Windows 10 KB4057142, KB4057144 and KB4073290 released
Microsoft released the updates KB4057142, KB4057144 and KB4073290 on January 17th, 2017 for the company's Windows 10 operating system.
One of the updates, KB4073290, addresses the unbootable state issue for select AMD devices after installing the January 3 update KB4056892. The company released updates for affected Windows 7, Windows 8.1 and Windows Server systems yesterday already.
The two remaining updates, KB4057142 and KB4057144 are cumulative updates for Windows 10 version 1607 and 1703.
KB4073290
KB4073290 is an update for Windows 10 version 1709 that patches the unbootable state issue that select AMD devices were stuck in after installing the January 3 security update for the device.
The update suffers from the same lack of actionable information that yesterday's updates for Windows 7 and Windows 8.1 suffered from. Should you install only this update? And how should you do so if the system won't boot? What about the January 3 patch, does it still need to be installed?
KB4057142
This update patches a large number of issues in Windows 10 version 1607. It brings the build number to 14393.2034. It addresses the unbootable state issue but patches lots of other issues on top of that.
- Some Microsoft-signed ActiveX controls did not work if Windows Defender Application Control is enabled.
- Excessive memory use when using smart cards on a Windows Terminal Server system.
- Virtual TPM self-test is not run.
- Compatibility with U.2 NVMe device hot-add/removal cases improved.
- iSCSI Initiator Properties Devices list fails to list some targets.
- NGUID and EUI64 I formats compatibility for NVMe devices.
- Fixed error 0xc2 and 7e sync errors when backing up large Resilient File System volumes.
- UWF file commits add old data to files.
- Access-based enumeration not working correctly after installing KB4015217
- Addresses issue where AD FS incorrectly displays the Home Realm Discovery (HRD) page when an identity provider (IDP) is associated with a relying party (RP) in an OAuth Group.
- Addresses issue where PKeyAuth-based device authentication sometimes fails in Internet Explorer and Microsoft Edge when AD FS returns a context that exceeds the request limits for URL length.
- Addresses issue in AD FS where MSISConext cookies in request headers can eventually overflow the headers’ size limit. This causes authentication failure with the HTTP status code 400: “Bad Request - Header Too Long."
- Addresses issue where AD FS produces an MFA Event 1200 log that doesn't contain UserID information.
- Addresses issue where retrieving the Certificate Revocation List (CRL) from the Certification Authority (CA) using the Simple Certificate Enrollment Protocol (SCEP) fails.
- Enables IT, administrators, to scientifically troubleshoot I/O failures using a comprehensive event log for the resiliency state transition.
- Transparency for replication health when free disk space is low, Hyper-V Replica Log size is growing to maximum limit and Recovery Point Objectives threshold violations.
- Addresses issue where, if the Online Certificate Status Protocol (OCSP) renewal date comes after the certificate expiration date, the OCSP-stapled response is used until the renewal date even though the certificate has expired.
- Addresses issue where backward compatibility for managing Microsoft User Experience Virtualization (UE-V) with group policy is lost. Windows 10 version 1607 group policy isn't compatible with Windows 10 version 1703 or higher group policy. Because of this bug, the new Windows 10 Administrative Templates (.admx) cannot be deployed to the Group Policy Central Store. This means that some of the new, additional settings for Windows 10 aren't available.
- Addresses issue with the App-V package folder access that causes the access control list to be handled incorrectly.
- Addressed delay when searching for new printers.
- Fixed issue where users could not change passwords on remote logon screens if the password expired.
- DISM command sometimes failed to import custom application defaults.
- Addresses issue originally called out in KB4056890 where calling CoInitializeSecurity with the authentication parameter set to RPC_C_AUTHN_LEVEL_NONE resulted in the error STATUS_BAD_IMPERSONATION_LEVEL.
- Addresses issue where some customers with AMD devices get into an unbootable state.
