MS16-072 may break Group Policy configurations
Microsoft released 16 security bulletins as part of the June 2016 Patch Day of which one, MS16-072, is causing serious issues on some computer configurations.
The security update patches a vulnerability in Windows that could result in elevation of privilege during a man in the middle attack.
The vulnerability could allow elevation of privilege if an attacker launches a man-in-the-middle (MiTM) attack against the traffic passing between a domain controller and the target machine.
The update changes the security context in which user group policies are retrieved. Previously, group policies were always retrieved by using the user's security context. Starting with the installation of MS16-072, user group policies are retrieved using the computer's security context instead.
Group Policy issues caused by MS16-072
While that makes sense from a security point of view, it led to severe issues on domain joined computers as all policies may fail on those systems.
The cause for this according to Microsoft is a missing read permission for the Authenticated User group, or missing read permissions for the domain computers group. Basically, what happens is that the policies cannot be read due to the missing permissions.
Considering that all policies may not be applied to a user or machine after installing MS16-072, it is clear that this may cause serious issues in business environments.
This ranges from simple things such as background images not showing up to serious ones like hidden drives showing up, changes in Windows Update, blocked features or tools becoming available, printers becoming inaccessible, and a lot more that may cause serious issues in those environments.
Administrators who are in a hurry can uninstall KB3159398, KB3163017, KB3163018 or KB3163016 and reboot affected machines to return to the status quo.
Microsoft's solution
Microsoft recommends other solutions, and it is probably a good idea to install the security update eventually. The security context change was done on purpose, and Microsoft won't modify the patch to resolve the issue in some other way.
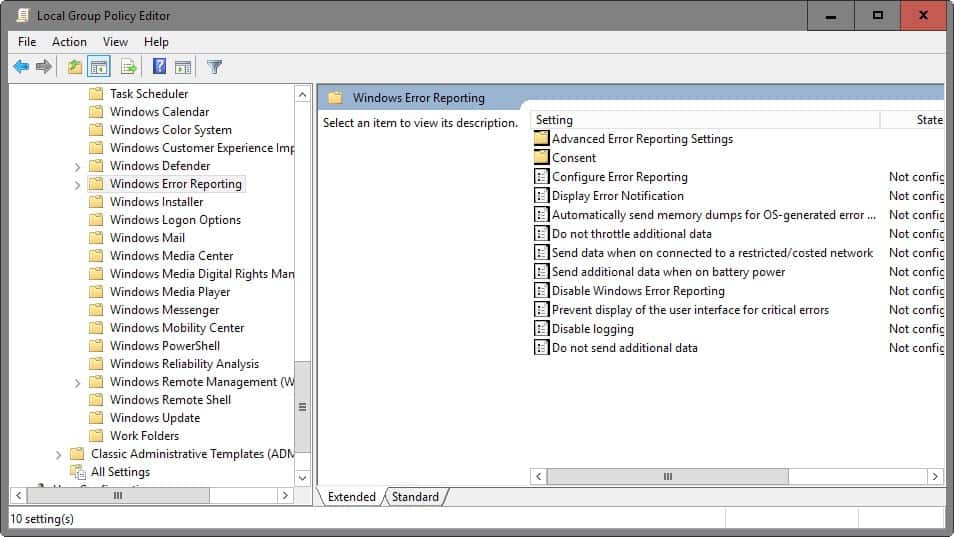
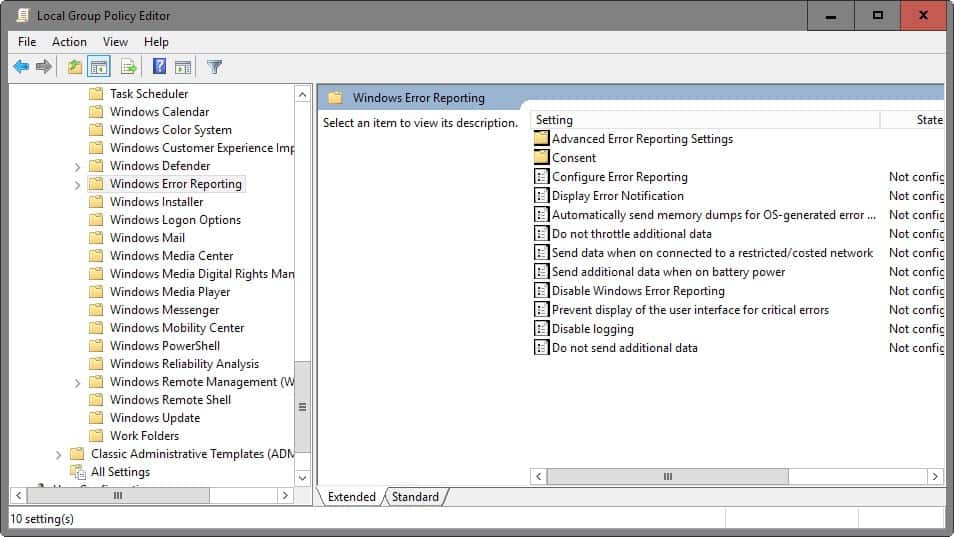
This means that you will need to apply Microsoft's solution on affected machines. Thankfully, it is not lengthy or complicated, but requires access to the Group Policy Management Console (gpmc.msc).
- Option 1: Add the Authenticated Users group with read permissions on the Group Policy Object.
- Option 2: If security filtering is used, add the Domain Groups group with read permissions.

















Thanks Martin!
This has been vexing me for a few days, looked everywhere for issue but should have started by looking at WSUS 1st!
THANK YOU!!! This was very timely for me and your article saved me lots of grief this morning. Granting Authenticated users Read access work perfectly.
What the normal & pro users need to do? Uninstall KB3159398 or would need to use any other workaround?
Also, gpmc.msc can’t be accessed/not found on Win 7/8/8.1 editions which have access to Group Policy.
Normal users would be confused and worried while reading this post. Hence, please add a note for normal users about what they should do.
This only applies to domain joined computers. If you are using a home computer, this won’t affect you.