Firefox 59: Referer Path Stripping in Private Browsing
Mozilla plans to strip path information from the referer when visiting third-party sites starting in Firefox 59 Stable. The new feature applies to the browser's private browsing mode only.
Web browsers provide sites with information when connections are initiated. Part of this is the referer value which holds the path of the referring site.
When you click on a link, the URLÂ the link was clicked on is sent as the referrer by default. The data reveals information to sites. While that is usually limited to the full URL a user came from, it sometimes may include critical information that users may not want to be shared with other sites.
Referer Path Stripping in Private Browsing
The Electronic Frontier Foundation discovered in 2015 that the site healthcare.gov was sending personal data to third-party sites through the referer.
https://www.healthcare.gov/see-plans/85601/results/?county=04019&age=40&smoker=1&pregnant=1&zip=85601&state=AZ&income=35000
The string revealed the user's age, zip code and state, income, and that she was pregnant and a smoker to linked third-party sites. While this may not be enough on its own to identify a user, one has to consider that sites may access a user's IP address and other information as well, and that is not taking scripts, and other means of finding out more about site visitor's into account.
Mozilla Firefox 59 will remove path information from the referer in Private Browsing mode when links lead to third-party websites.
Starting with Firefox 59, Private Browsing will remove path information from referrer values sent to third parties (i.e. technically, setting a Referrer Policy of strict-origin-when-cross-origin).
The healthcare.gov link above would be stripped to https://www.healthcare.gov/ so that third-party sites see only the referring domain but not the actual page or other information that may be part of URLs.
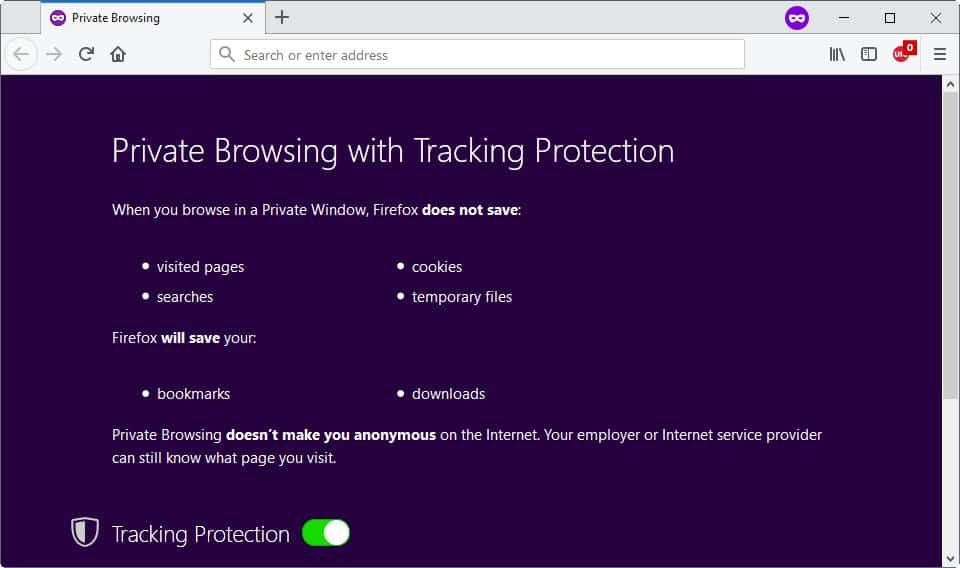
The stripping happens only in private browsing mode. Firefox users can start the special browsing mode with a click on Menu and the selection of New Private Window, or by using the shortcut Ctrl-Shift-P.
Add-ons provided Firefox users with options to strip or delete referer values for a long time. Users who prefer to have referring information stripped in regular browsing mode as well may check out extensions such as Smart Referer which does that.
Update
Mozilla removed the original preference that it used to set default referer policy in the Firefox browser. Users need to configure it using the following two preferences now:
- network.http.referer.defaultPolicy
- network.http.referer.defaultPolicy.pbmode
The preferences, the pbmode one affects privacy browsing mode only, support the following values:
- 0 = no-referrer
- 1 = same-origin
- 2 = strict-origin-when-cross-origin
- 3 = (default) no-referrer-when-downgrade
End
Firefox users may also change the preference network.http.referer.userControlPolicy to the value 2 which means strict-origin-when-cross-origin. Check out the Ghacks user.js file on GitHub for additional information on that and related preferences.
The main advantage of using an extension or changing the value of the preference in Firefox's preferences is that Firefox will strip the data in regular browsing mode as well.
