Firefox 102: Query Parameter Stripping improves privacy
Mozilla plans to introduce a new privacy feature in the upcoming Firefox 102 web browser. Called Query Parameter Stripping, it is designed to remove tracking parameters from web addresses to improve user privacy.
Mozilla integrated the privacy feature in Firefox Nightly 96 originally for testing purposes. Some sites and services add tracking parameters to links to track users across sites. Facebook, for example, appends a unique fbclid string to all outgoing links, which is unique for all users on the site.
The parameter may be used to identify and track users. Facebook can use it if one if the service's scripts is running on the target site, but others may use it as well, as the identifier is unique.
One of the main advantages of using URL query string identifiers is that these don't rely on cookies or other data bits.
The initial query parameter stripping version in Firefox 102 uses a blocklist to strip known tracking parameters from top-level URLs; this includes navigational events such as opening a new tab, clicking on links, redirects or window.open() events.
Mozilla decided to limit the processing to top-level navigation events to reduce the likelihood of web compatibility issues. Navigational events across the same site are not processed because of that.
Navigational tracking protection is enabled in Private Browsing Mode and when Firefox's Enhanced Tracking Protection feature is set to Strict. Firefox supports standard (default), strict and custom Enhanced Tracking Protection modes.
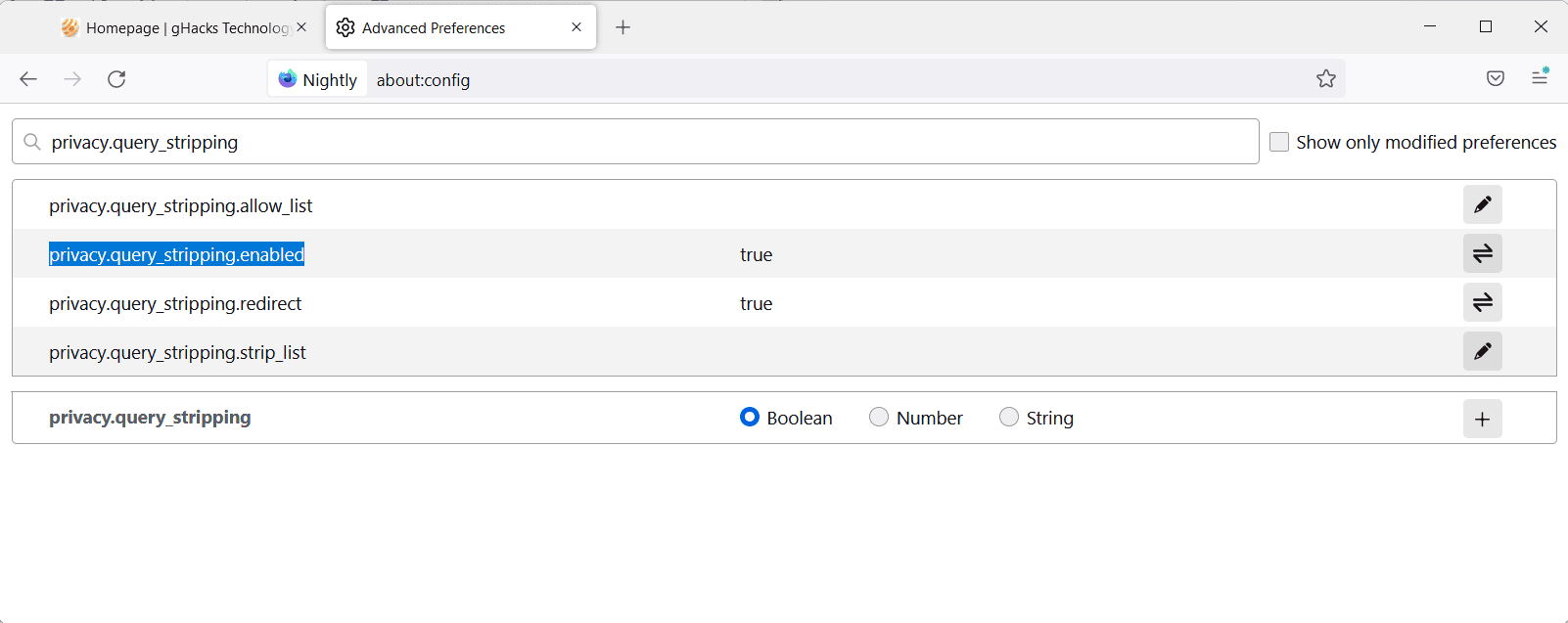
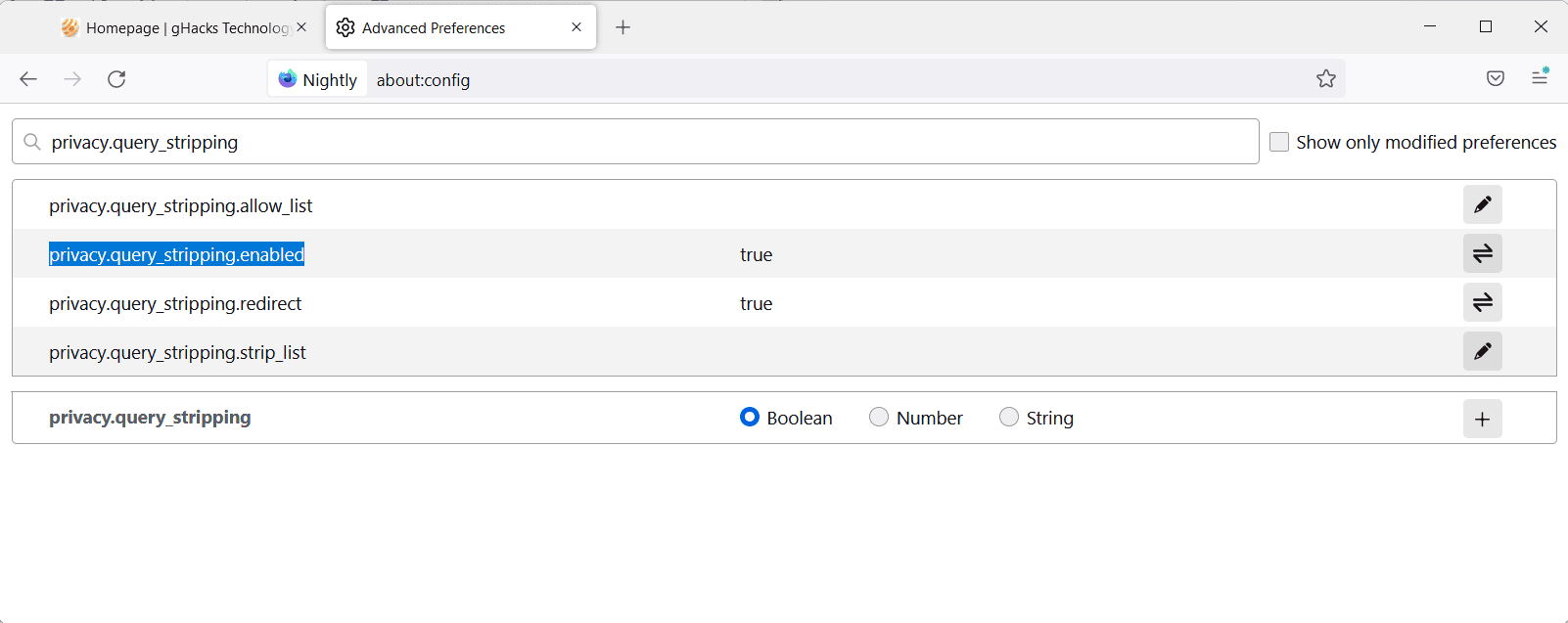
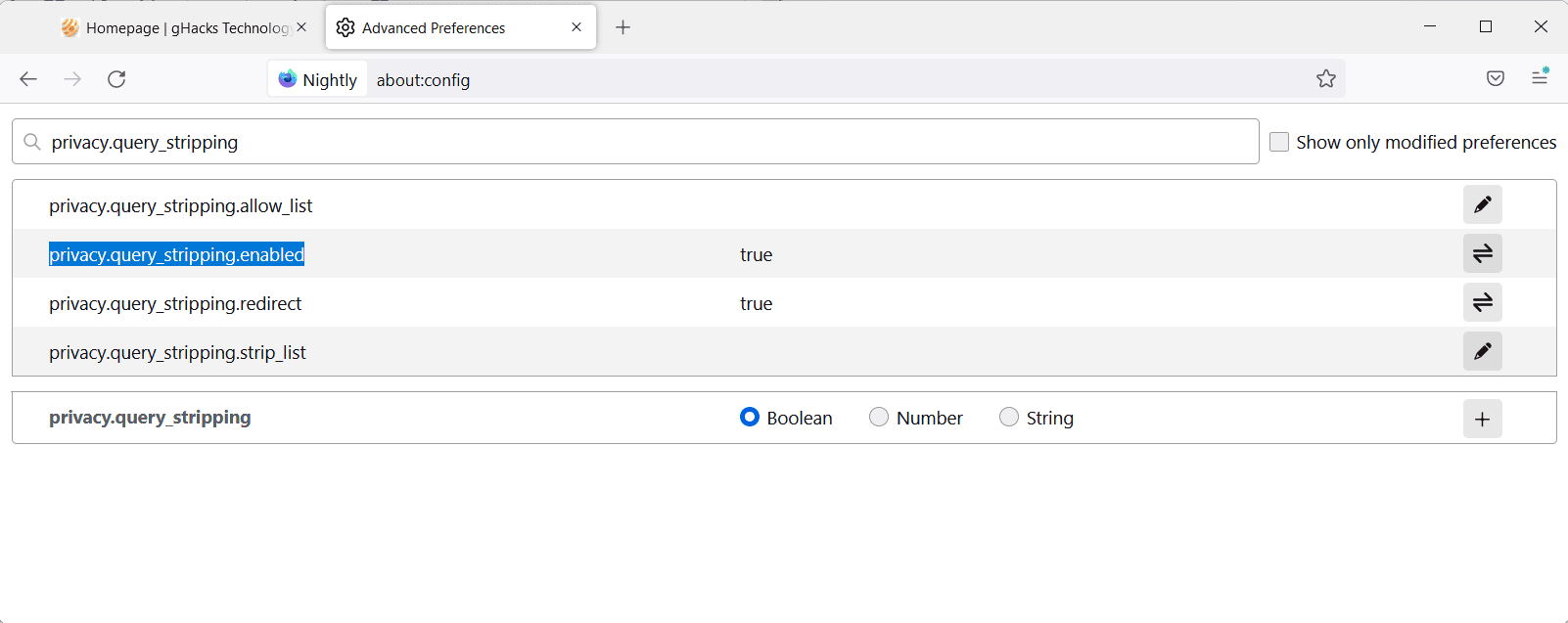
The preference privacy.query_stripping.enabled determines whether the feature is enabled or disabled in Firefox. Set the preference to TRUE on about:config to enable the parameter stripping.
Mozilla added support for custom parameters that users can add to Firefox to have them stripped automatically with the rest of the built-in stripping. The preference privacy.query_stripping.strip_list accepts query strings and uses space as the delimiter.
Brave Browser has a similar feature that is removing query strings from web addresses. The list that Brave uses is public; it includes Facebook's tracking strings, but also strings that other services use to track users across the web.
Closing Words
Firefox's query string protection improves user privacy, but only in private browsing windows or when the browser's Enhanced Tracking Protection setting is set to strict; this is a limitation, and most Firefox users may not benefit as much from the privacy improvement because of that.
Still, it is a step in the right direction, and there is a chance that Mozilla is enabling the feature for the standard mode as well. Most Firefox users may want to switch to strict tracking protection in the browser, as it improves their privacy while using the browser.
Firefox 102 will be released on June 28, 2022.
Now You: do you use your browser's tracking protection features?





















Following on from Tom’s Ublock Origin list from ClearURLs link, here is one for CDNs, which may, or may not (as it has not been updated in a couple of years), do away with another extension, Decentraleyes.
https://raw.githubusercontent.com/LanikSJ/ubo-filters/main/filters/cdn-filter-list.txt
I suspect Mozilla will conveniently excuse the search tracking URL that they use to track users search queries. lol
@Tony
The referral Firefox uses on Google can’t be used to track specific users because it is generic (not generated per user). That being said, Firefox users are being hypocrites here on a regular basis, because they attack Brave for having used such a generic referral on Binance at one time, while their browser literally does the same thing for every single Google search a user performs. One rule for me, one for thee. But yeah, it is not a tracking threat in either case.
