Secure your wireless router
There is no such thing as perfect security. Given enough knowledge, resources, and time any system can be compromised. The best you can do is to make it as difficult for an attacker as possible. That said there are steps you can take to harden your network against the vast majority of attacks.
The default configurations for what I call consumer-grade routers offer fairly basic security. To be honest, it doesn’t take much to compromise them. When I install a new router (or reset an existing), I rarely use the ‘setup wizards’. I go through and configure everything exactly how I want it. Unless there is a good reason, I usually don’t leave it as default.
I cannot tell you the exact settings you need to change. Every router’s admin page is different; even router from the same manufacturer. Depending on the specific router, there may be settings you can’t change. For many of these settings, you will need to access the advanced configuration section of the admin page.
Tip: you may use the Android app RouterCheck to test your router's security.
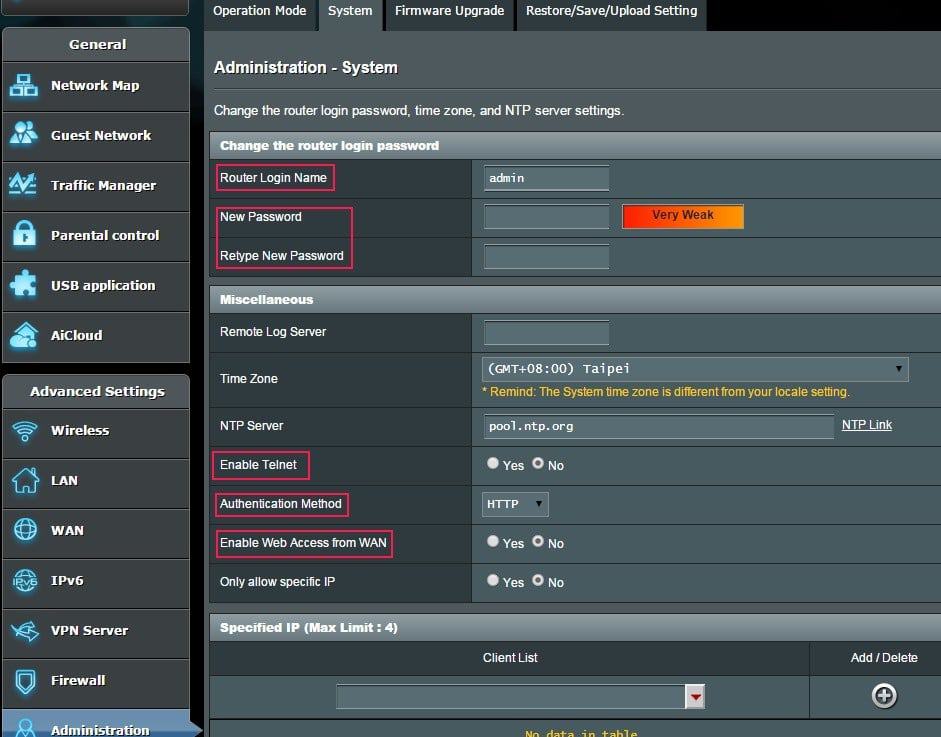
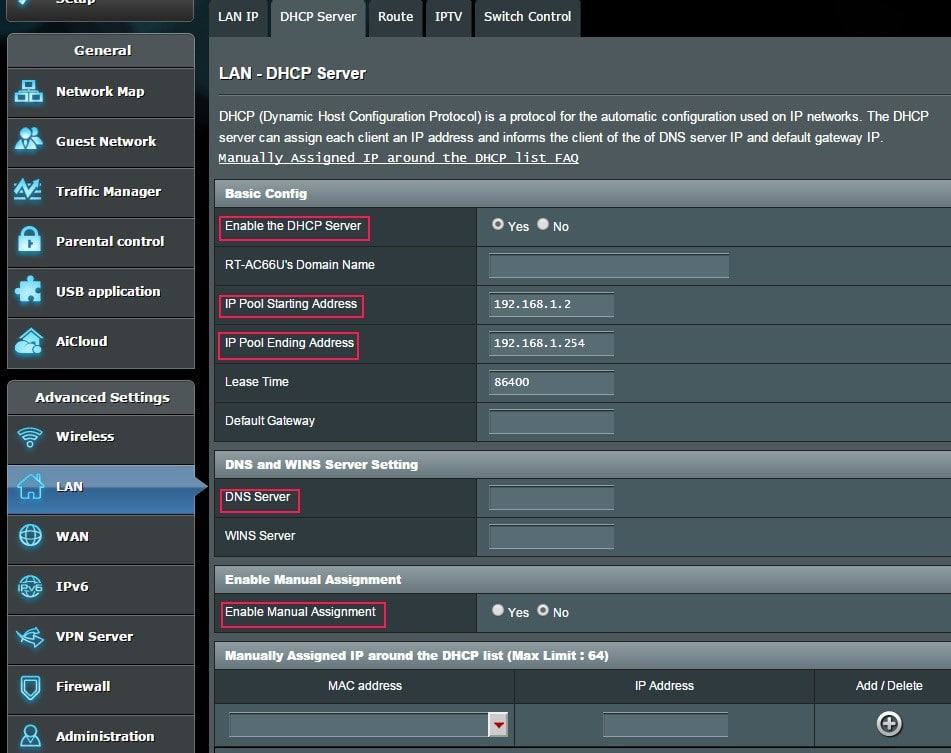
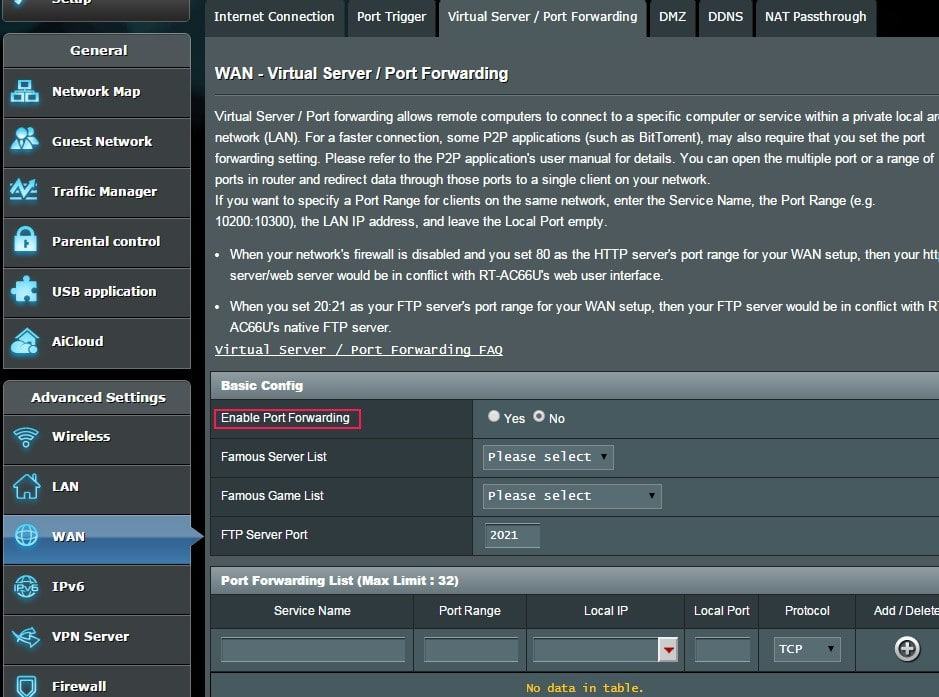
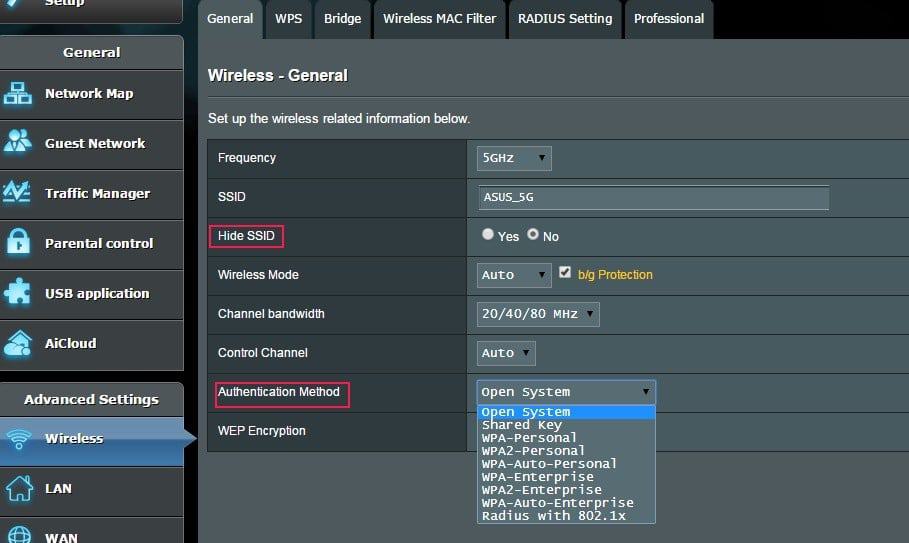
I’ve included screenshots of an Asus RT-AC66U. It is in the default state.