Now You: How do you handle referers?
Related articles
- Improve online privacy by controlling referrer information
- Smart Referrer for Firefox Blocks Cross-Domain Referrers
- The ultimate Online Privacy Test Resource List





















Who loves the rest of Firefox once powerful UI customization.. get ready to say slow bye bye, because official Mozilla dev says it is going away in the future.
Enjoy your lame Chrome imitation soon! Nothing more needed to be said to that Mozilla Open Source abusers. Total brainless morons!
————————————————————
https://www.reddit.com/r/firefox/comments/7tu98a/wontfix_the_future_of_userchromecontent/
https://bugzilla.mozilla.org/show_bug.cgi?id=1431962#c3
Kris Maglione=
“The functionality of userChrome.css will not be supported, for the same reasons that we removed support for legacy themes.
Support will probably be completely removed from Firefox in the future, yes, but there are no immediate plans to do so.”
How is this going to effect surfing porn using private mode?
When ever you click on a link to a video on pornhub you get “more like this” below your video. Will stripping the links break this function making it harder to find content you actually want to look at?
It won’t Dave. The problematic addressed here is what an external site to the one you’re on receives of information of you concatenated to the link it receives.
Should the outcome differ from my expectations one would have to rely on imagination to replace “more like this” with excitement for new videos, perhaps “less like this” but possiblye “better than this’.
Let’s not let them drive us out of our curiosity for innovative and thrilling perspectives. Even if in the area of porn, frankly, they all seem to be the same, no scenario and far from the diversity of the Kama Sutra…
Now that I think of it, a side note concerning what links may include even when addressed to another url within the same domain.
A friend of mine sent me recently an email with a link to a Youtube video he found interesting.
I replied to him stating that the other video was quite nice as well …
He then asked me, “What other video?”
I gave him the link to the other video
“How did you you know that, how did you find it out?”
It was included in the link he had sent me : Youtube opened the new link (the one he had sent me) with the one it was sent from included (as “source” or something).
Morality : beware of the links you send, look at what”s mentioned in the location bar, and strip what you’d consider as superfluous.
Here are the Firefox referer settings that I use:
network.http.referer.XOriginPolicy = 1
[Send referer only when base origins match.]
network.http.referer.XOriginTrimmingPolicy = 2
[Send only the origin.]
network.http.referer.trimmingPolicy = 2
[Send only the origin.]
network.http.referer.userControlPolicy = 2
[strict-origin-when-cross-origin]
network.http.sendRefererHeader = 2
[Default: send referer on all request types.]
I’m pretty sure that one or two of these settings might be redundant.
Thank you for sharing the referer addon. I was looking for something like that.
Other settings about referrer https://wiki.mozilla.org/Security/Referrer
I’ve been using:
user_pref(“network.http.referer.XOriginPolicy”, 2);
user_pref(“network.http.referer.XOriginTrimmingPolicy”, 2);
user_pref(“network.http.referer.trimmingPolicy”, 1);
I’ve seldom seen any site breakage with those settings in FF but results will vary. I do have other browsers that use less restrictive referer settings if needed.
user_pref(“network.http.referer.trimmingPolicyâ€, 1);
*confused
https://www.ghacks.net/2015/01/22/improve-online-privacy-by-controlling-referrer-information/
@leanon
Sorry, I didn’t have email notification enabled for my comment. You’re right, it is confusing.
When using “network.http.referer.XOriginPolicy=2” AND “network.http.referer.XOriginTrimmingPolicy=2” the XOriginTrimmingPolicy ends up being redundant because ‘cross-site’ referers are never sent because of “XOriginPolicy=2”. If “XOriginPolicy” is not set or set to 1 then… the “XOriginTrimmingPolicy” actually does something. Sorry for creating confusion, that was on me. I’ve been playing with XOriginPolicy set to 2 and 1.
If I used “network.http.referer.XOriginPolicy=1” or it’s default setting of 0 AND “network.http.referer.XOriginTrimmingPolicy=2” then the “XOriginTrimmingPolicy” would be in effect, when going from one site to another, instead of “network.http.referer.trimmingPolicy=1” because the XOriginTrimmingPolicy set to 2 is stricter than the trimmingPolicy of 1. The less strict trimmingPolicy would then be in effect when viewing pages on one site (same-origin). If I didn’t set “XOriginTrimmingPolicy” then whatever “network.http.referer.trimmingPolicy†was set to would always be used. If “XOriginTrimmingPolicy” and “trimmingPolicy†are set the same I would just use trimmingPolicy. Doesn’t hurt anything if both are used with the same setting though. Just remember, “network.http.referer.trimmingPolicy†set to 2 WILL break some websites and I can’t sign into my router. I haven’t seen any problems with any of the other settings.
