How web trackers exploit password managers
Most web browsers come with a built-in password manager, a basic tool to save login data to a database and fill out forms and/or sign in to sites automatically using the information that is in the database.
Users who want more functionality rely on third-party password managers like LastPass, KeePass or Dashlane. These password managers add functionality, and may install as browser extensions or desktop programs.
Research from Princeton's Center for Information Technology Policy suggest that newly discovered web trackers exploit password managers to track users.
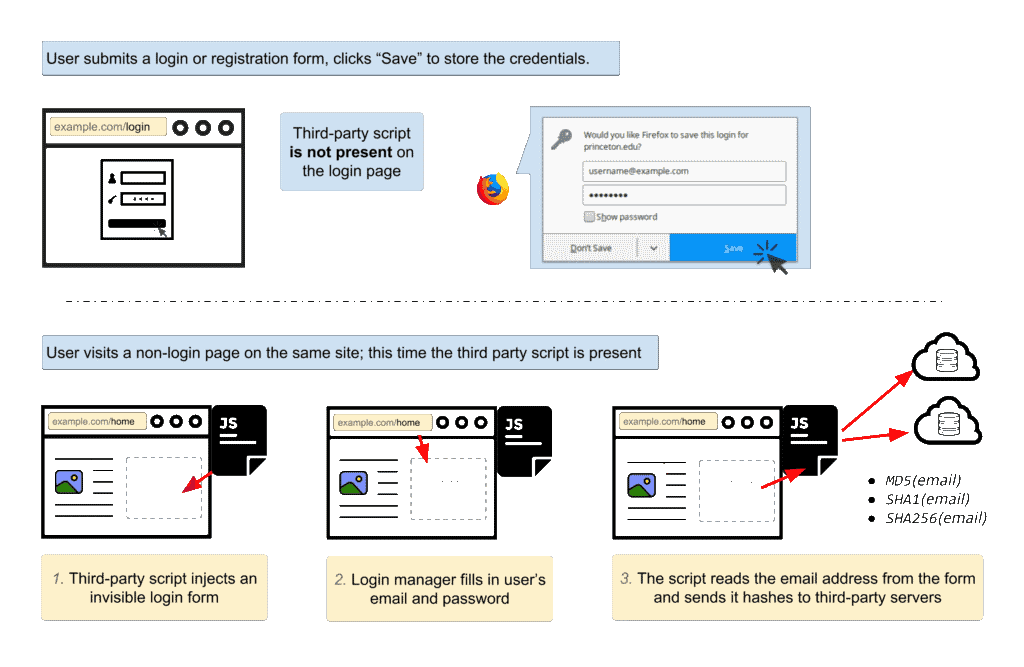
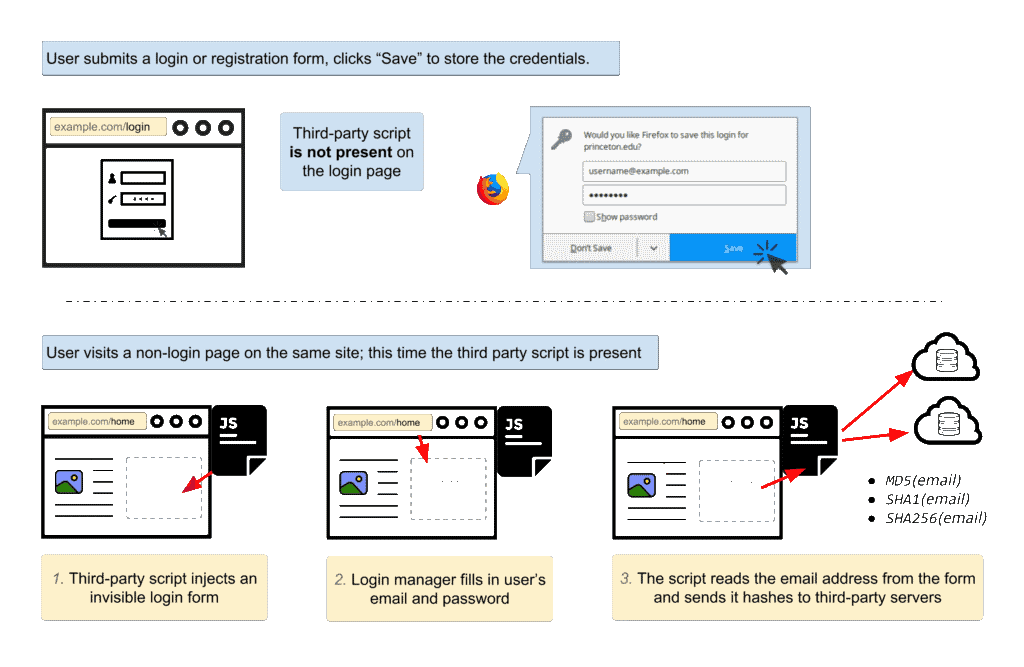
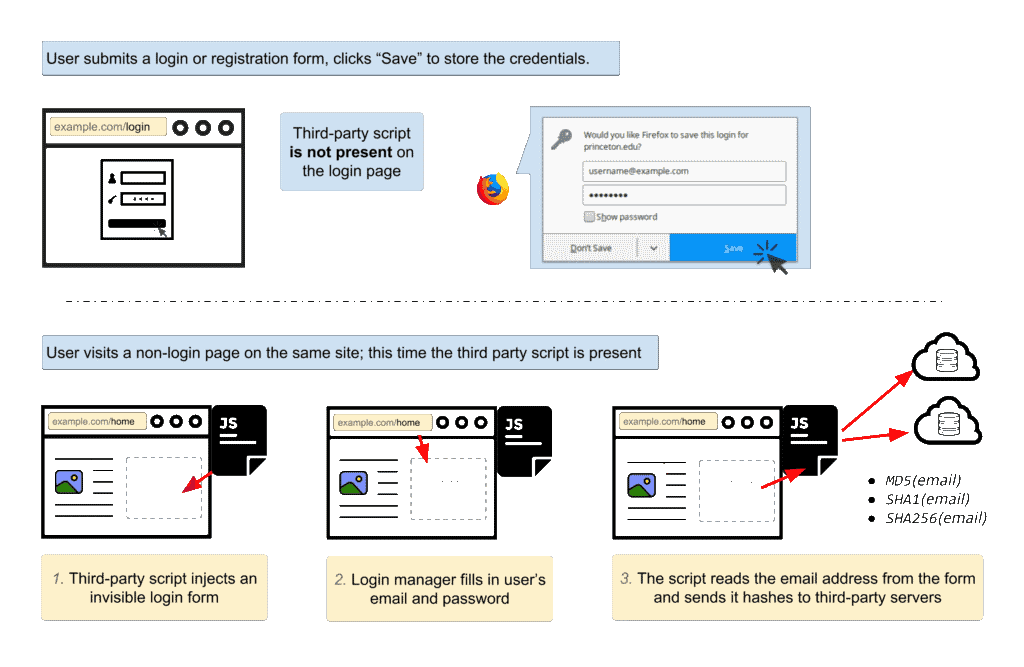
The tracking scripts exploit a weakness in password managers. What happens is the following according to the researchers:
- A user visits a website, registers an account, and saves the data in the password manager.
- The tracking script runs on third-party sites. When a user visits the site, login forms are injected in the site invisibly.
- The browser's password manager will fill out the data if a matching site is found in the password manager.
- The script detects the username, hashes it, and sends it to third-party servers to track the user.
The following graphic representation visualizes the workflow.
The researchers analyzed two different scripts designed to exploit password managers to get identifiable information about users. The two scripts, AdThink and OnAudience, inject invisible login forms in web pages to retrieve username data that is returned by the browser's password manager.
The script computes hashes and sends these hashes to third-party servers. The hash is used to track users across sites without the use of cookies or other forms of user tracking.
