Most Internet users still prefer weak passwords over secure ones
If you are a reader of this blog you know that it is essential to use unique and strong passwords for any online or offline service that you use.
Most use a password manager for that; either one that integrates in the browser and stores data in the cloud, e.g. LastPass or 1Password, a hybrid like Bitwarden, or a local password manager like KeePass that stores data locally and may also be integrated in browsers.
Most Internet users, however, seem to follow their own guidelines when it comes to selecting passwords for services; that's the impression that you get when you look at the top 100 worst passwords of 2018, and compare these to previous years.
Still at the top are insecure passwords such as 123456, password, or 123456789. Here is the entire top 10 list of weak passwords and the top list change compared to last year's listing.
- 123456 Unchanged
- password Unchanged
- 123456789 Up 3
- 12345678 Down 1
- 12345 Unchanged
- 111111 New
- 1234567 Up 1
- sunshine New
- qwerty Down 5
- iloveyou Unchanged
The number one password, 123456, has been the most widely used weak password in the past five years according to SplashData, and most passwords in the top 10 have been there for at least a year.
Why do Internet users select these weak passwords when they sign up for services? It is a mix of selecting a password that is easy to remember (comfortable) and, despite all the leak horror stories of the past, indifference and, in some cases, ignorance.
Companies could do more to prevent the use of known weak passwords but many Internet companies avoid complex passwords rules as they may discourage users.
Methodology
SplashData analyzes leaked password databases and the passwords they contain to determine which passwords are used most often by Internet users. The result is a snapshot of password selecting habits of Internet users; it is not complete or 100%, and that is without doubt the main criticism that the report faces.
The services the leaked passwords came from may also influence the results; people may select secure passwords on tech-focused sites and less secure ones on sites that have nothing to do with tech.
The leak sources and the age of passwords are not mentioned either.
Suggestions
SplashData published three suggestions to "be safer from hackers online":
- Use at least 12 characters with mixed types of characters, e.g. upper and lower case letters, numbers, and special characters.
- Use unique passwords.
- Use a password manager.
You may also want to consider enabling two-factor authentication for important services to add another layer of protection to the account.




















Say goodbye to weak password – use https://randompasswordgenerator.org/ + excel
Two pass authentications has been hacked and bypassed recently !
It was two weeks ago i demanded my email provider removed that feature from the their site because it wasn’t safe….how right was i ?
@ stefann
“Two pass authentications has been hacked and bypassed recently !”
No, it hasn’t. This is a cheap exaggeration for media types who seek clickbait. And it’s not “recent”. See here :
https://www.schneier.com/blog/archives/2018/12/real-time_attac.html
First of all, this latest piece of news is a targeted attack by Iranian spies. Do your Ghacks comments interest the Iranian government ? I doubt it.
Second, 2FA has not been “hacked”, because it has never been meant to protect against an attack like this. This “hack” has been done through spear-fishing. App-based 2FA specifically does not protect against spear-fishing. You need 2FA based on a hardware USB key for this.
No security measure provides complete protection against all attacks. 2FA provides added protection, but you still need to think before you act. It also introduces new risks and added complexity, inasmuch you need to carefully backup your 2FA secrets, and plan ahead for phone theft, for instance. It can also lower your attention. Here is a good explanation of what you have to expect if you choose to use 2FA :
https://medium.com/@stuartschechter/before-you-turn-on-two-factor-authentication-27148cc5b9a1
In most cases, 2FA will be better than no 2FA, but it’s still not a magic wand.
Also, it’s silly to “demand your email provider removes that feature from their site”. The fact that the feature is available at all does not lower your security. You don’t need to use it. And even if you did (some banks will force you to, and for good reasons), you need to understand the limitations and implications of the method.
Online life is more complex than offline, that’s for sure.
I’m retired now , but I used to work in I T. I have reasonably secure passwords for paypal , amazon and my domain but for everything else I use the same one short password with enough capital letters and symbols to meet the requirements of those websites. It is highly unlikely that some kid is going to change the details on my profile on any of my hobby and interest websites, and almost impossible to imagine that it could happen to two websites.
It is annoying that some websites don’t let you use special characters or only a few.
