Browserprint: advanced browser fingerprinting test
Browserprint is a fork of the popular Panopticlick browser fingerprinting test that adds a number of new checks to the whole process.
Browser fingerprinting refers to using identifiers revealed by the web browser itself or the user for tracking purposes.
When a browser connects to a site on the Internet, information such as the operating system, web browser and version, is revealed automatically during the process.
Sites may use scripts to get additional information about the browser or user system. For instance, sites may get a list of all installed plugins, of the screen size and color depth, installed system fonts, or language.
The main idea of fingerprinting is to compute an identifier from all the information and assign it to the browser. If nothing changes, the browser may be identified on future visits by running the test again and comparing the identifier against a database of previously computed identifiers.
Browserprint
Browserprint looks and feels a lot like the Panopticlick test. The service offers more tests and a couple of extra features that you may find useful.
A click on the "fingerprint me" button on the frontpage of the service gets you started. You need to fill out a captcha though before the site runs a series of queries against your browser.
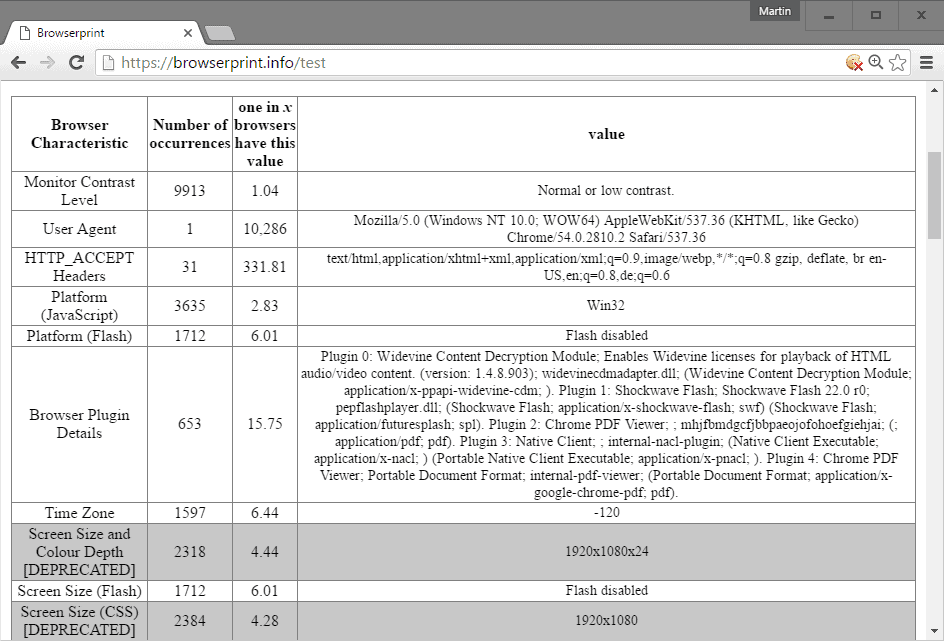
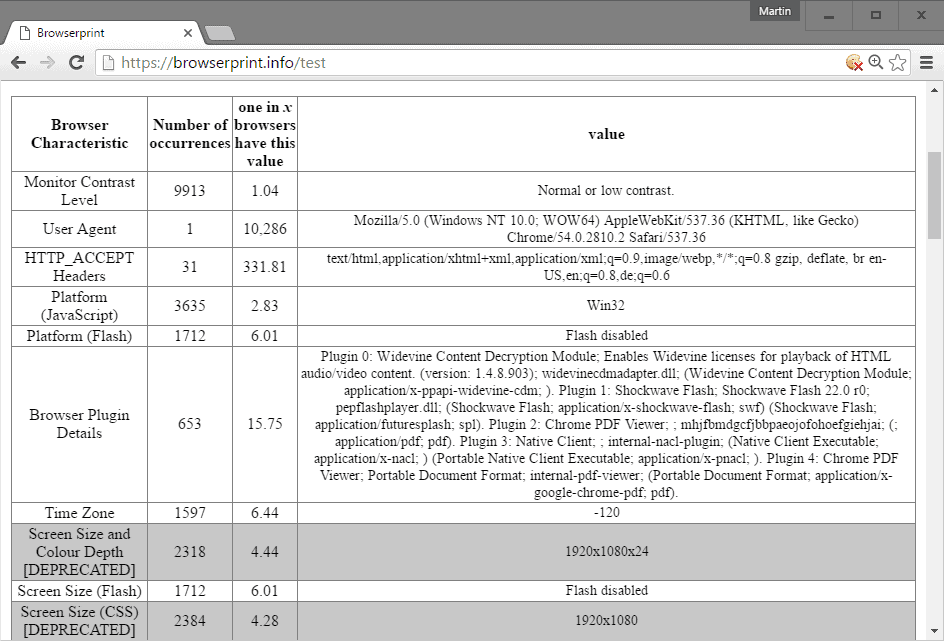
All results are returned in a table afterwards listing the name of the test, how unique your browser is compared to others, and the number of other user browsers that matches the value of yours.