Update your firmware. Most people update the firmware when they first install the router and then leave it alone. Recent research has shown that 80% of the 25 top-selling wireless router models have security vulnerabilities. Affected manufacturers include: Linksys, Asus, Belkin, Netgear, TP-Link, D-Link, Trendnet, and others. Most manufacturers release updated firmware when vulnerabilities are brought to light. Set a reminder in Outlook or whatever email system you use. I recommend checking for updates every 3 months. I know this sounds like a no-brainer, but only install firmware from the manufacturer’s website.
Also, disable the router’s capability to automatically check for updates. I’m not a fan of letting devices ‘phone home’. You have no control over what date is sent. For example, did you know that several so-called ‘Smart TVs’ send information back to their manufacturer? They send all your viewing habits every time you change the channel. If you plug a USB drive into them, they send a list of every filename on the drive. This data is unencrypted and is sent even if the menu setting is set to NO.
Disable remote administration. I understand some people need to be able to reconfigure their network remotely. If you have to, at least enable https access and change the default port. Note that this includes any type of ‘cloud’ based management, such as Linksys’ Smart WiFi Account and Asus’ AiCloud.
Use a strong password for router admin. Enough said. Default passwords for routers are common knowledge and you don't want anyone to just try a default pass and get in to the router.
Enable HTTPS for all admin connections. This is disabled by default on many routers.
Restrict inbound traffic. I know this is common sense, but sometimes people don’t understand the consequences of certain settings. If you must use port forwarding, be very selective. If possible, use a non-standard port for the service you’re configuring. There are also settings for filtering anonymous internet traffic (yes), and for ping response (no).
Use WPA2 encryption for the WiFi. Never use WEP. It can be broken within minutes with software freely available on the internet. WPA isn’t much better.
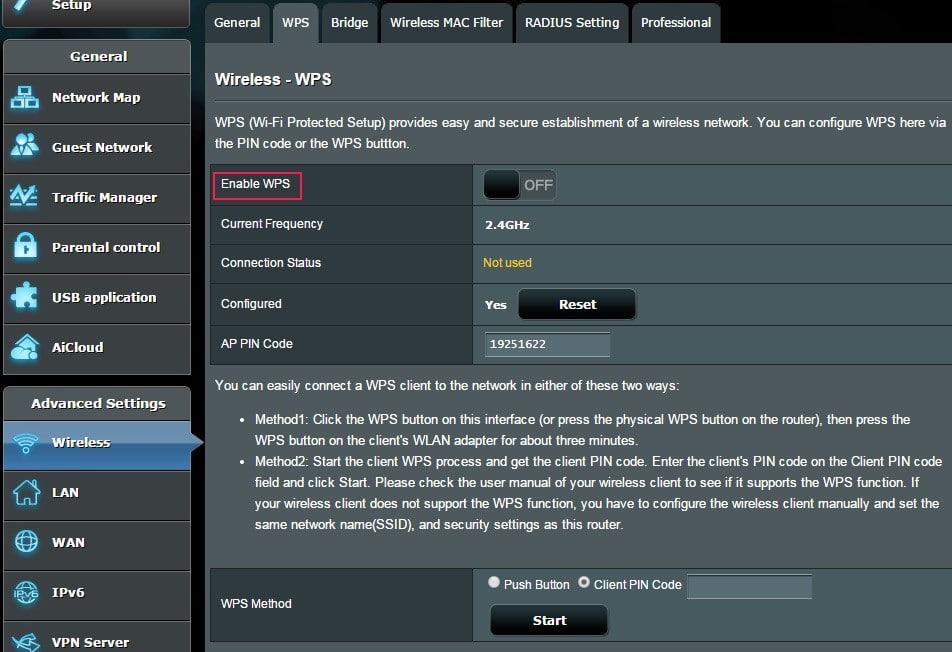
Turn off WPS (WiFi Protected Setup). I understand the convenience of using WPS, but it was a bad idea to start.
