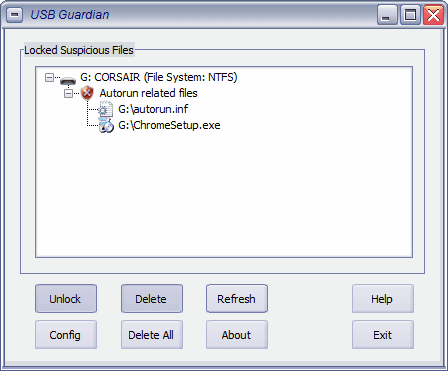
USB Flash Drive Guardian
USB Guardian is a free security program for the Windows operating system that can improve a system's protection against threats that use removable devices as an attack vector. USB storage devices, USB […]

Internet Explorer And Firefox Exploited At Security Conference
If there is one thing that you do not want to read as a web browser user or company that created a browser, it is that your browser has been exploited at […]

Use a secure shell configuration file for easier use
If you've ever used secure shell you know that it can get a little daunting with all of the command options available. But did you know you can make this task much […]
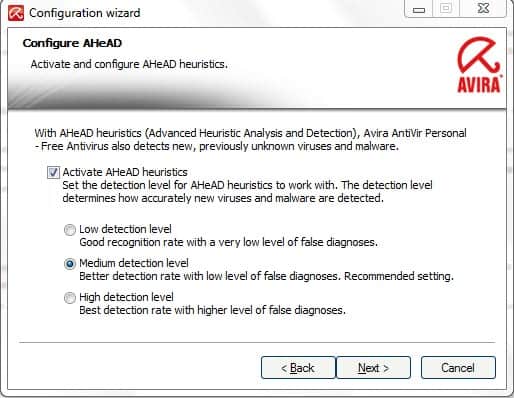
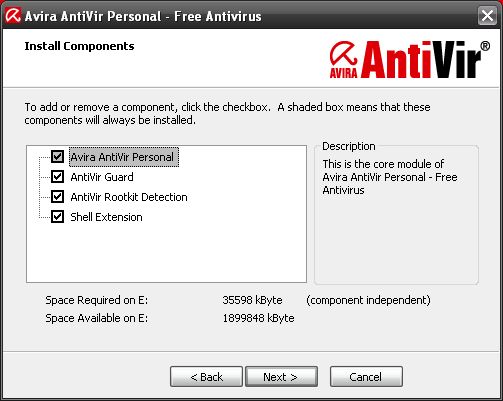
Avira Antivir 10 Personal Download Available
Update: Avira Antivir 10 is no longer the most recent version. You can download the latest version of the antivirus software from the official company website. The popular antivirus software Avira Antivir […]

Twitter Starts Scanning Direct Links To Improve Security
Twitter has been targeted by users with malicious intent ever since it started to become increasingly popular. One of the biggest problems up to yesterday were direct messages which one Twitter user […]

Microsoft Security Updates March 2010
Microsoft released security patches yesterday for Windows and Office products on the monthly Patch Tuesday which is always on the second Tuesday of each month. A total of three security bulletins have […]

Comodo Internet Security 4 Download
Update: You can download the most recent version of Internet Security from the Comodo website. The version discussed in this article is not the most recent one anymore and it is not […]
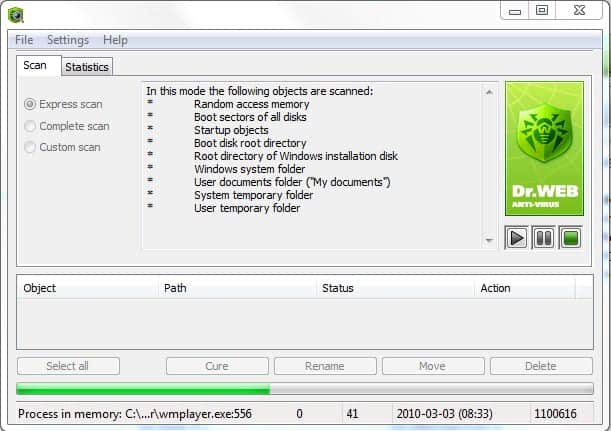
Dr.Web CureIt Antivirus Software Review
There is no antivirus software that catches all viruses. Even the best security applications do not have a perfect detection rate which means that it can happen that a virus slips past […]