Also, it lists how unique your browser is at the time, and how many bits of information it reveals.
If you ran the Panopticlick or another browser fingerprinting test before you know how this works already.
The additional tests that Browserprint runs is what makes the service interesting. For instance, it supports an audio fingerprinting test, tests for ad or script blocking, for Tor, or character sizes.
You may hover over any test to display a small blurb that reveals a short description.
The site displays a fingerprint UUID on the results page. You may use it to share it with others, or compare future tests against it. The latter can be useful if you decided to harden your browser version against fingerprinting, or if you want to run the test regularly without doing so.
Anti-Fingerprinting
One issue with hardening a browser against fingerprinting is that not-revealing information may be used for fingerprinting purposes as well. So, if you decide to block Flash for instance, the test will use the information as well.
Obviously, it may be better than revealing bits of information that are unique to the browser or computer.
The rise of new browser features has introduced new fingerprinting options. Audio fingerprinting for instance is used already on the Internet for tracking purposes, and there is little users can do about it since browsers don't ship with options to turn that feature off or make it work only after users give their okay.
Now You: are you worried about browser fingerprinting?

















More information is revealed about the system and browser through using Tor in this test than through the addon enhanced Firefox browser that I typically use, I am somewhat surprised.
All this makes me wish that the integration of Tor functionality would come much sooner to Firefox, so as to provide yet another layer of protection to the browser.
Hahaha. I’m a rich millionaire on the streets but none knows beacuse I run an old VW Polo with a worn out color and rust on it.
Random Agent Spoofer is one of some good addons.
What about installing more versions ofthe same browser? http://utilu.com/UtiluMFC/
Then there’s a browser inside a VM.
This article and the subsequent comments bring to mind a new type of add-on. I recognize that this has never been done but I wonder if it is at all possible:
Could there be an add-on created that literally masks a computer every time? – Even fingerprinting as well as audio fingerprinting. I don’t have the technical knowledge to even speculate on the feasibility of it but I’m envisioning a “mask†that inserts itself throughout the computer whenever the web browser is started. (I could see it causing a slight delay once implemented but that is a small price to pay for true anonymity.)
If it is possible I’m thinking of perhaps 10 to 20 different “identities.” The browser then taps into one of these identities at random and “voila” true anonymity.
I’m not capable of doing it (hell, I’m just learning to use Linux…) but I’m sure someone out there is capable of doing it. What about you, Martin? You’ve got extensive skills. It could be your avenue to fame and fortune.
@Valrobex:
Doesn’t an add-on similar to this already exist for Firefox? I’m thinking of Random Agent Spoofer. It doesn’t “insert itself throughout the computer” but it does tap into dozens of random identities comprising OS, browser, etc..
How do we block audio fingerprinting?
Also, Browserprint seems down for me.
You’d have to block api access. I’m not aware of a preference or extensions that does that, but have not done serious research on the topic yet.
Hi Martin Brinkmann
the link to the website that tests audio fingerprinting operates with several thirdparty trackers according to the add-on Privacy Badger and a very insisting popup. do you know of any alternatives, like browserleaks.com, with better ethics?
also: is foamy tape attached to the microphone a way to solve this issue?