> they attack Brave for having used such a generic referral on Binance at one time
way to be misleading – the outrage, and rightly so, was for altering TYPED URLS, not searches – even EichBat admitted it and apologized
> even EichBat admitted it and apologized
No, here is the the official statement from Brave Software and they show you that your beloved browser does the same thing on Google: https://brave.com/referral-codes-in-suggested-sites/
Note that this is the official statement of the company of which Brendan Eich is just one small part. There is nothing to apologize for really, even as a token gesture, since the privacy impact on the user was zero at all times, as the referral was generic and not generated per user. Grow up and get over it, and most importantly, stop being such a hypocrite.
> TYPED URLS
What is that supposed to mean? URLs are URLs, there are no “TYPED URLS” as a separate class, hahahahahaha. Btw, you type in the search term as well and the resulting URL would totally work without Firefox’s referral. Firefox uses the referral to get dirty ad money from Google. It’s the same thing but you will defend your hypocrisy tooth and nail. Funny.
@Tony,
> I suspect Mozilla
they use to track users search queries. lol
Your own hand is “front” from your point of view, but “back” from the side you are facing.
In short, even reason is “up to you, produces values that are diametrically opposed”.
At least, Firefox and Brave deserve more credit than those (Google, Microsoft, Opera, Facebook:Meta, etc.) who are silent on this issue (query strings from web addresses) without shedding light on it.
The important thing is to improve the ability of users to “know, understand and deal with the truth” themselves. The challenge is highlighted in this topic (article and Comments: @Tom Hawack).
@Owl, I’m think you ran that through a translator, because I barely understand what you said, so excuse me please if my understanding you is wrong.
Anyway, please don’t misunderstand calling out a company for hypocritical actions as a blind view.
Things change because people complain or provide feedback otherwise. I still use Firefox as my main browser and have so for years. That said, they claim to be a privacy-focused browser while at the same time gathering as much data on you as possible (if you don’t stop them). This has been proven fact multiple times. But as long as I can control Firefox to prevent it, it’s the better choice at the moment.
Why would any of those company tune in just yet when they have a vested interest in perpetrating these kinds of things. They will only do so when they find another way to achieve such things thus making for great PR and allowing them to continue doing what they are doing. Perhaps the companies that are or have been proactive in this space have already figured it out.
Mozilla has been capable of doing this and a great deal more via extensions for many years now. Extensions have always been and always will be a great asset to your browser and needs regardless of what browser you are using. I am sure everyone here is aware of that.
Out of curiosity I tried the test of ClearURLs with CleanLinks: 3\4 except the first. Same result after I added ClearURLs filter for uBlock, but this is a test to check if ClearURLs extension works correctly.
Redirected to Mozilla in the second test.
Martin, for the gazillionth time, Thank You for the info!
Looks like I’ve been seriously behind the curve when it comes to “Query Parameter Stripping”. I don’t even know how long I’ve been using the ClearURLs add-on and had no idea it was circling the drain. On the ClearURLs add-on page the dev mentions: “ClearURLs is currently being completely rewritten to make it better and faster. This may result in longer delays than usual when processing issue tickets.” No timeframe. On the gitlab page for the add-on there is a test link “https://test.clearurls.xyz/” where it failed two of the four tests. That said, Skip Redirect failed the same tests, for whatever that’s worth.
On the Skip Redirect add-on page there is a test link: “https://outgoing.prod.mozaws.net/v1/e066c7316c8b360a67103ff9a047f017fde9eb94365c9e5b517bde5a59d29ff1/http%3A//www.google.com/chrome/%3For-maybe-rather-firefox=http%253A%252F%252Fwww.mozilla.org/”. Using Skip Redirect I was sent to mozilla, when using ClearURLs add-on I ended up on google. For Now, I’ll be using Skip Redirect.
