Google Chrome 104: patches critical security issue and a issue that is exploited
Google released a new version of the company's Google Chrome browser on August 16, 2022. The new stable version is a security update for the browser that addresses 11 security issues.
It fixes a critical security issue in the browser and a high security issue that is exploited in the wild.
The update is also available for the Extended Stable channel, a longer-term support release version of Chrome for businesses and Enterprise users.
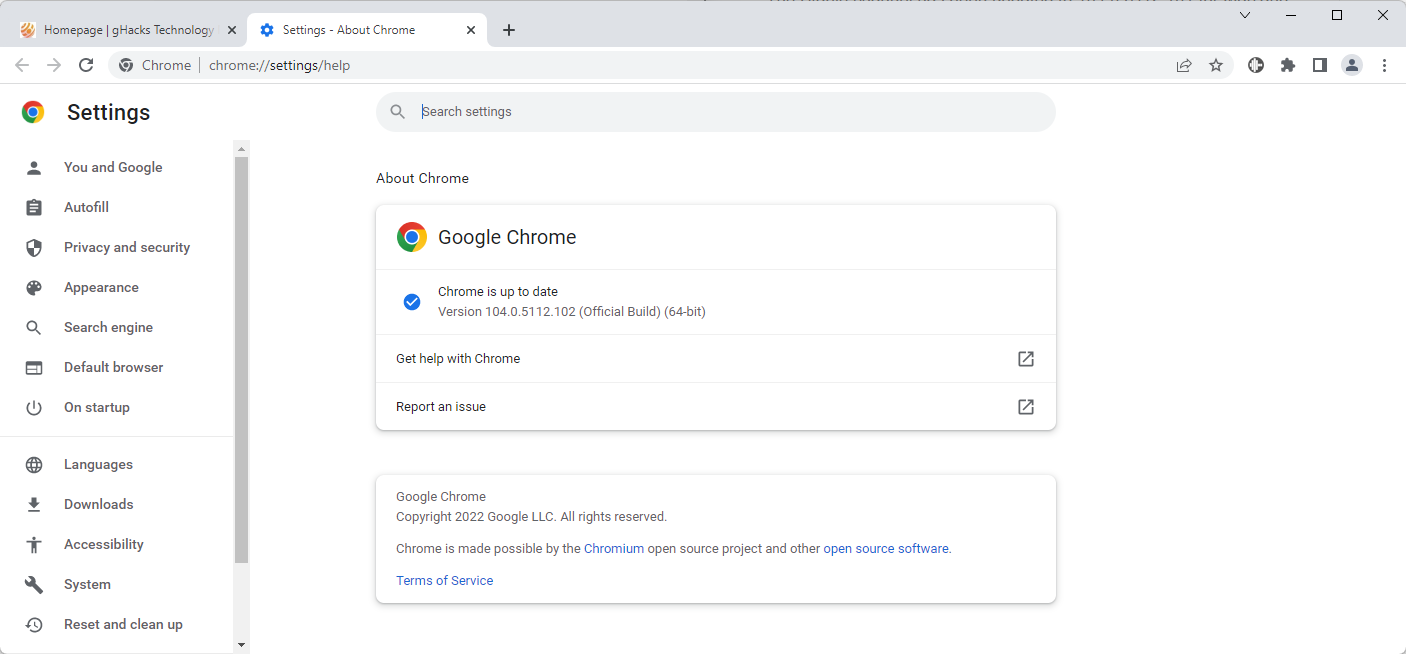
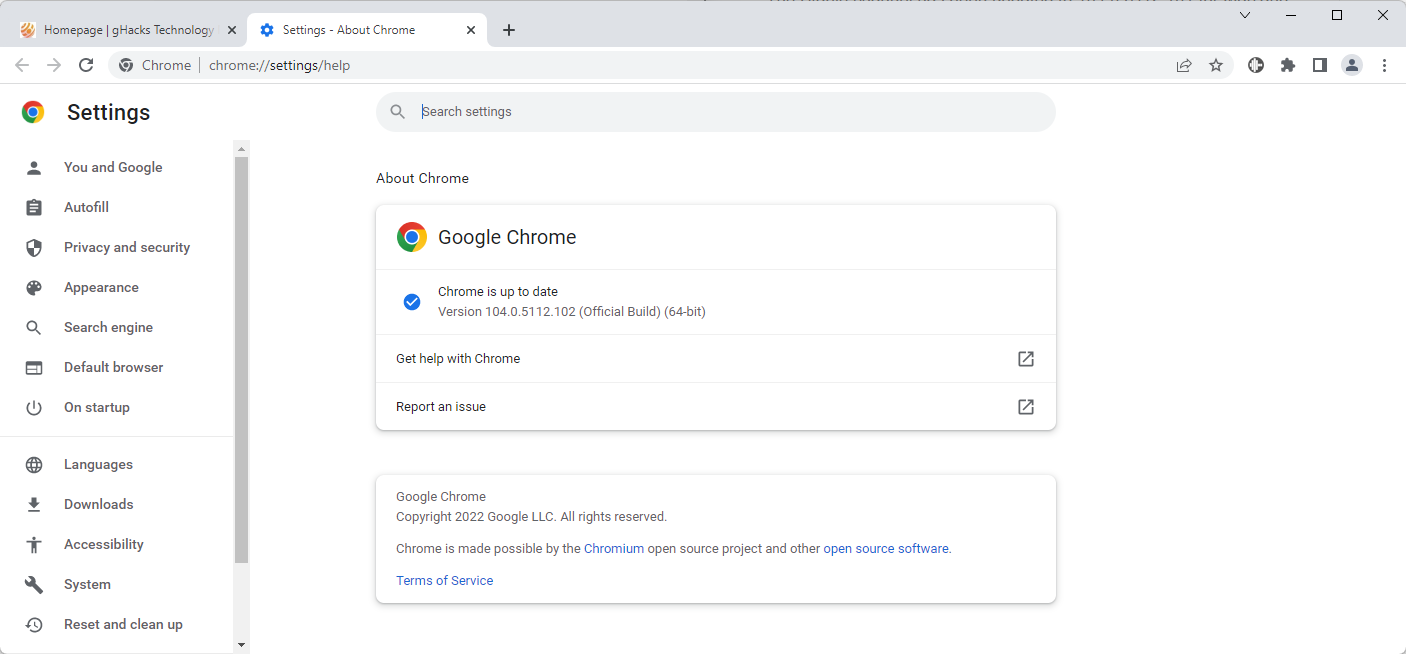
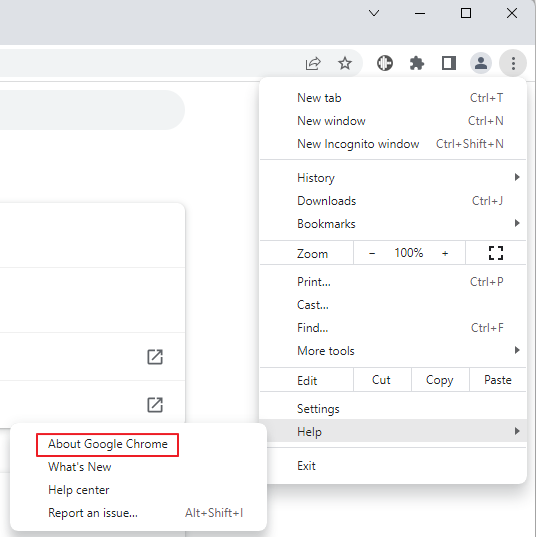
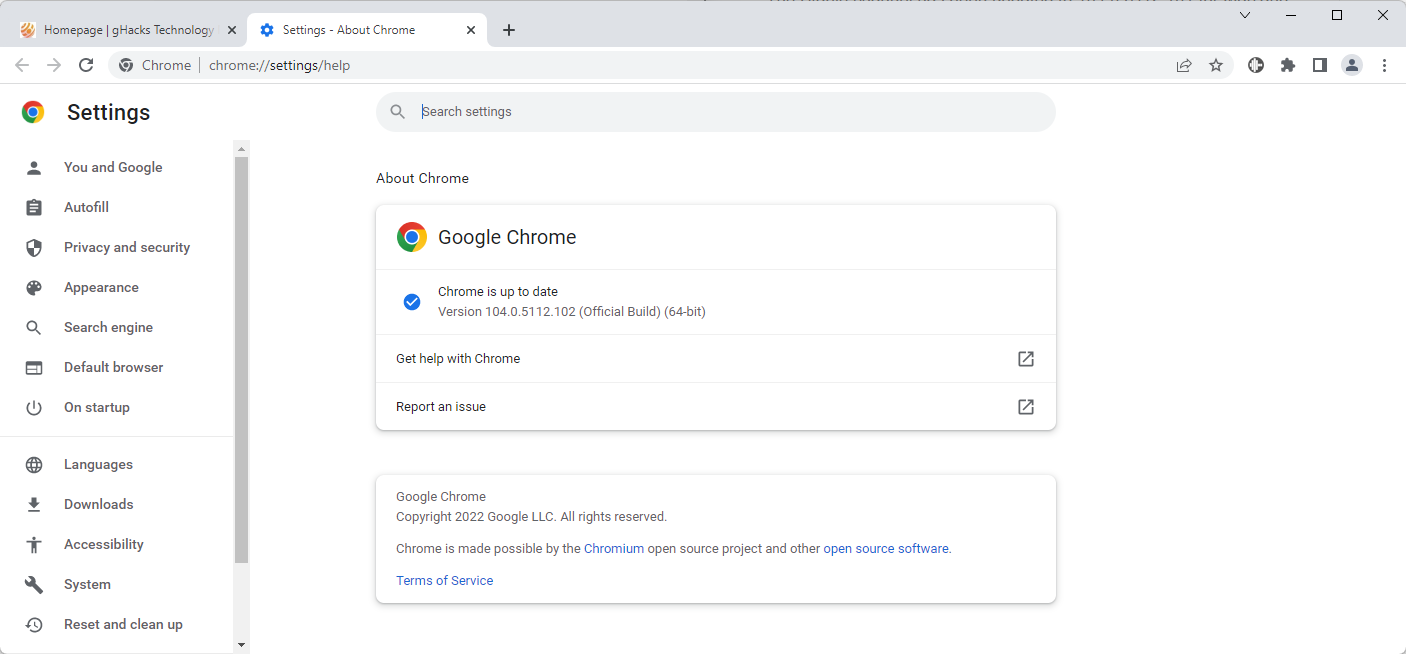
The update is available already, but it is distributed in waves. Chrome users who want to update to the new version immediately need to select Menu > Help > About Google Chrome, or load chrome://settings/help directly in the browser.
Chrome displays the current version of the browser and performs a check for updates at the same time. The new update is downloaded and installed automatically then. A restart is required to complete the update.
Chrome 104 security update
Google released the first version of Chrome 104 in early August. The release fixed 27 security vulnerabilities in the browser.
The stable channel is updated to 104.0.5112.101 for Mac and Linux, and 104.0.5112.102/101 for Windows when the update is installed. Extended stable channel installations are updated to updated to 104.0.5112.101 for Mac and 104.0.5112.102 for Windows.
The release announcement lists all security issues that have been reported to Google by external researchers. Google does not list security issues that it discovered internally.
- [$NA][1349322] Critical CVE-2022-2852: Use after free in FedCM. Reported by Sergei Glazunov of Google Project Zero on 2022-08-02
- [$7000][1337538] High CVE-2022-2854: Use after free in SwiftShader. Reported by Cassidy Kim of Amber Security Lab, OPPO Mobile Telecommunications Corp. Ltd. on 2022-06-18
- [$7000][1345042] High CVE-2022-2855: Use after free in ANGLE. Reported by Cassidy Kim of Amber Security Lab, OPPO Mobile Telecommunications Corp. Ltd. on 2022-07-16
- [$5000][1338135] High CVE-2022-2857: Use after free in Blink. Reported by Anonymous on 2022-06-21
- [$5000][1341918] High CVE-2022-2858: Use after free in Sign-In Flow. Reported by raven at KunLun lab on 2022-07-05
- [$NA][1350097] High CVE-2022-2853: Heap buffer overflow in Downloads. Reported by Sergei Glazunov of Google Project Zero on 2022-08-04
- [$NA][1345630] High CVE-2022-2856: Insufficient validation of untrusted input in Intents. Reported by Ashley Shen and Christian Resell of Google Threat Analysis Group on 2022-07-19
- [$3000][1338412] Medium CVE-2022-2859: Use after free in Chrome OS Shell. Reported by Nan Wang(@eternalsakura13) and Guang Gong of 360 Alpha Lab on 2022-06-22
- [$2000][1345193] Medium CVE-2022-2860: Insufficient policy enforcement in Cookies. Reported by Axel Chong on 2022-07-18
