Malwarebytes Anti-Ransomware Beta is out
Malwarebytes Anti-Ransomware is a new product by security firm Malwarebytes designed to protect Windows systems against so-called ransomware attacks that has been released as a beta version to the public two days ago.
Malwarebytes continues to expand its portfolio. After releasing Malwarebytes Anti-Exploit some time ago to complement the company's popular Anti-Malware product for Windows, it has now released the first beta version of Anti-Ransomware.
Malwarebytes Anti-Ransomware is available as a public download from the official forum of the company.
It needs to be noted that it is available as a beta version which means that it is not suitable for production environments right now.
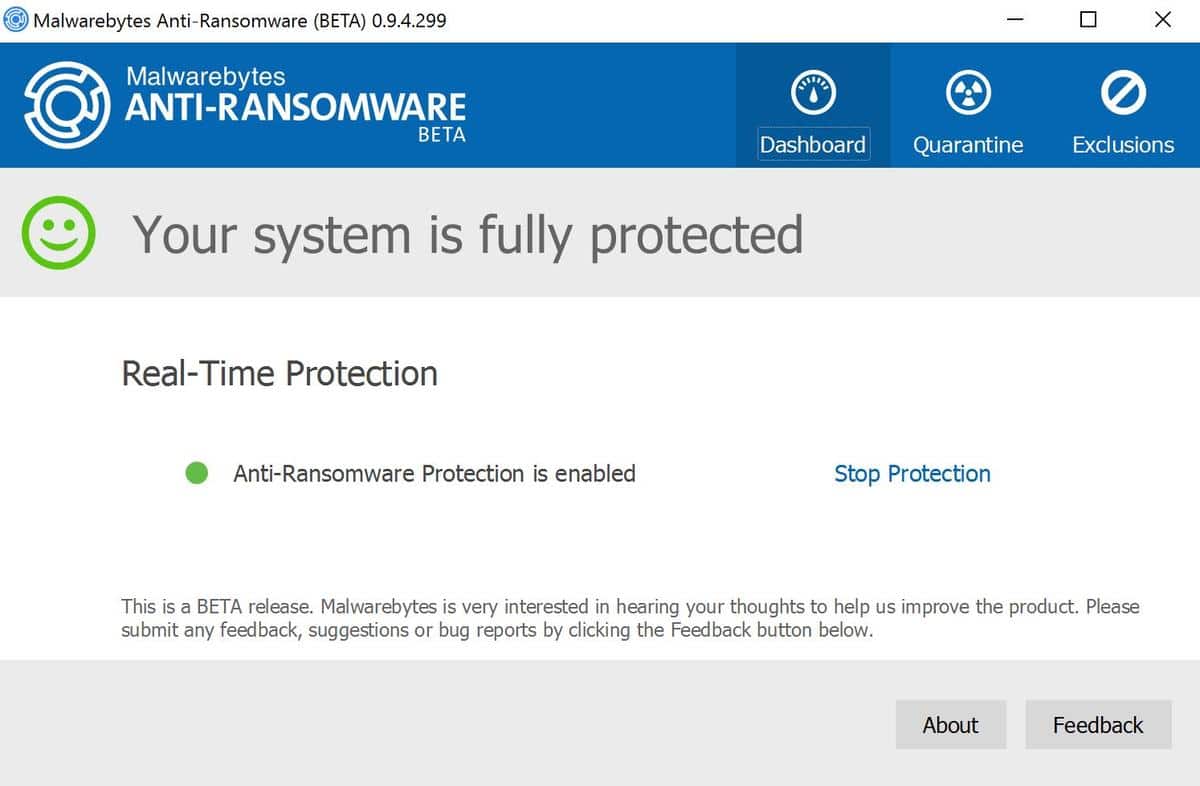
Malwarebytes Anti-Ransomware
The program has a size of more than 50 Megabytes which is quite large especially if you compare it to the company's other products.
The program itself runs in the background for the most part monitoring activity on the system to identify actions typically associated with ransomware.
According to Malwarebytes, it is proactive and not dependent on signatures. It will detect and block many dangerous ransomware variants.
[..] this beta is extremely exciting as it introduces the most innovative approach in the market today for protecting against ransomware; a completely proactive and signature-less technology that is able to detect and block even the most dangerous of ransomware variants like CryptoWall4, CryptoLocker, Tesla, and CTB-Locker.
The software will prevent the encryption of data on the system by ransomware, by quarantining processes or threads that attempt to infect the computer with ransomware.
The company notes that Malwarebytes Anti-Ransomware did block every single ransomware variant that it tested against it.
Malwarebytes Anti-Ransomware monitors all activity in the computer and identifies actions which are typical of ransomware activity. It keeps track of all activity and, once it has enough evidence to determine a certain process or thread to be ransomware, blocks the infection and quarantines the ransomware before it has a chance to encrypt users' files. During development Malwarebytes Anti-Ransomware has blocked every single ransomware variant we have thrown at it.
