Windows 7 and Server 2008 R2 updates KB4480970 and KB4480960 causing network issues
Microsoft published the security updates KB4480960 and KB4480970 on yesterday's January 2019 Patch Day for the operating systems Windows 7 SP1 and Windows Server 2008 R2 SP1.
Reports are coming in that installation of these updates may introduce networking issues. More precisely: network shares are no longer accessible using SMBv2.
Update: Microsoft published KB4487345 and a standalone fix that customers may download from the Microsoft Update Catalog website to fix the issue.
The security updates, both the monthly security update and the security-only update, fix security issues in several components. Additionally, they include a new protection against Speculative Store Bypass for AMD-based computers, and disable the option to configure PowerShell remote endpoints to work with non-administrator accounts. Microsoft made the change to PowerShell remote endpoints in all supported versions of the Windows operating system.
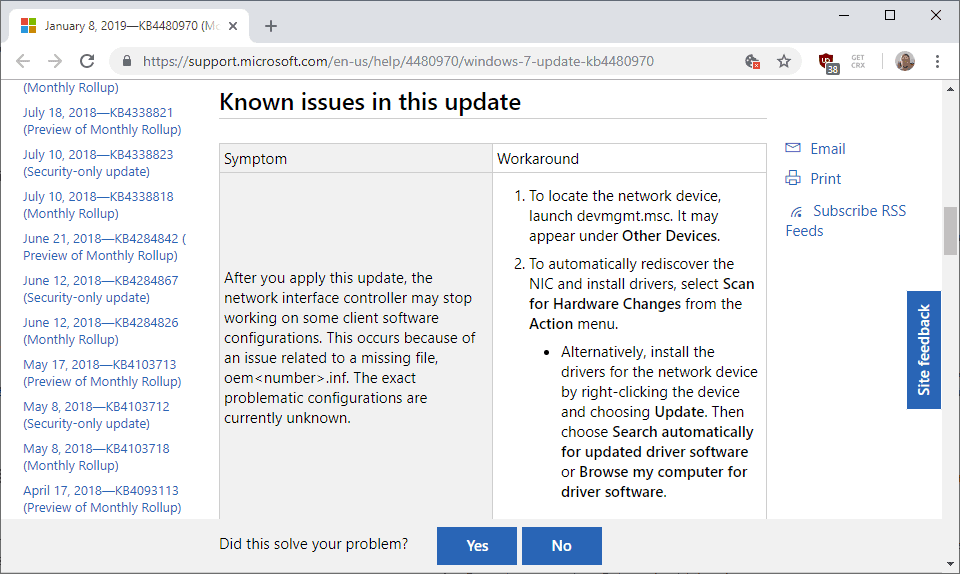
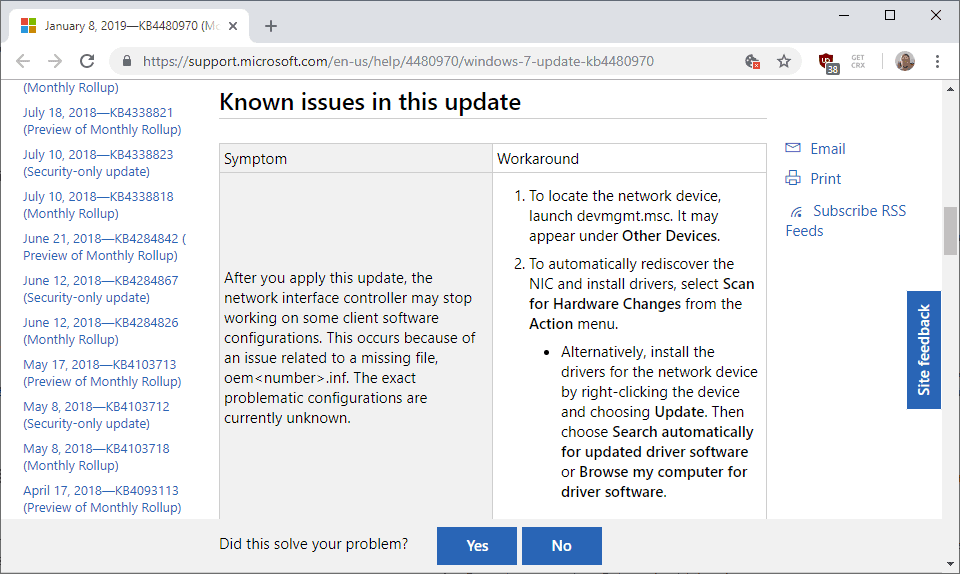
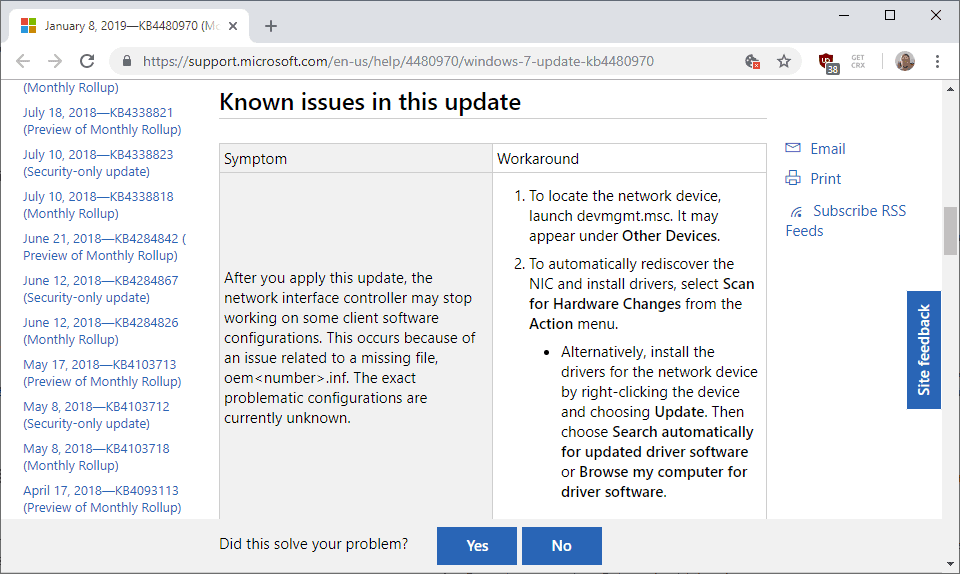
The only known issue listed on the update page for KB4480970 is the long-standing issue that network interface controllers may stop working. The workaround, also available for months, is to install drivers for affected devices.
Both KB4480960 and KB4480970 seem to cause issues with network shares under certain circumstances. Günter Born published a detailed account on his site about the issue.
Several administrators reported networking issues after installation of KB4480970 stating that shares could not be reached after the installation of the update.
An analysis of the issue was published on the German admin website Administrator.de. The analysis confirms the network share issue and that it is caused by the installation of KB4480960 or KB4480970.
The issue is triggered only if the user attempting to make the connection is an administrator on the machine that hosts the Share. If the user is "just" a user on the device that hosts the share, the connection should be fine.
A workaround has been published to address the issue. It modifies the Windows Registry and should be run on the system that hosts the share. Note that you need to run from an elevated command prompt.