- [$TBD][1346236] Medium CVE-2022-2861: Inappropriate implementation in Extensions API. Reported by Rong Jian of VRI on 2022-07-21
The list includes a security issue with a critical severity rating. The remaining security issues have a rating of high or medium. The critical issue was discovered in FedCM, Federated Learning with Client-level Momentum.
Google mentions that the security issue CVE-2022-2856 is exploited in the wild. The issue is rated high and has the description "Insufficient validation of untrusted input in Intents".
Chrome desktop users should consider updating the browser as soon as possible to fix the security issues and protect their data from attacks that target these issues. Expect updates from other Chromium-based browsers in the coming days and weeks.
Now You: do you use Google Chrome?


















@Iron Heart
Oh Hi
> Walls of text (something you say I write, while you write the longest by far)
Only in reply to your posts though, because you keep posting lines of text spreading misinformation and fear mongering BS about the Firefox browser.
> A browser with amateurish site isolation
According to you, But you are a nobody. It is common knowledge that Firefox is reasonably secure as it has been independently audited many times (Which is probably more than what you can say for brave or vivaldi) and gets nowhere near the security problems, patches and fixes that chromium based browsers do.
Firefox actually does have site isolation security architecture that offers genuine security despite your BS claims or claims from that stupid blog you likely are not allowed to spam anymore.
> Proprietary is not the same as insecure. The former means that the code is not public
Proprietary code is only maintained by a small team thus many tech experts see such code as not as secure as FOSS code, which can be observed and maintained by a much larger community under a type of peer review process, which is very unlike a small lazy team that never gets peer reviewed by a wider FOSS community. * [Editor: removed, stay polite, please]. Many security professionals worth their salt will always prefer FOSS.
> Chromium is open source,
Still built primarily for proprietary browsers like chrome and edge thus it is crap, because chromium is not really FOSS in a meaningful sense. Most FOSS applications are designed with excellent privacy in mind. Google or M$ being involved with FOSS is and always will be an absolute joke to many.
> Google has a large team as well. So does Microsoft. And the open source Chromium code is vastly more used and audited than Firefox.
Chrome and Edge are proprietary * [Editor: removed, stay polite, please], not FOSS. Chromium based browsers like Brave and vivaldi build their own features on chromium code when developing their browser and have not been independently audited (if at all) as much as Firefox, would be my guess.
> Brave is usually patched within 24 hours after the fixes land in Chromium, which is perfectly acceptable.
