Google's bad track record of malicious Chrome extensions continues
A report by security company Radware suggests that Google Chrome users were exposed to yet another wave of malicious extensions offered to them on the official Chrome Web Store.
The extensions were used to perform "credential theft, cryptoming, click fraud, and more" according to Radware.
The company detected the family of new malware for Google Chrome with the help of machine-learning algorithms which it ran on a customer's computer network.
Security firm ICEBRG identified another set of malicious Chrome extensions earlier this year, and 2018 was also the year that extensions with Session Replay functionality appeared in the Store.
Another wave of malicious Chrome extensions detected
According to Radware's analysis, the malware has been active since at least March 2018. It infected more than 100,000 user devices in over 100 countries, and pushed at least seven different Chrome extensions with malicious content using the following attack vector:
- The attackers use Facebook advertisement to reach potential victims.
- Users are redirected to fake YouTube pages.
- A prompt is displayed asking them to install a Chrome extension to play the video.
- The click on "add extension" installs the extension and makes the user part of the botnet.
- The malicious JavaScript is executed on installation which downloads additional code from a command center.
The extensions that the attackers used were copies of popular Chrome extensions with malicious, obfuscated code, added to them.
Radware identified the following extensions:
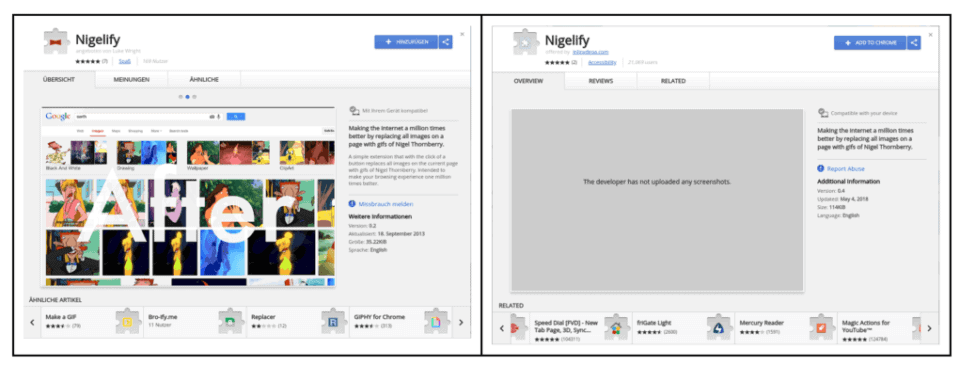
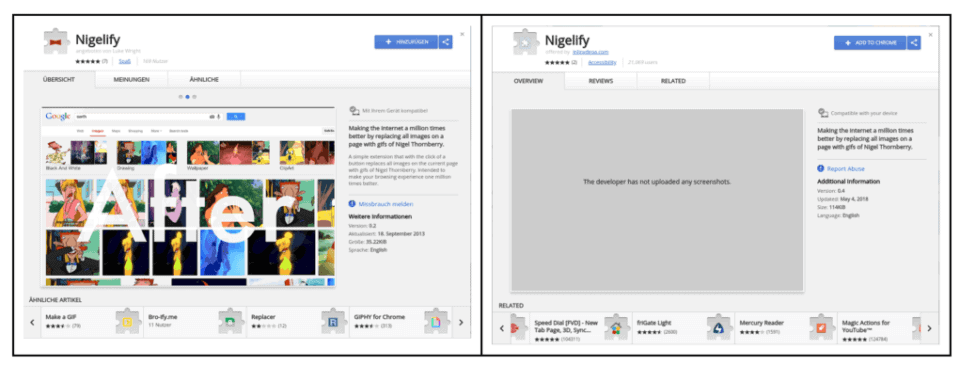
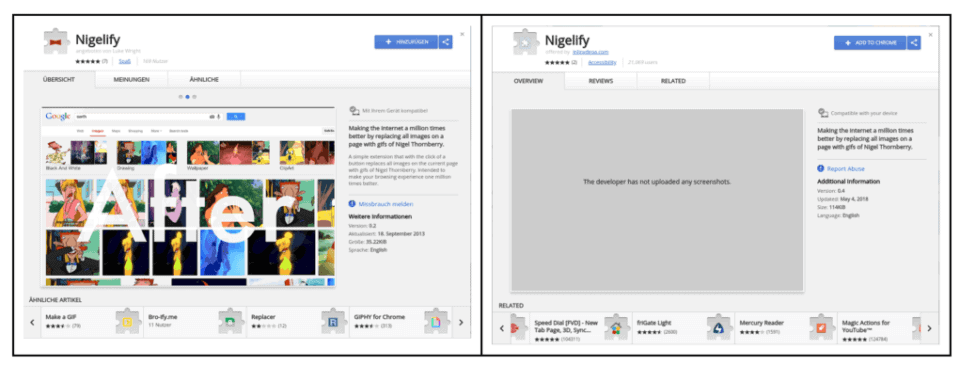
- Nigelify
- PwnerLike
- Alt-j
- Fix-case
- Divinity 2 Original Sin: Wiki Skill Popup
- keeprivate
- iHabno
You can check the company blog for extension IDs and other information. Google removed all of them in the meantime.