- reg add HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\system /v LocalAccountTokenFilterPolicy /t REG_DWORD /d 1 /f
- Reboot the PC.
The Registry entry defines how administrator credentials are applied for remote access. A value of 1 sets the restrictions to Audit mode.
Removal of the updates resolve the issue as well but will remove the security patches on the target system that Microsoft released in January 2019.
Now You: Have you been affected by the issue?

















After an update ladt night, I awoke to find that I couldn’t use the internet. Windows complained about the DNS server, but I discovered that my local router page was not accessible either. Windows showed internet connection, so the wireless card was not disabled by the update. Uninstalling KB4480970 and restarting resolved my resolution problem.
Microcrash seems more interested in spying and telemetry than on security or even, for that matter, basic competence. Microcrash consistently lies about what it or it’s updates do in an effort to ensnare users in their endless pursuit of money. Maybe I’m headed back to Linux and a VM windows to await the awakening of the sheeple who are currently too occupied with Big Brother (ironically) and Game of Thrones (hoping to catch a glimpse of some bits and bobs).
I can only imagine the nightmare being lived by Win 10 users. At least I got to choose my update poison. Take your medicine my baaaashful little flock!
thanks ! it helps us a lot to re-instate network shares
After installing updates on 2 completely different windows 7 systems in 2 completely different networks, I am unable to access published remote applications / desktops from either windows 7 system – both are returning an error that the servers certificate is either expired or revoked – but I can launch the remote app/desktop from a windows 10 machine with no issue. Both of the effective systems worked just fine last week. I installing KB4487345 and it did not fix the issue. I tried removing KB4480970, still does not work. I am also seeing similar issues with other people on Windows 7, all of a sudden having certificate trust issues.
I am pretty certain that M$ is just effing with people to try to force them off Windows 7 – well, I will be happy to dump Windows 7 – but it will not be for another piece of crap M$ OS.