Lol at usually. Probably weeks before Brave is patched and chromium codebase is constantly getting patched so for a time between those patches brave is very insecure lol.
> They are separate.
Nope. Without good security, privacy should not be expected. Your argument is at the noob level.
Operating systems like Qubes combine state of the art security and privacy as does fedora.
If privacy and security were seperate things then there would be no need to have a firewall if running privacy focused applications like a firefox fork like librewolf.
Security enhances privacy you absolute noob lol.
> You have no sense of coherent and correct terminology,
According to a noob like you, i take that as a compliment. Thanks.
> Secure means resistant against malware, and has nothing to do with the privacy policy.
Oh look another noob level argument. People calling win 10 or 11 spyware is actually a meme, you do know that right? You think windows defender is secure if M$ can see everything in the OS and probably get a lot of data from edge too? How is that security if M$ Can get so much telemetry data easily?
Security and privacy are seperate? only a noob would say that.
> This argument is irrelevant to me because I use Brave, which is open source. But open source is not the only way to verify whether a product establishes connections, you can also look at the connections closed source software establishes via tools like WireShark. You did not know that, am I right? But then you call me a noob, better clean up at your own house.
You seem to use Brave with closed source crap like windows whilst not turning off JS because you say it is annoying. Your security would be laughable in any linux and privacy discussion forums. Using Brave on closed source crap like windows is actually hilarious if you expect privacy. Windows is closed source. Lol.
> you can also look at the connections closed source software establishes via tools like WireShark.
Lol at wireshark? Am i meant to be impressed? LMAO. That still does not stop closed source crap like windows gathering your
real IP or other such info that decide to collect within windows. As i said you are a noob. lmao at you using wireshark though thinking it actually stops big tech operating systems like M$ gathering telemetrey IP adresses, hardware ID etc.
> What it was “designed for” is irrelevant. Of course Google develops Chromium primarily for Chrome
What it is designed for is relevant in any discussion. Google drives the chromium project and your beloved browser of choice Brave waits for google for updates, security patches etc. Funny how you say Firefox is dependent on google, but in reality chromium clones rely on them for fixes. Lol.
The amount of promotion chromium clones gets is absurd. Most people that use Brave or vivaldi are presumably users that dislike chrome or edge. Too lazy to configure Firefox lol.
> Not every part of the Chromium source code “violates” your privacy,
It is a security risk because there is way too much code and it is way too popular, it is bloated and google keeps adding in crap to it.
You see no problem in using google made code like chromium based browsers and you say you do not even turn off JS. Javascript turned on is a security risk in browsers.
> 3% market share,
Oh great, i can rest assured that by using not so popular browsers like Firefox that they are more secure unlike popular chrome and edge the security nightmare browsers getting constantly patched.
> Because there is the wrong impression that Firefox can improve your privacy and fights for a free web
So you are saying that Firefox has no privacy? Suggesting that chrome has more privacy and Firefox can not get excellent privacy? Again you are a noob and much of your posts are the ones that are misinformation. IN every GHacks FF article you have to literally reply to FF users trying to convince them of your mindless nonsense, but you do not convince anyone with technical knowledge about what makes a good browser. You are just a noob.
> Hard-limiting content processes to eight means that it is not site isolation since multiple websites can still share the same content processes. This is the design of amateurs and is no the same as the full site isolation Chromium has implemented for years now. It seems that you are * [Editor: removed, stay polite, please] here because you are not aware of the actual Firefox code.
Firefox has full site isolation. The design of amateurs? Not full site isolation like chromium has?
What you are trying to say is that you do not think FF has as good site isolation as chromium based browsers? Thats fine, but what is stupid is that you are trying to say that FF does not have any full isolation at all, which is very misleading thing to say.
Firefox actually does have site isolation security architecture. You are the one who knows nothing about FF Code and anyone with a brain that actually researched the news around FF new site isolation security architecture FISSION already know that FF has full site isolation that is already good enough when compared to chromium code.
With Site Isolation, Firefox loads each site in its own process, thereby isolating their memory from each other, and relies on security guarantees of the operating system. It is good enough, FF Has good security architecture already with FISSION. That process separation of content from different sites provides the memory protections required to allow for a secure browsing experience.
Using Firefox on Linux is way more secure than using chromium clones or chrome and edge on windows etc. You actually promoted M$ over LInux in previous discussions i had with you which only shows your noob level arguments to be stupid.
Btw, JAVASCRIPT off is good security already, JAVASCRIPT on in a chromium based browser is not good security considering how bloated chromium code is and the way it interacts with closed source crap like windows, chrome and edge on windows is a security nightmare and probably chromium clones too, just look at the constant news articles about all the security flaws in them.
Other commenters here have pointed that out JS is a security nightmare in chromium based browsers, you actually promote JS To be on. You do not give good security advice.
> The marketing term for site isolation, which is (as said) incomplete.
It is already good enough and is constantly improving, something your ignorant mind fails to understand.
> And you have no idea about the actual Firefox code.
For someone that says FF Has no site isolation security architecture? Go look in the mirror pal.
> . Censorship of websites at the browser level is possible no problem, and so is reporting websites users have visited back to the mothership.
FF is an open source browser that can be customized and has many forks, nice try in fearmongering you noob.
> I never said that they have the same reach is Google
You imply that they have the power of google to censor youtube etc. Your views are very delusional.
> No, according to actual code comparisons. Firefox lacks several key exploit mitigations.
Lol, says the one using chromium based cones that have to rely on weeks for google to fix SEVERE security problems of which FF gets nowhere near the problems.
You think reading mad aidans stupid blog and pruning his text looking for an argument against FF makes you smarter? It does not! It actually makes you less intelligent.
> So then the whole Firefox clown parade downvotes me, so what? Does this magically make your misinformation, lies, and wrong terminology correct? No,
The one spreading misinformation is you. You say FF has no site isolation, it does have good security architecture, read about fission. You are just a blatant hater of FF spreading many mistruths about it time and time again. You constantly look for an angle to hate on Firefox. Firefox does have fission, you sound hateful that they do.
So FF users are just a clown parade according to you? Ok, i can see why you have an inferiority complex towards those that use better browsers than you. How dare they actually choose something more secure and customizable than chrome, edge or chromium clones and point out that what you say about Firefox is very misleading.
> Doubt it.
You would likely get banned from any Linux privacy community for promoting M$ over Linux and closed source software like chrome over Firefox. Lol.
> Why should I stop using e.g. Brave or GrapheneOS when they send no data to Google. Because Google also wrote other parts of the code that have nothing to do with my privacy? Sorry, but that’s no reason to stop using anything.
Use what you want, i don’t care. I am only pointing out that Brave and GrapheneOS rely on google for things like security updates in Braves example and google pixel phones in GrapheneOS Example etc.
Anything that does not have to rely on google can only be a good thing in the long run.
> I said that meticulously maintaining one’s whitelist of what to allow for each and every website one visits is impractical for most people,
You said that turning off JS was annoying in previous discussions i had with you, which implies that you do not like it turned off. You also do not need whitelists for turning off JS when it can be turned on or off with a toggle.
You soundlike someone who never turns off JS which makes you look like a total noob from a security and privacy perspective.
> Most fingerprinting defenses, including those of the Tor Browser Bundle, are written with the assumption in mind that JavaScript is turned on,
Total BS, tor browser has a in built toggle to specifically turn off JS reminding people that it is the safest option.
> Factually wrong. Any experiment with JS turned off on all websites can and will prove me right here.
Privacy focused websites allow JS to be turned off whilst providing a good browsing experience. But you know nothing about security and privacy with your noob level arguments and hatred of FOSS Browsers like Firefox.
