New Windows Vulnerability in VDM Discovered [Security]
The last days have not been pleasant for Microsoft. A new Windows vulnerability affecting all 32-bit editions of the operating system from Windows 3.11 to Windows 7 was uncovered shortly after the revelation that an exploit in Microsoft's Internet Explorer 6 was used in the attack on several US companies that included Google and Adobe (read Microsoft Confirms Internet Explorer Vulnerability).
Cause of the problem is the virtual dos machine (vdm) that was introduced in 1993 to support 16-bit applications. The exploit was uncovered by Tavis Ormandy, a member of Google's security team.
The vulnerability can be exploited to run code with elevated rights on the computer system. The full technical explanation of the vulnerability and example exploit code are available at Neohapsis.
No patch has been issued by Microsoft until now even though Ormandy mentioned that he had contacted Microsoft about the issue six months ago. There is however a quick fix for most Windows operating systems: Disallowing VDM.
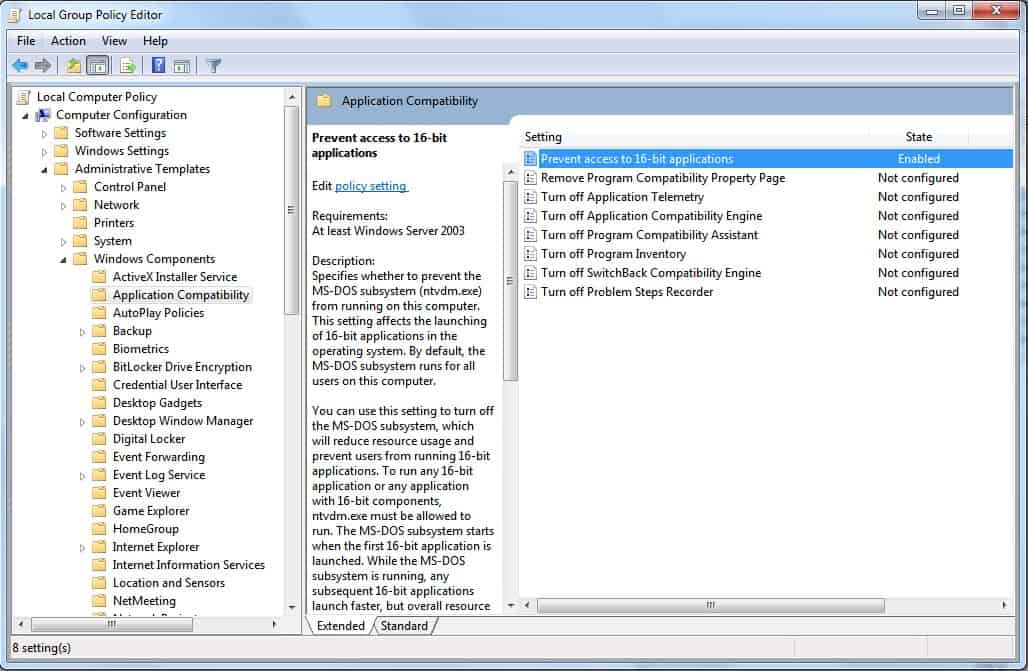
There are two possibilities on how to do that. System administrators and users with access to the Windows Group Policy Editor and an operating system that is Windows 2003 or newer can enable the policy to "Prevent access to 16-bit applications" in Computer Configuration > Administrative Templates > Windows Components > Application Compatibility".
This setting has the consequence that 16-bit applications will not execute on the computer system which should not have an effect on most home users but may render very old software unusable on the system (hint: virtualization is an option).
Users with operating systems prior to Windows 2003, Windows XP comes to mind, can alternatively create a new Windows Registry key to close the security vulnerability in the operating system.
- Open the Windows Registry Editor in the following way: Tap on the Windows-key, type regedit.exe and hit enter.
- Navigate to the key
HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\AppCompat - and create the new DWORD VDMDisallowed there with a right-click on AppCompat and the selection of New > Dword (32-bit value) from the context menu.
- Double-click the newly created preference afterwards and set its value to 1.















Hi,
@Martin & Siam
The “Group Policy” feature does not exist on Win XP Home Edition, which means that users on that Edition have to add the key manually into the registry.
Thanks,
26Dolphins
Hmm So this issue won’t affect users with 64 bit operating system right? since it’s incapable of running 16 bit program…
Hi Martin,
What if you don’t have that AppCompat key in your registry?
Does it mean that you don’t allow 16 bit apps anyway or the contrary?
Thanks,
26Dolphins
I couldn’t find it either, but I found this link that shows you how to configure it so it is disabled: http://windows7themes.net/how-to-prevent-access-to-16-bit-applications.html
If you do not have the key it means that you allow 16-bit apps unless you have set the Group Policy to disallow it (which probably sets the key in the Registry as mine was set and I did not create it but did apply the group policy fix.
Thanks Martin for the info, disabled access to 16 bit apps on my systems.