Restrict outbound traffic. As mentioned above, I normally don’t like devices that phone home. If you have these types of devices, consider blocking all internet traffic from them.
Disable unused network services, especially uPnP. There is a widely known vulnerability when using uPnP service. Other services probably unnecessary: Telnet, FTP, SMB (Samba/file sharing), TFTP, IPv6
Log out from the admin page when done. Just closing the web page without logging out can leave an authenticated session open in the router.
Check for port 32764 vulnerability. To my knowledge some routers produced by Linksys (Cisco), Netgear, and Diamond are affected, but there may be others. Newer firmware was released, but may not fully patch the system.
Check your router at: https://www.grc.com/x/portprobe=32764
Turn on logging. Look for suspicious activity in your logs on a regular basis. Most routers have the capability of emailing the logs to you at set intervals. Also make sure the clock and time zone are set correctly so that your logs are accurate.
For the truly security-conscious (or maybe just paranoid), the following are additional steps to consider
Change the admin user name. Everyone knows the default is usually admin.
Set up a ‘Guest’ network. Many newer routers are capable of creating separate wireless guest networks. Ensure it only has access to the internet, and not your LAN (intranet). Of course, use the same encryption method (WPA2-Personal) with a different passphrase.
Do not connect USB storage to your router. This automatically enables many services on your router and may expose the contents of that drive to the internet.
Use an alternate DNS provider. Chances are you are using whatever DNS settings your ISP gave you. DNS has increasingly become a target for attacks. There are DNS providers who have taken additional steps to secure their servers. As an added bonus, another DNS provider may increase your internet performance.
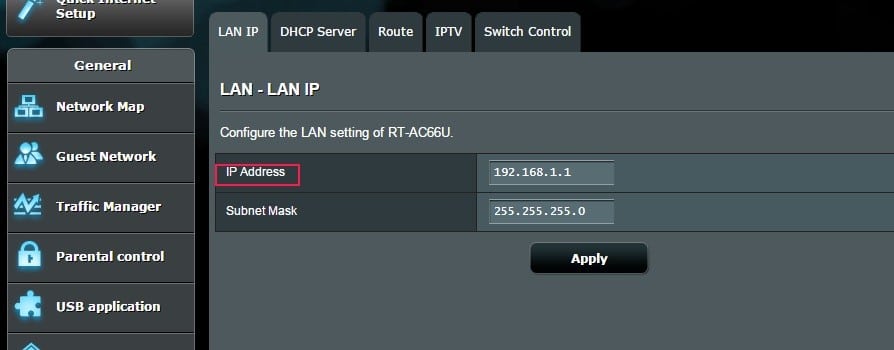
Change the default IP address range on your LAN (inside) network. Every consumer-grade router I’ve seen uses either 192.168.1.x or 192.168.0.x making it easier to script an automated attack.
Available ranges are:
Any 10.x.x.x
Any 192.168.x.x
172.16.x.x to 172.31.x.x
Change the router’s default LAN address. If someone does gain access to your LAN, they know the router’s IP address is either x.x.x.1 or x.x.x.254; don’t make it easy for them.