Microsoft Releases Blue Screen Rootkit Detection Tool
Last month's Microsoft security updates have caused some controversy over a single patch in the pack that was first thought to cause blue screens on some computer systems. It later turned out […]

Adobe Fixes Adobe Download Manager Vulnerability
A security vulnerability in Adobe Download Manager was discovered this month besides the recently discovered security vulnerabilities in Adobe Reader, Adobe Acrobat and Adobe Flash which had been discovered and fixed by […]

Please Rob Me Demonstrates The Dangers Of Location Based Services
Please Rob Me is a free service that demonstrates the dangers of using location based services publicly on the Internet. Location based services can be helpful to the user, no question about […]

Whitelist Hash Database Frontend
The National Software Reference Library has initially been designed to aid computer forensics experts in the investigation of crimes that involve computers. It consists of a list of nearly 40 million files […]

Malware Cause For Blue Screens After Recent Windows Update
Reports about blue screen crashes began to appear on the Internet shortly after the release of this month's security patches for the Windows operating system. Especially Windows XP users seemed to have […]

European Payment Cards Security Problem
A recently published technical paper entitled "Chip and pin is broken" by security researchers Steven Murdoch, Saar Drimer, Mike Bond and Ross Anderson reveals how criminals can use stolen payment cards without […]
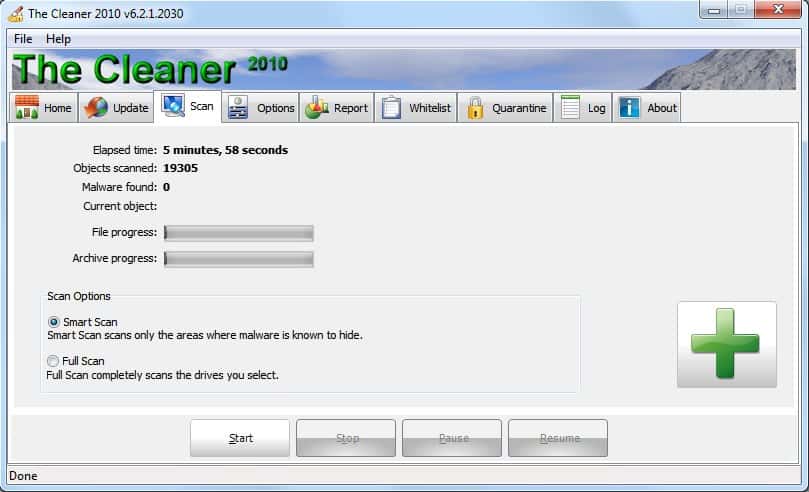
The Cleaner
The Cleaner was one of the few solid programs back in the good old days to clean malicious software from a Windows computer system. It somehow seems to have lost its appeal to […]
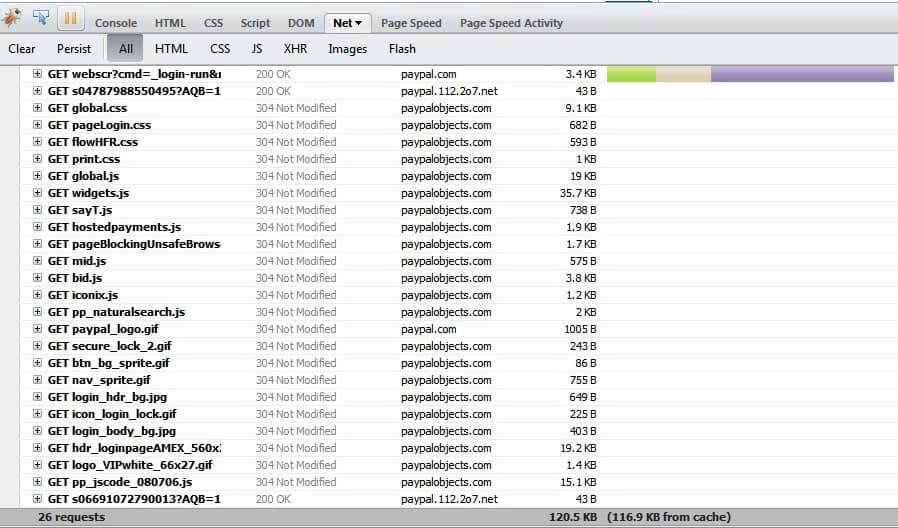
What Is paypal.112.2o7.net
If you are a very observant - or cautious - PayPal user you may have noticed that several connection requests are made whenever you connect to the main PayPal website that you […]
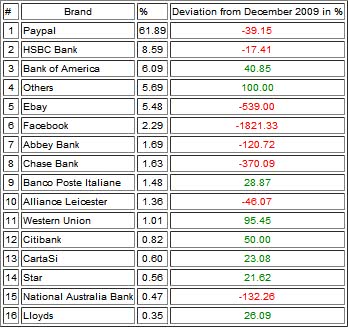
Avira Most Phished Brands January 2010
Phishing is still one of the biggest threats that users face on the Internet these days. Many security programs and web browsers offer phishing protection, but these only catch known phishing sites […]
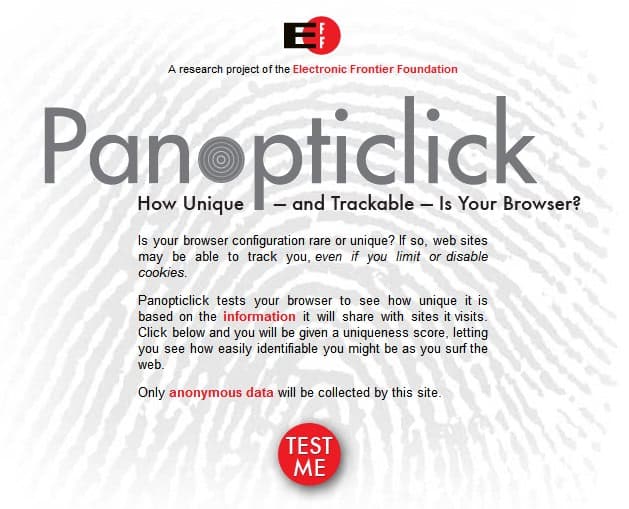
How Unique Is Your Web Browser's Fingerprint?
Can sites you connect to in your web browser of choice identify you using so-called browser fingerprinting? Lets find out. Sites can identify various technical information of a connecting web browser and […]
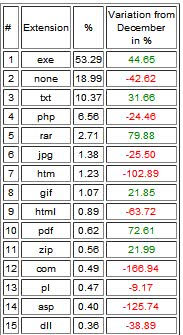
Avira Malware File-Extension Statistics
Malware is a generic term for trojans, viruses, worms, keyloggers, rootkits and other malicious program code. Avira posted on the official company blog interesting statistics about malware that gets distributed using url, […]

