Google's .zip Top Level domain is already used in phishing attacks

Google released the top-level domain .zip to the public recently, which means that interested organizations and users may register .zip domains. Cyber criminals are already using .zip domains in phishing campaigns.
According to the SANS Internet Storm Center, about 1230 names have been registered so far. The top level domain was approved in 2014 but it took Google until May 2023 to unlock it for public registration alongside seven other domain extensions.
It seems that Google has reduced the registration price to $15 per year for a .zip domain last week, which appears to be less than halve the previous price. The price drop appears to have increased interest for .zip domains, and some new registrations are already used in phishing campaigns.
The .zip extension allows cyber criminals to run phishing campaigns that abuse the fact that .zip is a popular file extension and also a top level domain.
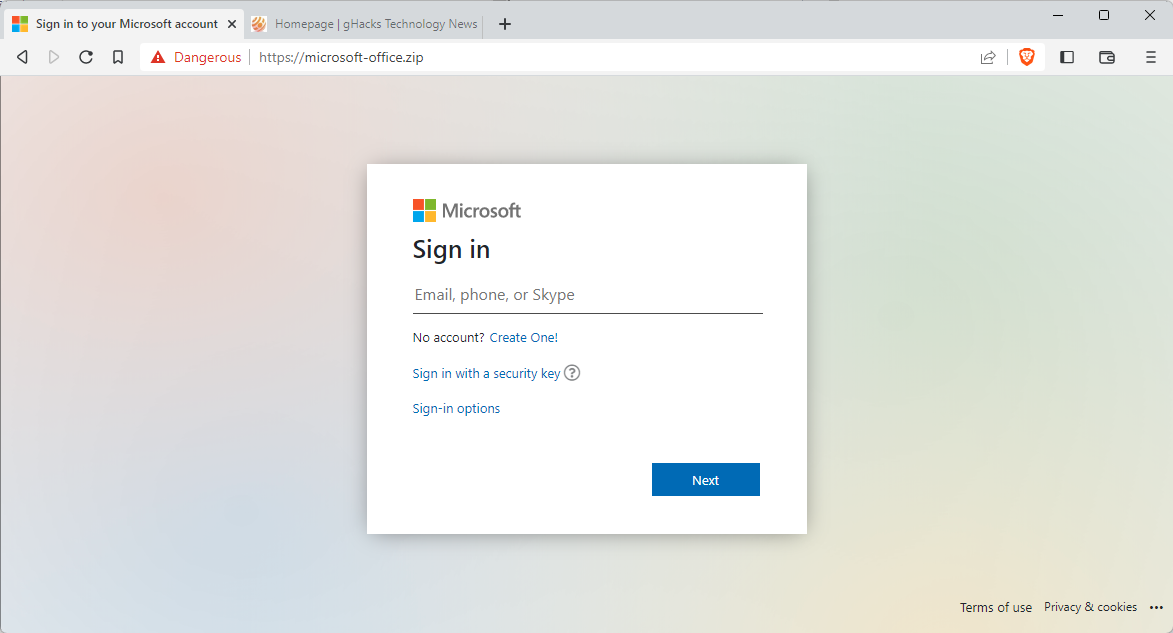
Domains such as officeupdate.zip or microsoft-office.zip have already been used in phishing campaigns. The latter is still online but safe browsing should warn users prior to accessing the site in question. Several of the registered domains could be used in phishing campaigns, while others may be used for legitimate purposes. The makers of archiving software might register a matching domain name for their products.
Most of the registered domains have not been set up to display web content. The message "the site can't be reached" or similar messages are displayed in this case.
The Microsoft phishing site displays a Microsoft sign-in prompt when it is accessed. Users should never see the page, but if they override the warning message, should not enter any data on the page.
Use in phishing campaigns is just one new option that cyber criminals have when it comes to .zip domains. Some applications may attach hyperlinks to ZIP file names now, which may lead to the firing of DNS queries and the leaking of information to the .zip domain.
The ICSS recommends to disable access to .zip domains entirely until the dust settles and risks can be accessed. Internet users need to take a closer look at .zip links and zip file extensions that may also be displayed as links in some applications.
For now, there is little reason to access .zip domains; this may change if legitimate companies and software developers announce that their products are now also available on a specific .zip domain.
Another one of Google's recently launched new top level domains might cause similar issues. The top level domain .mov is also available for public registration, and it too is also a file extension, albeit not as popular as .zip.
Now You: do you access sites that use newer top level domains regularly?

















Google’s motto went from “Don’t be evil” to “Evil is good”
I already block several gTLDs and visit regularly ‘Spamhaus – The Top 10 Most Abused TLDs’ at [https://www.spamhaus.org/statistics/tlds/]
For deeper information regarding TLds and gTLDs I visit ‘IANA – Root Zone Database’ at [https://www.iana.org/domains/root/db]
I’m adding .zip and .mov gTLDs to my DNS blocklist. I’ll maybe add ‘Google’s 101 originally applied for strings, separated by contested and non-contested’ available at [https://icannwiki.org/Google#New_gTLDs]
Any gTLD using a file extension is relevant of its owners’ questionable integrity in my view. Corroborates my extreme caution when it comes to Google.
“Any gTLD using a file extension is relevant of its owners’ questionable integrity in my view. Corroborates my extreme caution when it comes to Google.” <– Ditto that!
I'm using Firefox extension 'Block Site' where I added *.zip and *.mov for blocking. Works great! Easy to test too.
https://webextension.org/listing/block-site.html
I already have them blocked on our network. Thanks for the heads up.
One of the worst ideas by Google! Next idea will be the domain .Trojan, LOL.
How about .doc, .xls, .pdf, and .msg, John G.? Those would be real winners. Or .jpg, .gif, and .bmp.
They do already have .phd which i immediately misread as .pdf because i wasn’t paying enough attention.