Reveal or Reset the Bios Passwords
Password protecting the Bios is considered a weak protection, something that professionals can find out or reset in no time. Besides the obvious possibilities to set a jumper or remove the bios battery to reset the bios password it is also possible to reveal or reset the bios password by using a software like CmosPwd which is available for Windows, DOS and Linux. I suggest you check the list of BIOS versions the program works with before you download it and try to use it to reset the bios password of a computer system.
Most users will probably run the application in Windows. To do that they need to access the command line and install a driver that gives "direct port I/O access for specified ports to user-mode process (ring 3) using Ke386SetIoAccessMap and Ke386IoSetAccessProcess kernel functions." The driver is located in the Windows directory of the software package after unzipping it to the computer.
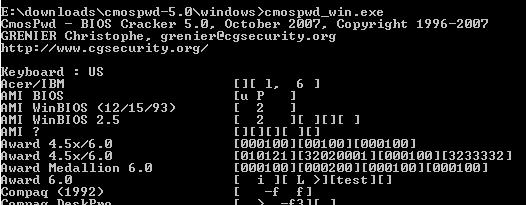
The command ioperm.exe -i is used to install the driver which can be uninstalled with ioperm.exe -u after the bios password has been revealed. Once the driver is installed the bios password can be revealed with the command Cmospwd_win.exe which displays a list similar to the one below.
The application requests the password for all known bioses. Only one hit will be found obviously which in the case of my bios was test in the Award 6.0 line. Reseting the bios can be initiated in DOS with the command cmospwd /k. Please note that the cmospwd.exe file is located in the DOS directory of the application. It can also be reset with the cmospwd_win /k in Windows.
Most notebooks store the bios password in an eeprom which can only be retrieved with an eeprom reader and not with the help of this program. Still, if the computer's motherboard runs on a supported BIOS it is definitely worth a try.
Advertisement















I run cmospwd command and restart laptop but laptop no display
This information is intended for experienced users. It is not intended for basic users, hackers, or computer thieves. Please do not try any of following procedures if you are not familiar with computer hardware. I’ll not be responsible for the use or misuse of this information, including personal injury, loss of data or hardware damage. So use it at your own risk.
A. By Using the Motherboard Jumper:
In most motherboards CMOS battery is soldered, which makes it difficult to remove the battery. In this case we use another method.
Almost all motherboards contain a jumper that can clear all CMOS settings along with the BIOS password. The location of this jumper varies depending upon the motherboard brand. You should read your motherboard manual to check its location. If you don’t have the manual then look for the jumpers near the CMOS battery. Most of the manufacturer label the jumper as CLR, CLEAR, CLEAR CMOS, etc.
When you find the jumper, look carefully. There will be 3 pins and the jumper will be joining the center pin to either left or right pin. What you need to do, is remove the jumper and join the center pin to the opposite pin. e.g. if the jumper joins center pin to left pin, then remove it and join center pin to right pin. Now wait for a few seconds and then again remove the jumper and join the center pin to left pin.
Make sure to turn the PC off before opening the cabinet and resetting the jumper.
B. By Using Software:
I have found that BIOS/CMOS Password Recovery Tool is the most effective.:
BIOS/CMOS Password Recovery Tool is a program that works instantly to remove any lost or forgotten BIOS/CMOS password. Simply boot your PC to DOS and execute the program, and get access to forgotten BIOS/CMOS passwords in just seconds
how can i install the ioperm!!??
ive been working on that for 3hours and
no progress…..
can u explain it to me really specificly
cuz most of the instruction just sais “install ioperm.sys. with ioperm.exe-i” and that does not help me at all..
Not worked on my
DELL OPTIPLEX GX-280
As I said it does not work on notebooks normally. If you tried everything and it did not reveal the bios password you have to reset it on dekstop PCs. Try the killswitch first, if that is not working your only chance is to remove the battery or set the jumper.
Didn’t work on my Dell Machine.. this sucks
zzzZZZzzz: Maybe the last line explains your problem?
“Most notebooks store the bios password in an eeprom which can only be retrieved with an eeprom reader.”
Didn’t work on my Dell laptop .. the password wasn’t revealed
Great article. This can truely be a livesaver. Stumbled.