Online Armor++ Review
Update: The Online Armor website and program are no longer available. Online Armor++ is an all in one Internet security suite that retails for $59.99. It offers all the security modules one […]
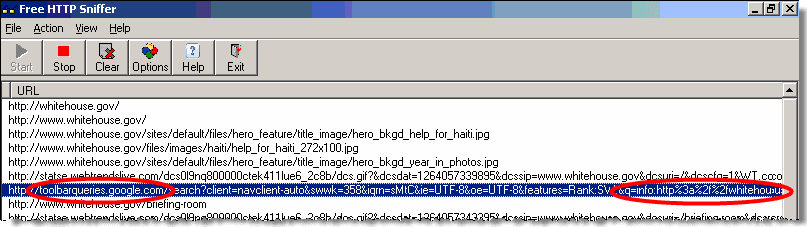
Study Suggests That Google Toolbar Transfers Data Even In Disabled State
Update: The Google Toolbar is only available for Internet Explorer 6 and up on Windows. Google has retired all other versions of the toolbar. The Google Toolbar is a web browser add-on […]
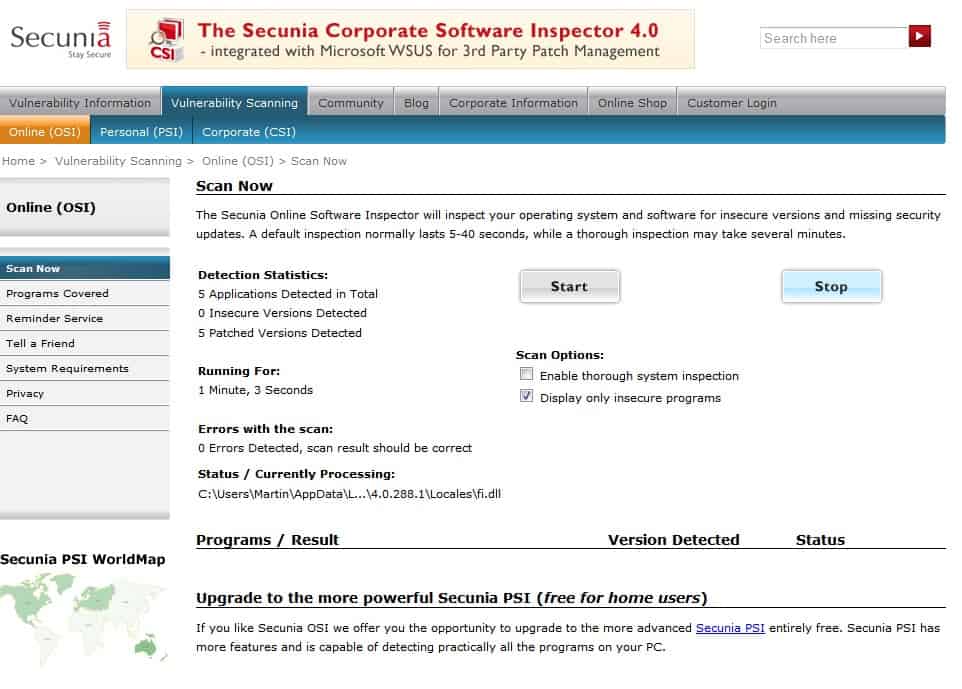
Secunia Online Software Inspector
Update: Secunia has discontinued the Online Software Inspector. The company is offering the Personal Software Inspector free of charge to private users which offers similar functionality. It is however only available as […]