No information about the tested ransomware strains were provided so that it is unclear how many different types of ransomware Malwarebytes tested its product with.
The software interface is simplistic. It offers an on-off switch, a quarantine tab that you can use to check all detected infection attempts, and a tab for exclusions which can be useful if you want to make sure that certain processes or files are not detected as ransomware by the application.
Beta users are encouraged to check the list of known issues. Probably the most serious of those are that Malwarebytes Anti-Ransomware won't be installed when users upgrade from Windows 8 to Windows 10, and that some ransomware may still display background information or dropped html/txt files with ransom instructions even if no files were encrypted by the ransomware process.
Closing Words
Malwarebytes Anti-Ransomware could become another interesting product by the company. It is likely that Malwarebytes will release a limited free and paid premium version of the program after the beta test but no information have been provided about this yet.

















Compared to eSupport – Trend Micro inc.AntiRansomware Tool 3.0 with USB would you choose for?
https://esupport.trendmicro.com/en-us/home/pages/technical-support/1098354.aspx
Today I was installing some updates and a message pops up, it says, RANSOM WARE DETECTED! Ok, sure. It detected Microsoft’s Office Click-To-Run. It runs thru its little process and says it fixed the issue. The software I had been installing required a reboot. I reboot and as soon as the desktop appeared a box pops up, RANSOM WARE DETECTED! Two more Office files, it removed them without giving an option to keep them. While this is going on I click on Outlook, it fails to open. Go into the Malwarebytes app, restore the file and Outlook was still broken. Go to run a repair via Programs & Features…Office 2016 is no longer in the list of installed applications. Uninstall the Malwarebytes application. Run System Restore, Outlook was still broken. Needed to reinstall the entire Office 2016 suite from original media…good news is that worked.
TL;DR : a beta anti-ransomware app killed my Office 2016
The same thing has just happened to me — 3 months later.
You’d figure they’d have fixed it.
The same happened to me today !! I stopped the process : Microsoft Office Click-To-Run, and after that i tried to start Outlook again and that worked.
Something must be done to fix this.
Benny
@rickxs and @Heinz Iten: You guys need to report this their support forum: https://forums.malwarebytes.org/index.php?/forum/172-malwarebytes-anti-ransomware-beta/.
I did, but they ignore it – no answers.
I also gave it a try and it quarantined Comodo Program Manager when uninstalling a program– Tried to “restore” it from quarantine but nothing in there –
I’ll stick with Bitdefender also
I have installed this beta program, and regretted it immediately. I have an Administrator account (Windows 7 x64 Ultimate), which I only use when I fiddle with something. I also have a user account, which does not have administrator rights, and which I always use when I want to do some work. Both are password protected (both different passwords).
After installing MBAR my user account got screwed up, and I was left with only the Administrator account. Fortunately I had a backup image of the system partition, which got me out of trouble again.
It seems this program is far from ready for prime time.
I hope somebody from Malwarebytes reads this, and does something about it.
Please be kindly educated that, currently, some legal software like some so-called system optimization programs are following the said term “Ransomware”. Personally, they are using the same tricks to pop up totally misleading or false information, such as disk/ system/ application error. The Trojan Horse powered fakealerts are, of course, worse, they won’t unlock a victim’s screen before they are paid.
How does this compare to the Bitdefender Anti-Ransomeware Product? MWB seems more comprehensive. You think one could run alongside the other without issue?
Ugh. Gave it a try and it quarantined Firefox.exe. Tried to “restore” it but apparently items marked for deletion cannot be restored (!). It must be restarted to complete the removal (which is fine), so I thought I would just uninstall the program and that would be that. However I had in a Windows update in the queue and after a restart Firefox was gone and had to be reinstalled.
While I realize it’s still in Beta, for now I’ll stick with Bitdefender.
Beyond stability, this really is the question. Will it play well with others? – EMET, CryptoPrevent, MWBAE, BitDefender Anti-Ransome, standard AV protections, etc.? And if so, is the responsiveness loss worth doing so?
I guess the program monitors processes to see how many files it is writing to and how quickly, e.g. if it writes to 100 files within a minute it blocks it, and other variables such as location and size.
Why does malwarebytes keeps on releasing new products instead of integrating them into malwarebytes pro? This product along with anti exploit should be included with malwarebytes instead of forcing people to pay for 3 different licenses. Pretty cynical move by malwarebytes. 24.95 x 3 = 74.85 a year for “complementary” protection, put in that perspective it is kinda ridiculous. Also since its “complementary” when people actually test said products and they fail, malwarebytes just waves saying that it is only “complementary,” or request they be withdrawn from any more test and say you should download an AV too.
This is a beta product. It has not been tested, and it needs to be tested before it will make its way into a release product. Whether they will charge money for it is yet to be determined. Whether it will be integrated into MBAM Pro is also yet to be determined. Right now the Beta is free for use. The free versions, in any case, do not leave out much of the good stuff anyway.