Disable or restrict DHCP. Turning off DHCP is usually not practical unless you’re in a very static network environment. I prefer to restrict DHCP to 10-20 IP addresses starting at x.x.x.101; this makes it easier to keep track of what’s happening on your network. I prefer to put my ‘permanent’ devices (desktops, printers, NAS, etc.) on static IP addresses. That way only laptops, tablets, phones, and guests are using DHCP.
Disable admin access from wireless. This functionality is not available on all home routers.
Disable SSID broadcast. This is not difficult for a professional to overcome and can make it a pain to allow visitors on your WiFi network.
Use MAC filtering. Same as above; inconvenient for visitors.
Some of these items fall into the category of ‘Security by Obscurity’, and there are many IT and security professionals that scoff at them, saying they are not security measures. In a way, they are absolutely correct. However, if there are steps you can take to make it more difficult to compromise your network, I think it’s worth considering.
Good security is not ‘set it and forget it’. We’ve all heard about the many security breaches at some of the biggest companies. To me, the really irritating part is when you here they had been compromised for 3, 6, 12 months or more before it was discovered.
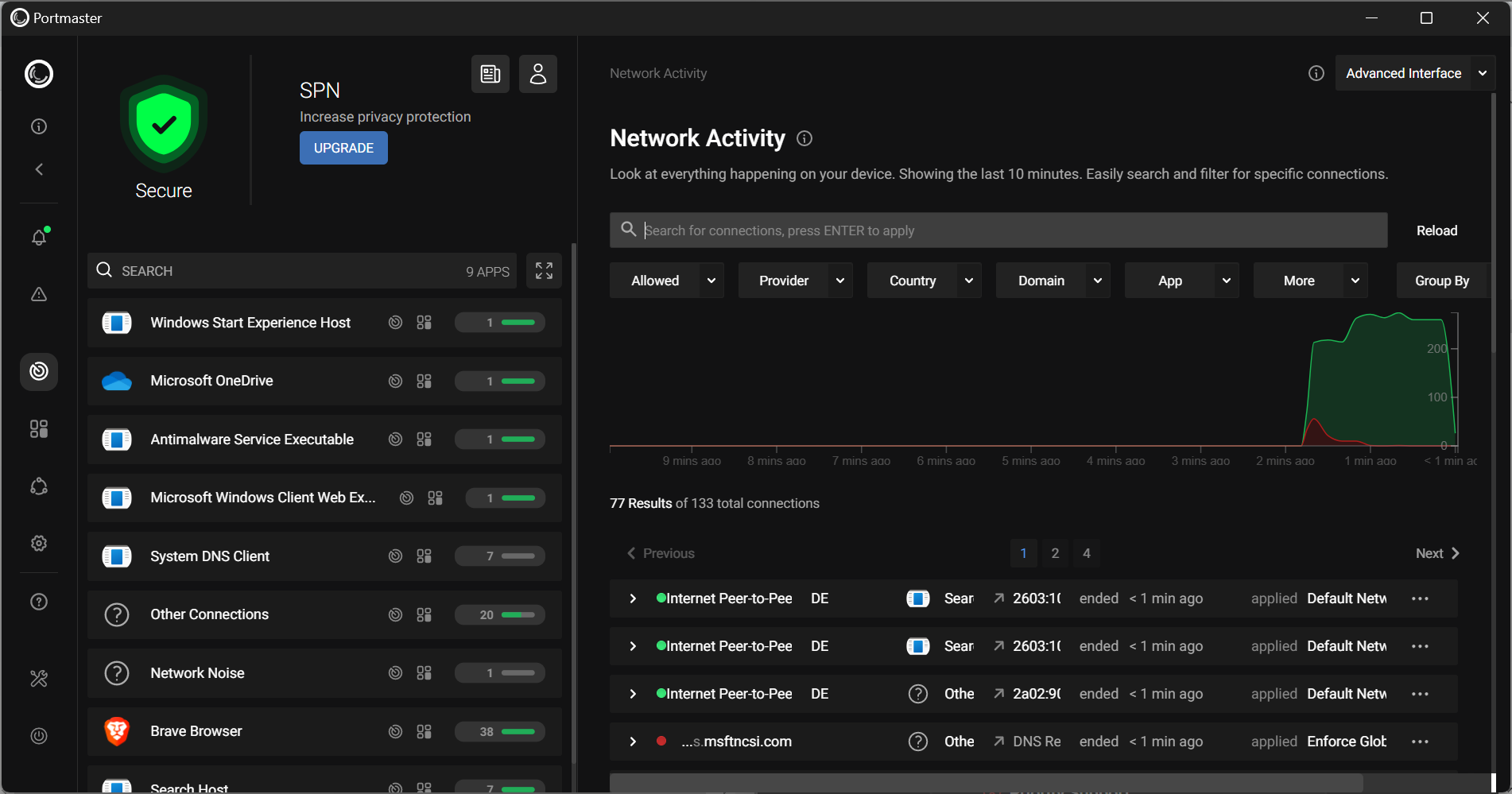
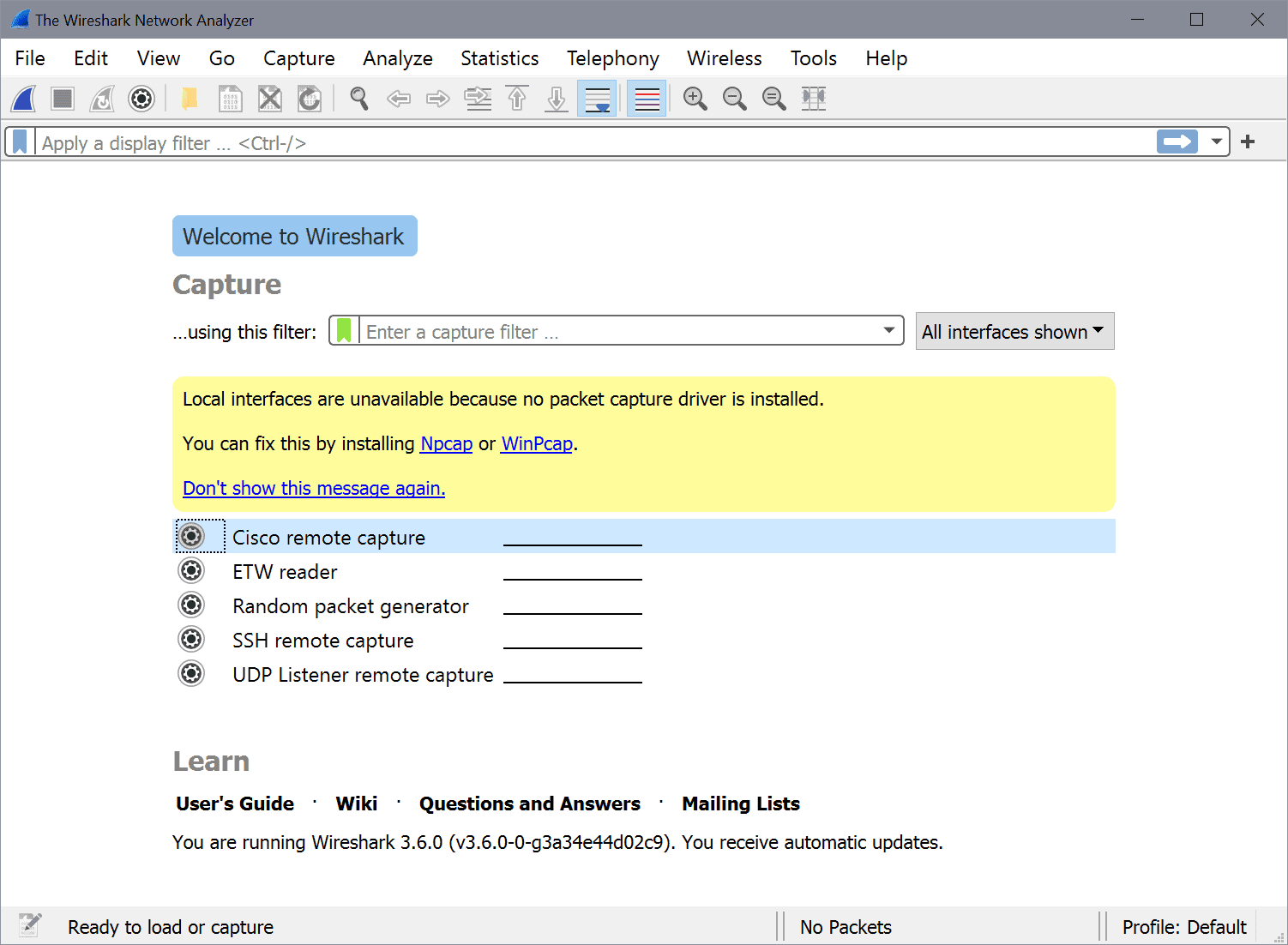
Take the time to look through your logs. Scan your network looking for unexpected devices and connections.
