TeamViewer Service Outage and hacking claims
TeamViewer, the company behind the popular remote desktop software of the same name, experienced a service outage caused by a denial of service attack on the company's DNS server infrastructure on June 1, 2016.
Since then, we have seen a spike in complaints on social media sites like Twitter or Reddit from people who claim that their devices were taken over by third-parties using TeamViewer.
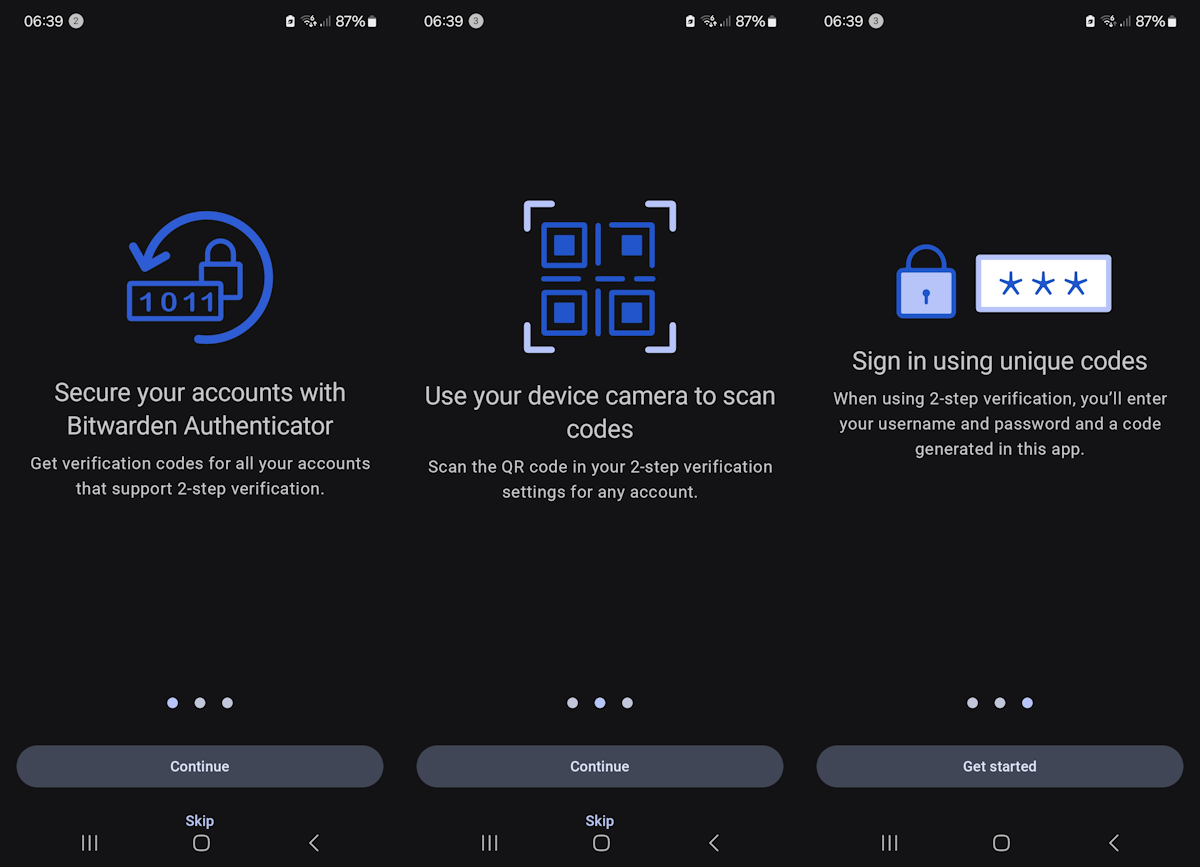
Statements range from user's noticing the unauthorized remote connection right away and disconnecting it, to users claiming that their PC was breached despite two-factor authentication and that the attackers managed to steal money from PayPal and other services.
TeamViewer denies that the company experienced a security breach and that the DNS issues caused by the denial of service attack are in any way related to the claims that some users are making on third-party sites.
The company points out additionally to other explanations for user system breaches and mentions explicitly password reuse and malware programs as two possibilities.