> Whatever they do in Chrome is irrelevant to me, Chrome and Chromium are not the same thing in terms of what can be patched out.
Chrome is a security nightmare, chromium is the base for chrome. It stands to reason that chrome getting so many security patches proves that chromium is bloated and very insecure. Chrome and chromium are similar in the sense of security patches, bugs and fixes etc. Google direction for the web.
Google having a hand in the FOSS community is an absolute joke.
> I never promote their data collection
Say that Firefox is a better browser than chrome. Say that Firefox offers better security and privacy? Will you say that? Not really, you will skip around it and make excuses for google chrome lol, like you have done previously.
> They are better engineered than Mozilla’s products
There you go. A google promoter.
> I don’t need Mozilla. Switching to Mozilla products would lower both security and privacy for me.
Well you are entitled to your opinion.
Brave likely will not be patched for weeks. FF is way faster getting updated. LMAO.
> If uBlock Origin can block connections, so can Mozilla since the browser runs with higher privileges.
You have been wishing for mozilla to censor users because you are actually so delusional to believe that they would make FF a censorship browser. You sound really dumb with your persistence in pushing that argument. The deplatform fox is old news an outdated meme.
You are outdated Iron Heart lol.
> Censor the web for users of their browser, yes.
Firefox an open source browser being a censorship browser? Completely delusional!
> No, Google makes money with data collection
Google also makes money with people buying google pixel phones. GrapheneOS relies a lot on a google product like pixel phones to able to install GrapheneOS. Google gains power by more people using chromium based browsers.
> Yes, if it’s better than Google’s engineering. Otherwise I have no reason to switch.
But nothing could ever be better than google engineering now could it? To question google is to question god itself? Lol.
> How about Mozilla actually fixing their shit? Would that be an option?
Mozilla does not need to fix Firefox all that often because it seems to be that FF is more secure than any chromium based browser.
> Listen, people interested look at this OPEN SOURCE code and remove minority code snippets that could be harmful to users, creating acceptable versions of the code. See Brave,
Chromium is a security nightmare. Too much code to maintain and clean for small teams like Brave.
Broken tor windows? Thats braves history. Weeks or days to get updated being dependent on google chromium project? Thats brave.
No thanks.
> Chromium actually uses less RAM and CPU than Firefox,
Chromium browsers run like crap on Linux compared to Firefox.
> Mozilla has analyzed the YouTube algorithm and found out that it actually recommends stuff based on your interests, so if you are into conspiracy stuff,
Mozilla’s RegretsReporter browser extensions for Firefox and Chrome? Lol. An extension? You do realize that people can remove extensions in firefox browser? Lol.
More fearmongering BS.
> why do you think that I need to support a company which believes that Google is not censoring enough yet? This is no alternative, this is nuts!
Lol. Mozilla can not censor anything like youtube can. Firefox is just a browser that offers a different engine to the google monopoly, a browser that can be forked like Librewolf.
Ask yourself this? Whats worse Google or Mozilla?
> 3 % market share is comparatively irrelevant, yes.
If it was, you would not be typing walls of text in desperation to hate on Firefox users.
Replying to you is actually fun, because you are somewhat delusional. lol.
> Firefox users around here, no disrespect meant obviously, usually promote erroneous concepts like “Let’s create a fairly unique browser setup via user.js that will defo make me less fingerprintable than before!
No disrespect? LOL. Really? You hate and hate on FF Users pal.
Again, JS off fails to be a thing in your stupid argument. JS off is a security and privacy improvement. It can be presumed that Sites can not fingerprint all that much with JS off in a browser. It can also be presumed that Hardened FF users are also not all that unique as firefox hardening guides are ultra popular in privacy communities or even on mainstream sites like ghacks.
> “Firefox has site isolation and a sandbox now because Mozilla said so, even so it doesn’t.
Not just Mozilla, but actual people that have a professional tech background reporting on many tech sites that FF does indeed have site isolation security architecture. Your noob views on what site isolation is, can be considered as IRRELEVANT as you lack knowledge.
> The moment Firefox users, especially around here, make me look stupid in comparison to them, is the moment you can officially call me Klaus Schwab in mockery
Why would they call you that? You are just Iron Heart the Firefox hater who knows literally nothing about privacy and security as regards browsers and operating systems.
* [Editor: removed, stay polite, please]
> satisfying the requirements for the term “propaganda”
You sound like a communist.
> I just say that Google’s engineering is overall years ahead of Mozilla’s, which is true.
Constant severe security patches? Bugs, bloat?
> Some open source forks of Chromium like Brave are. Chrome is not.
Brave will never be better than Firefox. Their company is not big enough to be an alternative to google.
And yes Firefox is better than chrome, you finally realized that? lol.
> Chrome is a closed source fork of Chromium. Brave is an open source fork of Chromium. I use Brave. Case closed… Your misinformation is getting old.
But Brave is slow to get security patches and also uses chromium codebase lol which is a negative. There is a choice, use out of date forks like brave or librewolf or use up to date secure browsers that are FOSS like Firefox?
The better choice is obviously Firefox once configured properly and some settings turned off and using good extensions.
No alternatives to Firefox, that is why it gets promoted often by the privacy communities, you want FF to have no market share only shows you prefer google influenced technology like chromium etc.
lol @ this guy defending google chrome and implying that it is better than Firefox.
@Iron Heart
> Which browser is supposedly more secure?
Firefox and its forks like Librewolf. They are more secure browsers than any chrome, edge or chromium clones. Chrome and edge are proprietary, so their code is only maintained by google or M$ which leads to lazy programming because they are closed source software.
Firefox is maintained by a large team and the code is reviewed by the wider FOSS community which is an advantage compared to private company teams maintaining proprietary garbage like chrome. Chromium clones like Brave are reliant on patches from google, which makes such browsers too slow to get security fixes.
> Expect updates from other Chromium-based browsers in the coming days and weeks.
Brave won’t be pathced for weeks? Ever hear of google dependency? Chromium based browsers are dependent on google for security lol.
You think Brave is not reliant on google for patches? LOL. You think Brave is standing up to google? LMAO.
> I think you are confusing security with privacy.
Oh look, a noob level argument from this guy again.
Without good security there is no privacy. They are not separate things.
Proprietary browsers and operating systems are not exactly secure if big corporations can gather huge amounts of data from users like M$ can do with windows, getting hardware ID and IP adresses, telemetry etc. How can those closed source operating systems or browsers be considered secure if big corporations can gather so much data from them?
Privacy should not be really expected when using closed source crap. You would only have to trust. That is why some people choose FOSS instead.
@Andy Prough
> I think it would be better to say that Chrome is basically the new Internet Explorer:
– Horribly insecure by design – check
Closed source crap and that is what the google chromium project was designed for. Chromium was designed to be the base of the chrome browser.
Iron Heart expects browsers like Brave and Vivaldi to be able to keep up with google and clean what they put into the chromium code. Lol. Those browsers will likely not even be patched for weeks, just read the news article. People also complain on how many bugs there are in such browsers.
Better to use FOSS browser like Firefox that gets updated FAST and from the company that maintains the ACTUAL CODE.
Even using standard Firefox is better than using forks from a security perspective because FF forks do not get fast updates.
@ Iron Heart
> Every single article about Chromium security updates turns into a clown parade where Firefox users try to promote their moribund browser.
moribund browser? A browser used by millions. And if it is a moribund browser? Why are you going out of your way to type wall of text replies to people who might think that Firefox may be a better browser than more popular ones like chrome and chromium clones?
> Firefox has no proper site isolation
According to a noob like you. But you see, most people who want to research what features there are in a browser go to more legitimate sources for information and do not listen to someone like you who seems to have no idea what he is talking about.
