Critical Windows Codecs security issue affects Windows 10 and Server
Microsoft published details about two recently discovered security issues in Windows Codec that affect Windows 10 client and server versions. The issues were found in the Microsoft Windows Codecs Library, more precisely in the way that the library "handles objects in memory".
Microsoft confirms the security issues and defines the vulnerabilities as a remote code execution vulnerability with a severity of critical and important.
All client versions of Windows 10 from Windows 10 version 1709 on, including 32-bit, 64-bit and ARM versions, and several Windows Server versions, including Windows Server 2019 and Windows Server version 2004 Core installation, are affected.
Update: Microsoft updated the descriptions of the vulnerabilities and added essential information to them. The company notes that default Windows 10 configurations are not affected, only those on which the optional HEVC codecs are installed. End
The issues are not exploited in the wild; an attacker could create a specially crafted image file and get it opened on a target system to exploit the vulnerability.
Workarounds and mitigations are not available, but Microsoft has created an update that needs to be installed on Windows 10 and Windows 10 Server devices to correct the issue and protect systems against potential exploits.
The update is pushed to devices through a Microsoft Store update. Microsoft notes that updates will land on devices automatically and that customers don't need to take any action in that regard.
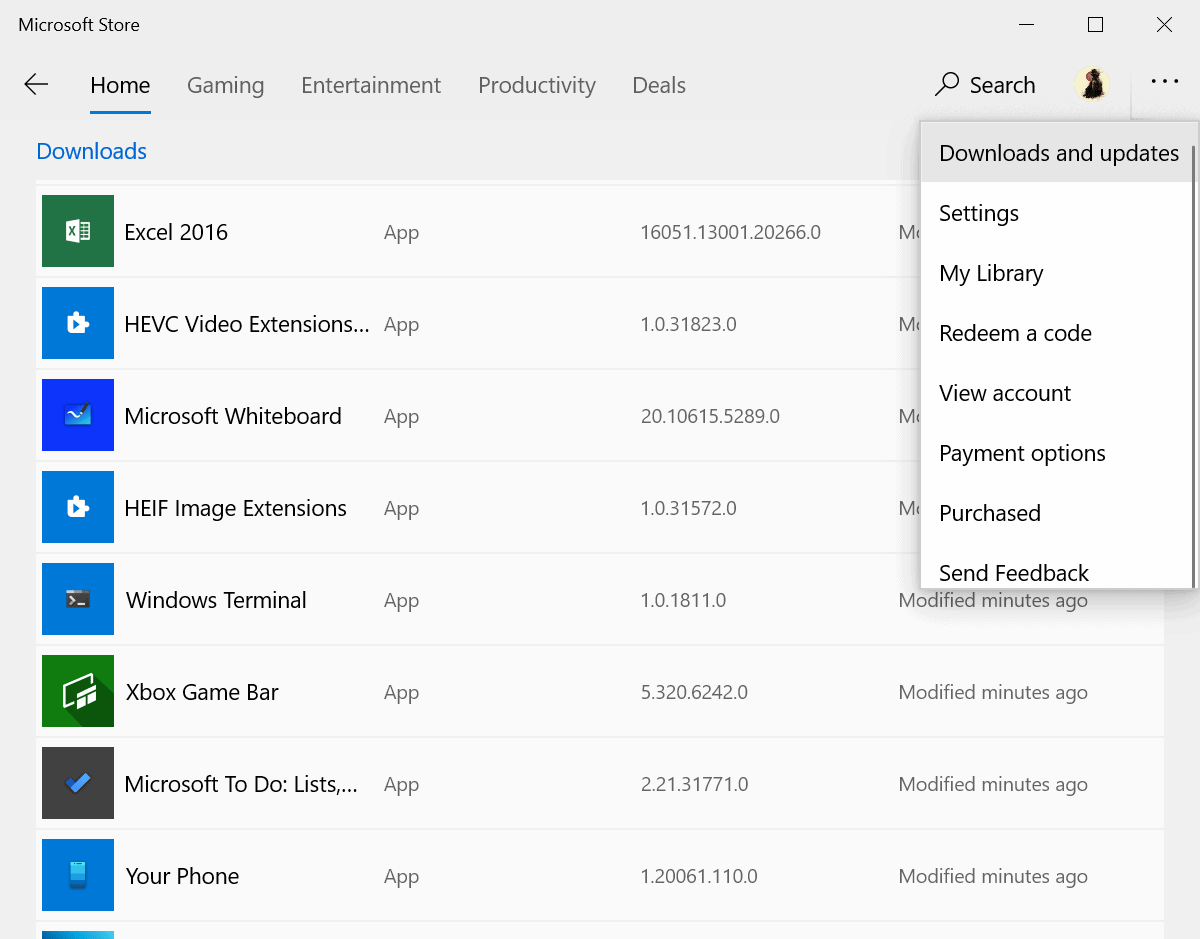
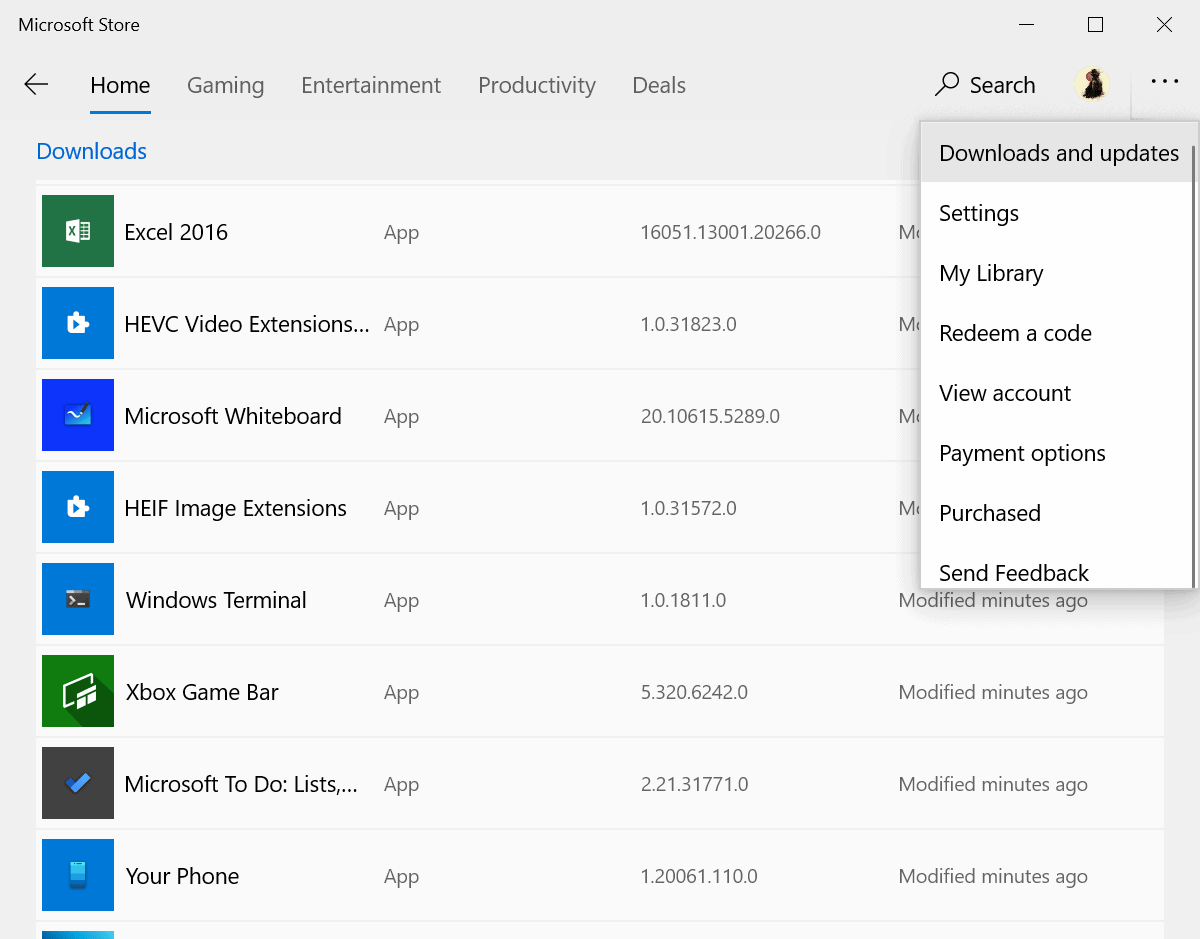
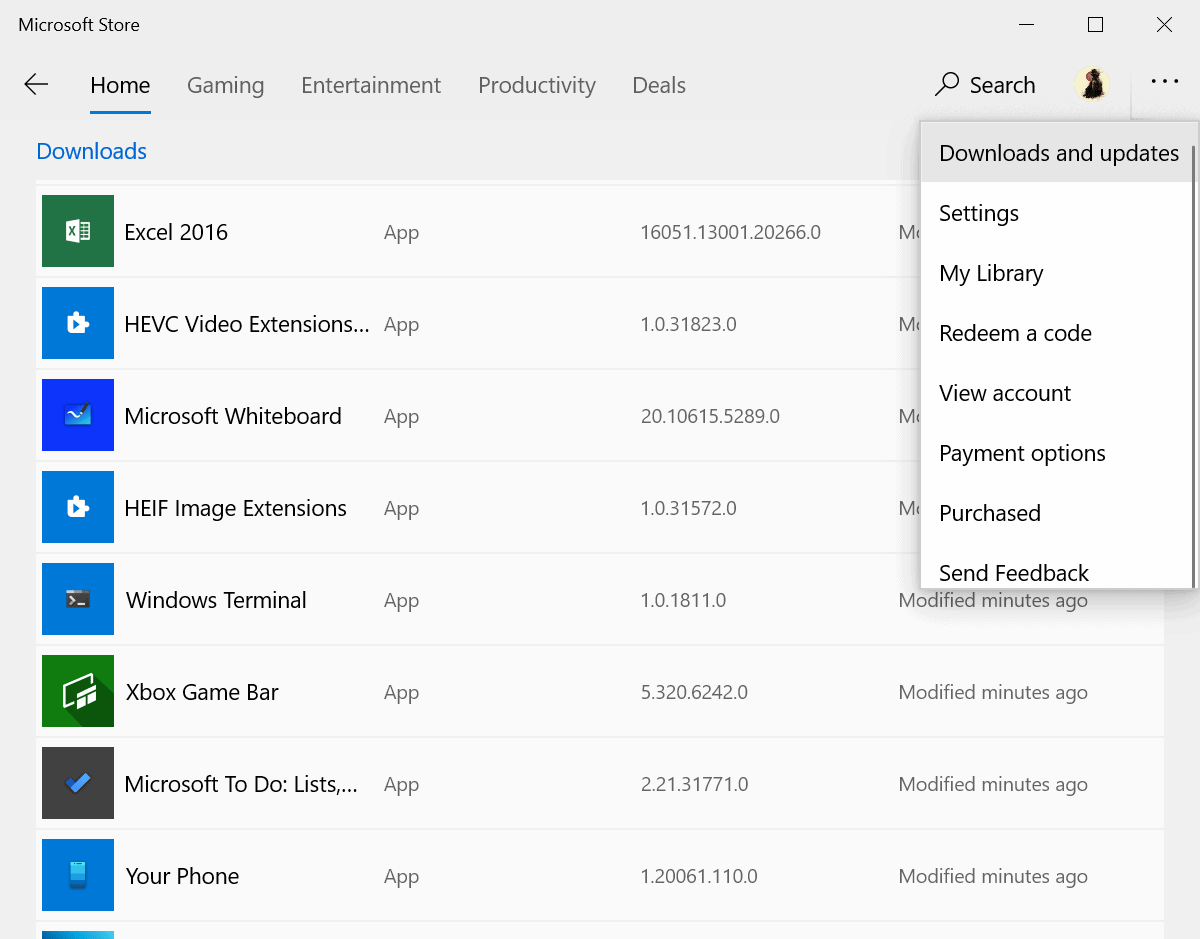
Administrators who don't want to wait for the update to arrive on systems may open the Microsoft Store application manually, select Menu > Downloads and updates, and there the "get updates" button to run a manual check for updates.