Fact is, there is has been an increase in users reporting that their devices were hacked by attackers using TeamViewer to get in.
Being a remote desktop software, attackers who successfully gain access to it can access the remote computer as if they were using it locally.
This includes opening programs, download files from the Internet, opening websites, recording passwords and other data if not protected, or opening documents and photos.
What you can do if you are using TeamViewer
The first thing you may want to do is check the connections log.
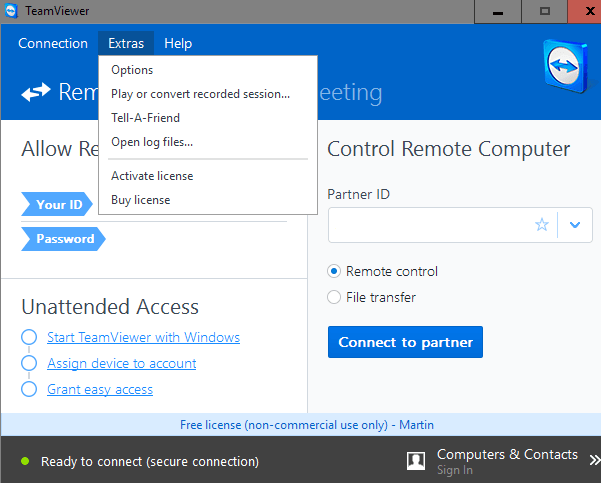
- Windows: if you run the full client, select Extras > Open Log Files.
- Windows: if you run the Quick Support version, click on the tool symbol in the upper right corner, and select Open Logfiles.
- Linux: run the command (with root) teamviewer -ziplog.
The log files -- on Windows -- are stored in the program directory, and they are usually kept even if you remove the program from a device.
You may want to go through the log file to make sure that you recognize all remote sessions of the past three or so days.
If you have noticed a breach, you may want to be extra cautious and start changing passwords, check accounts and the account history if provided, and online accounts on sites dealing with money such as PayPal or Amazon.
If TeamViewer is running on your devices, you may want to make sure -- at least for the time being -- that the device is not left unattended. Alternatively, you may want to consider enabling TeamViewer on demand only instead of having the software run all the time. This is a precautionary measure to protect the device against hacks.
Now You: Are you using TeamViewer?





















I use TV, and I was worried about how this article was worded. I did some research, and TV stated that any people affected are people who have actual accounts. I never signed up, and instead use the desktop client that only uses a machine ID and PIN/password to connect. No usernames or passwords for any TV accounts, so these types of people/connections were/are not affected. Could this article be updated to include that info? Here’s where I read it from:
http://arstechnica.com/security/2016/06/teamviewer-says-theres-no-evidence-of-2fa-bypass-in-mass-account-hack/
I’ve used teamviewer to remote control my desktop and laptop from my phone for my own convenience. I started getting weird charges on my PayPal a few days in a row when though I chanted the password each day. I found another article about this and checked my logs. They matched the times that these transactions happened. I have since stopped teamviewer from running in the background and am looking for a local remote desktop like service. My main problem is teamviewer can’t seem to admit they had a breach. How can you ever trust a company like that even if you’re just using it to help family with random generated passwords? I was able to fine the teamviewer ids and some emails that the hackers used but don’t know who to report them to. All in all, I seem to have gotten lucky so far with my problems as there are some horror stories on Reddit about this.
A good write-up here: http://www.howtogeek.com/257376/how-to-lock-down-teamviewer-for-more-secure-remote-access/
Personally I don’t have a TV account, but a lot of the stuff still applies. Don’t run on startup (or as a service), secure (and unique) passwords, 2FA, etc.
I think you should not have it on by default.
I’m thinking about the worst possibility: Team Viewer’s staff can browse into your computer undetected.
It has ‘freeze screen’ hidden feature so you can see the screen is not changing while actually someone is browsing your computer.
Or even looking at your computer without controlling so you don’t know someone is watching you undetected.
So scary!