Below is an authoritative reference:
















We are surrounded by routers nowadays. There’s evidence that hackers are now also trying to affect routers by making new viruses made especially for routers. It’s high time for us to start protecting our routers by securing it with all types of security. The steps shown here are very important & need to be followed by everyone who owns a router. Even the network providers should learn all this & implement it when the setup a connection.
What about NORDVPN added to the router? Wouldn’t this also discourage hackers?
I enabled HTTPS for admin connections as advised above… the fist impact was that I could not use the LAN (192.168.1.1) adress to access anylonger. I took note that the router says I should use:
https://router.asus.com:8443/index.asp
However, now Choogle Chrome says that this is an unsafe public location (unsafe). The URL bar shows “Unsafe: https://router.asus.com:8443/index.asp”
That does not sound like a good thing… is this normal?
I have the same issue as rap that when I use https, chrome says it is not secure. I also tried using a certificate and I could not get it to work.
Thanks in advance for your help.
Kevin, this is a fine article but it reminded me of a continuing major annoyance. Mainly, consumer routers REALLY SUCK as their firmware is updated (maybe) for a short period of time until the vendor moves on to hardware version 2 with a completely different chipset. With the continual evolution of new threats we need a router hardware platform with a stable design, longer warranty and, if all possible, an open source stack.
I don’t envy the OpenWRT devs who have to chase and reverse engineer all of these cheap little sh*t boxes. Just lucky that my old WRT54GL keeps on working but eventually I’ll need faster wireless, GigE and IPv6 support.
Possibly out of this sites scope, but please consider reviewing some lower cost and better quality firewall hardware on my short list: Ubiquity EdgeRouter Lite, RouterBoard RB750GL, PC Engines ALIX. Have I missed any? :) TIA, Mike
The How-To Geek addressed MAC address filtering and SSID hiding by saying that they are practically useless and that a strong password solves any problem these would “fix”. MAC filtering is a pain in the neck to administer and as Kevin said, they can be easily broken by an advanced user. A good password/passphrase will turn anyone away. Again, with SSID hiding, a strong password makes this pointless. An analogy HTG used was using tape and a strong lock to help secure your front door. If the lock can be breached, the tape isn’t going to help anything.
Also, how can a router that’s been made inaccessible from wireless be made reaccessible? Does it require resetting the router?
Thanks for these interesting and informative articles Kevin.
Although I have difficulty even wanting to read an article titled, “Secure you wireless router”, I buzzed through most of it.
These is too much stilted and incorrect English, especially on line. When an article’s headline shows someone either doesn’t know English or doesn’t care to say (write) what they mean, I don’t care to read it anymore than I do Nigerian email scams.
@Sta – So what was the purpose of your poorly written post criticizing someone else’s poor English, IYO), which was not poorly written at all)? You wanted to look dumb in front of everyone?
Suggest you try looking in the mirror, because your own use of English is pretty poor, in and of itself. [roflol]
Merlins Firmware is on top of the recent security exploits and his builds are just bug fixes, security improvements, and features.