I’ve never been one to throw a couple thousand filter entries at a problem because I can’t help but worry about any negative performance impact with uBO. If there is one. I’ve always been very conservative with the filter lists that I use and I’m currrently using 208,000+ filters and it’s very very easy to get it over 300,000. I can remember when ALL we needed was EasyList and EasyPrivacy filter lists but those days are gone forever! :(
Today I’ve enabled the built-in filter list “AdGuard URL Tracking Protection”. I’ve added the two custom filter lists mentioned in the comments but have left them disabled for now to see what I see. Looks like I’ll be using the network tab in the dev tools more often. I’ve also enabled the config setting for “privacy.query_stripping.enabled”. And moved from ClearURLs to the Skip Redirect add-on.
And a big Thank You to Tom and Everyone else for the useful info in the comments!!!
Peace!
I want to add that I use the Disable Javascript add-on in case any malicious redirects send me to a new website javascript will be disabled. I have the default state set to javascript disabled and I just have to click on the add-on toolbar icon to whitelist a website. Definitely overkill because I’ve never experienced a redirect like that but better safe than sorry!
Nice article Martin and a good update for Firefox.
Also great comments @Tom Hawack
Nice improvement. Thanks for the article! :]
I use the ‘CleanLinks’ extension (Firefox) which combines parameter removal redirects skipping.
Be noted that Mozilla itself on its [addons.mozilla.org] pages uses utm parameters as well as redirects (the latter when opening an external page). The former is not manageable by ‘CleanLinks’ because it originates from HistoryState (unless cookies are blocked), the latter is always handled by ‘CleanLinks’. Blocking HistoryState like the ‘ClearUrls’ extension allows it is problematic on many sites unless it includes a whitelist.
These utm parameters lead me to refuse cookies for AMO, not only for the principle but mainly because of possible confusion : for instance when opening an extension’s page which is already bookmarked but… without the utm parameters, which makes me think the page isn’t bookmarked : insane, Mozilla, insane.
Firefox 102 aiming at removing query parameters is a good thing of course for users who aren’t assisted by a dedicated extension. Hoping it’ll be applied on its very own pages.
> Hoping it’ll be applied on its very own pages.
Just tested this in Nightly, which has the feature set to true by default, but no, it doesn’t work on [addons.mozilla.org]…
That was to be expected.
Go to about:config and edit the domains listed under “extensions.webextensions.restrictedDomains” and you’ll be able to run stuff against *.mozilla.* again.
> [Query Parameters Stripping included in Firefox Nightly] doesn’t work on [addons.mozilla.org] …
Thanks for that info, @nicolasjan.
> That was to be expected …
Indeed. I admit otherwise I would have considered Santa Claus being a myth as a myth itself.
“Do what I say, don’t do what I do”.
Do I understand it correctly that it will just do the same that addons like ClearURLs already do? Stripping the utm_somethings and similar from the URL?
> Do I understand it correctly that it will just do the same that addons like ClearURLs already do? Stripping the utm_somethings and similar from the URL?
Yes, but ClearURLs is badly maintained right now (there are various issues on GitHub with no response from the author)…
Instead, you can use dedicated lists in uBlock Origin that do the same.
Like the built in list: “AdGuard URL Tracking Protection”
Or these ones, you’ll have add to “Custom”:
“ClearURLs for uBo”:
[https://raw.githubusercontent.com/DandelionSprout/adfilt/master/ClearURLs%20for%20uBo/clear_urls_uboified.txt]
And/or:
“Actually Legitimate URL Shortener Tool”:
[https://raw.githubusercontent.com/DandelionSprout/adfilt/master/LegitimateURLShortener.txt]
I had no idea, thanks. Already added to uBO.
@nicolaasjan,
> [‘Actually Legitimate URL Shortener Tool’] and/or [‘ClearURLs for uBo’]
“And” I’d say :)
The ‘Actually Legitimate URL Shortener Tool’ list :
Description: In a world dominated by bit.ly, adf.ly, and several thousand other malware cover-up tools, this list reduces the length of URLs in a much more legitimate and transparent manner. Essentially, it automatically removes unnecessary $/& values from the URLs, making them easier to copy from the URL bar and pasting elsewhere as links. Enjoy.
The ‘ClearURLs for uBo’ list :
Description: Want to use ClearURLs’ tracking protection without installing another extension? This list is a (unofficial) version of the ClearURLs rules, designed for use in uBlock Origin and AdGuard.
I use both, together with the ‘CleanLinks’ extension.