This has certainly happened, I was sat watching tv a few hours ago when my PC screen came on I thought nothing of it until I saw PayPal screen flash up, my passwords was saved in and it logged in, I jumped up and shut the screen off, I run online business and have quite a bit in my PayPal account, luckily nothing was taken, checking teamviewer logs there was 3 logins today but 2 different addresses but also some logins from 27th may, I wasn’t at home when the other logins happened today so seem very lucky no money was removed although I don’t know why, removed it now changed all passwords definately shook me up…
Probably unrelated but still interesting:
Statement on the appearance of the Windows Trojan BackDoor.TeamViewer.49 released May 27, 2016.
https://www.teamviewer.com/en/company/press/statement-on-the-appearance-of-the-windows-trojan-backdoor-teamviewer-49/
I have used TeamViewer on my old computer (Windows 8/not 8.1) but unistalled it.
June 3, 2016. The Teamviewer web site is still down here in Colorado. I uninstalled TV, and won’t/can’t use it until a new safer release is provided. At this point the web site isn’t even available.
The thing about TV is that you explicite allow someone the access to your pc, it comes with several additional protection. E.g. you get an warning on administrative execution stuff and more but overall I was never a fan of this, I helped some people here and there but after that I uninstalled/removed the entire software. So I only recommend to use it if you really need it, otherwise block access and ensure the service is only running if you really need it.
I haven’t read much about this yet, just a quick scan of the one article (plus Martin’s one as well), and TV’s statement on their site, and two reddit threads. So what I say next is just my thoughts. This has only happened to those who run TV as a service/run at startup, and I for those who have accounts. There is also 2FA to consider. Next, we have for sale, and cheap at the price, large scale databases of accounts + passwords – combined megabreaches from over the years. More than half a billion. Now let’s assume a percentage of these people use the same password on multiple accounts. How hard is it to automate trying to connect to those accounts but on TV and getting some % that work? Note that TV themselves say that TV has mechanisms to block brute force. It also uses end to end encryption, to answer Bart’s question above. As Jojo says, some people are reporting that 2FA didn’t save them. Can’t wait to find out the exact details and proof of what’s really going on.
As for myself, I use TV all the time with my clients. I use this because it shows transparency (the client can see me when I’m logged in and can kick me out anytime). They run portable versions (but even installed is OK. When you run the installer you have an option to not install as a service (even if you did you could disable that service)). And there is an option to not start when the system starts. When my clients run TV, it generates a new password every time. Passwords settings have been changed in options to 8 or 10 chars depending on the client – some clients have no idea what a some symbols are called, so they don’t get the hardest setting, but it doesn’t really matter in my case, because we don;t leave TV running unattended. When TV is finished, closing it closes it for good – no background service running here thanks. Clients only start TV with me over the phone so I can log in. And they click ok, thanks, when its finished after I jump off. Next time they open it, bingo new password. There are no TV accounts here, and none of them ever need to be able to remote into their own PCs.
tl;dr: I use TV with loads of clients
– all my clients all use portable versions, no unattended access allowed (no service, no run on system start)
– all my clients do not have any TV accounts
– all my clients have best or second best password strengths
– TV is only ever initiated by a phone call with the client
– TV is closed after each session
– every new start of TV creates a new random password
My clients and I are not worried one iota. It’d be a different story if they required 24/7 remote access. Especially if 2FA was not working.
Martin is clairvoyant and clearly means Wednesday November 1st 2016 when he says “Wednesday 1, 2016”. Don’t be so pedantic people. It’s not hard to work out. There are only two months in 2016 that .. oh wait .. TWO. Anyway, he clearly meant November. /s
Be careful with _installed_ Teamviewer. Even if you manually set the service disabled, it gets enabled every time you update the program!
I contacted Teamviewer about this over a year ago, but nothing has changed even though they answered that they understand the problem.
Pants, I agree with what you’ve said about passwords and running processes in TeamViewer (and I wrote something to a similar effect above).
But there is an important caveat for Linux users. So here is a public service announcement:
A TeamViewer process called teamviewerd continues to run in Linux even after the client is closed. If you manually kill the process it will re-start. On older versions of the client, the command “sudo teamviewer –daemon disable” did the job, though some people have trouble with this in newer versions. A more reliable solution may be to edit TeamViewer’s config file (probably located at /etc/init/teamviewerd.conf) and delete the two lines that have the word “respawn” in them.