Mozilla introduced its site isolation security architecture ages ago, you dummy.
Firefox has many safeguards in place. Fission autostart pref set to true is one example.
You spread a lot of BS about Firefox.
> Deplatformingfox, anyone?
Who have they deplatformed? Do mozilla run social media sites like youtube, facebook etc? Your views are stupid.
Mozilla is not google or not in power of social media platforms or search engines like google is.
Firefox is an open source browser, just a browser not a social media website you dummy.
> Yep, because there are no better alternatives. Quality-wise or otherwise.
According to you? you’re a nobody, just some noob on a tech site spreading much misinformation about technology, browsers and operating systems. I Think many more observant commenters would realize that if there ever was a voting system on ghacks, your opinions would get downvoted a lot. If you were on a privacy community forum, much of your views would be seen as pro big tech. That is fine, but you are definetly a pro big tech kind of guy, that is why you are going out of your way to defend google chrome from any criticism. Thats fine though, but you definetly seem to like google chrome.
@ Andy Prough
> As always though, your best bet security-wise is to simply not allow your browser to load js from websites. That’s the most frequent attack vector by far, and the chromium js engine is a horrifying mess.
Iron Heart does not seem to understand that. He actually promotes running JS and thinks turning off it is annoying. He does not give good security advice, he is a noob.
He also types about fingerprinting a lot, but he does not realize that javascript allows a browser to be fingerprinted more so than it would be if JS was turned off.
@Iron Heart
> . Disabling JavaScript breaks most websites (gHacks is a randomly picked example where nothing happens to break, and does not represent most websites at all)
Many websites work with JS turned off in browser. There is also the no script browser extension for better compatibility.
Again, more noob level arguments from you. But thats to be expected from someone who hates Firefox or its forks and promotes Javascript and google chrome.
> Mozilla’s vision of the web is not something I would like to see coming to fruition.
Lol. The guy thinks Mozilla has the power to control the web like google. Very delusional. Mozilla are big players lol, yeah as big as google? hilariously stupid argument from you.
@Karl
> You have posted long rants on this website hundreds of times defending and promoting Google. Your hatred of Mozilla and love of Google blinds you from the truth.
Promoting google is all he ever seems to do. That is fine though if he thinks google engineered products are the best. Lol.
> Hopefully you care more about that than you do ranting about all the websites Mozilla hasn’t blocked.
Funny that, he still has not referenced any legitimate news article about all the censorship and deplatforming that mozilla does. Iron Hearts spreads mindless nonsense with his idea of mozilla having the ability to deplatform and censor the web.
> Being Pro-Google means being in favor of data collection since that is how they actually make money.
Being Pro-Google can also mean being reliant on their products, their updates, their google pixel phones to install operating sytstems like graphene OS etc.
In your world, you do not want an alternative to google engineering? that is why you talk crap about Firefox, you want google to be a monopoly.
> I’ve already said that Google also censors. Mozilla is also strongly in favor of the practice, and is therefore no alternative.
Does this guy actually believe that Mozilla has the power to censor like google, i mean really believe? is the guy for real?
> Using degoogled builds of their open source software is not supporting their data
THEIR. Yes THEIR chromium code. THEIR as in googles code as they have the most commits to THEIR chromium project. Chromium is THEIR invention, they are constantly adding THEIR own code.
Most FOSS is never used as a base to fuel a massive proprietary browser like chrome or edge. That type of FOSS is not worth using because google writes the code, it is not a lean browser engine. It is actually a bloated mess.
> This will age like milk. And I don’t support pro-censorship stances even if they are only verbal so far. If you do, that’s on you. Where there is smell, there is also shit.
Describe where and how Mozilla has developed a censorship algorithm to go after opinions and views it dislikes like google has done with youtube banning conspiracy topics?
Your arguments are stupid.
You say Mozilla and Firefox are irrelevant? How can they censor the web if they are irrelevant? You seem scared of mozilla lol. But why would you fear their censorship if you believe them to be irrelevant?
@Aluminium
> Why rant about browser that has 3% market share and the power to censor nothing?
Likely because many Firefox users have made Iron Heart look like a complete dummy as relates to his poor technical knowledge about browsers. I guess he sort of feels like he has an obligation to try harder to satisfy his ego to prove them wrong whilst failing miserably in the process. Lol. I guess he really hates it when Ghacks posts a firefox article as he seems to want to defend his views about Firefox and that requires him typing walls of texts to reply to some comments that even hint that Firefox is a good browser..
@Aluminium
> He wants the right to demean and make personal attacks against others, so those who disagree with him will stop talking. That is his version of free speech.
He uses asinine walls of texts to silence criticism of some of his mindless nonsense, calls criticism propaganda etc. Lol. In his delusional mind he thinks Firefox is irrelevant, even though millions of people use it as a browser of choice lol and he goes out of his way with wall of text to talk crap about FF. But why spend time typing walls of texts if he thinks FF is irrelevant?
> Yes, he spends ALOT of time defending Google, but that is only to attack Firefox. Despite it looking like he is a hardcore Google fan, I don’t think it is so much that he loves Google, but hates Mozilla.
Defending google is all he ever seems to do, well that and promoting chromium clones. ASk him what he thinks about google engineering? Lol. It is godlike apparently.
Dear brother Iron Heart to question google is to question god itself. Lol at him though actually implying that chrome is a better browser than Firefox. Firefox is open source, chrome is not.
@Anonymous
Oh boy, this website has taken a hit in quality ever since you’ve appeared here. Walls of text (something you say I write, while you write the longest by far) with oftentimes repetitive nonsense, wrong terminology, false assertions, non-sequiturs, strawmen etc. It’s horrible, and I thought it couldn’t get any worse than the “Yash” comments, but here we are. I will only highlight some of the factually wrong things you’ve stated and then repeated ad nauseam:
> They are more secure browsers than any chrome, edge or chromium clones.
Provably false. A browser with amateurish site isolation (content processes hard-limited to eight, so that different websites can still share the same process) and trivial sandbox escapes can’t be more secure than Chromium which has these protections in place. The actual code of Firefox does not support your assertion at all.
> Chrome and edge are proprietary
Proprietary is not the same as insecure. The former means that the code is not public, the latter means that the code has actual design defects. It’s strictly not the same thing.
Also, the “proprietary” claim is nonsense in this context since Chromium is open source, and Chrome is just that with a new logo and some binary blobs that should hardly have any impact on security. There are also open source forks of Chromium, rendering your “point” doubly moot.
> Firefox is maintained by a large team and the code is reviewed by the wider FOSS community which is an advantage compared to private company teams maintaining proprietary garbage like chrome.
Google has a large team as well. So does Microsoft. And the open source Chromium code is vastly more used and audited than Firefox. Even Electron sees more usage than Firefox.
> Chromium clones like Brave are reliant on patches from google, which makes such browsers too slow to get security fixes.
Brave is usually patched within 24 hours after the fixes land in Chromium, which is perfectly acceptable.
> Without good security there is no privacy. They are not separate things.
They are separate. Security is resistance against exploits. Privacy is when the browser does not siphon off user data and takes steps to prevent web tracking. The latter has nothing to do with malware.
You have no sense of coherent and correct terminology, making discussions with you a waste of time.
> Proprietary browsers and operating systems are not exactly secure if big corporations can gather huge amounts of data
Secure means resistant against malware, and has nothing to do with the privacy policy.
> Privacy should not be really expected when using closed source crap.
This argument is irrelevant to me because I use Brave, which is open source. But open source is not the only way to verify whether a product establishes connections, you can also look at the connections closed source software establishes via tools like WireShark. You did not know that, am I right? But then you call me a noob, better clean up at your own house.