Internet Explorer Emergency Patch Download
Update: Microsoft has added the patch to Windows Update which means that all users of the operating system who use the service should have it installed by now. It is not an […]
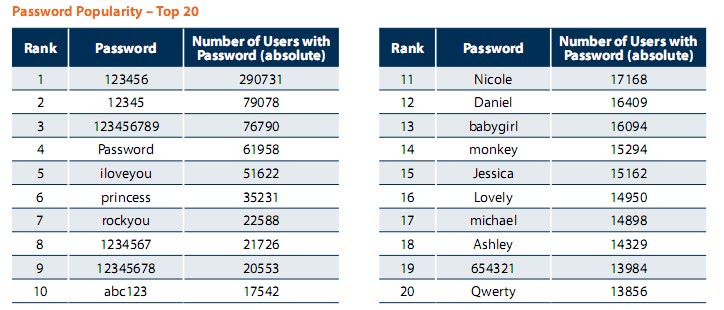
RockYou Hacked. Some 30 million passwords in the wild [Security]
RockYou, a service that offers applications like slideshows, games, layouts and more for social networking sites like Facebook, MySpace or Orkut was recently hacked and the service's entire database of 30+ million […]
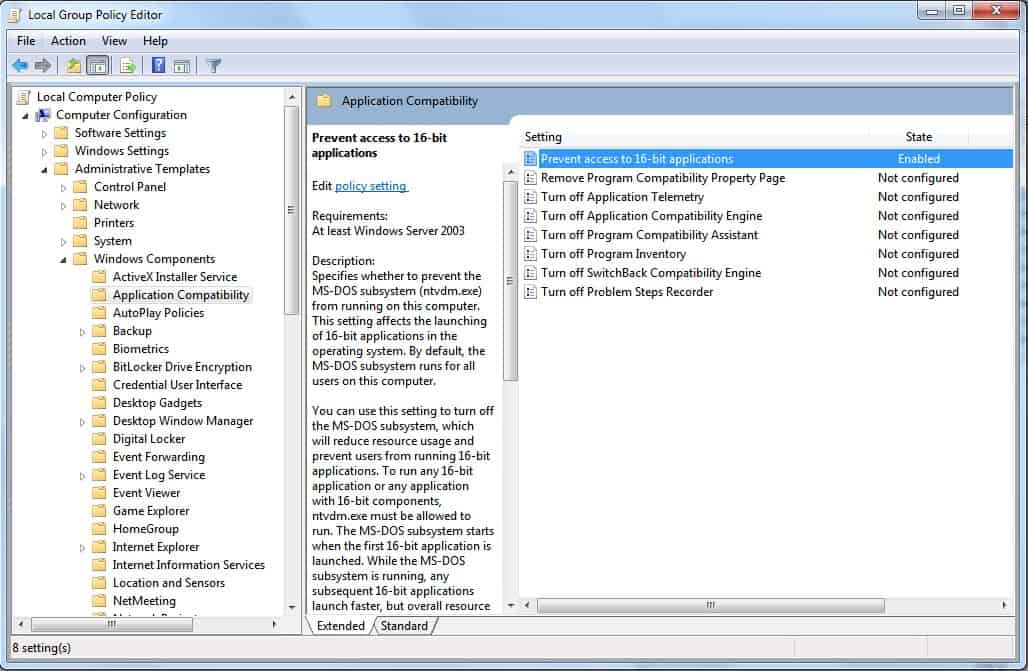
New Windows Vulnerability in VDM Discovered [Security]
The last days have not been pleasant for Microsoft. A new Windows vulnerability affecting all 32-bit editions of the operating system from Windows 3.11 to Windows 7 was uncovered shortly after the […]
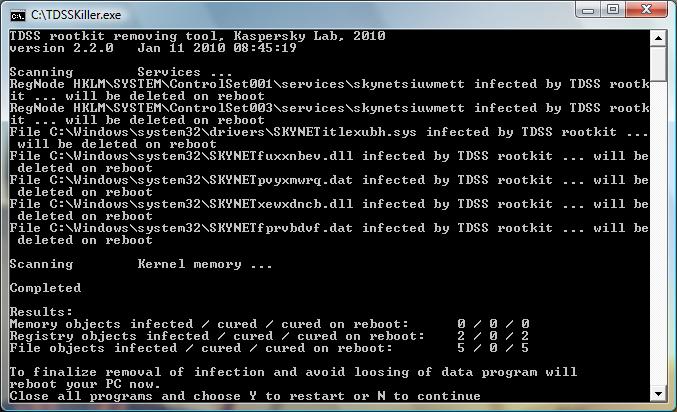
Another Fix For Unauthorized Google Redirects
We posted a solution for one of the causes of unauthorized Google redirects yesterday. These redirects can happen in one browser or multiple ones, and are usually related to searches that the […]