That trick mentioned above by Ron seems useful.
Why do your passwords need to be so complicated to prevent brute force attacks?
Most websites lock your account after so many failed login attempts.
Strong passwords won’t protect you from phishing attacks.
Strong passwords won’t protect you from malware and keyloggers.
Strong passwords won’t protect you from a hacker having your account password reset.
Strong passwords might help against hashed passwords stolen from websites.
I’m not saying you should use weak, obvious passwords like 123456, it’s just that I don’t want to use a 27 character long password.
Make sure to never reuse a password, and try to use a different username on each website if that is possible (some use your email address).
Here is an article from 2012 explaining the weakness of passwords https://www.wired.com/2012/11/ff-mat-honan-password-hacker/
Are those service accounts using weak passwords created by humans or bots?
For 5 years I use LastPass and I’m satisfied, really a great safe with passwords
Always like using some Nirsoft tools:
http://www.nirsoft.net/password_recovery_tools.html
Of course, some person said once, “I probably wouldnt [sic] post here if I had to sign up.”
Hmmm . . . I think there is a data storage consent form that needed to be checked. Merely coming to the site reveals one’s IP address–VPN or otherwise–along with other goodies such as the type of browser being used, etc. No privacy as soon as one goes online regardless of password use or non-use.
With the the “deviously” daring ‘Root,’ password given to the world, it is fortunate that nothing done online is either “risky” or “important” for some visitors to Ghacks–a point that brings makes Thoreau stutter as his mind echoes “For living is so dear.”
“Our lives are so precious. Not just ‘life’ but every single day and minute and moment,” yet some people prefer to avoid risk and do those things that are unimportant so that “when it comes to die, the great discovery is made, but I have not lived.”
What an existential dilemma for the holiday season. A crisis, perhaps!
Ennui?
“The White Rose.” Now there’s a classic German movie that shows that risk and doing that which is important changes the world and lives.
BleepingComputer did a similar article 2 days ago…
https://www.bleepingcomputer.com/news/security/123456-is-the-most-used-password-for-the-5th-year-in-a-row/
This all seems a bit moot to me.
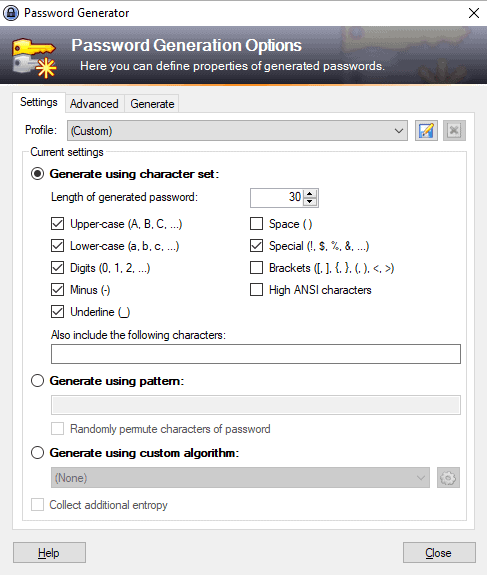
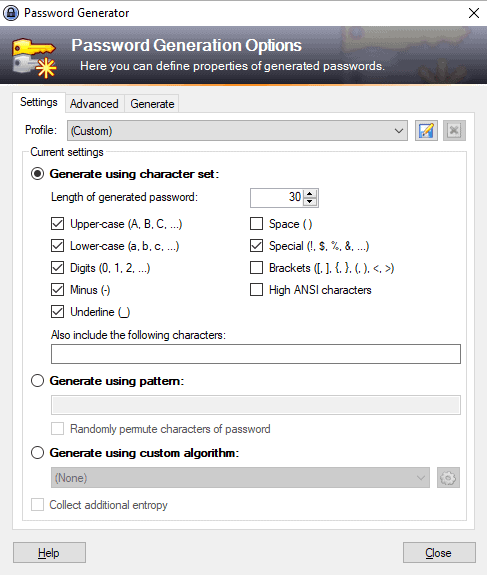
I use Keepass 2.x on all my devices. Within Keepass I have more than 225 entries, each with unique passwords that are as long and complex as the specific websites allow. With Keepass, I don’t have to remember or type any of them! I only need the master password for opening the password file. That password is long, has 94 bits of entropy, yet is easy for me to remember and quick to type in.