The malware has multiple purposes:
- Steal Facebook account data by sending Facebook login cookies or Instagram cookies to the command center.
- Create a Facebook API token if signed in to Facebook and steal it as well.
- Spread the malware through Facebook using the user's friends network. This happens either as messages in Facebook Messenger or new Facebook posts that uses contact name tags.
- Mine cryptocurrency using the user's browser. The malware could mine three different coins (Monero, Bytecoin, and Electroneum).
The attackers created several protective measures to prevent users from interfering with the operation.
- It monitored Chrome's extensions management page and closed it whenever the user tried to open it.
- Prevents access to cleanup tools on Facebook and in Chrome, and it tried to prevent users from editing or deleting posts, or making comments.
- Use the browser to watch or like YouTube videos, or write comments.
Closing Words
The identification of the malware happened by accident. Radware's machine-learning algorithm detected the malware and that led to the identification of the network and the removal from the Google Chrome Store.
Considering that the attackers operated the extensions as early as March 2018, it is clear -- again -- that Google's protective system does not work properly.
Chrome users need to verify any extension before they hit the install button. A rule of thumb is that you should never install extensions that prompt you to do so outside of the Chrome Web Store but since malicious extensions are always hosted in the Store, it is not a 100% safeguard against these.
The main issue here is that the majority of users can't verify if a Chrome extension is legitimate or not as it requires analyzing its code.
This leaves running Chrome without extensions as the only option to stay safe.
Now You: do you run Chrome extensions? Do you verify them before installation?


















government and public accesest yo my account done by government will pay for there damage pne way ir another
Our Lucy is getting very loosey — we must save this Lucy before it becomes a dust mosey 😩
This has nothing to do with the technology behind it. Google just doesn’t properly vet extensions. The same indiligence with XUL extensions would have your entire web browser under control.
FFS – it’s Google !!!!!!!
Was any sensible person expecting otherwise ??!!
We use this stuff because it’s there and there’s usually little other choice.
But how long has it been since ANY user with two brain cells connected had the SLIGHTEST confidence in “Google-approved” products – either in Chrome or Android?
Only reputable addons like Web Api Manager, and UBO, and one I have some questions about: Malwarebytes Browser Extension BETA. But that is only used for a general Google Chrome profile, never for my shopping and login profiles.
It seems to stop a lot of trackers/ malware, but being from Mbam, privacy could well be compromised. I will however read and implement your article about verifying. Thanks for a useful reminder.
The brainwashed Google lucy’s have always
come up with solutions after creating the problems in the first place.
Problem,reaction,solution.
That’s how these crazed, doped up on LSD Mountain View Ca. lucy’s roll…And since they receive U.S. goobermint fiat for their covert data collection/spy services and censorship duties…the google lucy’s are and always will be above the law.
WebExtensions will be more like Chrome extensions. They’ll be more secure!
Yeaaah NO.
I use three extensions in Chromium, they add simple features that should be there but aren’t. An easy to use zoom, cache cleaner and new tab homepage thing. It took hours to find these after rejecting many, many poorly functioning data collection sham extensions with 10^50 fake five star ratings. I do verify what extensions do but why trust anything in the chrome store when chrome is just a browser based ad server?
Once or twice I’ve seen an opt out FF install bundled with other software but chrome opt outs are hidden everywhere; then there’s the whole android phone universe. With all the volunteers out there doing QA on large companies’ software, google, ms, etc., have no reason to rigorously vet these malicious extensions if their ad business isn’t hurt by them. They get away with cursory checks. Periodically, google announces a clamp down on malware so they appear diligent but malware continues.
Password generator
chrome://flags/#enable-password-generation
chrome://flags/#enable-manual-password-generation
Bookmarks sync
Just sign in chrome and sync bookmarks, settings, passwords,… for all your devices
Poor Google baby…. been tackling with the malicious extensions for so long!!!
How about build and five majority of the users what they actually seek in a browser:
– Ad block / Tracking protection
-Bookmarks sync
-Password generator
-Secure VPN
-Cinema / nightmode.
Rather than working on converting a mere browser into an OS. 🙄
–
I am not getting ads even though I have whitelisted you in Ublock Origin in Firefox. Works fine in Chrome.
If you have uBO disabled and are still not seeing ads I would think some other type of content blocking is still being used.
FF Tracking Protection for instance will actually block virtually all ads. Not that I’ve spent a lot of time using Tracking Protection by itself but I am yet to see an ad when it is the only active content blocker. Any other type of tracking protection will also block most if not all ads, Ghostery is one example. Ads and tracking are so intertwined nowadays that it is hard to block one without inadvertently blocking the other. Oh well! :)
If you still see ads when using Chrome and gHacks is whitelisted, that rules out system wide blocking like with a hosts file. So it has to be something in your FF configuration… addons, javascript not enabled, and so forth.