> Closed source crap and that is what the google chromium project was designed for. Chromium was designed to be the base of the chrome browser.
Chromium is open source and there are both closed source and open source forks of the code. Brave is an open source fork, Chrome is a closed source fork. What it was “designed for” is irrelevant. Of course Google develops Chromium primarily for Chrome, but that does not mean 1) that Chromium itself is closed source and does also not mean 2) that they are the same product. You use incoherent and incorrect terminology again, rendering any discussion based on such falsehoods useless.
> Iron Heart expects browsers like Brave and Vivaldi to be able to keep up with google and clean what they put into the chromium code. Lol.
Not every part of the Chromium source code “violates” your privacy, therefore I expect them to be able to, yes. Do you think they need to touch every single line of code to make sure that Chromium no longer sends info? This is stupid, you have never developed a piece of software and boy does it show.
> moribund browser? A browser used by millions.
3% market share, down from 30% market share peak, and still declining, qualifies for “moribund”. Even the most hardcore of Firefox fanboys usually admit that it is currently not doing well at all.
> Why are you going out of your way to type wall of text replies to people who might think that Firefox may be a better browser than more popular ones like chrome and chromium clones?
Because there is the wrong impression that Firefox can improve your privacy and fights for a free web, both of which are false. Misinformation of Firefox fanboys about all competitors also makes me write stuff because misinformation is malicious and should be disputed by definition.
> Mozilla introduced its site isolation security architecture ages ago, you dummy.
Hard-limiting content processes to eight means that it is not site isolation since multiple websites can still share the same content processes. This is the design of amateurs and is no the same as the full site isolation Chromium has implemented for years now. It seems that you are the dummy here because you are not aware of the actual Firefox code.
> Fission
The marketing term for site isolation, which is (as said) incomplete.
> You spread a lot of BS about Firefox.
And you have no idea about the actual Firefox code.
> Who have they deplatformed? Do mozilla run social media sites like youtube, facebook etc? Your views are stupid.
They can absolutely throw their own users under the bus. Censorship of websites at the browser level is possible no problem, and so is reporting websites users have visited back to the mothership.
> Mozilla is not google or not in power of social media platforms or search engines like google is.
I never said that they have the same reach is Google. These are words that you and other people try to put in my mouth, but you don’t actually find them anywhere in my texts. I’ve only claimed and continue to claim that Mozilla has the power to throw their own users under the bus, and the more people use their product, the bigger this problem becomes. So I consequently don’t want them to regain any market share.
> According to you?
No, according to actual code comparisons. Firefox lacks several key exploit mitigations.
> I Think many more observant commenters would realize that if there ever was a voting system on ghacks, your opinions would get downvoted a lot.
Do you think I care? You are one of those people who think that, if 3 clowns utter the very same joke, that this adds any legitimacy to the joke. From my point of view, when there are 3 clowns instead of just 1 clown, the joke has just become much bigger. So then the whole Firefox clown parade downvotes me, so what? Does this magically make your misinformation, lies, and wrong terminology correct? No, it only proves that gHacks has been taken over by tribalist minds who downvote factually correct assertions, which is sad.
But all in all, you are right in that I would not waste my time with people who mistake the “downvote” (= what was said was inappropriate) button for the “disagree” button. I would end up doing the same thing that upvote / downvote buttons always seem to achieve – I would seek out my own tribalistic group, in this case the Brave community, where my words would get upvoted instead. You can go to the Firefox community and get your posts upvoted, and so we merrily part ways, each to his own tribalistic group, so that no discussion takes place anymore. Happy little filter bubble you got in your mind, but I guess it’s the standard of dealing with different opinions these days. Again, sad.
> If you were on a privacy community forum, much of your views would be seen as pro big tech.
Doubt it. There are some people who can differentiate between data collection and privacy violations on the one hand and the open source underlying code on the other. You are not one of them.
> That is fine, but you are definetly a pro big tech kind of guy, that is why you are going out of your way to defend google chrome from any criticism. Thats fine though, but you definetly seem to like google chrome.
Same as above, you don’t differentiate between actual privacy violations and the underlying code. There are forks of both Chromium and Android that go out of their way to protect user privacy. Such forks also send no PII to Google.
In your mind, I should make big drama around the fact that Google e.g. wrote Android’s calculator. The calculator has been shown to send no info back to the mothership, but in your opinion, I should lose my shit solely based on the fact that Google wrote it. That this is retarded should be self-explanatory, your stance is irrational to the core. Why should I stop using e.g. Brave or GrapheneOS when they send no data to Google. Because Google also wrote other parts of the code that have nothing to do with my privacy? Sorry, but that’s no reason to stop using anything.
> He actually promotes running JS and thinks turning off it is annoying.
I said that meticulously maintaining one’s whitelist of what to allow for each and every website one visits is impractical for most people, which is true. It’s the same reason why adblockers are popular, their curated lists take care of that instead of having to do it manually. You seem confused and / or you deliberately misrepresent what i wrote.
> He also types about fingerprinting a lot, but he does not realize that javascript allows a browser to be fingerprinted more so than it would be if JS was turned off.
Most fingerprinting defenses, including those of the Tor Browser Bundle, are written with the assumption in mind that JavaScript is turned on, again because most people have no time to meticulously maintain a whitelist. And fingerprinting is possible with CSS and partially at the network level as well, but you knew that, didn’t you (I doubt it…)?
> Many websites work with JS turned off in browser.
Factually wrong. Any experiment with JS turned off on all websites can and will prove me right here.
> Mozilla are big players lol, yeah as big as google?
I never said they have the same reach, just the same mentality. And they can totally throw their own users under the bus no problem, see above.
And by using a Chromium browser other than Chrome I do not support their potential browser-level censoring, since anything landing in Chromium can be patched out. Whatever they do in Chrome is irrelevant to me, Chrome and Chromium are not the same thing in terms of what can be patched out. As a Chromium / Brave user I also don’t need to use Google Search, which nullifies any search engine level censorship they could do.
> Promoting google is all he ever seems to do.
I never promote their data collection and other user-hostile actions, stop spreading misinformation.
> That is fine though if he thinks google engineered products are the best.
They are better engineered than Mozilla’s products. That’s all. The amateurs at Mozilla are five years behind minimum in terms of implementing exploit mitigations. I use Google products that, unrelated to security, also improve privacy by ripping out all outbound connections from the code. I have a well-engineered product at hand that provably does not violate my privacy, I don’t need Mozilla. Switching to Mozilla products would lower both security and privacy for me.
> Funny that, he still has not referenced any legitimate news article about all the censorship and deplatforming that mozilla does.
I have referenced articles talking about Mozilla’s pro-censorship stance multiple times, including under this article. What you say is easily proven wrong.
And that they can do censorship at the browser level is common sense. If uBlock Origin can block connections, so can Mozilla since the browser runs with higher privileges.
> Iron Hearts spreads mindless nonsense with his idea of mozilla having the ability to deplatform and censor the web.
Censor the web for users of their browser, yes. The rest I haven’t ever claimed.
> Being Pro-Google can also mean being reliant on their products, their updates, their google pixel phones to install operating sytstems like graphene OS etc.
No, Google makes money with data collection and data analysis. Brave and GrapheneOS, for example, actively hinder them from collecting data about me, data they could collect if I used Google Chrome or stock Android.
In your mind, I should freak out because Google also wrote the calculator of GrapheneOS. Sorry to use that example again, it works so well for showing your fallacy / ignorance.
> In your world, you do not want an alternative to google engineering?
Yes, if it’s better than Google’s engineering. Otherwise I have no reason to switch.
