla started to enable TLS 1.3 in Firefox Stable in 2018, and other browser makers such as Google added support for the new protocol version as well.
Tip: here is a way to determine if your browser supports TLS 1.3 and other security features.
Firefox and TLS 1.0 and 1.1 deprecation
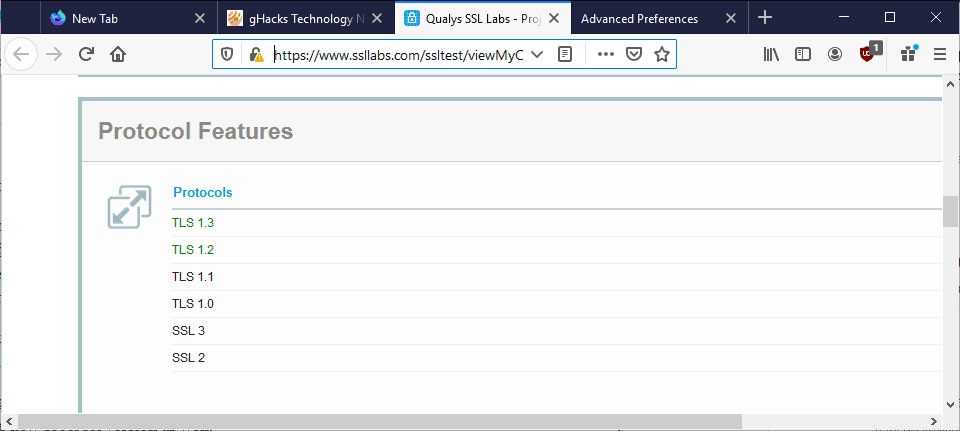
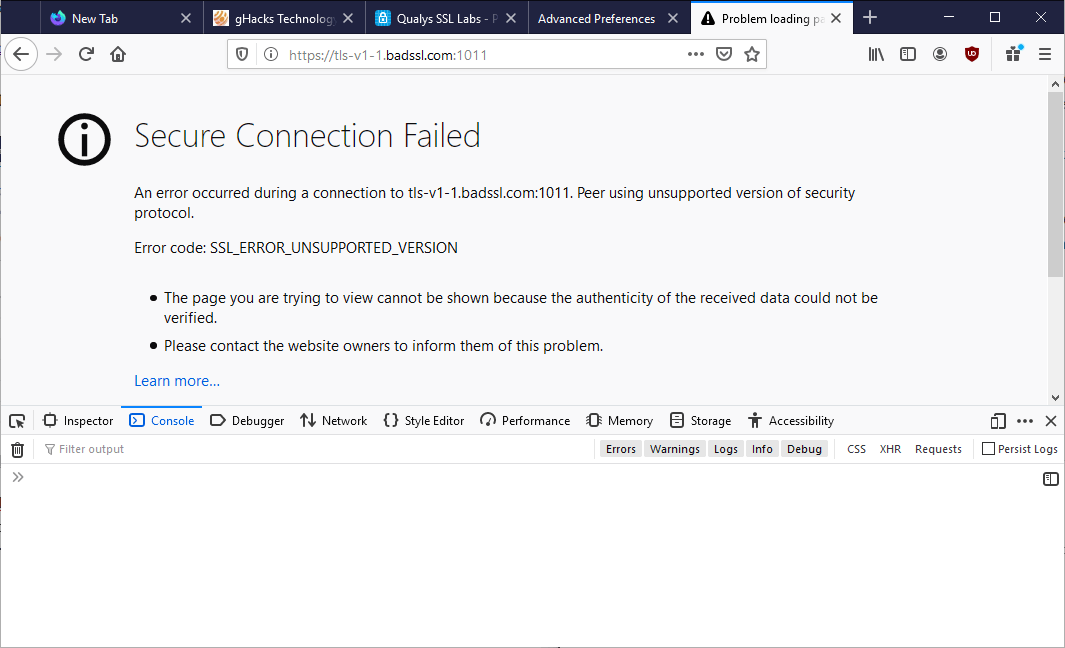
Mozilla disabled support for TLS 1.0 and TLS 1.1 in Firefox Nightly in preparation for the deprecation in Firefox Stable in 2020. A quick check on a SSL Labs test site confirms that TLS 1.2 and 1.3 are the only supported protocols by the browser.
