Mozilla to implement Encrypted Media Extensions in Firefox
Encrypted Media Extensions is a new technology to control the playback of protected contents in HTML5. Plugins like Adobe Flash or Microsoft Silverlight have supported DRM for quite some time and are used by streaming services such as Netflix or Amazon Prime currently.
The move towards a plugin-free Web and the rise of HTML5 posed a problem which Google, Microsoft, Netflix and others tried to resolve by proposing Encrypted Media Extensions (EME).
With support from both Google and Microsoft it was clear that EME would be implemented in Google Chrome and Microsoft Internet Explorer. Content Provider such as Netflix are moving away from plugins to a solution that uses Encrypted Media Extensions as well.
Organizations such as Mozilla criticized the use of a proprietary Content Decryption Module that was not described in the specification itself.
This raises a big problem for Mozilla. The organization prefers different approaches to protecting content but since major web browsers and streaming providers are moving ahead with the integration of EME, it is problematic not to implement the feature as well.
Considering that streaming video is highly popular and that major providers such as Amazon, Netflix or Hulu will make use of it in the future, it would prevent Firefox users from accessing those contents in the web browser.
While that is an option, it would likely mean that users would use other browsers for the streaming, and maybe for all other web activities as well.
That's why Mozilla decided to implement the W3C EME specification in Firefox as well. EME will be implemented in Firefox for desktop first, but users are given a choice and the implementation will be different from that in other browsers.
For Mozilla, it is an awkward step considering that the organization promotes an Open Web and that DRM is everything but, especially since a proprietary module is used.
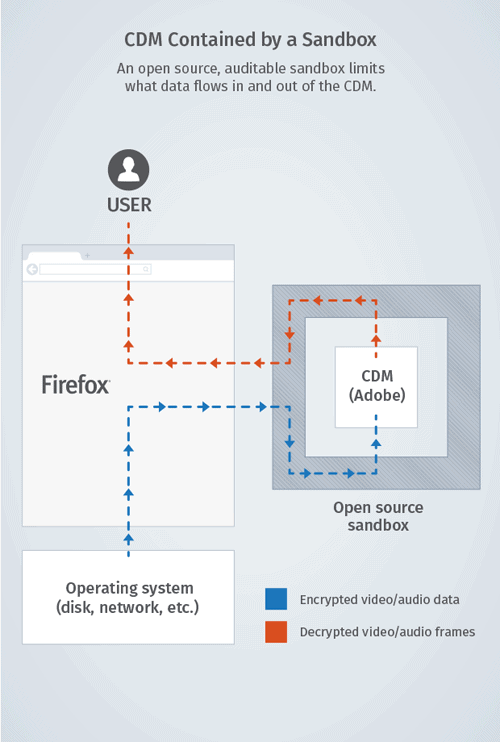
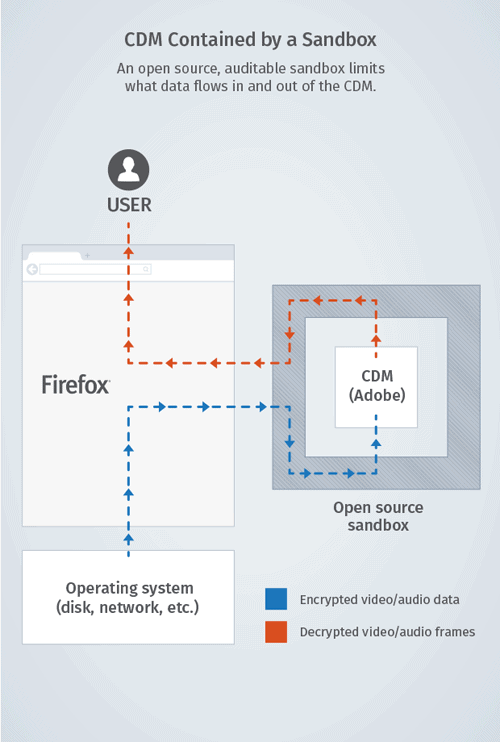
While there is no way around this, Mozilla decided to make this as transparent and open as possible. The organization selected Adobe to provide the CDM, but instead of loading it as a module directly in Firefox, it will be wrapped into an open-source sandbox.