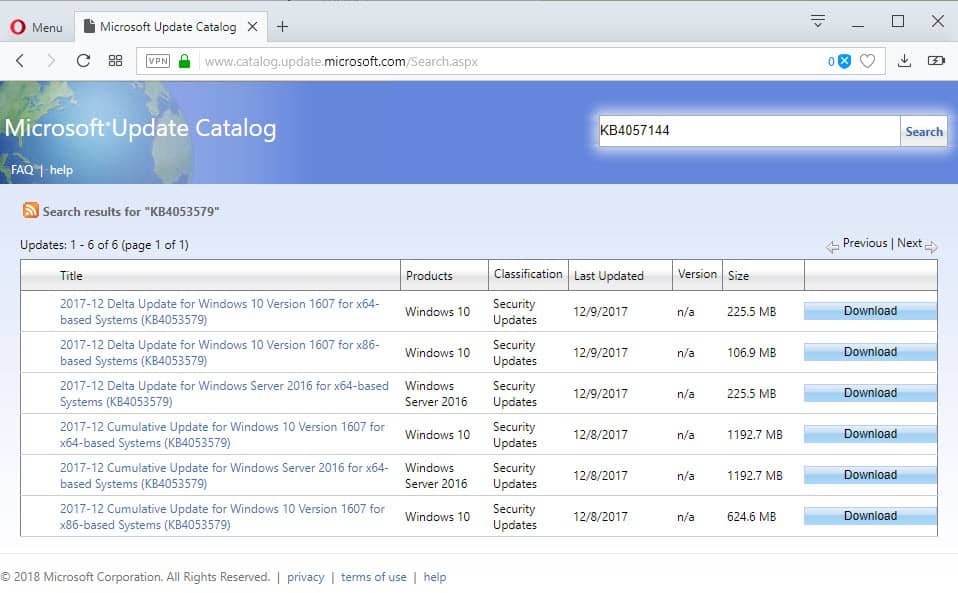
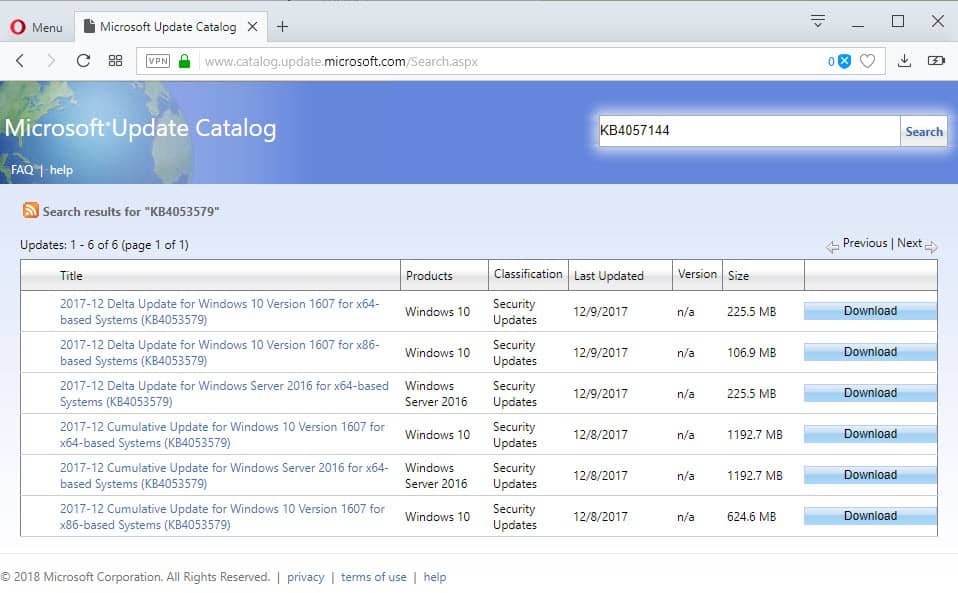
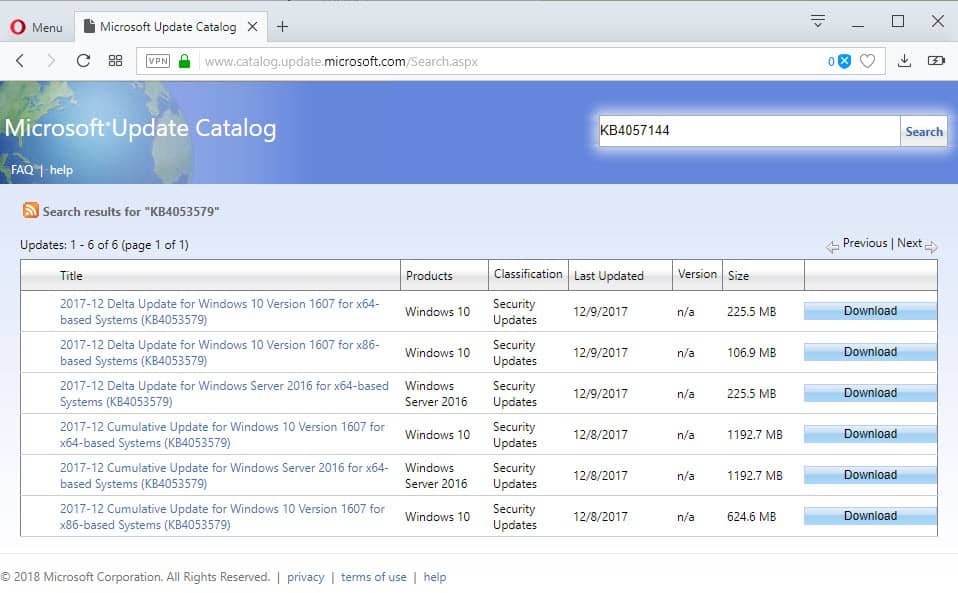
KB4057144
KB4057144is an update for Windows 10 version 1703. It patches the unbootable state issue as well on the version of Windows 10, and addresses the following issues on top of that:
- PDF printing issue in Microsoft Edge.