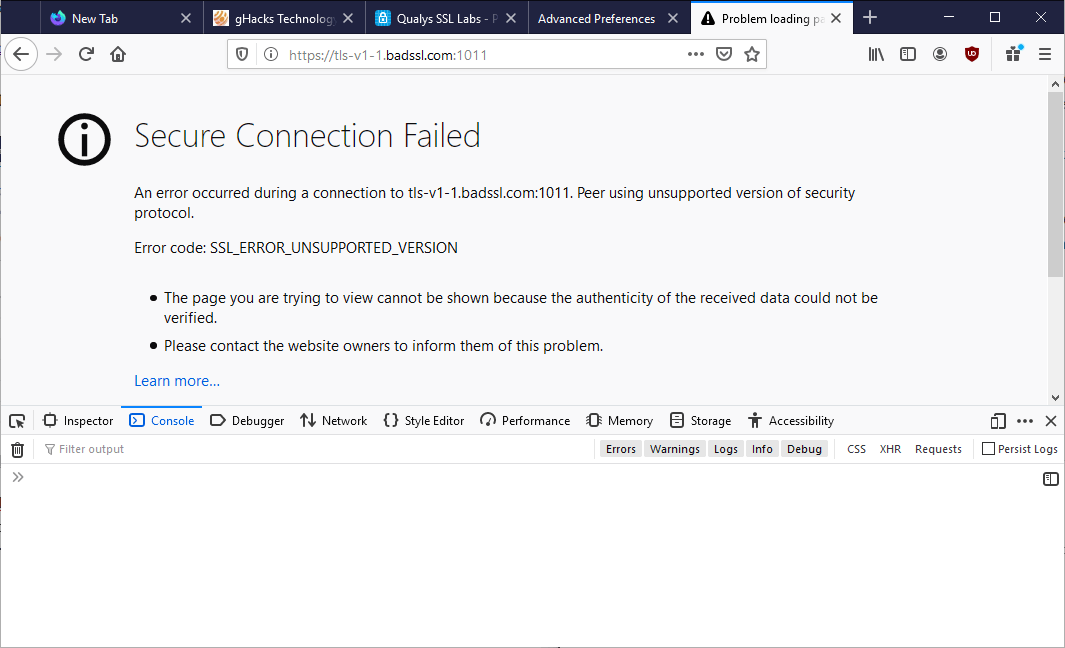
Sites that support TLS 1.0 and/or TLS 1.1 but not TLS 1.2 or newer will fail to load and throw a "secure connection failed" error instead. The error code is SSL_ERROR_UNSUPPORTED_VERSION.
Firefox users may override the limitation in the following way currently but that option will likely go away once the change lands in Firefox Stable in early 2020.
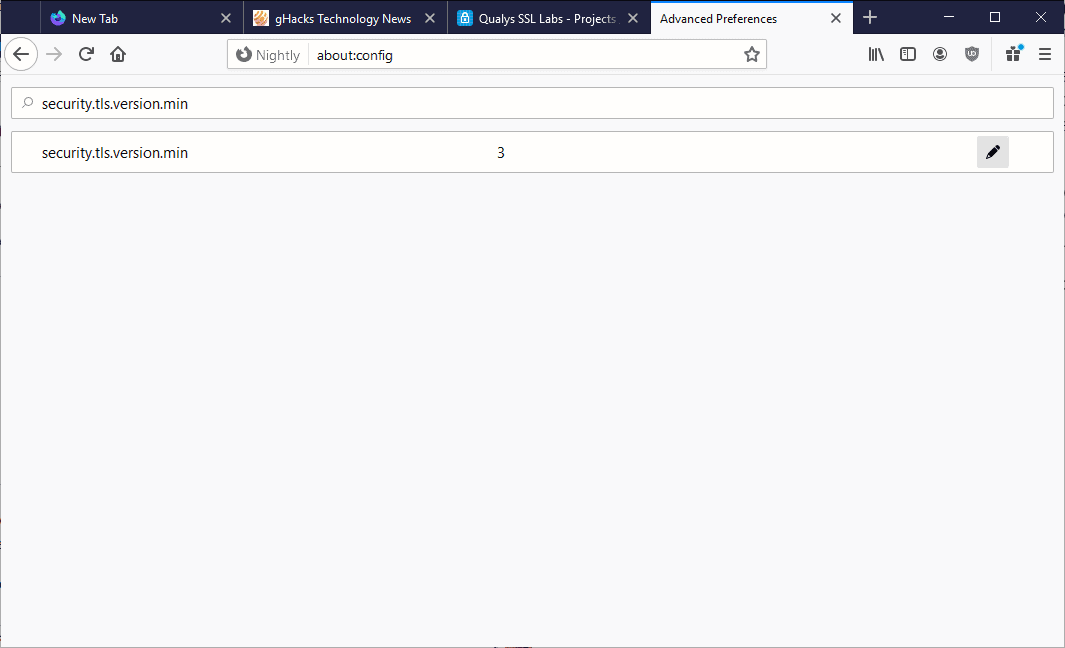
- Load about:config in the web browser's address bar.
- Confirm that you will be careful.
- Search for security.tls.version.min. The default value of the preference is set to 3 which means that Firefox accepts TLS 1.2 and higher only.
- Change the value to 2 to add support for TLS 1.1, or to 1 to add support for TLS 1.0.
The screenshot below shows the default value of the preference.
Sites, including the dashboard of modems, routers and other local peripheral devices, that support only TLS 1.1 or TLS 1.0 will load after you make the change.
Closing Words
TLS 1.0 and 1.1 support will be removed from browsers in early 2020. While that should mean minimal interruption for most users, some, especially those working in local Intranets and other non-Internet environments, may run into issues connecting to certain sites and devices that don't support newer protocol versions for one reason or another.
Some browsers may keep support for TLS 1.0 and 1.1 enabled, and it is also possible to use an older version of a browser to connect to these sites.