If your not sure how to download the official patch from Microsoft, check out this video which shows you how to do it step by step:
https://youtu.be/eMpkb-8ABok
hi Martin
this fix just came out from Microsoft – KB4487345
https://support.microsoft.com/en-us/help/4487345/update-for-windows-7-sp1-and-windows-server-2008-r2
anyone applied this update and lived to tell?
Yes I just applied it to a system and it works fine. KB4487345 does also fix the issue. For now one has to download that from the MS Windows catalog
This 10 January 2019 article at BLEEPINGCOMPUTER may prove useful for some, “Windows KB4480960 & KB4480970 Updates Causing Network and License Problems” —
https://www.bleepingcomputer.com/news/microsoft/windows-kb4480960-and-kb4480970-updates-causing-network-and-license-problems/
Just made the reg edit. Small business owner- asking my dad for a raise on this one! Thanks everyone!
Thank you so much! I just spent several hours last night trying to solve this. Your solution worked! Thanks again.
Several of my customers have encountered problems related to the KB4480970 update. I applied your registry patch and all is well.
Thank you very much for saving me hours of searching.
hello friend please can someone post here some *.bat file with fix problem or some ruller how fix this problem in register thx
Hello please very much i need info how fix register key. Please can someone write the procedure how fix this problem THX very much it is very important
All four of my 2008r2 servers ceased to function with network shares after this update, one even developed some weird account problem after the update. One with 7 still worked afterwards.
Thanks so much for this article, very much appreciated!
Microsoft seems to be speeding up releasing updates with no quality control. Have had numerous problems with W10 updates that required work to get clients going again. Support cost since switching from 7 to 10 is much higher, sad but true.
Hasn’t happened in our office, but 3 of my clients called with this problem, they could no longer scan using our equipment. Happened on 2 W7 machines and a Server 2008 machine. Forward this to them and suggested they get in touch with their IT support personnel. Thanks!
I have a small office (5 workstations) and just use a VERY simple shared folder setup. I have one case management program which acts as a “server”. Whatever update(s) microsoft pushed on 1/10/19 completely disabled network folder sharing.
I manually turned on:
Computer Browser (Browser)
Function Discovery Provider Host (FDPHost)
Function Discovery Resource Publication (FDResPub)
Network Connections (NetMan)
UPnP Device Host (UPnPHost)
Peer Name Resolution Protocol (PNRPSvc)
Peer Networking Grouping (P2PSvc)
Peer Networking Identity Manager (P2PIMSvc)
BUT NO LUCK. I had to do a system restore and disable automatic updates.
took me three hours to find out wtf is going on in my home office, this article saved the day
The picture at the top of this article shows a known issue that is not new to this KB, or related to the problem described. It is from spring 2018.
As the KB implies, removing the user account that is on the file server from the Administrators group (still on the file server) seems to have fixed this.
I fought with this issue for several hours yesterday and this article saved my butt!
FYI, the updates were listed under the update history, but not under uninstall updates… I used system restore to the day previous to the install and was able to fix the issue last night. However when I came in this morning they had automatically reinstalled.
Just applied the registry fix and that appears to be a permanent solution…until Microsoft breaks it again.
Huge thank you!
Yes the BUG shut down our entire network. Thanks for the info
still sitting pretty on 8.1 here, feel free to join.
so this bug prevents connection to shares. like RDP or only network shares?
i’m thinking if this was applied to VM servers like hyper-v and the only way to connect to those VM is via RDP, it means people need to rollback their image of the VM?
Very good solution, it helps me a lot. Thanks so much !
Like I said before, M$ has likely weaponized Windows Update to force about 800 million Win 7 users in the world to upgrade to Win 10 asap so that M$ can make more money asap. Hence, the many buggy and unfixed security updates in the monthly Rollups for Win 7.
Windows Update is now like malware, ransomware, spyware, adware, bloatware, etc. M$ or $atya Nadella is not your friend.
One more victim of Microsoft’s half baked “Security Only” patches. On my Windows 7 PC, I lost functionality of my network shares and the ability to use Remote Desktop Connection to remote into the unit. Hopefully this registry hack you’ve published covers all the NIC bases.
Microsoft needs to get its act together… or maybe dump Nadella.
Another victim of Microsoft’s half baked “Security Only” patches. On my Windows 7 x64 PC, I lost functionality of my network shares and also the ability to use Remote Desktop Connection to remote into the unit. Hopefully this registry hack you’ve published covers all the NIC bases.
Thanks Martin, you just saved us a lot of head scratching. :)
Registry fix worked perfectly for me. Thank you for posting this solution so quickly!
Anothar reason for use Windows 10!!!