This means that the module does not have access to the user's hard drive or network but only with options to communicate with Firefox "for receiving encrypted data and for displaying the results".
The CDM uses fingerprinting to identify systems. This usually means a fingerprint for the computer system. Mozilla's implementation on the other hand creates a unique identifier without revealing information about the underlying system or the user. In addition, that unique identifier is modified across sites.
It is interesting to note that users will be in full control. According to Mozilla, the feature won't activate or run on its own, so that the user is always in control in this regard.
Some users who have commented on Mozilla's official announcement on Mozilla Hacks dislike that Mozilla is giving in and adding this feature to the browser while others have expressed appreciation for the way it is implemented.
Mozilla will release a technical FAQ in the next 24-48 hour period that will answer several questions that users may have about the implementation.
What's your take on this? What would you have done if you were Mozilla?
Update: A blog post on Mozilla.com provides additional information and answers to some questions.
- EME will be integrated into all Firefox for desktop versions including Linux.
- Each user will be able to activate the DRM implementation or leave it turned off.
Resources:
- Can This Web Be Saved? Mozilla Accepts DRM, and We All Lose (EFF)
- Driven by necessity, Mozilla to enable HTML5 DRM in Firefox (Arstechnica)




















Mozilla is adding DRM support in Firefox.
https://hacks.mozilla.org/2014/05/reconciling-mozillas-mission-and-w3c-eme/
Choosing Adobe to handle this seems to be a poor choice. The fiasco about “smurfed” videos proves that Adobe isn’t willing to implement cross-platform technologies. A lot of people were upset that Adobe reversed some pins and dismissed the issue entirely and eventually after the public backlash Adobe decided to drop full cross-platform support for Flash. I am against DRM in general because having a requirement of the internet to watch something is a move in the wrong direction… where will the keys be stored? Sandboxed is good but fingerprinting needs to end. The internet is for everyone not just data mining. These are just a few thoughts running around after I read this.
Seems to me like someone upstream didn’t do their homework.
In my opinion, the main crux of the issue is having EME (or DRM) in the HTML5 standard, legitimizing it as a core web technology. But that battle is over, and the open web has lost. If Mozilla alone had refused to implement it, it would be not much more than a protest, as their market share is not major enough to force content providers to avoid EME. (They could hold the web back by forcing the content providers to fall back onto Flash, but this is also counter to Mozilla’s philosophy.) Having read their blog post, I’m mostly convinced that implementing it this way is the right way to go, but of course, the devil is in the details. Now to wait for the technical FAQ post to see how well or poorly they thought this out.
This is from: “https://www.eff.org/deeplinks/2014/05/mozilla-and-drm”.
“It (DRM) doesn’t prevent infringement, which continues regardless. Instead, it reduces the security of our devices, reduces user trust, makes finding and reporting of bugs legally risky, eliminates your fair-use rights, undermines competition, promotes secrecy, and circumvents open standards.”
Couldn’t agree more.
Make it an optional add-on, installed by default! Is that so difficult, Mozilla?
In my opinion, it may be a good move from Mozilla towards its users (the first one in quite some time), if the user really has full control to enable/disable that module and if it really runs isolated from the system….
But will content providers/vendors allow this? I don’t think so, the purpose of DRM would probably be defeated if the module is not in control of the outgoing unencrypted data stream, as it appears it would have be handled to an open-source browser for displaying instead ;) Other DRM schemes even use OS drivers to keep unencrypted data “safely concealed” from poor users.
Brendan Eich himself put it pretty clearly last year: “We see DRM in general as profoundly hostile to all three of: users, open-source software, and browser vendors who aren’t also DRM vendors.â€