MAybe this one is better? http://www.zdnet.com/article/think-youre-not-being-tracked-now-websites-turn-to-audio-fingerprinting-to-follow-you/
Audio fingerprinting does not rely on the microphone.
thank you. lots of numbers unfortunately, so I guess I’m easily detected.( I miss an explanation on how to read the result. the graph doesn’t make much sense either )
@ Tom Hawack : “hoping that these behaviors remain on the Web only and get not transmitted to real social and relational life.”
About security in real life, “le marché de la peur” is already invading everything. About privacy in real life, laws are more adapted, they can be applied with more success, although for my grandchildren I’m quite pessimistic on the subject. Fingerprinting on virtual life… I do not make any difference anymore between virtual or real life, something on the first could impact the second seriously. Presently i’m more preoccuped by drones’ projects like “Prime Air” from Amazon, and similar eventuals f****** mosquitoes, that’s why i keeped some competition slingshots in case… I know i should be really worried about Fingerprinting, but with my human brain i have to consider priority orders. Until cowboys save the Planet, boycott is my choice :-)
You know, yapadkoi, I sometimes, I still wonder, if radical approaches are not a surrender to fear, to this “fear market” as you named it. Yet, if I wonder intellectually (in a dialectic of concepts) I may have changed already as many of us have. There was a time when I practiced far more than I do today a medium, a balanced approach towards what I disliked, i.e. ads in the mailbox : I’d refuse then to put an “ad refusal” sticker on the mailbox because I believed that some ads may be ok, I disliked the idea of missing a possibly good for the sake of avoiding a certainly bad. I don’t anymore. Now I’ve put that sticker on the mailbox.
Boycott is one of those radical behaviors. Is it fear, or anger, revolt, or all together? Neither are good counsels.
There are in this modern era many good things but also a big issue which is identity and privacy. Both are related : less privacy means a diluted identity and diluted identities are manipulated far more easily. What annoys me in our world, more than its modern inquisition itself is the alternative it leads any awakened consciousness : if I accept the deal I’m accepting to lose my identity, if I refuse it I become confronted to bad feelings, those of hatred, revolt and even fear.
I want, I aim to avoid extreme positions even if I am tempted, even if I fail as with the advertisement issue. I wish not to choose one day secrecy on the Web (with its arsenal of tools) just to allow my privacy to prevail. But I’m not sure I’ll be able to maintain this equilibrium point I’ve always made a principle.
Concerning life (birds & bees & flowers & you, him, her, them, us) I cannot say I’ve experienced relatives, friends, strangers, people in town who would behave in such a way that I’d suspect a fear of being tracked. I’d even say that my feeling is that people fear so little that most of them sit on their privacy and lay their lives as they never did before. If many are afraid it is not, IMO, of loosing their privacy but rather of being excluded from the system, from the society should they adopt a singular attitude in the face of inquisition.
So when psychologists together (which is seldom) with a Church’s leader declare “Don’t be afraid” I’d rather hear “Don’t be afraid for wrong reasons” because if being free of fear is as such an aim then such an aim leads as well to blindness.
What happened to Google’s Glasses remember > boycott = “placard” for the moment. In this case boycott was the only solution, instead to see people at work or on the streets starting radical wars.
“Boycott is one of those radical behaviors. Is it fear, or anger, revolt, or all together? Neither are good counsels.”
I never advised people to make the same, i’m not a conscientious objector. I just think my choice is the only language an enterprise stealing your life with no remorse and without your consent can understand. All what i could choose to do otherwise will be futile, JMHO. Not a radical approch > just my choice. If you have a better idea and simples solutions to stop these enterprises doing this, then tell me Tom, i will try to be receptive to your arguments… :)
What is the real value of such a test? Most people will have added software to their computer & tinkered with/tweaked settings, all of which make each computer almost unique.
Furthermore, even if you know your computer is unique, the test does not show what is unique about it and/or how to make it less unique because that is what an interested/concerned user would want ultimately.
So: great to know your fingerprint, ten what?
The panopticlick test is useless now since they included canvas in their valules which always provides a unique value, even if spoofing. It is however useful in determining some variables.