Cleaning query parameters is a list approach, not an algorithmic one : some parameters are necessary.
Hence all depends of the list(s). Of course several lists may induce redundancy. These lists must be updated, obvious with uBO, less obvious when integrated to an extension such as ‘CleanLinks’ or ‘ClearURLs’.
Side-note : the time spent for OS maintenance is amazing if one wishes to be up-to-date, and an increasing part of this time is due to dishonest practices which are becoming legion and not specific of ‘bad guys’ : everyone (every domain) does it, or more and more anyway : tricking, be it for wrecking, for combating the wreckers or for business, has become the norm. A pain.
@Tom Hawack
This ‘CleanLinks’ looks interesting, but it seems to me as well that it requires a little bit of learning curve after seeing the icon menu.
I currently use ‘Actually Legitimate URL Shortener Tool’ on uBlock and SkipRedirect. As far as you know after using it what are the additional benefits?
Side-note: Ah! certainly when we were younger we did not think about a future where we lose time to understand how to clean tracking parameters or to skip redirect pages. Double pain.
@Shiva, hi there!
> I currently use ‘Actually Legitimate URL Shortener Tool’ on uBlock and SkipRedirect
As you I use the ‘Legitimate URL Shortener Tool’ filier list for uBO but as well the ‘ClearURLs for uBo’ filter list : both are complementary, no redundance, different scoped
Concerning the ‘SkipRedirect’ extension, it’s been my choice as well, together with the ‘ClearURLs’ extension.
Then I discovered ‘CleanLinks’. Why did I switch to the latter?
1- Because ClearURLs has a feature handling the so-called HistoryState, a process which allows qeary parameters to bypass query parameters blockers, to make it short. But this feature is problematic on several sites so I had to disable it given the lack of whitelist.
2- ClearURLs’ query parameters list is not frequently updated, is not editable, handles no whitelist as well.
Removing ClearURLs and relying only on ‘Actually Legitimate URL Shortener Tool’ and ‘ClearURLs for uBo’ filter lists? I wasn’t sure it would de sufficient.
3- I discovered ‘CleanLinks’ : it does what ClearURLs does (except for the HistoryState that I don’t use anyway) and it does what SkipRedirect does => I decided to give it a try and remove both ‘ClearURLs and SkipRedirect.
> This ‘CleanLinks’ looks interesting, but it seems to me as well that it requires a little bit of learning curve after seeing the icon menu.
> […] what are the additional benefits?
It does require a little bit of learning. I’m still learning and I confess that I happen to copy a rule to adapt it to a new rule, but it gets in (your brains) with time as always (though slower or faster from one person to another, lol).
The benefits are,
– for one that it combines query parameters stripping and redirected urls management, with Default Rules, with Modified Rules (the latter are the ones from default together with ones we create),
– for two, the “deepness” of the filtering : I’ve seen ‘CleanLinks’ block/modify queries and redirections that had never been blocked/modified by ClearURLs and SkipRedirect. The thing is powerful but indeed requires, especially at the beginning, some attention/concentration to get things right. But it is really powerful and, IMO, the best all-in-one tool for stripping query parameters together with handling redirected urls.
As always, I’m in the logic of “if you do it try to do it ultimately” but this approach is not IMO a “true truth” so to say : sometimes “the better is the enemy of the suitable” (approx. translated from French “Le mieux est l’ennemi du bien”).
So if anyone is OK with SkipRedirect for redirected urls and dedicated uBO filter lists for stripping query parameters, then they might very well be a better optimized arsenal than my choice. No idea really, trying it all as always.
@Tom Hawack
Thanks as always, I’ll give a try.
Interesting phrase (expressions-francaises.fr), I might also see similarities with ‘Don’t bother’ (too much) at Arkenfox’s extensions wiki. :-)
@Shiva
> Arkenfox
Yeah, well, why not just use the Tor Browser Bundle at this point? Arkenfox is a carbon copy of Tor’s config anyway.
@Iron Heart
I suppose it is well explained at: ‘1.1 To Arkenfox or Not’. I certainly wouldn’t use Tor Browser with the extensions I usually use on Firefox (on the contrary I wouldn’t install them at all), nor do I need such a strong anonymity.