> that is why you talk crap about Firefox, you want google to be a monopoly.
LOL, never heard such nonsense and I have heard many shit claims about me here. Pointing out that Firefox is missing adequate exploit mitigations, which is the truth, is the same as wanting a Google monopoly? How about Mozilla actually fixing their shit? Would that be an option?
> THEIR. Yes THEIR chromium code. THEIR as in googles code as they have the most commits to THEIR chromium project. Chromium is THEIR invention, they are constantly adding THEIR own code.
> That type of FOSS is not worth using because google writes the code
It can be fully audited and forked, that’s all one needs to know. All other considerations you make here fall under “smoke screen”.
It’s evil because “Google wrote the code” LMAO. Listen, people interested look at this OPEN SOURCE code and remove minority code snippets that could be harmful to users, creating acceptable versions of the code. See Brave, Ungoogled Chromium, Bromite, LineageOS, GrapheneOS etc. for more info. That this code can also be used for closed source forks like Chrome or Edge is irrelevant to me, since I don’t use them.
> it is not a lean browser engine. It is actually a bloated mess.
Completely unrelated to what you said before, also completely unrelated to security and privacy. Still, Chromium actually uses less RAM and CPU than Firefox, and consistently performs better in various benchmarks, so if it is in fact a bloated mess, what does that mean for FF?
> Describe where and how Mozilla has developed a censorship algorithm to go after opinions and views it dislikes like google has done with youtube banning conspiracy topics?
You know of Mozilla’s “YouTube Regrets”? If you don’t, check it out. Mozilla has analyzed the YouTube algorithm and found out that it actually recommends stuff based on your interests, so if you are into conspiracy stuff, you will get recommended other such videos. Big surprise right there! Since Mozilla feels like playing nanny and wants to stop people from going deeper into the *shudder* conspiracy theories *shudder*, they want Google to hide such content from users ’cause reasons, you know. They think Google is not heavy-handed enough in their YouTube censorship. Apart from the fact that this is hilarious, as it shouldn’t be Mozilla’s business at all, why do you think that I need to support a company which believes that Google is not censoring enough yet? This is no alternative, this is nuts!
> You say Mozilla and Firefox are irrelevant? How can they censor the web if they are irrelevant?
3% market share is comparatively irrelevant, yes. No, that does not exactly stop them from throwing *their own* users under the bus. Anything else you want to insinuate here is probably something I have never said or claimed.
> Likely because many Firefox users have made Iron Heart look like a complete dummy as relates to his poor technical knowledge about browsers.
Firefox users around here, no disrespect meant obviously, usually promote erroneous concepts like “Let’s create a fairly unique browser setup via user.js that will defo make me less fingerprintable than before! Yeehaw!” and “We need a different engine because some web standards are evil, even though support for them can easily be turned off in Chromium forks.” and “Firefox has site isolation and a sandbox now because Mozilla said so, even so it doesn’t. That it gets hacked less has nothing to do with its low market share at all btw!”
The moment Firefox users, especially around here, make me look stupid in comparison to them, is the moment you can officially call me Klaus Schwab in mockery (who loves Mozilla btw, according to the WEF partner website that also has Google on it, big oopsie right there, since Schwab aggressively engages in information warfare).
> calls criticism propaganda etc.
What you say is factually wrong yet is aimed at promoting Firefox, satisfying the requirements for the term “propaganda”
> Dear brother Iron Heart to question google is to question god itself.
Anything can and should be questioned. I just say that Google’s engineering is overall years ahead of Mozilla’s, which is true. Does that make them god? I doubt it.
> Lol at him though actually implying that chrome is a better browser than Firefox.
Some open source forks of Chromium like Brave are. Chrome is not. Don’t put words in my mouth.
> Firefox is open source, chrome is not.
Chrome is a closed source fork of Chromium. Brave is an open source fork of Chromium. I use Brave. Case closed… Your misinformation is getting old.
Iron Heart is a free speech absolutists only when it comes to him being censored, He complains about censorship, but is regularly censored on ghacks for rude comments and yet he still posts here regularly. He wants the right to demean and make personal attacks against others, so those who disagree with him will stop talking. That is his version of free speech.
Yes, he spends ALOT of time defending Google, but that is only to attack Firefox. Despite it looking like he is a hardcore Google fan, I don’t think it is so much that he loves Google, but hates Mozilla.
> I don’t think it is so much that he loves Google, but hates Mozilla
He is consumed
>Deplatformingfox, anyone? Censorship and “turn on tools that amplify factual voices over disinformation” will make the web a better place according to the overpaid Mozilla CEO.
Firefox does not block any website, however your beloved Google does.
https://www.ghacks.net/2022/07/25/google-chrome-is-blocking-all-downloads-from-portable-apps/
@Karl
That’s not political censorship at all. They are clearly targeting branding violations there.
Mozilla is partnered with Piere Omidyar and fought fake news(TM) before it was cool: https://www.firstpost.com/tech/news-analysis/mozilla-partners-with-piere-omidyars-full-fact-foundation-to-fight-fake-news-online-3913097.html
Pushed the CEO out for wrongthink, still has the YouTube Regrets a.k.a. “Google still doesn’t censor YouTube enough according to us” program running etc. And this company I am supposed to strengthen? Mozilla’s vision of the web is not something I would like to see coming to fruition.
Not saying that Google is not censoring shit (thanks for putting words in my mouth btw), but to push Mozilla as the alternative is trololololololol of you, Karl.
Hey * [Editor: removed, please use the correct username], quick question. How is Firefox going to censor anything with only 3% market share?
Short answer, they can’t because they lack both the resources and the influence. Which leads me to my next question. Why rant about browser that has 3% market share and the power to censor nothing?
If a crazy man on the street screams the world is ending, is it really necessary to write war and peace length rants on every single article about the homeless explaining why he is wrong?
@Aluminium
> How is Firefox going to censor anything with only 3% market share?
They can absolutely censor websites and report the websites you go to within Firefox.
> Short answer, they can’t because they lack both the resources and the influence.
They can definitely sell out their own users… And Chrome and Edge will be censoring as well, so good luck switching to that. Maybe some Firefox forks or forks of Chromium will remain neutral. Maybe.
> 3% market share
Just stopped there to briefly laugh at this, on to the next “point”…
> crazy man on the street
…has to be the one supporting censorship and a fundamentally unfree web. You are on the right track with the We.need.more.than.Deplatformingfox.
@Andy Prough
> 99% are probably bots and NPC’s
Delusional.
>”Why rant about browser that has 3% market share and the power to censor nothing?”
When you consider that over 99% are probably bots and NPC’s, then 3% could be huge.
>That’s not political censorship at all. They are clearly targeting branding violations there.
Oh sorry, I thought you were a free speech absolutist. I didn’t know you cared only about political speech, specifically political speech you agree with. Censoring political speech bad, all other forms of censorship good, ok got it.
>Not saying that Google is not censoring shit (thanks for putting words in my mouth btw), but to push Mozilla as the alternative is trololololololol of you, Karl.
Please show me my quote where I am pushing Firefox. You can’t because I never have. Don’t throw rocks in a glass house. You can’t be pro-Google and and pro-free speech at the same time.
You have posted long rants on this website hundreds of times defending and promoting Google. Your hatred of Mozilla and love of Google blinds you from the truth.