User tracking is one of the holy grails of online advertising. Companies use the data to create user profiles that record user interests based on a number of factors, for example based on the sites visited -- Sports, Entertainment, Politics, Science -- or from where a user connects to the Internet.
The scripts that the researchers analyzed focus on the username. Nothing is keeping other scripts from pulling password data as well however, something that malicious scripts have tried already in the past.
The researchers analyzed 50,000 websites, and found no traces of password dumping on any of them. They did find the tracking scripts on 1,100 of the top 1 million Alexa websites however.
The following scripts are used:
- AdThink: https://static.audienceinsights.net/t.js
- OnAudience: http://api.behavioralengine.com/scripts/be-init.js
AdThink

The Adthink script contains very detailed categories for personal, financial, physical traits, as well as intents, interests and demographics.
The researchers describe the functionality of the script in the following way:
- The script reads the email address and sends MD5, SHA1 and SHA256 hashes to secure.audiencesights.net.
- Another request sends the MD5 hash of the email address to the data broker Acxiom (p-eu.acxiom-online.com)
Internet users can check the status of tracking and opt out of the collecting of data on this page.
OnAudience
The OnAudience script is "most commonly present on Polish websites".
- The script computes the MD5 hash of email addresses, and also other browser data commonly used for fingerprinting (MIME types, plugins, screen dimensions, language, timezone information, user agent string, OS and CPU information).
- Another hash is generated based on the data.
Protection against login form web tracking
Users can install content blockers to block requests to the domains mentioned above. The EasyPrivacy list does that already, but it is easy enough to add the URLs to the blacklist manually.
Another defense is the disabling of login data auto-filling. Firefox users can set the preference about:config?filter=signon.autofillForms to false to disable autofilling.
Closing Words
Is the advertisement publishing industry shoveling its own grave? Invasive tracking scripts are yet another reason for users to install ad and content blockers in web browsers.
Yes, this site has ads as well. I wish there was another option to run an independent site, or a company that would offer native advertisement solutions that run only on the server a site runs on, and does not require third-party connections or use tracking.
You can support us through Patreon, PayPal, or by leaving a comment / spreading the word on the Internet.




















Don’t use password managers, period. Passwords are not something to be handled by anyone else except you.
How do you deal with 200 passwords, all different, all sufficiently complex, without a password manager?
I believe that many users, because they wish to avoid a password manager, use simplistic passwords and/or often (when not always!) the same, and get stunned when they’ve been cracked and possibly opened more than one login.
DO use complex passwords, all different and avoid a password manager if you have the brains, anyway the part of the brains dedicated to memory.
I wish to know whether other third-party password managers (keepass,lastpass,etc.) are affected..
@ Martin,
As an alternative form of revenue perhaps you could consider devoting one, two or possibly more pages entirely to ads. Users then have the option of visiting those pages if they want to rather than having ads forced on them like they are now. I’m sure visitors will open those pages purely out of curiosity to see what’s in there.
While I would not mind that, I don’t think that advertisers will be too pleased with that unfortunately.
I was thinking about something along these lines Martin: https://en.wikipedia.org/wiki/The_Million_Dollar_Homepage
Maybe would they agree with an outstanding concept (I’ve just invented it!) : start the article as a teaser and put as a condition to read it full a journey to an ad-only page, with a counter set, say, to 60 seconds to be sure the ads have had the time to deeply penetrate the user’s recalcitrant brains, together maybe with a funny message such as “One for mommy, one for daddy, you’ll have your article once you finish your ads!”.
New concept. :=)
So… disable autofill and (potential) problem gone?
Yes that blocks the issue.
Wait, if EasyPrivacy does already (and that is checked in my UblockOrigin), then why can I view both .js files posted in the article?
These sites are blocked as 3rd-party in EasyPrivacy.
Don’t forget the key-logging of ‘Session Replay ‘.
Static ads were tolerable.
The entire parasitic advertising sector should have been purged from society as soon as they introduced those screaming video ads (nearly 20 years ago).