The analogy between the aphorism and ‘Don’t bother’ was ‘Don’t install thousand privacy\security extension to achieve the perfection, but actually doing more harm than good.
Of course it has nothing to do with the choice between a recommended extension and a similar one that is perhaps more performing, in fact I’m evaluating CleanLinks after the comment above of TomH.
@Shiva
Arkenfox is, at the end of the day, a custom setup. Firefox is unique by default but modifying it in a way that not many people do is not necessarily fixing this. Honestly, do you think more than 1% of Firefox users use, or have even heard of, “arkenfox”? Firefox is normie-heavy and you are in a very small pool of users with your custom setup still. This is not unproblematic at all, but I have mentioned this so often I am tired of it already.
When you follow these instructions and when you have broken WebGL support, Canvas rendering, IPv6 support etc. successfully via arkenfox, wouldn’t you go all the way and also hide your IP address (…which is what Tor does)? Is there a use case for Tor’s setup but still leaking your IP address? I don’t think so. Tor seems like the obvious choice; it doesn’t suffer from being a custom setup with major version fragmentations and adds the last obvious step of also anonymizing the IP address.
Extensions are tricky, some of them may improve privacy but they can have leaks. For example, uBlock Origin: It is very easy to detect that you load several resources from a website but not others (the tracking scripts & ads). uBlock Origin also leaks the lists you are using in the extension. At worst, you run a very unique list combo and this becomes a strong identifier. Running uBlock Origin only with its default lists may mitigate this but is not optimal because ads might still get through. Same story for Brave’s native adblocker btw. It would probably be better to block ads at the network level and run adblockers with their default lists only or even no adblockers within the browser at all. Adversaries can then still see that you load some resources and not others, but at least the “list leak” is mitigated. Just my 2 cents, detectable extensions are always a mixed bag (hence why Tor avoids them entirely, aside from the included ones). Cheers.
> Firefox is unique by default
So you agree that doing nothing changes nothing
– https://github.com/arkenfox/user.js/wiki/3.3-Overrides-%5BTo-RFP-or-Not%5D#-fingerprinting
“Changing a few prefs from default is not going to make you “more unique” – there is no such thing”
But you are again being willfully ignorant of the fact that Arkenfox does not claim to defeat advanced fingerprinting, that mitigating other forms of tracking are also if not more important and that changing those do not make things worse for fingerprinting, and that it does in fact reduce the fingerprinting threat.
All your screaming about a few pref changes, much of your claims are ignorant and flat out wrong, out of 140+ that are changed, is bogus. Arkenfox is not looking to defeat advanced fingerprinting, never has
– https://github.com/arkenfox/user.js/issues/1274#issuecomment-965694513
> Arkenfox is a carbon copy of Tor’s config anyway.
– Tor Browser changes over a hundred pref values from Firefox default that Arkenfox does not
– Arkenfox changes over a hundred prefs values from Firefox default that Tor Browser does not
– Arkenfox adds pref changes that Tor Browser eventually does BEFORE Tor Browser with their own documented research/notes
– The prefs in common that are changed from Firefox default are less than 10%
– It doesn’t matter which version you compare, Arkenfox 91 and Tor Browser based on ESR91, or Arkenfox 100 and Tor Browser for Android based on Firefox 101 – the prefs in common that are changed from default are less than 10% because they are simply common sense
Clearly arkenfox is not a “carbon copy”. The two are radically different. One uses Private Mode, one doesn’t. One uses sanitizing on close, one doesn’t. One uses FPI, one doesn’t. One uses Tor, one doesn’t. One uses window.name protection, one doesn’t. The list is very long.
* [Editor: removed, please no personal attacks]
@Iron Heart
In fact (in part) and I do not understand the meaning of the discussion. I use Firefox together with other extensions (TileTabs, TranslateWebPages, ContextSearchweb-ext, Image Picka, SingleFile, ViolentMonkey, …) in addition to the few and not redundant ones recommended for a little security\privacy and I don’t look for anonymity.
Honestly, it is a problem of the remaining 99% of users if they do not know or do not use user.js with a lot of customizations and the possibility to override them (like WebGL or RFP).
I am aware that for example there is also the IP tracking. If and when I won’t want to be traced I will use what is recommended and, as written, I would certainly not install all those listed extensions that could reduce entropy or the risk of losses.
