How to properly protect your Outlook.com account
If you are using Microsoft's Outlook.com email service you have various options to connect to it. You can use the web interface, mobile apps or desktop email clients.
Regardless of how you use the service, you may want to make sure that it is properly protected against hacks and other malicious attacks.
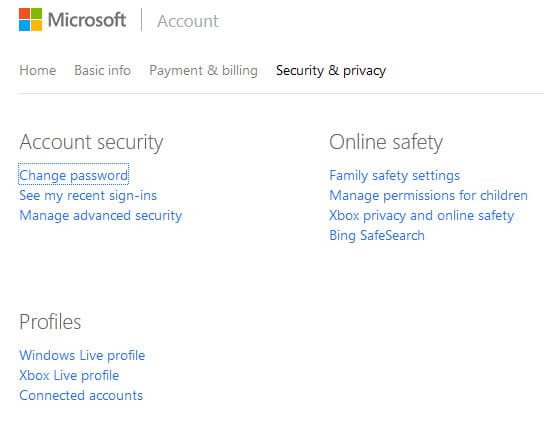
Outlook.com accounts are directly linked to Microsoft Accounts. This shows when you try to locate security related settings on the Outlook website as you will notice quickly that there are none.
All security and the majority of privacy related features and settings are accessed on the Microsoft Account website instead.
You can use the link posted above to get there which is the fastest option to access it. The Security & Privacy overview page lists important preferences that allow you to modify these account-related settings.
Lets take a look at the most important options on the page:
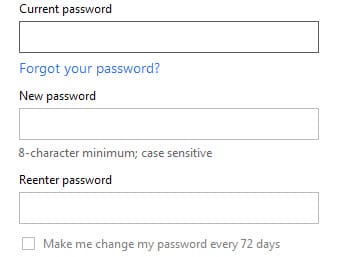
1. Change password
Link: https://account.live.com/password/Change
It is highly recommended to select a secure password. There is no catch-all definition for secure though but generally speaking, the more characters the password has the better.
Microsoft's requirements are that the password needs to be at least 8 characters. If you want to improve security, I suggest you use at least twice the number using a mix of letters, numbers, upper and lower-case characters and special characters.
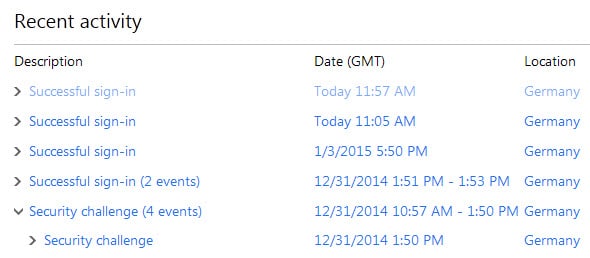
2. Monitor activity
Link: https://account.live.com/Activity
This page lists the last sign-ins on a single page. Information such as the location of the device the sign in was recorded from, date and time, IP address or platform are listed for each sign-in attempt regardless of whether it has been successful or not.
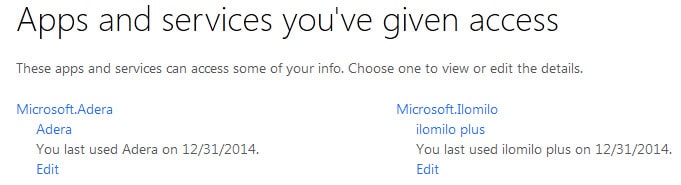
3. App permissions
Link: https://account.live.com/consent/Manage
Here you find apps and services that you have given permissions to. This includes Windows apps and may also include Web services and mobile applications.
Each app and service is listed with its name and the data you last used it. A click on the edit button allows you to remove permissions again.
4. Advanced Security features
Link: https://account.live.com/proofs/Manage
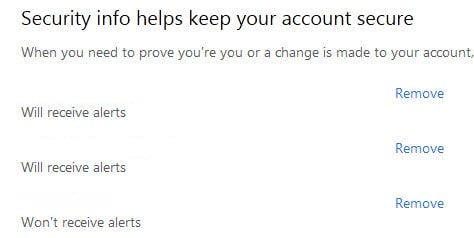
You find additional, some would call it the most important - security settings and features on this page It lists all email addresses and phone numbers associated with the account, and offers options to remove them or add new ones.
This is important for a number of reasons. First, you want to make sure that old accounts and numbers get removed immediately from the account as others may use them to gain access to your account.
Second, if you plan to enable two-step verification, you may need to add a phone number in case you have not already.
Last but not least, it is also possible to define alerts for each account and phone number. Microsoft will notify you if the company believes there is a problem with the account security-wise. Note that it is not possible to opt-out of receiving alerts for the primary account.
Sign-in preferences allow you to select the email addresses that you can sign-in with. While you cannot modify the preference for the main account, you can enable or disable all other accounts on this page.
Two-step verification on the other hand improves the login process by adding a second verifier to it. Instead of signing in just with the username and password, you are asked to supply a code that is sent to your email address or mobile phone. This is probably the best option to improve account security.
Identify verification apps can be used configured to generate that code locally.
App passwords come into play once you have configured two-step verification. Since some programs and devices don't support it, you need to create so-called app passwords for them that allow you to sign in without using the verification codes.
Recovery Code on the other hand comes in handy if you need to restore access to your account. It can be used for that purpose and should be kept in a safe location because of it.
Recommendations
This is a quick list of recommendations to secure your Outlook.com / Microsoft account.
- Pick a secure password that is at least 16 characters long and uses upper- and lower-case characters, numbers and special characters.
- Enable two-step verification for the account.
- Create a recovery code and safe it in a secure location.
- Review account activity and app permissions regularly.
















it seems Microsoft removed 16 characters password limitation.i changed my password to o around 25 characters
but not tested for 100 characters
dont allow me select longer than 16 characters
Your password can’t be longer than 16 characters.
I have modified the recommendation to 16 characters. Wonder why they limit it to that.
It was was made a big fuss about 2 years ago when Outlook.com took over. “Explanation” is here:
http://windows.microsoft.com/en-us/windows-live/microsoft-account-password-16-characters
And to Quote another site that “quoted” Microsoft (they didn’t supply a source link):
Please note our research has shown uniqueness is more important than length and (like all major account systems) we see criminals attempt to victimize our customers in various ways; however, while we agree that in general longer is better, we’ve found the vast majority of attacks are through phishing, malware infected machines and the reuse of passwords on third-party sites – none of which are helped by very long passwords. Sixteen characters has been the limit for years now. We will always prioritize the protection needs of users’ accounts and we will continue to monitor the new ways hijackers and spammers attempt to compromise accounts, and we design innovative features based on this. At this time, we encourage customers to frequently reset their Microsoft account passwords and use unique passwords that are different from other services.
(http://thenextweb.com/microsoft/2012/09/21/this-ridiculous-microsoft-longer-accepts-long-passwords-shortens/)
I don’t think that makes a whole lot of sense considering that it should be the user’s decision and not Microsoft’s to artificially limit the password length. Thanks for digging up the explanation!
i remember hotmail (now outlook) 1 year or 2 year ago even allow 100 characters for password
but after sometime they removed this feature and limited it.
i use roboform password generator and it show me 16 characters= 95 bit strength
i think it is not Enough and this is not good