Things like the new Brave browser and Basic Attention Token should help eliminate a lot of this.
According to rumors I’ve read, Firefox is receptive to the idea of BAT integration. Regardless, extensions can be made for most browsers anyway. This is the only solution I’ve seen where everybody wins. The alternative is continue as we are in an arms-race until we end up having to use 10 browser plugins just to make the web tollerable (I’m half way there now).
Re: TelV
I’m not sure about which negative publicity you are referring to but I know some people got triggered by Brendan Eich and his beliefs. Eich is the creator of JavaScript and a co-founder of Mozilla and thus has contributed more than almost anyone to the internet as it stands today. Watch for news about BAT in the coming days.
Try Brave on mobile. It’s going to win that space in short order.
I’ve read the background info on tokens and I’m aware of the concept, but it’s currently only available in Brave. Given the negative publicity concerning that browser as reported by Ars Technica and many other sites such as Verge.com, BusinessInsider.com and Extremetech.com for example, I doubt if users will be persuaded to switch browsers if they know they’re going to bombarded by ads.
Tom: “user attention is PRIVATELY monitored ON-DEVICE in the Brave browser” “Ads are then anonymously matched with customer interests using LOCAL machine learning algorithms.”
Where everybody wins?
I read on basicattention (the link you’ve provided above),
“The Brave browser knows where users spend their time, making it the perfect tool to calculate and reward publishers with BATs. ”
What am I missing, misunderstanding, when a browser knows where I spend my time would fit into a win-win scenario? I don’t want a browser to know where i’m spending my time!
Again the problem is moved from the only valid solution which is a fundamental change of the ads business mentality, policy, philosophy! It’s up to that business to lower its expectations, not to the user to agree on a “compromise” which would lower his privacy. But, as i wrote, I may be missing something.
According to Ars Technica blocking ads and then replacing them with your own is frowned upon by the advertising industry: https://arstechnica.com/information-technology/2016/01/mozilla-co-founder-unveils-brave-a-web-browser-that-blocks-ads-by-default/
Go read for yourself how it works: https://basicattentiontoken.org/
Ars is not a reputable website imo, like Slashdot (who reads it anymore?), they became heavily politicized and agenda-driven in recent years.
I’m using Pale Moon with uBlock Origin. I didn’t even get to the test page – it was blocked by my adblocker. I don’t run the adblocker on this site or a few select others.
I hate ads. Never watched TV for over 15 years because of the commercials. Funny thing because i was a broadcaster for 20 years. Where I live ads are in a different language which makes it even worse. My phone with NO internet service loaded still gets ads from the phone company a few times a day. Thank goodness for kodi & ublock origin, ad muncher etc.
I hate ads also. Since I live alone, what I do is use headphones to watch TV while I am generally surfing/working on the computer. When ads come on and I haven’t recorded to the DVR to skip over them, I just take the headphones off and focus my full attention on what I am doing on the computer until the show returns. It’s much easier to multitask like this using the headphones. I’m really glad I discovered this!
TV advertising is a world unto its own. I find it so obnoxious that it made me stop watching TV entirely.
@Tom – Ahh, so you are French! That might explain the sometimes ‘lyrical’ tones about your dialogue. At the risk of getting rather off topic, some of my most lovely memories are of France….the little markets, the fresh food, the olive oil and hand-made soaps, the tapenade…and the sunflower fields and lovely golden vibrancy and quality of the light….not to mention the sound of the language, especially when a Frenchman speaks english.
But we were talking about the rather more dry subject of advertising, malware, Hosts files and greedy marketeers… what a contrast!
Now you Martin? Is it Olive Oil for you…………..or is it Hosts files?
My answer is that both are great….but each have their own moment.