Here are links of Google working with the CCP to go after political dissidents. Hopefully you care more about that than you do ranting about all the websites Mozilla hasn’t blocked.
https://theintercept.com/2019/07/11/china-surveillance-google-ibm-semptian/
https://tfiglobalnews.com/2021/09/14/google-provided-user-data-to-the-ccp-which-helped-it-in-sacking-hong-kong/
@Karl
> Oh sorry, I thought you were a free speech absolutist
Free speech absolutists are usually the same people who also care about property rights. You can’t distribute Chrome and Firefox (and other software) as portable apps without changing the branding, since the portable builds are not official builds of the actual brand owner. You may be able to fork the open source code under the respective licenses, with a new brand of your own making. The people of PortableApps being too stupid to come up with a new logo + name is why they are blocked now, sorry to break this to you.
> Please show me my quote where I am pushing Firefox
Karl, I don’t have a protocol of your posting history and I won’t search 100 articles for your useless comments only to prove that you are a raving fanboy. I will remind you of it the next time you run your promotion again. I also believe your rabid reply proves my point.
> You can’t be pro-Google and and pro-free speech at the same time.
Using their open source code is not being Pro-Google. That’s retarded. If that were the case, all LineageOS or GrapheneOS users would be “Pro-Google” as well. Same for Ungoogled Chromium. Totally nuts.
> You have posted long rants on this website hundreds of times defending and promoting Google
Can’t remember, sorry. Using a non-Google build of their open source code is not being Pro-Google. Being Pro-Google means being in favor of data collection since that is how they actually make money.
> Your hatred of Mozilla and love of Google blinds you from the truth.
I’ve already said that Google also censors. Mozilla is also strongly in favor of the practice, and is therefore no alternative. How is that not the truth, buddy?
> Here are links of Google working with the CCP to go after political dissidents.
Uh oh, the shaming begins. Sorry, I don’t use Chrome / Google Search / GMail / stock Android, I fear you are barking on the wrong tree here. In no way do I support their data collection. Using degoogled builds of their open source software is not supporting their data collection either, by definition. Nice try though, I give you that.
> Hopefully you care more about that than you do ranting about all the websites Mozilla hasn’t blocked.
This will age like milk. And I don’t support pro-censorship stances even if they are only verbal so far. If you do, that’s on you. Where there is smell, there is also shit.
For some folks censorship means censoring far right people and theories. Nothing to do with ethics and morality. Sad.
For absolute free speech follow MyPillow guy. There’s your free speech against deplatforming fox.
Yes, I use Chrome; yes, the updates each week seem odd; yes, update with a few clicks and minutes. I’m okay–on with the show.
No, Firefox is my main browser. Google sometimes works better for certain sites. It’s there if I need it.
Thanks for the update news!
If the issues are reported by Oppo – not a tech security company but hardware selling company, maybe then issue is with underlying code in the first place. No end it seems. Which company is gonna report security issues next? Mcdonalds.
@Yash
You do realize that Oppo is in charge of their version of Android for their phones, right? Thus coming into contact with Chromium… gHacks comment section at its finest.
Android version and Chromium, yeah both are intertwined with each other. Ghacks comment section at its finest indeed.
If even a company which doesn’t even base their business around browsers is finding vulnerabilities, then underlying code is beyond repair.
@Yash
> Android version and Chromium, yeah both are intertwined with each other
Yep. Chromium is preinstalled and also serves as the web view.
> Ghacks comment section at its finest indeed.
Indeed.
> underlying code is beyond repair
You mean like having no real site isolation after a decade and suffering from trivial sandbox escapes and having shared resource leaks all over the place? Oh wait, that wasn’t Chromium.
Mate last comment was full of puns, exactly opposite of what you wrote in response to that.
Anyway Chromium will always have huge issues. If chromium project was to be managed by any other company than Google, take Brave for example then there will be less issues with Chromium. Simple as that. Google is just hoarding chromium with unnecessary bugs otherwise known as latest security updates.
Adobe Flash (every week):
This update fixes a critical security issue that is being exploited in the wild.
Google Chrome:
Adobe Flash needs to go, as it has too many security issues.
*** Skips forward a few years ***
Google Chrome (every week):
This update fixes a critical security issue that is being exploited in the wild.
I think it would be better to say that Chrome is basically the new Internet Explorer:
– Horribly insecure by design – check
– Making the web worse daily by its very existence – check
– Impossible to ever fully fix – check
– The only solution is to replace it with something better – check
– The problem being that over half of users are addicted to its use – check
@Andy Prough
Every single article about Chromium security updates turns into a clown parade where Firefox users try to promote their moribund browser. If Firefox is what you mean by “something better”, which I guess it is, since you are promoting it in your other posts as well… Then bruh. The truth is that Firefox used to be an outdated single process application while Chromium started out multiprocess. “But this is outdated info” you might think now, to which I would reply “not quite”, because you can’t foist a multiprocess architecture unto a single process application. I mean, you can, but it takes years and years and cross site leaks will plague you along the way, as is the case with Firefox.
Firefox has no proper site isolation – they hard-limited the content processes to eight like amateurs, meaning that different websites can still share the same process. Firefox also suffers from trivial sandbox escapes and various cross resource leaks as well. So much for “better”, as if a frankensteined single process application that still doesn’t have site isolation is any better.
And “can never fully fixed”, what does “fully fixed” mean, according to you? No security issues ever again? Sorry pal, we are talking about a codebase the size and complexity of an operating system here, so that is unlikely to occur for any browser EVER.
> Making the web worse daily by its very existence
Deplatformingfox, anyone? Censorship and “turn on tools that amplify factual voices over disinformation” will make the web a better place according to the overpaid Mozilla CEO.
> The problem being that over half of users are addicted to its use
Yep, because there are no better alternatives. Quality-wise or otherwise.
@IronHeart – I’m not using Firefox at the moment. I used to use it with Arkenfox and wrote a few thoughts about it on Ghacks at the time.
If you are worried about proper sandboxing of processes, then your best bet is to open browsers in disposable VMs for a variety of uses, such as banking, video streaming, etc. Qubes OS has a good way to set that up. And Whonix. Firefox has an add-on called “Multi-Account Containers” that can help you.
As always though, your best bet security-wise is to simply not allow your browser to load js from websites. That’s the most frequent attack vector by far, and the chromium js engine is a horrifying mess. You can get the info you need from a lot of sites without js. For example, Ghacks works perfectly fine without it.
@Andy Prough
> open browsers in disposable VMs
Of course you can come up with non-standard scenarios like this to avoid any discussion, but I think we both know that this is both unlikely and impractical. You can’t excuse trivial sandbox escapes with “Set up a VM around it, it will be fine.”… Sorry but no sorry, that doesn’t fix the issue and doesn’t relieve anyone of the responsibility to improve the code.
> not allow your browser to load js from websites
The second unlikely and impractical suggestion. You know why adblockers are so popular? Because they come with curated lists that aim to block preselected scripts, because not everyone has the time to maintain their personal whitelist. Disabling JavaScript breaks most websites (gHacks is a randomly picked example where nothing happens to break, and does not represent most websites at all) and then we have the “time to maintain your personal whitelist” debate. The popularity of adblockers are based on the very fact that your suggestion is unworkable.
They don’t have an in-the-wild exploit every week, and I don’t recall them being the driving force behind retiring flash (that was Apple IIRC), but you still make a good point.
I think it would be better to say that Chrome is basically the new Internet Explorer:
– Horribly insecure by design – check
– Impossible to ever fully fix – check
– The only solution is to replace it with something better – check
– The problem being that over half the world is addicted to its use – check
welcome to google everyday-is-a-patch-day .. chromium is a security joke
> chromium is a security joke
Which browser is supposedly more secure?
Ungoogled Chromium
@b’Aaal
That’s Chromium minus the Google connections, pal. I think you are confusing security with privacy. Security = resistance against exploits.
Would you be happier if they delayed updates and only patched once per month? This is risky and crazy, and developers doing that are too lazy to create a new build in reality.