HijackReader analyse HijackThis results
HiJackThis is a sophisticated security tool that checks a computer running Windows 2000 or higher for possible signs of hijacked applications or potential malware.
The application checks lots of different elements like startup items, Browser Helper Objects, running processes and the like and presents a log of the results at the end.
This log is hard to read for beginners because it contains "good" and "bad" elements in it and it requires knowledge of those items to make a distinction between elements that you have to keep and those that are indeed malicious or problematic in nature.
The program makes no distinction in regards to items in the list so that it is necessary to check item after item to find out about its nature.
Most users tend to post their logs in forums so that experienced users can take a look at them and recommend actions. There are actually several forums that can be used.
Note: HiJackReader has not been updated since 2007 and should not be used anymore to analyze HiJackThis log files.
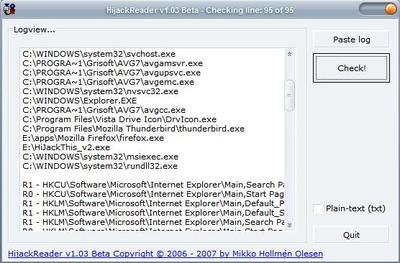
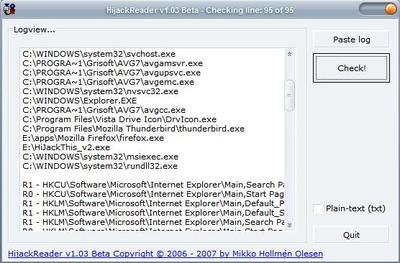
HiJackReader
If you would like fast results you could also use the software HijackReader which analyzes HijackThis logfiles in an attempt to rate items. It should be clear from the description that it is necessary to analyze the ratings of the helper application as well before you remove any items. HijackReader uses two lists to analyze the logfile.
Those two lists are the CLSID list by Tony Klein and the Startup info list by Paul Collins.
A single HTML file is created after the analysis of the system. Ratings of items can either be OK (no fix needed), FIX IF UNKNOWN (check for more information if you do not know the element), FIX (CHECK NOTES!) (read the description and fix the issue because it is indeed malicious) and UNDETERMINED (find out for yourself).
The HijackReader application can be of help especially if items are found that are marked as Fix (Check Notes). The user can fix those without having to wait for someone else to analyze the logfile.
It does not help that much for elements that are undetermined or marked as fix if unknown; users will still have to get professional help or do extensive research before they can be sure if the item is malicious or not.

















Gees,
You don’t really need to download software and go through what you can simply do by going to the Web Site below and do it on line. I mean how Sophisticated to you need to get!!!
http://hijackthis.de/index.php?langselect=english
T BIRD
Oh, finally someone engineered a companion for it.
I love the genius of technology innovation.
Thank you Ghacks!