7-Zip vulnerability affects security software
7-Zip is a popular open source file compression program that supports all major compression formats and support for a variety of other features.
Talos, a Cisco company, discovered a vulnerability in 7-Zip that allows attackers to run code on computer systems that has the same rights as the underlying process.
To be precise, the vulnerability was found in the code that handle Universal Disk Format (UDF) files in 7-Zip.
It is the default file system for DVD video and DVD audio, and used for other optical disc formats.. The vulnerability takes advantage of flawed input validation. If you are interested in details, follow the link to the Talos blog that reveals the two vulnerabilities found in the subsystem.
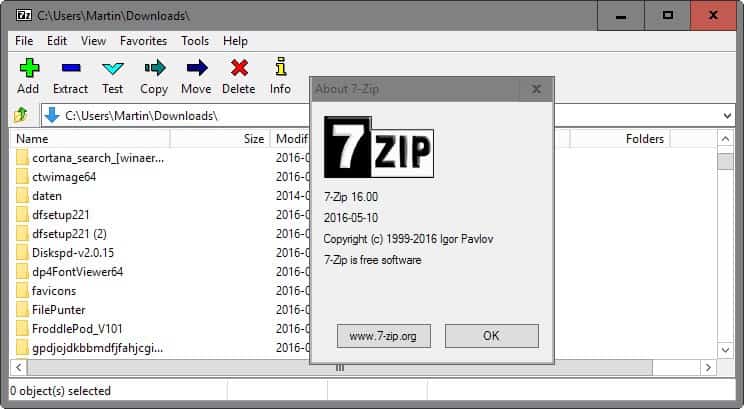
The security vulnerability has been fixed in 7-Zip 16.0 which has been released this month.
The issue
If you are using 7-Zip you should update the program immediately to protect the system from attacks targeting the vulnerability.
The main issue however is that third-party programs make use of 7-Zip's libraries as well. This includes many compression programs, security software from Malwarebytes, and other programs that offer or use compression functionality.
If those programs use pre-7-Zip 16.0 functions, then they are also vulnerable to the attack. This is of special importance when it comes to security software as it may run with elevated rights while other programs may not necessarily.
Since the code that the a successful exploit runs on the system uses the same rights as the host process, consequences can be more far reaching because of it.
What makes this particularly problematic is that there is no way of finding out whether a program that you are using is making use of 7-Zip functions or not. There is no master list of programs that use 7-Zip for compression functionality, and many developers and companies don't disclose if 7-Zip is being used.
One of the first programs to fix the issue is the popular file compression program PeaZip. It was just updated to fix the 7-Zip vulnerability. It is likely that other programs will be updated in the near future to use the new fixed functions that 7-Zip provides instead of the vulnerable ones.
Until that happens though, they and with them the underlying system remain vulnerable to the attack.

















The tricky thing with these two vulnerabilities is the fact, that 7-Zip or any application using their library, can trigger the bug even when the user is careful to avoid using any UDF/HFS files/images. As another commenter writes on the Cisco Talos blog post “These bugs will trigger with a malformed UDF/HFS file with a .zip extension unless the added command line argument is used”.
Or in other words: the reasonable vulnerability vector is to mislabel a file and try to get the user to open/access it with an application that uses the 7-Zip library. I know its use is incredibly wide-spread and I assume that many of those haven’t been updated yet.
This is a prime illustration of why I run SUMo at least once a day — more typically, once in the morning and once in the evening — and try to keep my system as up to date as possible. Thanks to this practice, I had updated 7-zip before the story broke.
Is anyone still using Secunia PSI? It’s an update-checker that focuses exclusively on security (not functionality or bug-fix) updates. I stopped using it a while ago for a number of reasons (e.g., it was slow on my system, its auto-updating feature was problematic, Secunia got bought out by a company whose privacy policy seemed confusing). I’m curious to know whether anyone who uses it (either in background or on demand) has been getting timely warnings about programs with the 7-zip vulnerability.
Now, here is something that worths being updated (…not those windows updates)
I’ve been using 7-zip for a long time and I updated to v16 a couple days ago, prior to reading this article.
Since 7-zip alternatives uses 7-zip.dll they also got the vulnerability.
I’ll stick with 7-zip until some command line compression tool as-powerful-as 7-zip comes up.
The alternatives we have today have a fancy gui and little command line support.
Thks for the info
It’s done
Thnx, updated :)
Is 7-zip
for Linux also vulnerable by this?
Is Bandizip one of the 3rd party programs that uses the 7-Zip libraries?
Yes. In my case – Bandizip and MBAM 1.75 .
Later I’ll try to replace 7z.dll in MBAM Program Files folder with 7z.dll from 7-zip Portable 16.0 .
Doing searches for *7z* on my system, I see:
Malwarebytes (others have reported/noted this)
Adobe Reader
ComicRack
CDisplayEX
Andy (Android emulator)
IZarc
Autopatcher
and a few more…
This is going to be ugly. 7zip was the go-to-source for a free .ZIP/.7Z library for *LOTS* of programs.
I found 7-Zip in
Bandizip
DropIt
MBAM
WinMerge
7-Zip Portable 16.0 : http://portableapps.com/news/2016-05-13–7-zip-portable-16.0-released
Thanks for the heads up Martin!
This issue may turn out to be MASSIVE.
There are thousands of applications used by hundreds of millions of people that use 7-Zip libraries.
Getting all those applications updated will likely be a very slow process.
Applications that are no longer under active development may be forever vulnerable.
Hopefully the 7-Zip developers will release drop-in patched replacements for affected libraries. That way, at least savvy users can replace some of their vulnerable libraries.
This will be a boon for blackhats and security agencies.
They could release a tool that scans and updates anything on your system. But they won’t.
So, it’s just the malwarebytes that uses affected libs or some other security software is doing the same?
Malwarebytes isn’t the only one effected by this, far from it in fact.
To name a few things that use the 7-zip libraries there’s FireEye, Comodo Cloud Antivirus, Nero software products, IBM Endpoint Manager, Gpg4win, Acronis, Nullsoft Scriptable Install System, Java, TeamViewer, Symantec, and the list goes on and on.
Does some software change the names of the used 7-Zip components? If not, why not just replace them?
Search for 7z* (eg. via Everything), download 7-Zip installer, replace the found files with the ones from the installer.
Or could this lead to problems?
I don’t know how the libraries get integrated so cannot say if this could work or not.
Ok, so far WinMerge didn’t like that I replaced the 7z.dll
Bandizip was fixed in the meantime btw.
I replaced them, no crashes or abnormal behaviour so far. At least none noticed.
Phew….
I’ve fresh installed win 2 days ago
and yesterday fresh installed 7z…
I don’t always look for new versions, as my PC is old and sluggish, but in this [and few more] case[s] this time – i did :)
got me worried for a sec :D
Keep up the good info streaming M.B. =]
Trying my best ;)