Chrome bug allows sites to listen on conversations after you close them
Speech recognition is one of the big things that will improve a lot in coming years. Right now, it boils down to giving short commands, or recording what you talk into the microphone.
Eventually, you won't be using the keyboard anymore but use voice to command your computer, at least for the majority of tasks.
Back last year it became known that the NSA can turn on the iPhone camera and microphone without the user knowing about it.
This was also the time when a new security issue was reported to Google that was found in Chrome. It described a way that malicious websites could use to continue listen in on what is being said around the computer after the website the speech functionality was used on was long closed.
First of all, it means that users who do not use speech recognition right now have nothing to worry about. If you are using speech recognition in Google Chrome, you may want to know more about the bug.
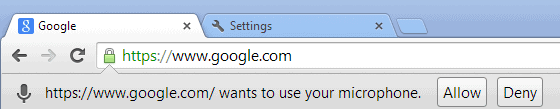
When you use speech in Chrome, a prime example is the main Google search engine where you can search by voice, you need to explicitly allow that before the feature becomes available.
Once enabled, a clear indicator is shown in the address bar that speech is enabled and that the site is listening. Any noise that is in reach gets recorded and send to the site in question.
The problem here is that sites may open a second window on the screen, a popup maybe that is hidden underneath the main window.
Since there is no restriction in regards to which page of the site can listen in on the conversation, this can be exploited. The second window can be disguised as a banner ad for example, and since it does not give any indication that speech is enabled, you may not even notice anything suspicious about it.
So, you enable use of the microphone on a site, that site spawns a hidden popunder window, you stop the microphone use and while everything seems normal to you, the site continues to listen in on your conversations.
Here is a video demonstration of the concept.
The only way to stop this right now is to close Chrome completely after you use speech in the browser, or to make sure that no secondary page of that site spawned in another window or is open in another tab.
The full source code of the exploit was hosted on GitHub by the author, so that you can check it out yourself if that is of interest to you.
Advertisement
















thanks for info, not a big fan of chrome but good to know these things.
in similar vein… be wary of using skype “auto answer” … it’s very easy to not realise people have called you and can hear everything over the microphone
There are USB-connected mics that are simply not capable of being on without a light either right on the mic, or in its base, or in the box between the USB-port and the mic, itself, along its cable (if any), being on. If one can find such a mic, then one may go into DEVICE MANAGER and disable the laptop’s/notebook’s internal mic; leaving only the USB-connected one (and, of course, there’s always opening-up the notebook and snipping the mic wire, or unsoldering one of its contacts).
As for the camera, it’s amazing what a little square cut from near the glue edge of a Post-It Note will do! I’ve had one covering the built-in camera on my notebook for YEARS! In fact, I’ve got an old, external, USB-connected DYNEX brand, 640×480 (which, if you think about it, is plenty big enough for video chatting and most uses) webcam (in fact, I have two… one mounted on the wall right above where the notebook screen opens to when its in the docking station; and the other in my notebook’s carrying bag) which I prefer to use, anyway, because its not being hi-res and wide-angle (like a typical notebook built-in webcam) makes it look like I’m looking right into the lens of the camera even though I’m actually looking at the screen immediately below it.
Between the USB-connected mic which simply cannot be on, no matter how, without its light being on (simply because of how it’s hardwired inside); and the USB-connected old DYNEX camera that may very well be capable of being turned-on without the light being on, but which I keep physically disconnected from the USB port until and unless actually needed…
…I can either disable (in DEVICE MANAGER… if that even works) both the notebooks’ built-in camera and mic; or, perhaps better yet, go in and physically disconnect them (also disabling them in device manager, of course) and just using the USB-connected ones.
It’s less than ideal, but easy to get used to once you’ve got it all set up.
For whatever all that’s worth.
__________________________________
Gregg L. DesElms
Napa, California USA
gregg at greggdeselms dot com
Veritas nihil veretur nisi abscondi.
Veritas nimium altercando amittitur.