You can steal Chrome data (if you have local access)
Whenever someone reports a vulnerability that requires local access to a system, a discussion erupts about whether that is really a vulnerability that needs fixing.
One side argues that it is, considering that there are numerous ways that someone could gain local access to a device. The other side argues that it is not, as an attacker can do anything on the machine anyway with local access (at the user's level).
A issue in Chrome was revealed recently by Lior Margalit on Medium that allows anyone with local access to a system running Chrome to steal saved data from the user account.
A prerequisite to that is that the actual user needs to be signed in to a Google account. If that is the case, an attacker can use the method to steal any sync data from the account including passwords, form field data, bookmarks, or the browsing history.
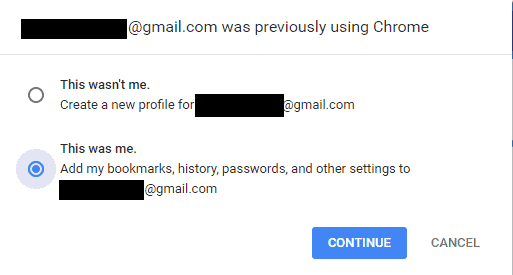
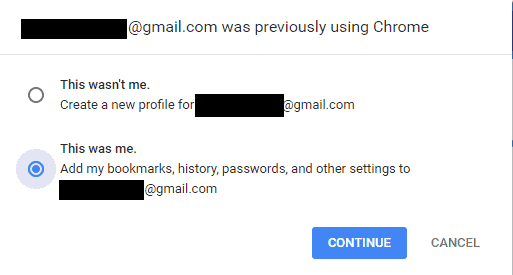
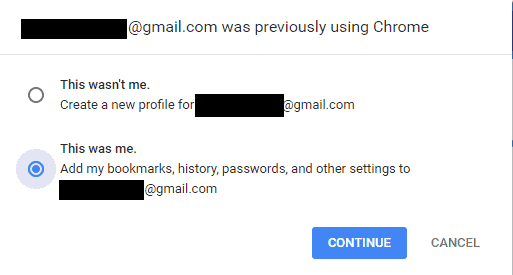
The problematic thing about this is that this requires no authorization whatsoever. Basically, what the attacker needs to do is sign out the actual user, and sign in using a different Chrome account. Chrome displays a prompt then to add the user's bookmarks, history, passwords and other settings to the new account.
Since the data is synced to the new account, it is now possible to access all stored data, e.g. passwords on chrome://settings/?search=password on any device you sign in with that new account. The process itself takes less than a minute to complete
Lior reported the issue to Google and received a "won't fix" response by the company according to the article.
The process in its entirety:
- Go to chrome://settings/manageProfile.
- Click on "edit person".
- Select "sign out".
- Click on "sign in".
- Sign in using a different Google account.
- Select "this was me" when asked about the previous Google user who used Chrome on the machine.
- The data is synced to the selected account.
- Go to chrome://settings/?search=password to browse passwords on any machine running Chrome provided that you are signed in with the new account.
The whole process won't take longer than a minute to complete.
Closing Words
The best protection against the issue is to never leave your device without shutting it down or locking it. Another option that you have is to not sign in using a Google account. This reduces functionality however and some users may not want to do this.
There are other means to steal data from a device if local access is available. Nothing's stopping a user from opening the password listing in Chrome directly for instance
I think that Google should add a fail safe to the process, for instance by asking the user to enter the password of the other account to proceed with the merging of data.
Now You: What's your take on this?


















“There are other means to steal data from a device if local access is available. Nothing’s stopping a user from opening the password listing in Chrome directly for instance”
If someone wants to enter your house, he will find a way to do so, so why bother locking the door?
Derp.
“Hey is this other account also yours? Do you want the private data of it?” is a horrendous practice. What the fuck were they thinking?
> If someone wants to enter your house, he will find a way to do so, so why bother locking the door?
Your analogy is incorrect. It’s more akin to leaving the door open because you cannot close all of the windows inside a fully fenced property with a looked gate.
“There are other means to steal data from a device if local access is available. Nothing’s stopping a user from opening the password listing in Chrome directly for instance” This is wrong. If you try to view passwords on Chrome you must enter the Windows account password first. So if the computer has a Windows password, but someone left the computer on/open, and somebody else tried to view passwords, and didn’t know the Windows password, they couldn’t see Chrome’s passwords.
The issue is a wontfix because:
* This not only affects Chrome, you can locally copy any data for all applications including Firefox.
* The first protection is already the other user account, which then needs to be hacked/logged in – good luck on it. Otherwise why want you allow strangers on your account?!
* There already tools to read out Chrome passwords from NitSoft and it still works cause the data aren’t encrypted. https://www.nirsoft.net/utils/chromepass.html
* You can opt-out saving passwords so it won’t sync, …
* There tools to protect others to get access to Firefox, Chrome and other applications. Chrome or Mozilla is not responsible if someone abuse an account in general.
* Using password manager and won’t sync passwords or logins should be prefered no matter what, cause the database is encrypted.
* Revealing the password (within Chrome) – click on the eye button requires a password if you setup a password during the sync-setup.