Mozilla launches Tracking Protection feature in Firefox Nightly
Advertising and marketing companies use tracking to learn more about users that visit properties on the Internet that their services run on.
Knowing more about users increases the profitability of advertisement which is the core reason why tracking is used so widely these days.
Do Not Track was a first attempt to give control back to users but the main problem with the feature is that it is not mandatory.
Advertising companies can honor the Do Not Track setting of a browser but don't have to.
Side note: if you are interested in finding out more, check out the following recent guides: what websites know about you and who can see your IP address on the Internet.
Mozilla launched a new experimental feature in Firefox Nightly, the cutting edge version of Firefox, as part of its Polaris initiative.
Tracking Protection is not enabled by default but when you enable it, it will improve user privacy on the Internet by using so called block lists of domains and sites that are known to track users. It is also enabling Do Not Track automatically.
Basically, it is blocking known tracking sites in the browser whenever sites try to make those connections. The first initial version of Tracking Protection uses the blocklist of Disconnect.
Turn on the tracking protection
You need to do the following to enable the Tracking Protection feature in the Firefox browser (note that it is only available in Firefox 36 Nightly currently):
- Type about:config in the address bar and hit enter.
- Search for privacy.trackingprotection.enabled
- Double-click the entry to set it to true.
- Restart Firefox.
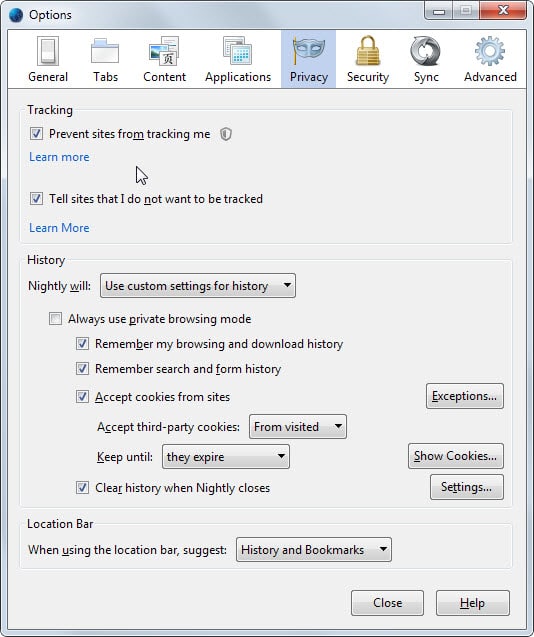
Make sure it is enabled
Nothing changes after the restart right away. If you want to know if the operating worked out fine, do the following to test that:
- Tap on the Alt-key on the keyboard while Firefox is open.
- Select Tools > Options from the menu.
- Switch to Privacy in the options window.
If you see Tracking - Prevent sites from tracking me there, you have successfully enabled Tracking Protection. There you can also disable it again at any time without having to open the about:config page to do so.
How it looks on sites with contents that track you
When you visit a website that is tracking you directly or loading scripts that do, you will see a new icon in Firefox's address bar next to the url.
When you click on it, it displays that elements on the site track your online activity and that the feature has disabled those elements.
There you can also enable these for the site in question which can be useful if they power other functionality on the site or if you don't mind that those scripts are loaded on that particular site.
A click on the options button displays an option to disable the protection on that site.
Closing Words
What I like about the Tracking Protection feature is that it does not block advertisement completely but takes care of tracking domains only. As a webmaster who earns his living from advertisement, that is obviously better than getting ads blocked outright and not earning any money from users visiting the site.
The feature is experimental at the time though. An option to load and manage different tracking lists would be useful for example as you'd get more control over the feature in the process.
Mozilla's Tracking Protection is not the first attempt at integrating block lists into web browsers natively though. Microsoft introduced a similar feature (enable lists, block or allow sites based on those lists) some time ago in Internet Explorer for example.
The feature itself is not really for experienced users either, as they are likely running add-ons or programs already that protect them from ads or tracking on the Internet.
Less tech-savvy users on the other hand may benefit from this.





















I have nothing against EFF, on the contrary, but concerning their two leader browser applications, that is HTTPSEverywhere and Privacy Badger, I’m sorry to say my opinion is not favorable. The former lies on a more than arguable concept and is a pain in the neck when applied, the second is an ersatz of protection built around the idea that between theory and practice a few lines of code are sufficient . I believe EFF should remain where it’s best at : speech.
Well, it’s a nice try but as said it’s difficult to trust this solution (like every single installed or integrated solution). But if it works, we should give it a try and may find some more details how they get money with it or if there are some side notes that comes with it.