Anyone got the remote control? I need to skip an…………ADVERT!!! :0
@Sophie, “I’d prefer if anything, longer ads, more spaced out”, OK! As I said I’d rather the opposite; this is so personal but one can wonder if these “cycles” have any coincidence with what would be perceived by advertisers as a country’s, a culture’s best predisposition to “eat” ads :=)
I receive US news channels here in France so I don’t know how it goes in the States with movies, series etc. When I watch CNN here I get annoyed by the frequency of ads but in fine they get to annoy me less than those on French TV because they are so short. I’m interested with this because of psychological and maybe sociological, cultural links. I must admit that, as far as I’m concerned and for a reason I still cannot explain, advertisement in English bothers me far less than in French. Maybe because I *am* French! (I’ve spent my childhood in NY, a wonderful and so happy childhood, which also participates to my affection for America even if what I knew from the country was its East coast. I got to imagine other areas of the grand country and its people later on, from here in Europe but not “physically” on those grounds, blended what I intellectually discovered with what I had lived and remembered personally. Beyond, I cannot say I’m representative of an average Frenchman, but I do feel stronger ties with french who travel or have traveled. I won’t end with my phone number but I can add that Dutch father origins contribute to explode my mind with diversity, lol.
Concerning the thousand and one ad business maneuvers to combat all resistance (!) I remember the story of a Japanese invention which would pause the recording of TV programs whenever it detected ads! That must have been a heaven’s technology. Never heard about it after that… :=)
To finish this chapter with a smile, this funny scenario “Well, let’s stop talking about my little me : now, you, what do think of me?!” — I love that!
@Tom – It wasn’t entirely clear if you are from the US? Whenever I’ve traveled and watched satellite US channels, I am struck by the desperately frequent US-based adverts. Not sure which now, but it was certainly a major news channel and very well known, while I was in Spain just a few weeks ago, and the frequency was nuts! At the worst level, it can’t have been more than 2.5 to 3 mins. In that time, they literally squeeze in 1 or 2 little segments. Then to have to suffer the repetitive nature of the trailers, fillers, just make this completely unworkable, from a viewers’ perspective.
I’d prefer if anything, longer ads, more spaced out….and then you can at least go and do something else. But as I say, I have zipped through TV adverts for years, with ease and no difficulty, thanks to digital recordings, and usually feeling just a little smug at the thought!
By the way, TV companies and advertisers well know that we all do that, so they are trying to deliver adverts via set top boxes now, that are effectively “in-App”, that you can’t bypass. But that won’t affect me, because I tend to prefer to make DVR recordings, to watch at my leisure, and not within an App. And back on a PC, my bases are well and truly covered, with whitelisting just for the most most most deserving. Ghacks is one such example of excellence, and a well updated Hosts file among other things helps to guard against Malvertising.
@Sophie, now this is an interesting topic in the scope of advertisement distribution on television.
I don’t know, not sure of how ads are allocated on TV in the U.S. nowadays, but I do remember that back in the sixties we had 1 minute of ads every 5 minutes, that is 20%. In France ads are allocated differently, not every 5′ but within slots which can last from 3′ to 10, 15 minutes on “prime-times”. And my rough calculations come up to a similar 20% of ads within 24 hours.
Perhaps different cultures are more sensible to certain cycles than others. When I view a TV series or a movie, long ads are unbearable. Private TV channels here break a 120′ movie with 3 times 6minutes ads, which makes me explode (implode, rather!). Finally I believe I suffer less with extra short ads on short cycles than 6, 10, 15′ slots, even if the latter usually offer the time for dish washing :=)
To paraphrase Martin : Now you, what’s your preferred ad distribution cycle?!
Exactly me! headphones off for a while………….99% of TV on DVR, and the Panasonic has a lovely button that lets you dial in how many mins. to move forwards…. in the UK, almost all Ad breaks are 4 mins long, so it magically moves past the adds in a perfect 4-min block.
Where would I be without my Panny? But actually….UK TV is still not entirely unreasonable with TV advertising. When I’ve been in the USA or Australia……..the TV is UNWATCHABLE!!! There are so many adverts that you might as well just give up.
Greed has overtaken common sense, and relationship-building with the consumer.