Now You: Are you affected by the change? (via Sören)





















I believe setting security.tls.version.enable-deprecated must be set to False, otherwise there is no check on the Min version!
I am unable to access internal corporate website within intranet using TLS1.0. Did enable the min security.tls.version.min to 1 for enabling TLS 1.0 and it still doesn’t allow gives Secure Connection Failed with “SSL_ERROR_UNSUPPORTED_VERSION”. Any suggestions what could be done to override default TLS support and enable older version ?
I am using 68.9.0esr (64-bit) (firefox quantom)
There’s an interesting Firefox extension which provides information regarding the visited site’s TLS :
‘IndicateTLS’ at https://addons.mozilla.org/en-US/firefox/addon/indicatetls/
Quoting the extension’s presentation on AMO :
“This Add-on uses the new SecurityInfo-API in Firefox to display information about the transport security used on the sites you visit.
The TLS protocol version is displayed by an icon in the address bar. More detailed information can be viewed by clicking on that icon, particularly to display the TLS protocol version of 3rd party servers that the website you are visiting fetches resources from.”
Works very well.
Thanks for that, Tom! That’s quite interesting. I didn’t now about it, but I’ve installed it now. I like being able to see the TLS version, and especially whether HSTS is being used. Thanks again!
@Hy, glad you enjoy it as well! ‘IndicateTLS’ is bound to improve, some have mentioned the pertinence of having it include info regarding PFS (Perfect Forward Secrecy) which indeed would be welcomed.
Anyway this add-on fits into the article’s wondering about sites still using TLS 1.0 or 1.1
Haven’t met any for some time, but I don’t surf that much. Maybe visiting some government sites as mentioned by Harro Glööckler (1st comment above which made me laugh!).
There is also CipherFox, which I have used and found to work well.
Its GitHub releases page does not have the current version:
https://github.com/gavinhungry/cipherfox
CipherFox was available on the Mozilla add-ons site, but appears to have been removed. It was avialable at:
https://addons.mozilla.org/en-US/firefox/addon/cipherfox/
DO you mean mozilla’s “secure connection” descriptor is not enough?
I think it pertinent to mention that there is also a maximum setting which is security.tls.version.max the default of which is 3. Just searching for the minimum setting will of course only show that which in the case of Waterfox 56.2.14 is 1.
Users should just enter “tls” (without quotes) in about:config te view the other settings.
the minimum version of tls for me is 1.
what does it mean?
do i face difficulty openning websites in the future or not?
should i change it to 2 or not?
i use firefox 52.3 forever which is the best for me!
@Zahra Ayat:
To explain a bit — when your browser establishes a connection with a webserver, it negotiates with that webserver to determine (among other things) the TLS parameters that will be used. The minimum version that you have set is informing the web server that you won’t accept a TLS version less than that.
If the webserver cannot support TLS versions equal to or higher than what you have set, then an HTTPS connection cannot be established. In theory, this could mean that you’d have to use HTTP for some websites. In practice, though, very nearly all websites support TLS 1.2.
I’d be rather surprised if setting it to 2 caused you any real difficulty.
I checked my current setting which is 1; I changed it to 2. Not using Nightly.
But I continue having the SSL Error page thrown at the screen.
My guess is I am using the Firefox Private Network Extension VPN, so whatever settings my browser has are basically overridden by the Cloudflare Warp settings?
The figure about .1% must be an erroneous figure because I have solid sites that I’ve gone to before throwing out the SSL Error message. In a sense, it’s made researching topics much more difficult.
“Back then [2018] it was revealed that TLS 1.1 was used by 0.1% of all Internet connections; the number has likely gone done in the meantime.”
Likely even less for TLS 1.0 so one may wonder why TLS 1.0 (at least!) is still supported now on Firefox 69 : security.tls.version.min is 1 (1=TLS 1.0, 2=TLS 1.1, 3=TLS 1.2, 4=TLS 1.3). Confusing?!
If I leave it at default it’s only because our Ghacks-user.js recommendations (https://github.com/ghacksuserjs/ghacks-user.js) state (Ghacks-user.js version 69-beta) :
/* 1202: control TLS versions with min and max
* 1=TLS 1.0, 2=TLS 1.1, 3=TLS 1.2, 4=TLS 1.3
* [WARNING] Leave these at default, otherwise you alter your TLS fingerprint.
* Firefox telemetry (April 2019) shows only 0.5% of TLS web traffic uses 1.0 or 1.1 ***/
// user_pref(“security.tls.version.min”, 3);
// user_pref(“security.tls.version.max”, 4);
Otherwise, considering 0.5%, I’d push the minimum to 3 (TLS 1.2) or at least to 2 (TLS 1.1).
Always the same problematic : if you set as a wise guy you get more quickly spotted.
Hence, Mozilla’s decision to disable TLS 1.0 and 1.1 is welcomed as far as I’m concerned : wise browser needs no wise guy being pointed. Wisdom for the people, viva la wisdom.
Damn, now half of all government sites will stop working…
Oh god, what a great comment..
:)