I think we are saying more or less the same things, but if you have any particular or technical issue with the config of the user.js (which then based on what Firefox and its development policies offers) perhaps it is better to go directly to the author and I will read the counter-replies. At most I take a surf sometimes at privacyests.org to look how my non Tor-Browser choice is doing.
Brave has been doing that for ages… Good to see that Mozilla is taking a page out of Brave’s playbook.
Brave? The same Brave using a decentralized crypto currency? LOL.
Yes exactly, been using that for years via addons. The addon dev community in Firefox is simply better, plain as it is. Did you know that uBlock Origin works best on Firefox?
[https://github.com/gorhill/uBlock/wiki/uBlock-Origin-works-best-on-Firefox]
@Frankel
How often do you want to post this meaningless article? This compares uBlock Origin on Chromium vs. uBlock Origin on Firefox. It says nothing about native adblockers that are not under the restrictions of extension APIs (which is the thing the article actually describes) and is not applicable to e.g. Brave’s native adblocker.
I don’t need uBlock Origin on Brave.
the removeparam filter lists for uBlock Origin, which works best in Firefox, are vastly superior to the puny token Brave list
Everything Brave does is a token gesture to be maximized for marketing to suck in the gullible, like removing some cookies after seven days, or adding blocklisting but not contributing blocklists, or adding a shit Tor window but adding nothing to Tor. Brave is an advertising company parasite that leeches and steals content creators income
how about not grifting private never divulged user details and spamming them with ADVERTISING
https://old.reddit.com/r/privacy/comments/v44vut/brave_browser_sending_unsolicited_marketing_mail/
https://old.reddit.com/r/privacy/comments/v44vut/brave_browser_sending_unsolicited_marketing_mail/
Brave is an advertising company – they broker adverts. They are happy to use third party data to send their own ADVERTS.
Never forget, Brave is funded by VCs
@brave privacy lol
Brave does not have your E-Mail address, you don’t even need it to set up sync. The entity sending these E-Mails does have your E-Mail address and various companies may ask them to do advertising for them.
If you want to imply that Brave itself is collecting your E-Mail address, then this is false, and you have just added additional fake news upon the heap of fake news already present here.
@herman zee german
Source for any of your ridiculous claims?
PS: Even if they were true, which they aren’t. Brave would still do more to improve user’s privacy than Firefox does. You don’t even get token gestures from Mozilla except perhaps the middle finger and a nice fat Google ad money deal.
Thankfully Mozilla haven’t copied Brave’s spyware, “ad replacement program” or built in crypto miner
https://www.computerworld.com/article/3284076/brave-browser-begins-controversial-ad-repeal-and-replace-tests.html
https://www.reddit.com/r/CryptoCurrency/comments/nxce6t/brave_browser_scam_a_fake_privacy_browser_sharing/
@Daffy Jones
I originally wrote a reply debunking every single horseshit point in these links you’ve posted, but Martin would have none of it because I apparently dealt too bluntly with the fake news for his liking.
So, because I won’t write it all over again, it must suffice to say that none of what these links claim is truthful. These are deliberate, well-crafted misrepresentations of trolls out to damage Brave Software. That you believe them says more about you than it says about Brave.
If you want genuine discourse and if you are not a troll I can list all of their errors, but I won’t do this right now just for Martin to randomly delete it again.
@Martin Brinkmann
* [Editor: removed, @Iron Heart. Just make sure that your comments do not attack users or communities in any way, it is not that hard.]
@Martin Brinkmann
> removed, @Iron Heart. Just make sure that your comments do not attack users or communities in any way, it is not that hard
Don’t give a platform to fake news then. :D
That’s not all too hard either.
Man you really behave like those twitter accounts like utdtrey or cfcmod11. Absolute joke behaviour.
@Yash
So, are they fighting fake news and ridiculous takes on various topics (including yours at various times) too?
Yep. Actually in football twitter world there are so many whataboutery merchants. Don’t act like them. Learn to take a joke. If not do whatever. I couldn’t care less anyway.
Good for Brave team that they’ve launched a feature which was introduced earlier than Firefox. Not a high bar though, uBO and especially ClearURLs had that for years. Chuckle.