LONG LIVE ADVERT BLOCKING!! ;-)
NoScript blocks tracking scripts already i think as with NoScript, it doesn’t load scripts unless you allow it.
I use No Script religiously.
I went to the opt out page & yep Sure enuff I was opted in….
the sites that I HAVE to login to, I HAVE to turn NoScript off…
Do away with ALL Logins I say….LoL
Any solution that runs within a Web Browser is not enough. On my home networks, I have quite a few devices that use various protocols to do all sorts of things, including controlling an air conditioner, monitoring a solar generator, updating firmware and so on. All of these activities potentially provide tracking information to other parties.
As an interim solution, I run a firewall box that blocks access to undesirable sites via DNS spoofing. That works well at present, even for HTTPS traffic (the TLS Host ID is always in plain text), but with the increasing use of DNSsec, such approaches will soon be ineffective.
Makes you wonder whether all that encryption overhead is worth it, given that the remote end is probably selling your private details to the highest bidder!
Darfnix: I’m insufficiently experienced to comprehend your response, but wonder if you view Quad9 as useful to achieve your objective.
There’s zero mention of Keepass or any specific managers in the article.
The only mention native password managers, Firefox and Chrome is vulnerable.
Firefox 52 + Native PW man: Fail
Firefox 57 + Native PW man: Fail
Firefox 56 + Keepass + Passifox: Pass
Firefox 57 + Keepass + Keepass-Connector: Pass
Firefox 57 + Keepass + Kee: Pass
The line:
1.The script reads the email address and sends MD5, SHA1 and SHA256 hashes to secure.audiencesights.net.
should read:
1.The script reads the email address and sends MD5, SHA1 and SHA256 hashes to secure.audienceinsights.net.
Incidentally, I personally don’t mind topic-relevant ads. They can sometimes be quite interesting and useful, and they require no user-tracking. In fact, they could actually consist of just links to related web sites that users can click if they want to. What I try to block at all cost are tracking sites and those rubbish ads for gambling and dating sites, which most people would probably only click or touch by mistake anyway.
BAT – Basic Attention Token. It essentially solves the problems for both advertisers/content creators and privacy advocates alike. It kills several birds with one stone. It’s the no-brain solution very few have noticed. The team behind it are some of the best brains in the business. I’d be interested in your thoughts Martin.
I’m not Martin, but here are my thoughts. I’ve never heard of it before, but from reading the summary at basicattentiontoken.org, it’s hard to see how this is that much different than tracking. It’s only changing where the tracking is taking place.
Also, the site keeps mentioning “anonymization” — which is a red flag word to me. I’ve yet to see an “anonymization” system that actually provides the sort of anonymization that matters to me, so I tend to view such claims (and those who make them) with a jaundiced eye.
Also, this seems to be tied to the Brave browser specifically which, to me, isn’t a positive thing.
https://www.reddit.com/r/firefox/comments/7n4jas/ad_targeters_are_pulling_data_from_your_browsers/drz04qk/
Mozilla employee:
“I think the FF built-in manager won’t be affected since it hides autofilled passwords from JavaScript anyway. Or at least I think it does. This is third party password managers.”
The problem is with the internet ad model that everybody accepted blindly, since day 1. TV stations get paid on the number of people who watch, there is no ‘requirement’ of how many actually go buy after seeing the ad. Internet however is often click or buy based.
To make it work Martin has had to include 7 ads on this page I am typing – I have ghacks whitlelisted of course – it is excessive but it is the side effect of the acceptance I mentioned.
I’m also fine with ads, but only a VERY small number of them actually talk about the “feature(s)” of the product I’m interested in knowing about, e.g. auto ads are almost totally about the exterior, but the buyer, me, sees the dash most of the time !! (and I’m not at all interested in a car that slides on wet pavement). 2nd I’m always leery of products with lots of small (usually in 2 point type) disclaimers at the bottom of the page. These companies must think we’re all idiots.