Well, my guess is that it is lucrative to offer multiple products. Customers who have bought Anti-Malware Premium, may be inclined to purchase the other products as well.
Hi Martin. Totally off-topic as I take the opportunity here to send you a big “Hello” from good old Europe, hoping your holidays are most pleasant. And thanks for staying nevertheless connected. Do relax, we wont mess around the place, promised :)
The vacation is really nice, thank you :)
I have mixed feelings about this product, though I admit that I have not tried it. Malwarebytes products tend to be good. I like their clear user interface designs, and I know their basic antimalware app has a good reputation. (In fact I use it on Android, and in the past I used it in Windows). So I commend the company for trying to tackle ransomware.
But I also feel that antimalware programs give people a REALLY false sense of security. These programs cannot catch everything. In fact, some of these programs can hardly catch anything. O_o Also, despite all the talking points about “heuristics”, I don’t believe these products are very good at identifying zero-day malware.
The *real* antimalware solution involves:
-informed and intelligent user behaviour (are you still clicking things you shouldn’t be clicking? visiting sites you shouldn’t be visiting? installing software you shouldn’t be installing?)
-a good software firewall behind a good hardware firewall
-sandboxing of internet clients
-a hardened operating system (including the separation of user and root accounts)
I think it’s more important to do these things than to have a third-party antimalware program. If you’ve done these things and still want more protection, by all means download the Malwarebytes beta and give it a try.
@Jason: I’m with you, I’ve actually lived without an AV/AM suite for awhile and wasn’t effected by anything malicious. But I think most people just feel safer having an AV/AM scanner on hand so they can do a good second round security sweep of their OS.
Agreed: all of these steps you outlined above are vital to protect your system (especially user behavior).
But when it comes to products like Malwarebytes, an extra layer (in addition to the steps you outlined above) probably can not hurt.
Strangely however, despite my agreeing fully with you, I find it very difficult to bring myself to run as a limited user, rather than administrator. I guess I like to have full control of my computer!
And so I guess that will come back to bite me in the @ss one day. But so far so good: my last infection with malware, that I am aware of, was probably about 7 years ago. And as you said, user behavior is the key factor in that track-record, especially in terms of simply not clicking on things you shouldn’t.
Ouch! I have trouble understanding why someone stays logged in as an admin user ‘to have full control of their system’. Besides a quick login switch, there are many options for running programs, say installers, as administrator.
I have *very* few older applications that only run as admin, which I start up with a graphical shell that prompts for a password. If I wasn’t tight fisted with my $$$ I would upgrade these programs or find an alternative.
Several engineers told me that the firewall was far more important than anti-malware software, as you point it out. Moreover, a hardware firewall is most advised : “steel to not be stolen” (steel, double “e”!). Concerning sandboxing I’ve read that it could not always be as promising as it sounds.
But, even with a strong defense, brains is required and often makes the difference, even if not always. Both, “masterware” and mastermind make a good team : together they can :)
Far too many users believe, as you mention it, that their software protectors enable them to move around sites (and downloaded applications) with no risk. Risk zero does not exist and believing so increases one’s vulnerability.
i dont know why you promote malwarebytes products when we all know they stole from their costumers last year…
@Woomera: Yes what are you talking about? I think I would’ve heard this if such thing ever took place, especially since I’m a register member of their forum. I also think Martin Brinkmann would’ve covered this.
What are you referring to?
I reckon he is referring to this:
https://support.malwarebytes.org/customer/portal/articles/1834849?b_id=6438-#can-i-buy-lifetime
I wouldn’t call it stealing personally.
May be interesting because ransomware is among the most frightening threats and can be devastating.
At this time I rely on SurfRight’s HitmanPro.Alert (which can run alongside the better known HitmanPro) and an annual fee offers the complete arsenal in what seems to be a rather innovative and (I hope!) strong protection against zero-day exploits and substantially against ransomware attempts.
I may have a look at this Malwarebytes Anti-Ransomware (Beta).
You are correct, this stuff is bad news and now it appears the ransom fee is going up from the usual 1 or 2 bitcoins to 13 btcs (approx $5000) as demanded by the author of a variant which supposedly does extensive damage to the operating system in addition to file encryption..
Now running MBRW alongside EMET, no hiccups so far.
if it was real economy and if windows was a real product and microsoft was real company there would be class action lawsuit by the government on behalf of consumers against microsoft putting it out of business. Of course if there were any such lawsuit in the future it would be just a sham spectacle to funnel money.
Yeah this is juju, the nonsense talker. Man, if your going to talk crap about Malwarebytes, could please explain it in plain English.
I think Juju has been sucking down too much Juju Juice, or spent too much time watching The X-Files. This way to your padded cell Sir…
@ juju – I suspect you missed taking your medications today…
the hell you talking about? I think you’re posting on the wrong page bro
>>>/out/
Great review and good to know more people are trying to stop this horrid type of infection. I wonder if anyone has done any real world testing to see what the detection rates are like and if they’re positive?