I have a client network with Windows 7 WS and a 2008R2 Server….One machine came up with the Invalid Handle error when connecting to the share on the 2008R2 Server.
I worked on it all day before this post was on the web several days after.
I thought maybe it was a corrupt hard disk or a Windows 7 issue so I installed Windows 10 on the WS.
Same issue on Windows 10 “Invalid Handle” and I still could not connect to the share.
So its not just a Windows 7 issue
No Windows 7 to old Windows 10 new bettar. Windows 7 lose suport soon 10 will life longer less bugs more update every month.
Pretty ignorant comments to say the least.
Windows 7 in right hands is more secure and private than windows 10. Till today.
In best scenario Microsoft will need two or three years more to make win 10 stable.
Currently it is incoherent piece of crap.
These updates are targeted to push users from stable Windows 7/2008R2 to Windows 10.
Then want more beta testers.
Are you kidding? In Windows 10 bugs are distributed more frequently :-O
this broke our shared connections on all of our machines. uninstalling last nights updates fixed the issue. I had installed a new printed and subsequent drivers yesterday before leaving work and it seemed like it was all working correctly when i left. Came in to all these issues this morning and assumed it was the new printer drivers so i have spent my entire day removing and then after I found the that uninstalling the last Windows updates fixed it i found this site… wasted my entire day! Thanks again Microsuck…
Are you going to sue Microsoft for damages and lost hours of work ?
You should.
same problem expect is it on both windows 7 and 10
I had the problem this morning on a 2008 server running shares, gave me invalid handle error after entering credentials. The administrator account however would work fine, just other accounts that had admin privileges did not work. The work around fix the problem.
My AMD discreet graphics card (HD 7450) driver no longer loads after this update.
can someone help this small business owner uninstall this MS update?? I’m dead in the water.
Hi, check out this guide: https://www.ghacks.net/2014/08/18/how-to-uninstall-windows-updates/
Thank you for the note.
For us, KB4480970 started causing this issue. This particular client has a simple setup, no domain, just file sharing from a Server 2008 R2. We removed the update before reading this post and everything went back to normal, but we will keep in mind the workaround for future reference.
Yep, had issue where scanners were no longer seeing the shared folders. Adding the registry key fixed it. thank you.
I just re-installed Windows 7 Ultimate x64 on one of my computer with an ISO with integrated updates until May 2017. That is where i will stay as well, no further updates. It works with almost no bugs (not more than those introduced in SP1).
Microsoft has become crap to be honest….
Hi Stefann,
Where did you find a Windows 7 ISO with integrated updates until May 2017?
Many thanks, Bob.
@Bob Hill: From a friend that probably downloaded it via torrent (safe source).
An update released by Microsoft is causing problems? There should be zero surprised users at this point.
Surprise is when Microsoft updates doesn’t cause any problems.
Ah Microsoft and their broken updates…what else is new?
I also experienced that my W7 machine with shares was not accessable after patching. Adding the registry entry fixed it.
Just another attempt to force you on to windows 10 and onedrive. Your network is ours!
Dave: You get an imaginary up-vote from me. MS doesn’t care. as they arrogantly believe that they own the corporate future. My crystal ball tells me that future may be short lived, if the current crud they’re been releasing continues.
@seeprime I honestly believe they are doing it all on purpose.
When M$ took notice of how much money google was making from data collection they started to change thier business model.
Amazon, FB, google, they are all making as much or more profit but none have the financial burden of supporting the #1 OS on the planet.
M$ needs to change windows into a data collection tool to survive along side the other sharks currently in the waters and they are in a prime postion to do so.
You must go through windows to open a browser or app to start sending data to google and others so M$ basically has “1st dibs” on your personal data. There no reason they wouldn’t manipulate all windows users into providing them with as much data as possible.
Anyone who doesn’t realize the reasoning behind giving away windows 10 for free needs to look for the box that pc came in ;)
This update broke network shares between my computers. Tired of Microsoft BS. Why wasn’t this update tested before release?
Another monthly/sec patch that may get pulled … and since there is a provided workaround, may never get fixed. This has become business as usual for Microsoft. The new normal.
Ignoring the underlying issue and pulling patches is now their ‘new normal’.
e.g. Microsoft has seen more patch recalls in the past two years than in the past decade.
Sigh… workstation os, lowering the bar of quality, chose one.
Martin
no issues this morning with KB4480960 nor ..970. SMBv2 working ok in my farm.
Shares ok. North American Windows 7 / 2008. Dell racks.
John
Thank you for the report. Do you use a user or admin account to access the shares?
“Oops.” Me did type far too soon; apologies. User account reports issue. darn.