Security Paper suggests to remove McAfee from PCs, finds issues in OEM devices
A recent security analysis of OEM laptops running Windows 10 by Duo Security Inc concluded that all analyzed devices had privacy and network protocol related issues.
The seven laptops, produced by Dell, HP, Lenovo and Acer, shared many of the privacy and security issues, while some laptops had additional issues caused by installed OEM software.
The team looked at the network traffic that each device produced, and noticed -- among other findings -- the following:
Finding 1
Six of the seven laptops came with McAfee security software pre-installed. The researchers discovered that systems the software was installed on connected to a third-party tag server on the Internet.
Tags allow for management of cookies, tracking a browser/computer/user across time and space for marketing purposes, helping a vendor comply with “Do Not Track†settings in browsers, allow for the management of content such as new product offerings based upon numerous factors including time (like the first 30 days of a trial that starts after you power on your computer for the first time).
Odds are that McAfee is mainly using tags for the latter, but as I could find no documentation anywhere about how they are actually using it, I am assuming they are gathering at least some data from users
Suggestion: Uninstall McAfee software and use another security solution instead.
Finding 2
Automated network services put the computer at risk as soon as it started to talk on a network.
The researchers found the following protocols or services to be problematic from a privacy or security perspective:
1. Link Local
Link-local is an older protocol. In basic terms, it allows for a network interface to “self-configure†an IP address when other methods are absent (such as DHCP) or have simply failed (unable to read a config file).
However, when a wireless network interface is introduced, the local network segment is now confined by how powerful the wireless network interface actually is. This means that an attacker could conceivably start manipulating the wireless “local network†as they see fit.
2. WPAD and LLMNR
WPAD is really trying to make things easier for the end user. One common thing for the computer to ask is “where is the web proxy so web browsing will work?†WPAD is the one that asks the question and fields the answer. The issue - much more prevalent for wireless - is that anyone nearby could provide that answer, even when no proxy is required.
LLMNR is the IPv6 version of link-local, and as we mentioned previously an attacker could answer some of those important questions the victim computer is asking, allowing for the manipulation of traffic to the attacker’s advantage
3. Smart Multi-Homed Name Resolution
Smart Multi-Homed Name Resolution remembers what DNS server is the quickest. You connect up to the Wi-Fi at the coffee shop, the DNS for the coffee shop is deemed the fastest (probably by default), and then you connect up to the VPN at work.
Sure, your DNS requests are now going over the VPN, but a copy of the requests are still being sent to that coffee shop DNS, leaking DNS queries to the coffee shop’s ISP, or to anyone else in the coffee shop sniffing the Wi-Fi.
4. Teredo Tunneling and ISATAP
Teredo Tunneling and ISATAP are both technologies that build upon the same territory laid down by our friend link-local. Both are intended to help the computer operate IPv6 in IPv4-only and IPv4/IPv6 mixed environments respectively. However, if you plan on taking your new laptop to the coffee shop (or any other place with free Wi-Fi), there is an inherent danger of MITM attacks
Fixes for these issues:
Tap on the Windows-key, type regedit.exe and hit enter. You may need to confirm an UAC prompt before the Registry Editor opens. Keep it open until you are done disabling all features below.
To disable LLMNR
- Navigate to the key: HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT
- Right-click on Windows NT and select New > Key.
- Name the key DNSClient.
- Right-click on DNSClient and select New > Dword (32-bit) Value.
- Name the Dword EnableMulticast.
- Set its value to 0.
To disable Smart Multi-Homed Name Resolution
- Navigate to the key: HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\DNSClient
- Right-click on DNSClient and select New > Dword (32-bit) Value.
- Name the Dword DisableSmartNameResolution.
- Set its value to 1.
- On Windows 10, the following is required as well.
- Navigate to the key: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Dnscache\Parameters
- Right-click on Parameters and select New > Dword (32-bit) Value.
- Name it DisableParallelAandAAAA.
- Set its value to 1.
