Firefox Add-on Signing criticized for being ineffective
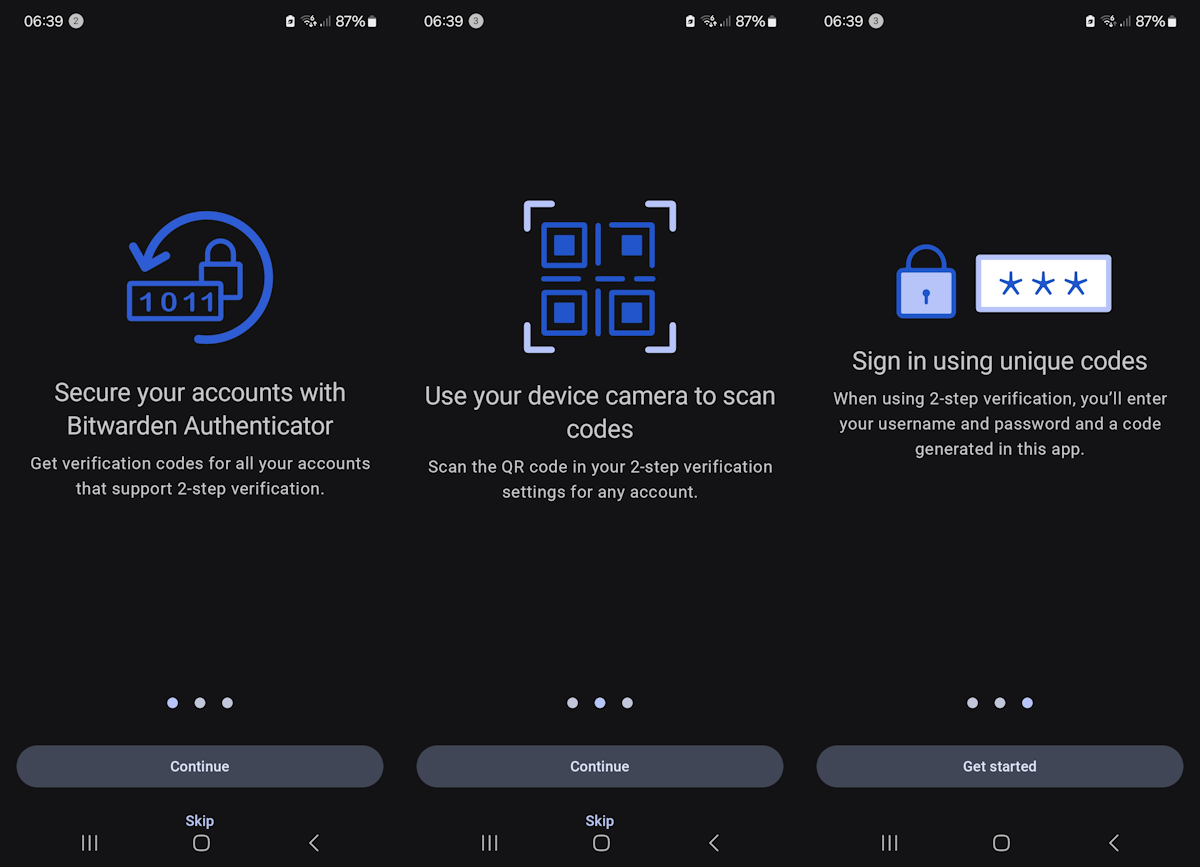
Mozilla announced back in the beginning of 2015 that it would require Firefox add-ons to be signed before they could be installed in release and beta versions of the web browser.
The idea behind the move was to make the Firefox add-on landscape a safer place for users by protecting them from invasive or outright malicious add-ons (since those would either not be submitted at all, or if they were, blocked by the signing scanner).
It turns out though that the process may not be as effective as Mozilla hoped it would be. Dan Stillman, a developer working on the Zotero add-on for Firefox criticized Mozilla's add-on signing plans heavily in a recent blog post.