The master Keepass file is kept in Dropbox and each of my devices are set up to point to that Dropbox file. This works great as I never have to worry about syncing. I back up the Keepass file regularly to an external drive as an added measure.
And I never use someone else’s device or a public computer to sign in to any of my accounts – even though it’s possible to set up a portable way to do so if I wished.
I think using a few numbers and phrases from something unique to yourself (hobby, occupation, etc.) would be the best. ex. civil war buff…use some obscure dates and terms known only to yourself and such people
Let’s be realistic here, and admit that the online world is getting more and more intractable by the day for the larger public.
“We” have trouble getting to terms with it (I take this word to mean the generally very technically aware people commenting here), so just imagine how hard it may be for normal people, who are nevertheless compelled, by fact or even by law, to conduct their lives over the Internet.
Realise also that many, many big mainstream sites people need to use (banking sites, government sites…) have horrible password and security policies. Realise most of them prioritise ease of use over security any day.
A huuuge number of people can’t even get a percentage right, or give the correct answer to a question such as : you deposit 100 euros in a bank account providing 2% interest, how much money will you have one year from now ? And you expect them to have sound security practices that only professional spies get right — if that ?
Remember the director of the CIA who got his email account hacked, through some stupid mistake of his. The friggin’ director of the CIA !
Couldn’t websites defeat brute force attempts by limiting the rate at which log-in attempts could be made?
They could easily, but then they would have to put in extra effort (a few seconds).
The same thing is true with spam emails.
Ha! I just tried to post this and I got a message saying I’m posting too fast (I haven’t posted anything today).
Yes, brute force is most efficient when done locally, e.g. after someone hacked a service and dumped the password database.
it’s my party. I can cry if i want to…
Password managers are good for convenience but I can’t see how a browser plug in allowed to access the items they can including syncing across devices can give fewer potential attack vectors. A local manager seems far better.
For those uninterested in not using autocomplete, not storing anything but the minimum info on sites, saving pwds in a local encrypted file, using burner emails on sites that demand an account for purchases, not keeping credit card numbers online, changing pwds periodically, etc., could be benefited.
Years ago a friend had me sign into their facebook account. Their password was “facebook.” Oh, the good ol’ days! LOL!
I’ve been known to use phrases like “6h4cks.n3t” and “g006le m41l” as passwords. to help me remember them, but decided that they might just be too easy to figure out. Now, I just randomly plop something down and save all my login crap to a text file, which is zipped and encrypted. If a site tries to force me to register, to take part, I just close the site. Even the BBC tries to force registrations, now, for some things (iplayer).
Their loss, not mine. :)
Might as well use Keepass to generate random passwords and save them encrypted in a file that you can store safely in the cloud or share with other devices in some other way. Keepass is by the way the program from the screenshot in the article, very easy and convenient.
Also please note that password protected zip files and encrypted files are not the same. There’s not much difference for the average user but still not the same; if you are sharing something over the internet or store in the cloud always go for encrypted files.
Check out Cryptomator to encrypt files in a very easy way locally in your computer.
https://cryptomator.org/
Not only that… I have only one password with only 8 letters that I use excessively.
For few things that I truly need strong password I use one with 14 letters of all kind, plus numbers, plus strange characters. For Steam and Origin.
I never use the PC to pay for anything. Usually I pay with the item I ordered come to my door. I take the advantage of Web Offers plus without using the PC to pay. For me that is more than OK. They can steal whatever they want. I’ll just format and re-install.
Case in point, I just got the new Samsung SSD 860 1GB ( Web Offer ) and I only paid plus 3 euros for the “pay on delivery”. My other 2 SSDs are Samsung 850. I don’t use magnetic disk nor will I ever use ’em again anyway. Did the clean install, too and without the post, it only take me 4 seconds to boot ( the last few 3,8 wrote ). And the Post can set it to 1 second anyway.
Paying with a credit card(via the PC or otherwise) is zero risk to the card holder. Fraudulent use of the card by anyone other than the card holder, absolves the card holder of any liability. Simply report any such use within the time limit listing on the terms of the CC agreement( IIRC 60 days).