I just added this to my Firefox a week or two ago, and I’m thinking this does basically the same thing.
https://www.eff.org/privacybadger
privacy badger looks interesting but it says it does not work if one has private browsing enabled. i always use private browsing and am sandboxed and also use ghostery.
I use Privacy Badger as well. Ghostery never. They sell data to the advertisers. MIT Tech review mention it two years before. The same applies to Adblock Plus according to Slashdot they unblock for the big Internet companies.
http://yro.slashdot.org/story/15/02/03/1517230/google-amazon-microsoft-reportedly-paid-adblock-plus-to-unblock
Tracking seems to be a relatively complex topic in terms of the techniques used. I don’t understand how it’s usually implemented but a blacklist/whitelist approach based on domains seems like it might not cover all avenues. For example, doesn’t facebook store some sort of super cookie that unrelated websites can read and are people likely to accept blocking of a big site like that? Seems there might be more granularity required but perhaps the is a good start.
The more promising aspect of the a Polaris initiative is the hook up with the tor project. Hopefully it won’t be long until mozilla finally integrates a new ground-breaking feature into Firefox for the first time in a very long time: tor support in private browsing mode
I like for the android version when I hadn’t disconnect and every addon really sllows the smartphone
Well, my purely personal opinion is that advertisers and their host websites need to police their turf a hell of a lot better before I’ll pay attention.
Snip from a recent news story: “Malicious advertisements have been discovered infecting the Web browsers of people who visited certain major websites between Aug. 19 and Aug. 22… The ‘malvertising’ was found on Java.com, DeviantArt, TMZ, Photobucket, IBTimes, eBay.ie, Kapaza.be and TVgids.nl, and eventually detected by Dutch Internet-security company Fox-IT. The websites themselves were not hacked; rather, the malicious ads had been spread through the online advertising network AppNexus… When victims visited websites containing these malicious ads, hidden links triggered a drive-by download. The victims’ browsers were redirected to a malicious Web page hosting the Angler browser exploit kit, a software bundle containing exploits for several known flaws in browser plugins, such as Flash Player, Java and Microsoft Silverlight.”
It’s been going on for a long time. Here’s a snip from a story published in 2011:
“Rik Ferguson from Trend Micro described an incident when the New York Times was hosting a banner ad that attempted to social-engineer people into installing a rogue antivirus tool. In another example, the London Stock Exchange website was also observed inadvertently serving malicious ads to its users, as described by Paul Mutton. This incident was traced to a possible breach at Unanimis–the company serving the ads the London Stock Exchange and many other companies. Mary Landesman from ScanSafe/Cisco pointed out that the list of popular websites serving malicious ads in the recent years included Hoovers.com, USNews.com, Tucows.com, TheOnion.com, SpeedTest.net and many others. She also explained that malvertisements aren’t limited to a particular ad network; they’ve been delivered via DoubleClick (Google), YieldManager (Yahoo!), and rad.msn.com (Microsoft), and also through webmail services, such as Windows Live (Hotmail) and Yahoo! Mail.”
I have no problem with webmasters making money by selling advertising space. (Nothing against GHacks or Martin… !)
I have a problem with an advertising server industry which has allowed itself to become a disease vector for malware — and which has been strikingly unwilling to do very much about it.
This is so true. Malvertising is a reality.
Two more articles :
– Online ads are attacking you http://money.cnn.com/2014/10/15/technology/security/malvertising/index.html?utm_source=feedburner&utm_medium=feed&utm_campaign=Feed%3A+rss%2Fmoney_latest+%28Latest+News%29
– Large-scale malvertising campaign hidden in online ads hits Last.fm http://www.theinquirer.net/inquirer/news/2371234/large-scale-malvertising-campaign-hidden-in-online-ads-hits-lastfm
Performing a Web search for malvertising will deliver fewer results than reality, i’m afraid.
I guess this Polaris protection will not be enabled by default even within the final release of coming Firefox and that as always will be a problem for million of users who are simply not aware of 1- privacy concerns and 2- privacy defense.
On another hand people are responsible so they cannot expect to be protected as a child without making at least the effort to discover the minimum provided i.e. Polaris, minimum in terms of effort to be already protected substantially.
Last but not least those users who simply don’t care, don’t care about privacy issues mainly, don’t care about ads and tracking, and those users are not only a few. This is what I say to advocates of advertizement on the Web : don’t cry for more than what you already have : many many users. And they don’t cry because they know that crying will awake those users whom until now are still the strong basis of ads business. To them I say : forget Polaris, forget privacy, thanks for the others who do care and whom without you would be responsible of many sites disappearing.
In a global economy everything is global and numerous : life is a balance and it has always worked out that way when both parties avoid striving beyond reasonable limits. So, advertisers : keep calm, do better within respect due to all, don’t try to force, you’d lose everything.