Play with “network.http.referer.XOriginTrimmingPolicy” and “network.http.referer.trimmingPolicy” on “https://searchengineland.com/an-easy-way-to-check-what-referrer-data-google-bing-or-yahoo-pass-to-your-secure-site-182421” and you can see what I’ve tried to poorly explain. On that page, in the content is a link for “what is my secure referrer”.
Another referer test: “http://www.stardrifter.org/cgi-bin/ref.cgi”
About:config referer entries:”https://wiki.mozilla.org/Security/Referrer”
Martin you wrote,
“Firefox users may also change the preference network.http.referer.spoofSource to the value 2 which means strict-origin-when-cross-origin.”
Isn’t it rather network.http.referer.userControlPolicy ?
// set the default Referrer Policy (FF53+) – 0=no-referer 1=same-origin 2=strict-origin-when-cross-origin 3=no-referrer-when-downgrade
user_pref(“network.http.referer.userControlPolicy”, 2); // Default=3
network.http.referer.spoofSource is true or false :
// disable spoofing a referer
user_pref(“network.http.referer.spoofSource”, true); // Default = false
Hope I’m not mistaking, had to read again my user.js (built on Pants’ Ghacks-user.js, I’ll never repeat it enough)
You’re right about spoofSource, but userControlPolicy sets the default policy, which means a 2 will set strict-origin-when-cross-origin unless the website specifies otherwise. Other prefs should be used if the goal is to override website decisions. Should we override website decisions ? No because that can be part of security measures taken by the site, and useful for compatibility, Yes because the site may use it for tracking.
Here’s the list of referrer prefs. (sendSecureXSiteReferrer and enablePerElementReferrer don’t exist any more)
the property “network.http.referer.userControlPolicy” don’t exist any more, too.
https://wiki.mozilla.org/Security/Referrer last changed @ 12.April 2018
As far as I understand – the property was replaced in FF59+ by two new properties
“network.http.referer.defaultPolicy”
“network.http.referer.defaultPolicy.pbmode”
Optimal about:config settings
network.http.sendRefererHeader
2 = (default) send on all requests (e.g. images, links, etc.)
network.http.referer.trimmingPolicy
1 = send the URL without its query string
network.http.referer.XOriginTrimmingPolicy
2 = only send the origin
network.http.referer.XOriginPolicy
0 = (default) send the referrer in all cases
network.http.referer.spoofSource
true = send the target URL as the referrer
network.http.referer.userControlPolicy
2 = strict-origin-when-cross-origin
network.http.referer.hideOnionSource
true – strip out the referrer when it’s a .onion address
Per: https://chefkochblog.wordpress.com/2018/02/02/referer-path-stripping-in-private-browsing-mode-in-firefox-59/
Sadly by default the mode is only enabled in the Private Window, for no reason.
Tom you are right of course. Edited right away ;)
Thanks, was going to say the same thing. You beat me to the draw. ;)
I use this since forever:
https://addons.mozilla.org/en-US/firefox/addon/smart-referer/
Send referers only when staying on the same domain.
Before 57+ I had:
https://addons.mozilla.org/de/firefox/addon/referrer-control/
(more powerful)
Referer Control:
https://addons.mozilla.org/en-GB/firefox/addon/referercontrol/?src=api
is very powerful and compatible with 57+
You can even define rules based on regular expresssions.
But the settings page is not a 100% intuitive, in my opinion.
This. I don’t see any reason for websites to get referrer information unless I’m just coming from a different page on the same site.
It’s just as easy for me to go in the backend and do this.
It’s for non tech-savvy users, aka the vast majority. Studies show that they expect Private Browsing modes from the different browser brands to protect their privacy on the web, which is not what they were meant for initially.
Firefox is going to progressively meet user expectations in this area through 2017-2018-2019. In 2017 Private Browsing got Tracking Protection, it’s going to get First Party Isolation and fingerprinting resistance in 2018, and they’re studying Tor network integration in 2019.
Features that are smaller in scope but provide useful protection (low hanging fruits) may come along the way, see Ghacks’ article on Mozilla’s study on privacy features if you want hints regarding what could be such low hanging fruits.
It’s good times for privacy on the web.
If I remember with Privacy Settings or Random Agent Spoofer add-ons you already do this. Only for ESR now