Upcoming policy changes to Google Chrome's certificate handling

Most financial websites and many popular services and sites offer SSL connections exclusively or in addition to regular connections. Whenever a browser connects to a website via SSL, it will download a certificate that it verifies to make sure the connection is legit.
The certificate includes information about the website's address, confirmed by third party organizations, so that the address the browser connected to and the address in the certificate can be compared with each other.
This is done to make sure that you did not land on a site that pretends to be the site you wanted to connect to.
Secure websites are highlighted by all browsers in the address bar, and certificate errors are displayed as prompts to the user as well.
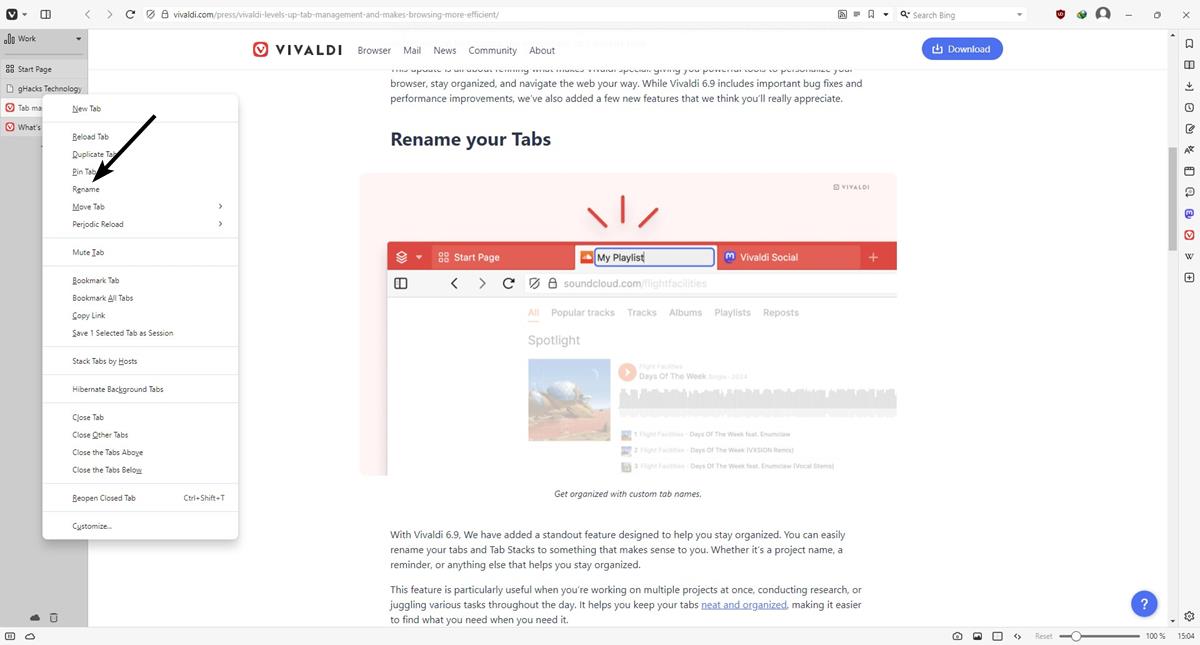
Google has just published information about upcoming policy changes in regards to the certificate handling in Google Chrome, Chromium and Chrome OS.
1. Minimum RSA key size of 2048 bits
Google Chrome will warn users in early 2014 if certificates contain RSA key sizes of less than 2048 bits.
Beginning in early 2014, Chrome will begin warning users who attempt to access sites with certificates
issued by publicly-trusted CAs, that meet the Baseline Requirements' effective date [..]
Root certificates are exempt temporarily from this. Google may however "remove trust for root certificates with RSA keys less than 2048 bits" in the future.
The company estimates that less than 0.1% of all sites are impacted by this change. This also means that users will run into certificate warnings when they connect to these websites from early 2014 on. It is likely that they will receive a message like "The site's security certificate is not trusted!" when they try to connect to these sites. This prompt is displayed currently if the certificate of a website is not trusted.
2. Improving Extended Validation (EV) certificates
Extended Verification certificates are issued after extensive verification of identities by certificate authorities. Google Chrome will require Certificate Transparency for all Extended Validation certificates issued after a data that is yet to be decided upon.
Certificate Transparency aims to eliminate flaws in the SSL certificate system by "providing an open framework for monitoring and auditing SSL certificates in nearly real time".
This can be used to detect certificates that have been maliciously acquired or issued in error, and also to identify rogue certificate authorities.
Advertisement