Here are the links to the two vulnerabilities on Microsoft's MSRC portal:
- CVE-2020-1425 | Microsoft Windows Codecs Library Remote Code Execution Vulnerability
- CVE-2020-1457 | Microsoft Windows Codecs Library Remote Code Execution Vulnerability
Lack of information is a problem
Microsoft does not reveal the name of the update that it created to address the security issue. A quick check on an up-to-date Windows 10 version 2004 Surface Go device returned updates for the apps HEIF Image Extensions and HEVC Video Extensions from Device Manufacturer. It is unclear if these are the updates that Microsoft is referring to or if the company has not yet released the security update to the general population.
I will keep an eye on the updates and update the article if a Windows Codecs Library related update becomes available.
Microsoft needs to provide additional information. It is unclear how administrators can check if the updates are installed on devices because of the lack of information. Information about the nature of the vulnerability, e.g. which image formats are affected, would also be useful.
Lastly, a Store update excludes systems from receiving the update if the Store application has been uninstalled or neutralized.
Now You: What is your take on this? (via Bleeping Computer)

















I started seeing the following images in my shaw webmail account around the time this CVE was released… makes me wonder: https://postimg.cc/k2YTtqbV
they change slightly each time on reload, colors from one to another. Initially before learning about this latest exploit, I intuitively thought, maybe bugged.
All the people who didn’t get suckered into Windows 10 are likely smiling every time they read one of these many articles showing serious problems with Windows 10.
Folks who don’t use Windows can imagine all they want with their dopey smiles, yet most Windows users rarely have any serious problems with the OS.
Updated 1.2 version at https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2020-1425 makes me say “What, me worry?”
¯\_(ツ)_/¯
and if in the microsoft store get update not showing video extension, then the computer need wait and not use for short time for avoid security risk while connect to internet?
Microsoft Store is not available on Wndows Server, I wonder how they are gone update
Not only that, but I know of many people who either disable, or completely remove, the Windows Store. How do they get patched?
It is strange that they have chosen to fix vulnerabilities through the store. You wouldn’t think that codecs are used by only store apps, but perhaps they are in this case? If that’s true, which they don’t make clear, then it’s not a problem if you never use the store and uninstall the included store apps. As usual not enough info to be sure either way.
@Doom
It’s not “strange” as you clearly don’t know why they did that. You can be curious, but that’s about it. That said, although our speculations are rather moot in this matter, I speculate that they provided this temporary help through the store as it provided the best and secure method right now for some users. This is not a huge threat, and I reckon they will roll out a proper solution to all users soon enough. As such, I’m not at all concerned with this news.
Windows Update on 14th July. But neither LTSC nor Server 2019 support HEIC and HEVC natively. I don’t know about WMP as I have it disabled, but I doubt.
These are still new and changing codecs, with very little market usage. A fully up to date SGS10 still produces JPEG and h264/MP4 files by default, with the HEIC/h265 being “experimental” features.
These image extensions are a total joke. The handling of images is unbelieveable clumsy (especially with AVIF), you can’t tag the files; the Photos app doesn’t allow them (Live Photo Gallery accepts third-party image codecs, even PSD, with no trouble). Leave it to Microsoft to invent WIC codecs and fail to properly handle them. Also, it’s a mystery why so many of the MS Store apps require you to sign in – To Do needs you to be online! Same with the Phone app etc.