Definitely NOT zero risk. It’s quite a pain to deal with the credit card company. I lose my credit card for at least two weeks waiting for a replacement. I need to reset automated payments.
Still better to use a credit card than “pay on delivery” – IN THE US.
I subscribe with my ISP for Internet, TV, and Phone. Yesterday someone who obfuscated their caller ID called me over 20 times in one hour as they tested their automated scam. The ISP says they have no way to blacklist a caller like this. They said it is a political problem to solve this illegal activity. Good passwords are not the only Internet problem to solve these days.
I have passwords with upper case, lower case and numbers like 902Fatman628 or something similar. So far I’ve never had accounts stolen.
I prefer this method: pick four randoms things, and separate them with dashes or slashes. Found out about it here:
https://sites.google.com/site/easylinuxtipsproject/password
Problem is that many sites have these weird restrictions – and maximum password length is the most problematic.
You are right. What’s more annoying is that sometimes they won’t even warn you, let alone give exact info on the supported password format.
They might even accept your new password, only for the users to discover later that they cannot log in for reasons seemingly unknown.
@Ron: Crackers have adapted to the XKCD method, and that method is no longer better than using shorter random passwords that can include punctuation and numbers. However, it is still far superior to what people usually do!
Very interesting, definitely worth switching passwords following this method. I was just playing around with this and the other website that @tony church mentioned, and I was thinking: How well would these passwords to against quantum computers? Any ideas?
Very interesting! I checked a few random variations using this method and every single online password strength checker verifies it as being not only safe but would take literally trillions of years to crack.
Thanks for the excellent information and link.
The “reason” is right there in the #1 Suggestion” which is not only wrong it also promotes ignorance.
Password strength is a math function. Simply put, the longer it is, the stronger it is. Add 1 charcter and you increase it’s strength by a factor of 10.
If all these so called expert would stop incorrectly telling people to use passwords that are impossible to remember and instead to use “passphrases” that are both long and easy to remember, this problem would eventually become rare instead of the norm.
“14dirtyBIRDS!flewinthewater” is a much stronger password then “0u9.[N25&?z!” and it’s super easy to remember.
As long as the “experts” continue to teach ignorance, that’s what we’ll have.
Lengthy passphrases are better than a shorter password, true. But if the hacker suspects a passpharse it reduces the likely character space to a much more limited number of characters. Long enough, it probably is not worth effort to try to crack. If not long enough, it is easier to crack as most of the passphrase will be words in a known language. A random password is always stronger than a passphrase of the same length as you have to assume any character on the keyboard could be used anywhere.
What is overlooked with advice of using longer, complex, unique passwords is to make your passwords not worth the effort to crack in a reasonable period of time for the information to be possibly useful. If the password is long enough you will have several years before a hacker is likely to crack them, by that time it is likely you have changed the password anyway. Also using unique passwords means even if one got the password for a site in plain text it is only useful on that site. So at worst the hacker might know some details about you but cannot use the password to login to your bank.
12 characters minimum if the website allows you to use all types, numbers letters upper and lower case plus special characters.
But if the website doesn’t allow special characters then the minimum should be 16.
You should also have a look at GRC.com Password Haystacks.
https://www.grc.com/haystack.htm
Obviously his website doesn’t take dictionary attacks in to account, but it gives you some idea as to how long it could take to crack a password.
Haha I Love it!
https://www.grc.com/haystack.htm
ILikeBigButtsAndICannotLie
1.34 billion trillion centuries…isnt that a Quintillion?
Ill bet in 50 years it could be cracked by 12year old in 5 minutes
@supergirl: 50 years is a very long time in computer terms. Computers as we know them today will in all likelihood not exist anymore, and passwords may also have become obsolescent having had to give way to something more secure, maybe even uncrackable.
So that future 12-year old kid may well not be interested in cracking your password.
>> “Why do Internet users select these weak passwords…?”
well… because nothing really important is being protected on masses of casual web accounts.
Most people are more careful with important financial accounts, but this vague “insecure password” estimate lumps all types of web activity together.
the huge internet data hacks that happen constantly … happen at the business server end — not at the user end by some average person with an insecure password. User passwords are NOT the big web security problem.