Add-ons that are not hosted on Mozilla's official add-on store need to be submitted whenever they are updated, and they are signed if they pass automatic inspection, or need to be submitted for manual review if they don't pass the automatic test.
These reviews take up to seven weeks for preliminary reviews which means that a new version of Zotero could not be released while still under review, and that is not only problematic because of the time between submitting a release and getting it signed, but also because it makes it impossible for the developer to react quickly when time is of the essence (think security or stability fix).
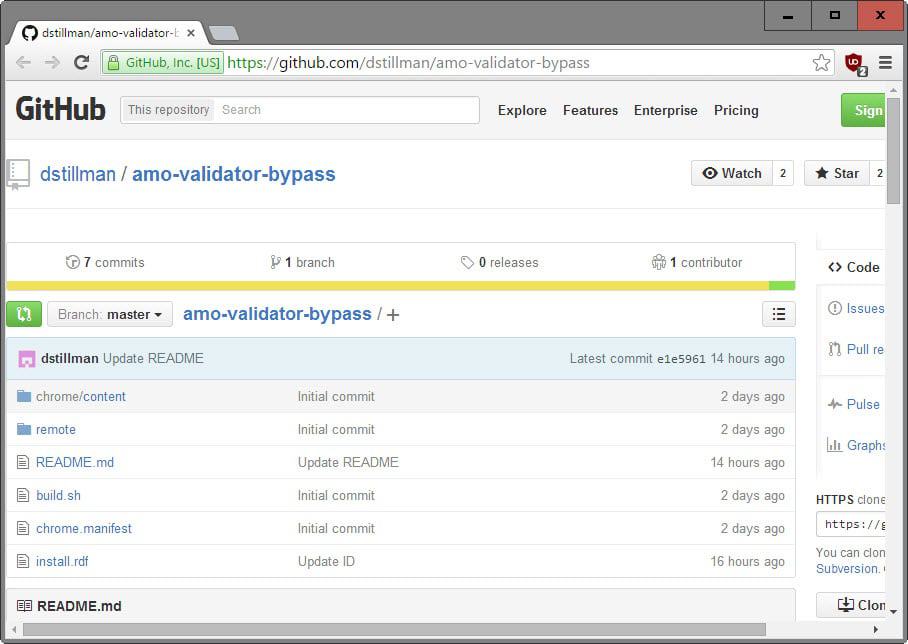
If that would not be bad enough, Stillman points out that the AMO validator script is not effective as it can be bypassed easily.
What this means? Malicious add-ons will be signed if they pass the automatic validation, and since they are not reviewed in this case by Mozilla employees or volunteers, can be offered on third-party websites or via software installers, and will install just fine in release Firefox or beta Firefox.
A quick proof of concept add-on was created to proof the point. It monitors HTTP(S) requests for Basic Auth Credentials, and posts them to a HTTP server. It furthermore runs an arbitrary local process when a given url is loaded, and will download arbitrary JavaScript code from a remote server and run it with full privileges when another is loaded in Firefox.
Mozilla's response? According to Stillman, Mozilla's Add-ons Developer Relations Lead stated that "most malware authors are lazy" and that the scanner would "block the majority of malware".
That was back in February and nothing seems to have changed in this regard since. Mozilla did however add the proof of concept add-on to the Firefox blocklist (not the code used by it though), Stillman then went ahead and added a random ID to the add-on which meant that it would once again pass add-on signing validation with flying colors.
One thing that Mozilla considers currently is add whitelist exceptions to add-ons under certain circumstances. This is discussed on the Mozilla Add-ons User Experience group currently.
According to the information posted there, exceptions could be made if add-ons meet certain requirements such as a 1-year solid track record with no serious review issues, and more than 100,000 active daily users.
Implementation would help popular extensions get releases out quickly to users, but it won't fix the underlying issue that add-on signing is not effective in preventing malicious extensions from being installed in Firefox.