- App-V package folder access issue that affected the access control list.
- Addresses issue where backward compatibility for managing Microsoft User Experience Virtualization (UE-V) with group policy is lost.
- Addresses issue where some Microsoft-signed ActiveX controls don't work when Windows Defender Application Control (Device Guard) is enabled. Specifically, class IDs related to XMLHTTP in msxml6.dll don't work.
- "Cannot create a file when that file already exists." error when changing the Smart Card for Windows server start type from Disabled to Manual or Automatic.
- Windows Defender Device Guard or Windows Defender Application Control would wrongfully block some applications in Audit only mode.
- Addresses issue where the virtual TPM self-test isn't run as part of virtual TPM initialization.
Addresses issue with NoToastApplicationNotificationOnLockScreen GPO that causes Toast notifications to appear on the lock screen. - Addresses issue originally called out in KB4056891 where calling CoInitializeSecurity with the authentication parameter set to RPC_C_AUTHN_LEVEL_NONE resulted in the error STATUS_BAD_IMPERSONATION_LEVEL.
- Addresses issue where some customers with AMD devices get into an unbootable state.

















I have KB4057142 installed after a long fight with Windows Update. Windows is still trying to install security updates. It’s not rolling back, it shows as installed. However, I have no idea what it is trying to install as nothing seems to have installed after that and it’s not rolled back.
I was previously unsuccessful in installing the Fall Creator’s update… Leary of trying again. Has anyone gotten any further?
My computer will upgrade everything except KB4057142. How do I get it to do it, or just go away?
KB4057144 crashes my computer when I try to install. Clean boot, safe mode, nothing seems to work. Ugh.
Installed on win 10 pro via my update request. Infected with pop-ups most times when going to another page about 90% of the time. Also, pop-ups while reading a page. Using Firefox 57.0.4(64 bit) with pop-ups not allowed. Win 10 also doesn’t allow pop-ups.
Before download pop-ups were controlled with little or no pop-ups. Thinking to delete upgrade and download and install fresh upgrade?
2018-01 Cumulative Update for Windows 10 Version 1607 for x64-based Systems (KB4057142) is stuck at 5% download – once again Microsoft never test these products.
Will reboot ….. again (sigh)
KB 4056892 gave us version 1709.16299.192 .
I dont get all these latest updates , so far .
Is it all right ………….??
How do I install an update if my machine will not boot Windows?
why KB4073290 is not available in x86 yet ? :(
I am searching x86 version too but no luck :(
@ Searcher,
M$ are only issuing Meltdown patches for 64bit Windows. Patches for 32bit Windows will come later.
But their patches for Spectre 1 & Spectre 2 apply to both 64bit and 32bit Windows.
How do you install an update when your computer is unbootable? Do you have to reinstall Windows 10? Excuse me for asking – I don’t use Windows 10.
It is not just AMD processors that have the BSOD issue and can’t boot after KB4056892 – seems there are plenty of people like me with Haswell processors that can’t boot either ! How come this hasn’t been picked up in articles ?
So if the patch on January 3rd makes some systems unbootable…how would someone install this update to fix that problem if their system is unbootable?
Hmmm…
I have just updated my brother-in-laws Acer (AMD) processor laptop Windows 10 system with KB4073290 and it is now working fine.
Whether this only applies to Acer laptops I am not sure but what I did was switch on the laptop and of course it fails to boot and then switched it off I repeated this procedure three times and on the third attempt a message appeared stating “Windows will attempt a repair”. It then proceeded to check the laptop and a further message appeared stating “Windows update could not be completed” it then removed the update KB4056892 and then it would boot into Windows.
Following information on ghacks.net I then downloaded KB4073290 from the Microsoft Update site and installed it on the laptop and now everything is back to normal, the only evidence that KB4056892 was on the system is when I check “Installed Update History” and it show that there had been six attempts to install and all had failed the latest being on 18th January 2018.