Consider that the front door on your home probably can be kicked open by any health adult male — why don’t you make the small effort to install quality door locks ??
Why are you so careless with the security of your family and property?
@dennis: “Most people are more careful with important financial accounts”
The data that I’ve seen indicates that this is not nearly as true as we would hope. Do you have different data?
It’s interesting to see how today’s recommendation is to use at least 12 characters, when a few years back was at least 8. Obviously the more characters the harder it it to guess, but is there some kind of ‘brute force’ or other technology of some sort that is catching up? Will we be looking at “at least 20 characters” password recommendations 10 years from now?
Yes, processing power improves which means that brute force attempts per second improve as well.
That’s a thing I don’t understand. Why is it possible to brute force attack a site / service in the first place? They must use timeouts. Say, at least 30 seconds per try, then it’s almost impossible.
@Steve:
“Why is it possible to brute force attack a site / service in the first place? They must use timeouts.”
They usually do, but that’s not actually as great of a defense as it used to be. It’s cheap and easy to leverage cloud providers so that multiple endpoints balance the load of brute forcing, so the timeouts don’t really affect you anymore.
Also, it’s quite common that the brute-forcing is done after obtaining a list of users and hashed passwords some other way. Then you can do it entirely offline without touching the system you’re attacking until you have a valid password.
Thirdly, if users are choosing bad passwords, brute-forcing can be surprisingly quick to do. The use of rainbow tables, etc., can reduce the search space considerably. Extending the minimum required length of passwords helps to mitigate this a little (not enough, but you take what you can get).
I notice that at number 20 in the list on that site the p/w comprises of 9 special characters, 7 of which are in consecutive order together with 3 alphabetical characters (amp) which aren’t consecutive, but only in lower case. It does add up to a total of 12 characters though.
Odd how so many users think alike when it comes to creating a password.
& a m p ; is & in HTML, maybe that is what is meant, not sure.
I dont use sync for my browsers…..
If I want to pass info from comp to comp I email it,
Or put it on a USB.
I preferred the web when you didnt have to login to do anything.
I dont use sites that you have to create an account to enter.
As the USA & Israel shall some day learn…”Security” isnt making us any safer.
Its an illusion. I Trust no password manager.
If I put one on my computer it would like a honeypot.
All faked passwords & logins.Let them THINK they got something.
So all those high security tech “experts” are maybe just missing the point,no?
Only this year I started using KeePass. I would never give away my passwords to something like LostPass just because they claim to be responsible with them. And never suggest to anyone doing so. Still, even before that I was using passwords generated “randomly”. It has been the case for many years.
That being said, right now I store all my passwords in plain sight. They’re only on my desktop though, which is my only trusted device, unlike my phone which while it is using full disk encryption I don’t trust it with sensitive data, or my laptop which anyone could potentially nick away.
I do hate it when websites try to be protective and tell my my password, which looks like “8b5ec0aafdc303e13eb4c64b67bc0ec7be748071b01c07222f2d105478d1ba28” is “not safe enough because it does not contain any special characters or mixed caps”. I hate this, developers should stop enforcing this nonsense.
Please do an article on LessPass.
https://lesspass.com
First time I’ve heard about it, but 5 minutes on Google suggests that it may not be all that great of a solution to the password problem.
@foolishgrunt, I think you are referring to this: https://github.com/lesspass/lesspass/issues/88
This was 2 years ago, and it was fixed in less than 10 days. It’s good to see how developers acknowledge their mistakes and learn from them, although just in case I’d still use offline password managers for important stuff.
+1 to the article on LessPass, Martin!
Good idea, but what happens if the website or extensions disappear? What is the algorithm, how can you regenerate your passwords in such a case?
I probably wouldnt post here if I had to sign up.
Another fave site of mine is earthsky.org It uses disqus to handle commments
Its a shame …Often I would like to converse.
I value my privacy ALOT more than any passworded security.<<<>>>>>
My Longest most devious Password is to Root on my computer.
I created my email accounts in 1997-99 time frame most have 5-7 letter logins.
Odd ones but short ones. I have never changed them.
I use weak passwords because nothing I do on-line is risky for me.
Or truly important.