To disable WPAD
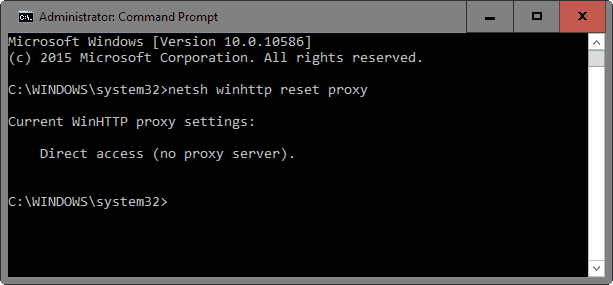
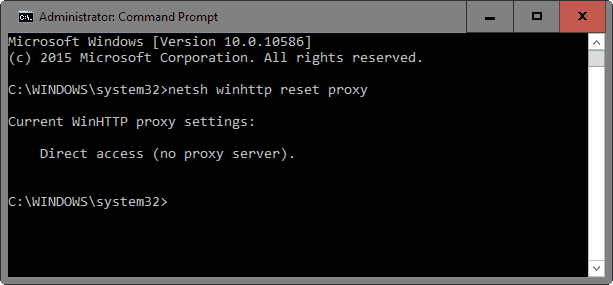
- Tap on the Windows-key, type cmd.exe, hold down Shift and Ctrl, and hit enter. Confirm the UAC prompt. This opens an elevated command prompt window. Keep it open after you run the following command.
- Run the command netsh winhttp reset proxy.
- Tap on the Windows-key again, type services.msc and hit enter.
- Locate the WinHTTP Web Proxy Auto-Discovery Service and stop it if it is running by right-clicking on it and selecting "stop" from the context menu.
- Double-click on the service to open its properties and change its startup type to disabled.
- Switch to the Registry Editor and navigate to the key: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\Tcpip\Parameters
- Right-click on Parameters and select New > Dword (32-bit) Value.
- Name it UseDomainNameDevolution.
- Set its value to 0.
Disable teredo tunneling and ISATAP
- Switch to the elevated command prompt window and run the following commands
- netsh interface teredo set state disabled.
- netsh interface isatap set state disabled.
Finding 3
Privacy related settings were reset after certain updates were installed on machines running the Windows 10 operating system.
Since it cannot be helped, it is suggested to go through the Settings after updates are installed to make sure they have not been reset.
Closing Words
If you notice issues after making changes to the computer running Windows, then it is suggested to remove the Registry keys that you have created, and to change the state of services to enabled again.

















Hi Martin, thanks for the article.
“To disable LLMNRT” is a typo? Should be LLMNR, right?
What about fixing “Link Local”? I don’t see fix for it.
You are right, fixed.
Ok, but what about the other thing? Where is the fix guide for “Link Local”?
You have these problems/issues listed:
1. Link Local
2. WPAD and LLMNR
3. Smart Multi-Homed Name Resolution
4. Teredo Tunneling and ISATAP
But the fixes section only has these:
1. LLMNR
2. Smart Multi-Homed Name Resolution
3. WPAD
4. Teredo Tunneling and ISATAP
Where is the fix for “Link Local”?
I don’t have a fix for that. If you stumble upon something let me know.
I had the time to read the PDF these security researches published and it make for enlightening reading, how a lot of the “necessary” traffic that people point to and claim is normal for Windows 10/8.x to be sending just increase the attack vector, something that was probably already known but it’s good to have proper research done.
Question:
Martin, do these issues only apply to Win 10 or also to, let’s say Win 8.1 ? I don’t want to start fiddling with my reg if not necessary. Thank you.
Also to Windows 8.1 as far as I remember reading.
Absolutely no problems if you use Emsisoft
Windows 10 Codename Threshold has NO issues whatsoever. It does the NSA work in a splendid way.
McAfee seems to integrate even better with NSA requirements to hunt down potential terrorists and future customers of NSA-Friendly Corporations. Sorry but McAfee… is yours complete negligence?
“Do Not Track†is a joke! Go Private Browsing instead.
Responder is a LLMNR and NBT-NS poisoner, with built-in HTTP/SMB/MSSQL/FTP/LDAP rogue authentication server:
https://github.com/SpiderLabs/Responder
This python script totally owns a local client… Wonder if some three-word-letter agency could do it remotely? I mean, SURE.
So, McAfee is voluntary adhering to official spying standards?
Is it me or does it seem like Windows 10 has a lot of issues.
@Rockin’ Jerry, Either posted a reply to the wrong article or doesn’t know McAfee (bought by Norton ages ago) has nothing to do with Windows 10. :?
@Martin, Sorry i must have mixed up McAfee with one of the many companies Norton has bought up over the years, i wonder if all those OEM’s get any kickbacks from Intel for including McAfee like discounts on CPUs.
McAfee was acquired by Intel ;)
ANOTHER WINDOWS 10 TROLL ..GETTING OLD