I have also just run “Check for updates” and it shows that there are no further updates available.
If you have a non booting laptop you might be able to get it back to normal doing what I did.
They probably will have to re-install from scratch. Thanks Microsoft.
You have two options: recover the system to pre-update state, or install from scratch.
Moral of the story: don’t patch on the first day. If you must then wait a while, a week, two, a month; then do it, when it’s safe. Let others test the ground for you. Chances of you being the victim of said patched exploit/s are smaller than you might think.
Personally I won’t even bother with this workaround “fix”. If it ends up in Simplix’s UpdatePack I’ll just use the registry entry and disable it. I don’t want my performance being dragged down due to some mitigation of some exploit that nobody is going to bother leveraging it.
You must not be using Windows 10 Home. You have no choice but to install the pushed updates. I’ve had customers roll them back, only to have hundreds of MB of data again pushed back onto their machine, shortly thereafter. Consumers don’t know how to put off installing the now risky updates for Windows. It has brought in more business to our shop. However, I ask what they do on their computer. If there are no Windows only programs, I recommend that they consider installing Linux Mint and to switch to a Chromebook for their next machine. Since the local schools assign Chromebooks to the students, many have tried it and switched. Microsoft doesn’t care one bit about consumers.
>>>Consumers don’t know how to put off installing the now risky updates for Windows.
— Updates for Windows are now VERY RISKY. In my view, far far greater than the exploits possibly waiting.
It’s still possible to disable/delay the updates using Regedit.
There used to be an option ‘defer upgrades’ in the Home version but it seems that many people turned it on so Microsoft decided to remove it.
Someday if Microsoft decided Home Users don’t need Regedit, maybe it will be removed too
Why does everyone keep bothering with “Microsoft Sanctioned” methods to disable, ie: (postpone) Windows update?
All you have to do is disable a couple of services, and make sure that Task Sched. is not primed to switch those services back on again. A few more tweaks, some registry entries, and you will not be bothered again.
I do appreciate this is becoming harder, but messing around with “deferred upgrades” is not really going to help you in the long run.
@SeePrime, FreeBSD Has not made any updates yet as well. So what’s the point of running Linux Mint or switching to a Chromebook going to help with this problem SeePrime? You have no clue what you’re talking about here. So hilarious switching to linux mint, never laughed so hard.
@ Anonymous,
FreeBSD =/= Linux Mint or ChromeOS.
By default, Linux distros do not force auto-updates/upgrades. For computer dummies and most average users, Linux Mint/Ubuntu and MacOS are good alternatives to Win 10’s forced auto-updates/upgrades which have just borked many AMD-based computers.
The Linux open source operating system, or Linux OS, is a freely distributable, cross-platform operating system based on Unix that can be installed on PCs, laptops, netbooks, mobile and tablet devices, video game consoles, servers, supercomputers and more.
System Based On Unix, So what do you think FreeBSD is based on AnorKnee Merce??
https://en.wikipedia.org/wiki/Linux
Really!! =/= Not equals.
Chrome OS is an operating system designed by Google that is based on the Linux kernel and uses the Google Chrome web browser as its principal user interface. As a result, Chrome OS primarily supports web applications.
https://en.wikipedia.org/wiki/Chrome_OS
@ AnorKnee Merce.
Linux Mint/Ubuntu make good alternatives to win 10’s for the “Average Users”. When was the last time you have seen a user an Average User, use the command line using linux mint or ubuntu. You seem to still miss the point here. Switching to some other OS will not fix this problem. But thanks for the laugh again. So now after you have switched the user to linux mint or ubuntu. Oh wait that user is going to be calling you for help.Good luck with that problem. Sudo make me a sandwich!!
I disliked Linux Mint when I tried it. It just felt all wrong.
With the release of Windows 10 as a free “upgrade”, Microsoft got rid of much of their highly paid QA group and replaced them with millions of free beta testers.
I am old enough to remember when Microsoft kind of worked. This *PATCH* just freezes. Fifth reboot this morning. Microsoft expects millions of us to spend a whole day waiting for a patch to not freeze, with no warning messages.
No wonder the US GDP is shrinking! We all are waiting for Microsoft to work instead of being productive.
Microsoft is the Right Hand Arm of the KGB.
If they just had any feedback for
2018-01 Cumulative Update for Windows 10 Version 1607 for x64-based Systems (KB4057142) It gets stuck, eventually times out and restarts at 0%.
My internet is 50 MBS high-speed. But, this retro Update Status on Settings is a reminder of how the old 56K modems worked.
The new series of the X Files poster now shows “I want to believe Microsoft has QA”