He covers all of the ASUS routers from the low end to the high end AC87U
http://asuswrt.lostrealm.ca/
Slight slip of the finger. Didn’t you mean “Secure YOUR wireless router”?
Was about to post it to our FB page when I saw the misspelling.
Maury
Thanks, corrected. How could I overlook this..
Thanks Martin,
Excellent article
Just shared it on our FB timeline, http://facebook.com/spaug.net but it still says ‘YOU’ not ‘YOUR’. You might want to check that out.
Maury
Nice informative useful article.
Thanks.
In order for Chromecast to work properly, Google says I have to enable uPnP on my router. Is there some way to make uPnP more secure when enabled short of toggling it on and off when I use the Chromecast?
I have 3 in my house that work fine without uPnP.
I also have had no problems for years using my Chromecast with uPnP disabled on any of my routers.
Where did you read that it was necessary? There isn’t any official statements from Google stating uPnP is necessary, perhaps it was just some reference in a random comment made by an anonymous user in one of Google’s help forums?
Such a shame that many browsers still don’t route to HTTPS yet. I would think that in 2015, this would be default.
You didn’t mention using alternative firmwares like DD-WRT. I don’t use it but have considered. What is your opinion about something like that?
I love DD-WRT; have one in my network as well as a few others distributed among my family and friends.
Thought hard about including it, but decided that, by itself, DD-WRT was not really a security measure. And because I believe DD-WRT (and/or Tomato) deserve a standalone article. It’s on my list of topic ideas.
Timely for me. Just getting ready to try a router/modem combined unit, as 2 attempts to use a router for wi fi messed up my wired service. Of your article, I am afraid my ignorance of what is actually going on could cause me to screw things up, and I don’t want to begin by screwing things up – I don’t have the expertise to be confident of being able to fix it. I will do the easiest things first and then one step at a time test using some of the more obscure things, so any problem can be fixed by undoing the last step of the process. Hopefully there is also a simple restore entire unit to factory defaults button to save me also if needed!
Martin,
Hopefully you will be around a long time.
Back to router configuration – the first time I did a firmware upgrade it totally screwed up my router. The connections would keeping resetting themselves. I had to go back to the original firmware and let me tell you it was not easy. It had taken me several days to find the right documentation and the original firmware software. Needless to say I won’t be doing another upgrade. I do have most of the other security settings here will have to go back and check them all.
Though Kevin is correct why there is a need for firmware upgrades, not every ISP can work with the new firmware which may be the reason why you’re having connection issues. Much like my Blackberry when I purchased it it had firmware version 2.5, according to the manufacturer’s suggestion and knowing which service providers protocol I was on, they suggested the maximum I could upgrade to was version 4.0.
When I brought my phone in for repairs, afterwards the service provider kept upgrading me to 4.1 without my permission which really screwed up my phone. It would not longer ring any tone, it would only vibrate, and when I put the phone into sleep mode it kept rebooting. So to make a long story short, no unless the protocols of the new firmware can work with your ISP/hardware, I would not suggest upgrading firmware.
I would encourage you to reconsider.
The reason for firmware updates is to fix bugs and vulnerabilities. These cannot be solved by configuration alone.
If you are running the original firmware, more than likely you have a security vulnerability, maybe multiple.
Remember, your router is directly on the internet with a public IP address. This means anyone in the world can reach it.
There are people that scan whole blocks of internet IP ranges looking for vulnerabilities. Some do it to inform/educate, most have other intentions.
Kevin,
If I do this again and it does the same thing where I cannot use the router at all how does that help me?
Also, spent many hours on phone with support.
Glad to see you are back online. The web wasn’t the same without you Martin.
That being said, excellent article as always.
I’m not back online permanently yet though. Hopefully all will get sorted out tomorrow.
A thorough, excellent post. Thank you, Kevin!
Btw, about a week ago there was a post on russian resource about Asus routers’ AiCloud vulnerability tested on latest firmware ver. 3.0.0.4.370 and it seems it hasn’t been fixed yet for most Asus models, so you definitely should turn AiCloud off.