Emergency Patch for Windows vulnerability MS15-078 released (KB3079904)
Microsoft pushed out an emergency patch yesterday via automatic updates to all supported versions of its Windows operating system that patches a critical issue that could allow remote code execution when exploited successfully.
Specifically, the vulnerability exploits an issue in the Windows Adobe Type Manager Library when specially crafted documents with OpenType fonts are loaded on the system.
This may happen when users open malicious documents on the system directly or when they visit websites that use embedded OpenType fonts. Since ATM may be used by other programs besides Internet Explorer, it may affect systems where other web browsers are used to browse the Internet or open documents.
When successfully exploited, attackers can take control of the system by installing or removing programs, modifying user accounts or deleting data.
It is interesting to note that the patch replaces MS15-077 (KB3077657) which Microsoft released on July 14, 2015 which patched an elevation of privilege vulnerability in the Adobe Type Manager font driver.
The vulnerability affects all versions of Windows including the unsupported Windows XP and Windows 2003 versions. While Windows XP did not receive any of the two patches, Windows 2003 did receive the first of the two but not the second due to EOL of support.
Microsoft Windows XP and Windows 2003 admins and users may find the manual workaround instructions helpful on the official bulletin website which they may use to protect systems from exploits. The company suggests to rename the file atmfd.dll on pre-Windows 8 systems, and to disable the Adobe Type Manager on Windows 8 or later systems.
Rename atmfd.dll on 32-bit systems
cd "%windir%\system32"
takeown.exe /f atmfd.dll
icacls.exe atmfd.dll /save atmfd.dll.acl
icacls.exe atmfd.dll /grant Administrators:(F)
rename atmfd.dll x-atmfd.dll
Rename atmfd.dll on 64-bit systems
cd "%windir%\system32"
takeown.exe /f atmfd.dll
icacls.exe atmfd.dll /save atmfd.dll.acl
icacls.exe atmfd.dll /grant Administrators:(F)
rename atmfd.dll x-atmfd.dll
cd "%windir%\syswow64"
takeown.exe /f atmfd.dll
icacls.exe atmfd.dll /save atmfd.dll.acl
icacls.exe atmfd.dll /grant Administrators:(F)
rename atmfd.dll x-atmfd.dll
Disabling atmfd on Windows 8 or later
- Tap on the Windows-key, type regedit and hit enter.
- Navigate to the key: HKLM\Software\Microsoft\Windows NT\CurrentVersion\Windows\DisableATMFD
- If DisableATMFD does not exist, right-click on Windows and select New > Dword (32-bit) Value.
- Set its value to 1.
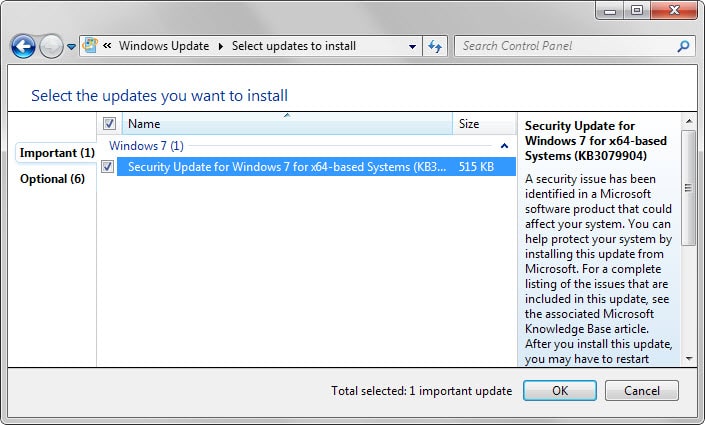
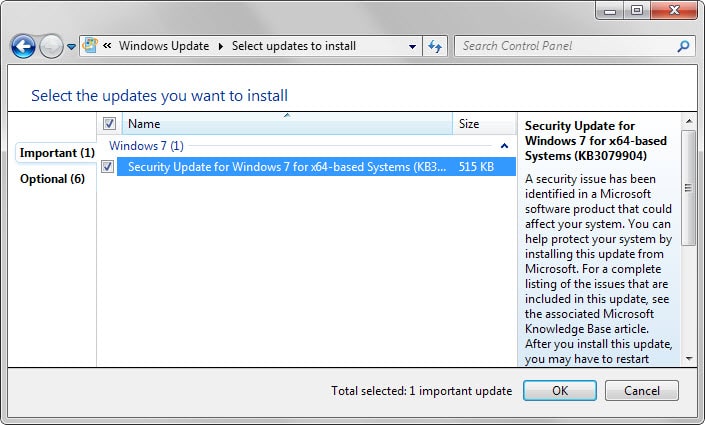
The patch that Microsoft pushed out today patches the vulnerability on all supported systems. It can be installed via automatic updates on Home systems of the operating system, or downloaded via Microsoft's Download Center. Download links for each affected operating system are provided under "affected software" on the MS15-078 support page.