If I want to use a credit card….I have family do it.
Most have Cash tied up in pay-pal & are glad to have my real cash-money in hand.
2 two-factor authentication is a REALLY Bad idea to me.
if enforced everywhere I would stop going on-line.
@Supergirl: you are obviously in the lucky position that you live near you bank so you can go there in person. Not everyone is in that position.
I don’t like to use my credit card on line either, so I avoid it at all costs. Nevertheless, sometimes one cannot avoid it. You’re lucky there too, with family to handle it for you. Not everyone has that ;-)
@Klaas Vaak: “I don’t like to use my credit card on line either, so I avoid it at all costs. Nevertheless, sometimes one cannot avoid it.”
I recommend using one-time-use prepaid temporary cards to do this. Most card companies have such an option, but you can also pick up prepaid cards at many supermarkets that can serve the role (they aren’t one-time use, but you don’t have to reload them).
@ John Fenderson
That’s an area where advice should come with information about the country, or maybe continent, where it is applicable. Europe is at a distinct disadvantage from the United States in two notable fields, as far as online privacy and anonymity is concerned : credit cards, and mobile phones.
Virtual credit card numbers provided by non-banks, top-up debit cards available in retail, disposable phone numbers or burn phones are unavailable in Europe, because the law somehow makes sure that it stays that way.
Some banks do provide one-time use credit card numbers, which is good from a security point of view, but ineffectual if you’re after privacy, since they are linked to your main credit card, and therefore to your identity.
As to not using one’s credit card online at all, this strikes me as tinfoil hat-level, unless you’re Oussama Ben Laden. If you’re concerned about financial security, as far as I know, in America you can revert any credit card charge you don’t agree with, and in Europe, again to the best of my knowledge (that’s certainly the case in my country), your bank, by law, has to credit back any fraudulent expenditure you didn’t authorise yourself. You just have to ask, and they just need to do it.
So even one-time virtual credit card numbers (which I happen to use) are really belt + suspenders. They will save you the trouble of laying a claim with your bank and waiting for the funds to come back.
Now if you don’t want the electricity company to know who you are and where you live when paying your bills… except they already know that… If you don’t want Amazon to know that it’s Mister John Smith who bought the best-seller “I really, really don’t like my government”… except they need to ship it to you…
@Clairvaux: “That’s an area where advice should come with information about the country”
You’re absolutely right. I try to be more careful about this, but I messed up this time. I’m speaking about the US. Other nations may differ.
@Clairvaux: you stated
“… in Europe, again to the best of my knowledge (that’s certainly the case in my country), your bank, by law, has to credit back any fraudulent expenditure you didn’t authorise yourself. You just have to ask, and they just need to do it.”
That is true, but I don’t feel like having to enter into that discussion with my bank, which can drag on with no indication as to when you get your money back. Esp. if you used your card online they could argue you were not careful, bla bla bla. No thanks.
Incidentally, in which way do you obtain one-time virtual credit card numbers?
@ Klaas
My bank offers this service as an extension to my Visa card (also provided by my bank).
In exchange for a small annual fee, each time I want to pay for something online, I can launch a program, or connect to a specific Visa site, type my user name + password, type the 2FA supplementary code given to me by voice message over my land line, type the amount required, and the app generates a one-time use credit card number + CCV code + expiration date, which I then type into the e-merchant or service provider payment page, exactly as if it came from a plastic Visa card.
I don’t think I ever met a website which rejected this type of payment, provided they accept Visa. If you return the product, the money is credited back to your regular Visa account, to which your virtual Visa card is linked. You can also set recurring payments for subscriptions. The amount you authorised has some leeway automatically factored in, to allow for unexpected shipping or customs charges, etc.
This might, or might not be available in your country.
@Clairvaux: interesting, thanks for that. I’ll see what my bank can offer.
@John Fenderson: thanks for the tip John. I had heard of them but somehow never gave them much thought. I’ll definitely check it out because a few times now I have had to abandon a purchase or a donation because of this. Thanks again :-))
I love KeePass, been using it for 10 years. Nevertheless, the Linux version does not perform as well, and needs Mono (.NET emulator) to run, and then it is still iffy. KeepassXC is a potential alternative.