“Half the money I spend on advertising is wasted; the trouble is I don’t know which half.” is a quote attributed to John Wanamaker, US department store merchant (1838 – 1922). Already then. Drove merchants crazy, the ad business had to do something to get that lost half smaller! Hence tracking for the purpose of targeted ads.
I’m fine with ads, they do get on my nerves because of their omnipotence but they don’t revolt me. Tracking does.
The ad business with its “always more” is basically stupid. Some advertisers are starting to understand the fact that an advertisement is meant to create a relationship between a product and a consumer, not to rape the consumer’s psyche.
I’m fine with ads as a concept but I do block them, because they are tied to tracking (even if those trackers are blocked here), because of malvertisement which remains an apparently forgotten issue, because of its excess, lack of elegance/humor/imagination/tenderness in most of its campaigns brought up by a force-feed concept of efficiency.
These issues resolved I’d understand and accept the intrusion of a clean and respectful advertisement, mainly on Websites which have but this mean to survive. Not before.
Web-trackers exploiting password managers proves that the ad business remains stubborn on its very way of conceiving their affairs. Big mistake.
“I’m fine with ads as a concept but I do block them, because they are tied to tracking”
Yes, me too. Tracking is, by far, the major problem I have with ads. I won’t even consider allowing ads through unless the tracking stops.
You always write very genuinely and thoughtfully, and I really like that!
As was noted somewhere, Brave’s password manager is the only one not to fall for this. Seemed like Vivaldi filled the e-mail address on the test page but not the password but that might have been me.
Nothing beats the security of plain paper and pencil. That’s how i store my passwords. Haven’t been hacked.
thats until you either lose the paper or someone steals it.
I have a friend who keeps his password list printed out in his wallet, with a backup copy at home. His reasoning is that if his wallet is stolen, he has bigger security problems (lost ID, credit cards, etc.) than the small window of time between the exposure of his passwords and when he goes through and changes them.
Personally, I keep all my passwords in a (non-networked) password locker on my phone, and keep a printed copy of them all in a physical lockbox in case my phone is lost or destroyed.
Until your boy/girlfriend, guest, kid, guest’s kid, burglar, plumber or what have you steals your paper and knows it all :)
Boy/girlfriends in particular can be sneaky because they bet a lot on you.
I fill login data manually using Keepass and the Self Destructing Cookies addon ensures local storage data is deleted after I logout along with cookies.
Maybe you should consider a subscription as a means of accessing your site Martin. I’m sure most readers including myself wouldn’t object to an annual fee of say €10 for the valuable information you provide daily.
I cant do that .
I Have no Credit cards & live at the poverty level on Disability Insurance
I would be excluded…
Big thanks Martin for all your work, care and thought you put into everything.
We all know the dilemma. You have to have support, nothing is really free….but the industry (because of its own greed) works against itself, spoiling it and undermining it for all.
The end result is more and more blocking, and holding intrusive things at arms length…..its the same as television adverts…they are always “louder” than the content on TV.
Why does every have to keep shouting at us? Intrusive and sometimes dangerous ad-servers are just like that “extra loud” and SHOUTY adverts on television, and what do we do to those?
….we turn off, or we turn over……..or we turn off and make a cup of tea!
Thanks from all! And happy new year.
Happy New year to you dear Sophie (I love that name), to all : may 2018 enlighten our hearts and our minds.
That’s all, folks :=)
Hey, thanks Tom! I hadn’t seen many messages from you here just of late. Good to know all great, and Happy New Year to you Ghacks, and all! Best of days, Sophie.x
So glad to have always listened to my gut on this one. Copy and pasting from a Veracrypt file container isn’t the most convenient but it still looks to be the most secure at the moment.
Me too!! In my case it’s Keepass, but same idea.
This exploit actually crosses the line from unethical to completely malicious, in my opinion. And it reinforces the idea in my mind that only I, the user, should have control over which particular 1s and 0s are allowed to get though to my computer. I’ve heard of all kinds of counter-arguments (e.g. “bypassing advertising is unfair”, etc.), but these arguments all fall apart when you realize how malicious some people can be when they have power over your computer.