Microsoft states that the vulnerability is public but that it is not aware of attacks making use of it currently. The emergency release nature of the patch indicates a high probability for the issue to be exploited in the near future.
The exploit was discovered after hackers leaked internal files of Italian company Hacking Team.
















Well, if removing/disabling atmfd.dll seems the (only) solution to the vulnerability within atmfd.dll: What is that DLL actually supposed to do and why is it part of Windows? Removing Type1 font support may not be a good idea for many users. Reminds me of removing the brain to cure headache …
As the auto-loading of web fonts seems to be the walk-in for the trouble, might it be wiser for people heavily using Type1 and/or PDF editing (with embedded Type1 fonts) to disable web fonts by default?
Plus: Does the MS fix replace the DLL with a patched one (and is the DLL the same on all Windows versions), or does Microsoft disable the DLL as well?
just remove it from registry
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Font Drivers
Adobe Type Manager REG_SZ atmfd.dll
and reboot
hey lolz,
exactly how did you modify the registry (for us non geeks)
did you try and open a document with Adobe open type fonts?
what happens? do you get an error message or does the system crash.
I like your solution if it works and does not destabilize the system
Thanks
I have it on good authority this update only fails on systems running ‘suspect’ versions of Adobe products.
Adobe are loosing their monopoly on the browser based flash plug-in (Firefox has discontinued using it in favour of HTML5 (about fucking time!) )
The person who told me about this is insisting that M$ have released this patch (in conjunction with Adobe) to lock-out and identify patched Adobe products, they are going to need all the money they can get now they can no longer harvest user data and sell it on via Flash Cookies so they are hoping all the users running ‘patched’ versions of Adobe (CS3, CS4, Cs5, Cs6 etc) and get them signed up to CC cloud based as they have no way to stop all the patched versions that are out their on the Net!
As always, it is always about money!
Goodbye Adobe and good fucking riddance you pile of bloatware, spyware, monopolising cunts
microsoft is a funny clown corporation
they wrote:
“Vulnerability in Microsoft font driver could allow remote code execution: July 16, 2015
How to obtain and install the update
This update is available through Windows Update.”
Today we have July the 22th. And I still got no message from my windows automatic update to install this update
fortunately I read the news, otherwise I would never hear of this vulnerability. Or I would get this update through my automatic update service in the next month after my computer is already controlled remotely
I love microsoft
Nice patch, after it was installed it turned off the activation key of my original windows and i must activate it again than it turned off the rootkit scanner of Malwerbytes Anti-malwer.
9904 completely hosed my system this morning.
Actually, a restore worked just fine — just irritated. I wish I would have read this earlier. Stupid patch tuesdays. Guess I’m BACK to ‘no auto downloads/installs’ …on a brand new laptop. Sweet. :/
Before you rename those files, you need to rename the file in \WINDOWS\ServicePackFiles\i386 first.
Also, you may have to do sfc /purgecache to make sure it doesn’t restore from dllcache.
it seems this kind of “fonts related” flaws happen a lot lately…
i stopped counting how many patches mentioning fonts exploits i’ve seen this year.
on another topic, would clicking on random ads on your site help you get more money than a basic whitelisting in adblock ?
i don’t really know how this works for you, and i would be glad to support a little bit more (but for free ;)
Using Agent Ransack to search my system for *atmfd*.* I get 26 hits in various directories dated over the past six years. Most of these files appear to be backup copies stuffed away for safekeeping by some system maintenance activity of which I was previously unaware. After the corrected copy of atmfd gets installed I hope that none of these vulnerable backups gets called up inadvertently.
Hi Martin and All,
OK, Any idea about why I can’t install KB3079904, even manually, on my Windows 7 64 bit desktop?
After running the downloaded Windows6.1-KB3079904-x64.msu and when it fails, I see these problems in View all problem reports in start menu:
Source Windows Modules Installer
Summary WindowsWcpOtherFailure3
Date 7/‎21/‎2015 4:33 AM
Problem signature
Problem Event Name: WindowsWcpOtherFailure3
OsVersion: 6.1.7601
File: base\wcp\componentstore\com\store_transaction.cpp
Function: Windows::COM::CComponentStore::ApplyTransactionNow
Line: 1841
Status: c000042a
StackHash: 0x8ec81db3
OS Version: 6.1.7601.2.1.0.256.1
Locale ID: 1033
Source Windows Modules Installer
Summary CbsPackageServicingFailure2
Date 7/‎21/‎2015 4:33 AM
Problem signature
Problem Event Name: CbsPackageServicingFailure2
Stack Version: 6.1.7601.18766
Package: Package_for_KB3079904
Version: 6.1.1.0
Architecture: amd64
Culture: unknown
Status: 80070308
Failure Source: Stage
Start State: Staged
Target State: Installed
Client Id: WindowsUpdateAgent
OS Version: 6.1.7601.2.1.0.256.1
Locale ID: 1033
any help will be greatly appreciated. Thanks
The easiest way to disable it on Win XP is to execute these two commands:
ren C:\WINDOWS\System32\dllcache\atmfd.dll atmfd.bak
ren C:\WINDOWS\System32\atmfd.dll atmfd.bak
After that it will ask you to insert the windows xp cd, just click cancel and it will ask you if you’re sure that you want to keep the files, click yes.