I use a SlingBox that’s set up for remote access. I also use a pfSense router that has logs out the wazoo. I’ve never seen a probe on the port I have open for the Slingbox, and it’s a standard port. I was worried for a while, but, given the utter lack of hacker interest, I assumed it was safe an haven’t wrapped any other security around it. As the IoT grows, I may someday put it on a different subnet in the future with other IoT devices if I ever get some.
Wednesday 1, 2016? when?
Used it, to support others, till I recently updated my WIN OS [XP to 8.1]
I’ve read a comment at some forum [haven’t checked it, I don’t have Teamviewer installed atm] that suggested that one could allow only specific linked devices [according to mac address was it?!…] to access his temviewer and also to of course set 2 factor authentication….
wait.. these users [as reported] said also these measures didn’t help?
I give up :P
Not sure if you can restrict MAC addresses, but I don’t think this would help much. My understanding is that MAC address spoofing is pretty darned easy.
http://arstechnica.com/security/2016/06/teamviewer-users-are-being-hacked-in-bulk-and-we-still-dont-know-how/
TV are going to roll out a “Trusted Devices” feature. How it determines the device is anyone’s guess at this stage. Guessing a MAC address to spoof would be rather hard – it’s not like you can watch wifi traffic and pluck it out of thin air.
Wednesday 1, 2016.
Hi Martin,
Is this date format really valid ;)
Of course it is ;)
I always said: The connections between 2 teamviewer programs, goes by a server of teamviewer.
The outage day, before yesterday, confirmed my suspicions, because my friend and i could not
get connection with eachother.
So the thought is now: Can they monitor our conversations, and store them too?
Bart
Bart, to be specific, TeamViewer has two modes of access. One is a ‘relay’ through their servers. I don’t know the details, but their servers are involved in the middle. The other is access only over the local lan. The latter is useful for in-house only support and as I described in my comment above.
To me, password-only access from anywhere into the home network is frightening regardless of the remote desktop program used. A good guess from some goofball could allow said goofball complete access to your home, privacy, and savings. Asymmetrical security, such as security that’s certificate based, combined with dual factors, such as certificates, passwords, and specific user ids tied to the installed client certificate are needed. Anywhere Access and SSTP on Windows servers provide decent VPN security, although pfSense is free and you end up with a powerful router in the process and don’t need a Windows Server to be involved.
cdr:
Thanks for the reply and the info.
What i just did: after the installation of teamviewer
disabeled the TeamViewer_Service.exe in services services.msc
and renamed the TeamViewer_Service.exe in TeamViewer_Service22.exe
so it will not start anymore.
I will do so with my friends.
Have a nice weekend, and thanks for the help
Regarding TeamViewer passwords, doesn’t the client automatically create a new complex password every time you launch it? Unless you leave the client running day and night, week after week, the odds are pretty low that a hacker will crack the particular password you have during a short-lived access session. I mean, it would be easier to just find an exploit in the client code that will work on all clients all the time, rather than try to hack someone’s password.
I guess the real security problem is not the method of access, but the fact that some people probably leave TeamViewer running all the time for their convenience. That DOES seem like a terrible idea. For me, TeamViewer is just a tool for occasional remote tech support, not for continuous access to your computer.
Bart, I know what you mean although I doubt TeamViewer has any interest in any individual user’s affairs.
I use TeamViewer, but with a twist. It can only access a client via the local lan. To get on the local lan from elsewhere I use a tap connection on OpenVPN via my pfSense router. This bridges to my local network securely. It has certificates, a specific user id tied to the unique certificate on each remote pc, and dual passwords. TeamViewer servers are not involved, as all it would take for someone else to break in would be their discovery of my TeamViewer password.
It took a little know how to build but allows me to use the very superior TeamViewer remote desktop program with absolute security.
The only possible downside is that OpenVPN / tap access is not available from Android unless you buy a specific app. A Windows laptop can get through without any effort, assuming the server is set up properly.
As far as I understand from their docs, teamviewer only does a handshake in the beginning and then the connection really is between both devices. There is a diagram in there security statement, that kind of explains it: http://downloadeu2.teamviewer.com/docs/en/TeamViewer-Security-Statement-en.pdf