The other downside to panopticlick (and probably other tests, including this one – Jason-the-commentger-on-ghacks for one is a good “viewer”/perspective on this) is that that, despite an attempt to be real world, they in fact influenced by visitors. Repeat visitors to panopticlick would (in the past) reduce your fingerprint. I also note the incident of Firefox browser to be almost double – not surprising given the mindset.
As of typing, totally drunk and nude (pics on request), the site is down or not responding.
Personally … its a never ending battle to stop fingerprinting – The REAL answer lies in a critical number of users implementing the same “set” (notwithstanding things like canvas which are 100% unique)
https://www.browserleaks.com/
1) Test CanvasFingerprinting
2) Test Content Filters
“are you worried about browser fingerprinting?”
Fingerprint is a serious thing, that should be reserved to the police. Those online using this method and trying to sell me something will never have my money. Not worried, i just boycot them systematically, like those using anti-adblockers.
Well, if you have the ability to distinguish sites that fingerprint from those which don’t, you have a good formula. There are so many techniques, and should all be known by the user, and should all be identified within a domain in order to start having a chance of filtering correctly … and should correct filtering be done… how many, what percentage of non-fingerprinting sites would there remain? An odyssey.
yapadkoi, Pale Moon won’t prevent all fingerprinting, even if it does handle natively what is now a well-know fingerprinting technique, that of canvas (handled in Firefox with an add-on such as CanvasBlocker).
Browsers started to handle partially the worst ads, the popup ones, then came adblockers, now the advertisement business together with malvertisement together with whatever ears spends fortunes of skill, time and money to track users, be it for targeted advertisement, be it for a quicker return on investment than ads (malvertisement), be it for the sake of so-called or rather so-claimed state security.
From there on no browser will ever counter fingerprinting, should they even be able to.
I’ve always considered for myself privacy rather than secrecy but it appears that secrecy would be the last rampart for privacy itself, and IMO this leads to a dangerous trend, that of paranoia or at least such a troubled perception of the Web that it invokes sneaky behaviors, hoping that these behaviors remain on the Web only and get not transmitted to real social and relational life.
Some Websites that make use of this technique (javascript on):
https://blog.malwarebytes.org/
https://github.com/
http://film-stream.cc/
Use “CanvasBlocker” for Firefox and “ScriptSafe” for Chrome.
If i have for intention at first to buy something on a site, I do a thorough investigation. It depend the degree of spying, if fingerprinting is used to spy my habitudes, my tastes all other the site, or just 2 or 3 small things. Generally surfing i use Palemoon and add-ons as formula, that’s why i’m more worried about the decision from Mozilla with ChromFox to remove xul >:(
I’m bothered by being tracked, I’m annoyed by us all being tracked. And the fingerprinting means are increasing.
Also, as mentioned, “One issue with hardening a browser against fingerprinting is that not-revealing information may be used for fingerprinting purposes as well.” : try to be smart and it’ll be at your disadvantage.
In fact more a setting, a behavior is shared by few more it points us out : be a sheep among the sheep and avoid trying to be the shepherd.
To melt away into the crowd appears to be an interesting approach in society but a lousy one when it comes to the systematic tracking by means of fingerprinting on the Web.
I’d say that because, whatever we do or do not we remain tracked, rather than trying to hide we may adopt another mental attitude, an active one which is to misinform whenever possible. Make the puzzle more complicated. Also, regularly change “fingerprintable” settings. Take it as a hide and seek game.
All this may be at best funny but if it is an intellectual stimuli it certainly doesn’t participate to quiet and peaceful happiness. “Deal with reality not with dreams” says psychology, “Live in order to make your dreams become true” says entrepreneurial philosophy. At the end it’s all in one’s skills together with determination.
When I wrote :
“To melt away into the crowd appears to be an interesting approach in society but a lousy one when it comes to the systematic tracking by means of fingerprinting on the Web.”
I should have wrote, of course :
“To melt away into the crowd appears to be a questionable approach in society but a pertinent one when it comes to the systematic tracking by means of fingerprinting on the Web.”
Being dyslexic with arguments is highly problematic :)
@ otm wahakc
same here :P