Everytime I rename atmfd.dll it just creates a copy with a new name, but atmfd.dll remains, what can i do?
@ams
I give up…
let em crackers try steal my info through fonts :)
btw, does disabling JAVA [through chrome\plugins has anything to do with this all :)
GL 4 all
no, don’t attempt to “do it quickly”.
Instead boot to SafeMode and remove, or rename:
C:\WINDOWS\System32\dllcache\atmfd.dll
C:\WINDOWS\System32\atmfd.dll
Afterward, or if you’ve similarly removed other dllcache -pathed files,
take care to NEVER run SFC (System File Checker) because SFC will attempt to replace the
missing files and will demand CD/DVD insertion if it fails to find ’em in …dllcache/ directory.
IIRC, an SFC “manifest” file exists and you can edit that file to nix references to the files you’ve removed.
I don’t recall where that manifest is pathed & personally avoid running SFC. In fact, after butting heads with it so many times, I think I ultimately renamed the SFC executable itself.
It has to be done quickly or Windows will just replace the files. Also the file may reside in ServicePackFiles\i386 as well.
So it’s best to put these commands in a batch file and execute it:
ren C:\WINDOWS\System32\dllcache\atmfd.dll atmfd.bak
ren C:\WINDOWS\ServicePackFiles\i386\atmfd.dll atmfd.bak
ren C:\WINDOWS\System32\atmfd.dll atmfd.bak
wow, nice, easy and short!!!
Tried it?
Thanks man!!
BTW, why is the answer to rename, and not just remove\cancel it’s purpose somehow instead?
:)
WIN XP, SP2
“C:\WINDOWS\system32> takeown.exe /f atmfd.dll
‘takeown.exe’ is not recognized as an internal or external command,
operable program or batch file.”
Takedown is only available in Vista and newer: https://technet.microsoft.com/en-us/library/cc753024.aspx
Check out this help article on taking ownership of files in Windows XP: https://support.microsoft.com/en-us/kb/308421
Oh, thought your textual\manual instructions were to help remove danger off of XP systems…
o.O
In other news, MSDN releases .NET Framework 4.6 (yet to be added to Windows Update but offline installation links are available) and Visual Studio 2015.
atmfd.dll is preinstalled with what program?
This is a bit over my head, but is in normal for computer Operating Systems to handle fonts in Kernel Land, or just Windows? That seems rather, umm, at risk of being exploited no?
So if you disable it you don’t have to patch it right….?
Thanks Martin.
Yes that seems to be the case.
Um the MS suggests to disable it. So if disabled you don’t have to patch it right…..?
Thanks Martin.
Patched. Thanks for the info, Martin. Especially when I have Windows Update disabled here.
So… Adobe again mentioned in the crime scene is it? It would be John Doe or Smith, one could state that the homonym explanation is valid, but not when it comes to Adobe : there ain’t (fortunately) no two Adobes!
I wonder when that company will ever resign, retire, coconuts daiquiri white sand and blue oceans… but move off from the Web. When?! Wann, sag, wann?!
I hear ya. Each time I see the name Adobe, regardless of context, my first thought is usually “friggin adobe @#$%”
I have an older (v5.5? v6?) licensed version of Photoshop that I occasionally use (in recent years, I don’t often find a need to use it) but, with the begrudging exception of Flash, I’ve learned to “remove, with extreme prejudice” any other Adobeware which finds its way onto my PCs. Umm, Shockwave (older Macromedia-branded version) might still be installed to a few of our older, seldom powered on, PCs.
ATM? AFM? Is AdobeTypeManager the same beast as AdobeFontManager? I recall that causing me a lot of grief on winXP. Also, IIRC, having it (ATM) installed/enabled along with Flash deepens the fingerprint-ability of your PC (per EFF privacy test).
Who the HELL decided it would be amenable to have such components enumerate (and exfiltrate) a manifest of installed fonts?!?
Recent Windows 10 version is slower than earlier Tech Preview, and a lot program can run on Windows 10 but not well enough.. Well, I doubt I will downgrade to Windows 7.
Hi… Now it’s my time to complain… It do not install on my desktop PC at all. either through Microsoft Update or downloading/installing it manually on my Windows 7 64 bit. It installed on my Lenovo laptop though. Whatever I do, I can’t get installed it on my desktop.
“Security Update for Windows 8 for x64-based Systems (KB3079904)
Installation date: ‎2015-‎07-‎21 06:24
Installation status: Succeeded
Update type: Important”
This harmful update created a new drive (H) on my system and forced me to use system restore and disable all Windows updates.
As usual Windows updates do more harm than good.