Now You: What's your take on add-on signing?



















Further Note: using the about:config command to change the signature demand to false, does not work with FF v 43.0.1 – just so you know. Oh, you can change it to ‘false’ without any drama – but in reality, it changes absolutely nothing, that’s all.
Kaspersky Internet Security is STILL disabled by Firefox with absolutely no way to enable it and no option (naturally) to do so in ‘addons>extensions’.
Dan Stillman’s ‘final update’ in his blog post states: “Update (December 1, 2015): Mozilla is changing its signing policy and will no longer block releases of unlisted extensions that don’t pass the validator. Manual reviews will be performed separately from the signing process. Thanks to everyone for speaking up in support of Zotero and other unlisted extensions, and to Mozilla for listening.”
Clearly that isn’t the case and Mozilla seems to have been infected with Google’s gestapo-like mentality.
S: You said: “Clearly that isn’t the case and Mozilla seems to have been infected with Google’s gestapo-like mentality.”
Can you explain that? I’m not sure what part of your post that last statement applies to, and I could only guess, which might or might not be a correct guess.
In a February blog post introducing extension signing [1], Mozilla told that “Extensions that change the homepage and search settings without user consent have become very common, just like extensions that inject advertisements into Web pages or even inject malicious scripts into social media sites.” They explained that extension signing was their new idea to combat such extensions.
These extensions are quite elaborated, they often come with a fake brand and logo and operate at a commercial-scale by being bundled into software’s installers.
There’s no way the broken AMO validator will stop them. It’ll, however, stops legitimate extensions that raise false alarms.
[1] https://blog.mozilla.org/addons/2015/02/10/extension-signing-safer-experience/
I agree, Ireneus, not to mention that since “There’s no way the broken AMO validator will stop them” (those operating at a commercial-scale if not a few others) the same problem as relying totally on an anti-malware may lead to excess of confidence in settled security, the same may happen when users will be totally confident in the “signed” add-ons.
Mozilla has to find another approach. Signing won’t do it.
http://danstillman.com/2015/11/23/firefox-extension-scanning-is-security-theater?firefox-against-censorship That is the way Mozilla treats people which they do not agree with.. That guys are becoming more and more an utterly disappointment!
Yeah, I’ve read that as well, good thing you post that link to allow all of us to realize what is the sectarian, stubborn mentality of this unqualified Mozilla staff. Totally amazing : “1+1=2 … nops, do they reply, =3, because we said so”.
Stunned immaculate.
Yeah, that link is already in the article above I saw ;)
I Don’t know what Mozilla is doing, looks like some serious issues in decision making and communicating regarding problems for their decisions and adjusting their course based on feedback…
I’ve used Firefox for a very long time, if I could step over to a good alternative that gives the functionality I need, I would… but so far the forks don’t allow me to do all I need with them. I’m not a dev, so I can’t do them myself, and don’t have time to start on that either.
I hope the whole idea with the add-on signatures will be dropped.
Take a look at Ant Video Downloader… read their privacy policy. It’s effectively spyware and it’s still availabe despite user complaints.
Mozilla needs to actually do something or get out of the way. Add-on signing is a half measure that hurts more legitimate devs and users. Their response to it’s effectiveness that “most malware authors are lazy” sums up the current state of Mozilla as a whole… pathetic.
I’d love to see a Mozilla dedicated site perform with add-ons what VirusTotal performs with files. Is it not possible to develop an algorithm that could scan an add-on and determine at least a score of trust on a given scale? This would at least limit possible malware even if it did require in fact the user’s active participation …
Concerning how things are going on right now, how they seem to be planed to remain concerning the signature feature, if it appears that indeed the signing process may be hijacked then I really see no reason to not reconsider the entire signing policy, far above a sad “most malware authors are lazy” and that the scanner would “block the majority of malware”. which sounds ridiculously cynical if not plain stupid.