Fix Uninitiated Google Redirects With GooredFix [Firefox]
Goored is an abbreviation for (malicious) Google Redirects. although redirects have been experienced by users affected by the issue in other search engines like Yahoo as well. Firefox users who have been […]
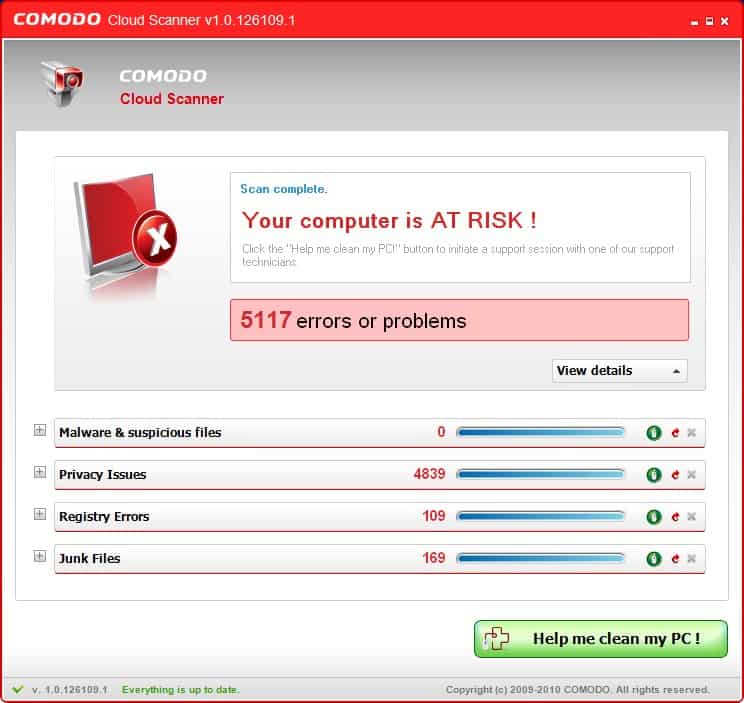
Comodo Cloud Scanner
Update: Comodo has discontinued the standalone Cloud Scanner product and integrated it instead into the company's Internet Security application. Moving virus definitions and other core files into the cloud seems to be […]

Microsoft and Adobe January 2010 Patch Day
Microsoft and Adobe have released their regular security updates today. Microsoft has only released one patch that applies to most of its operating system. The patch fixes a vulnerability in the embedded […]
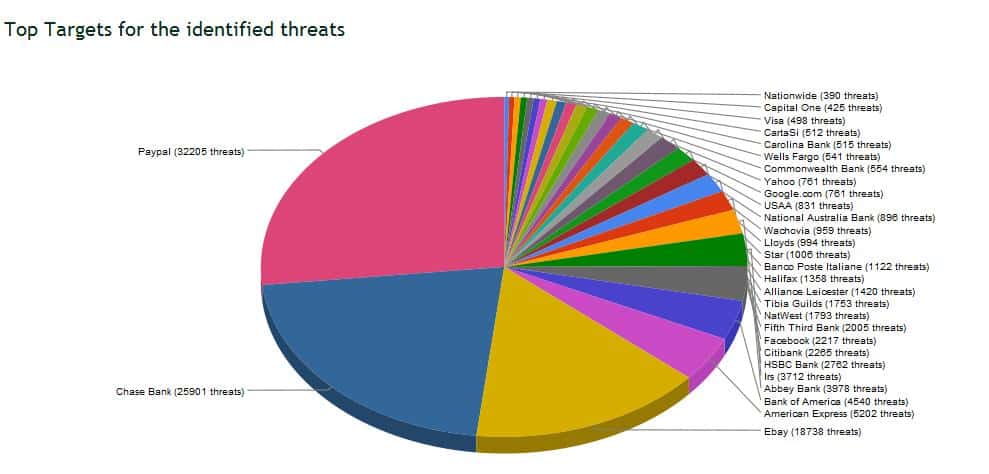
Top List Of Brands That Experienced The Most Phishing Attacks In 2009
Avira has published a top list of brands that experienced the most phishing attacks in 2009. The top 3 brands according to Avira's chart are PayPal with 32205 threats followed by Chase […]

Another Adobe Reader Zero Day Vulnerability In The Wild
Adobe Reader and Adobe Acrobat have been hit with yet another zero day vulnerability that is affecting all versions of both programs up to and including Adobe Reader and Adobe Acrobat 9.2. […]
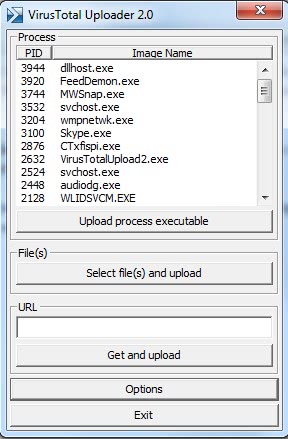
Virus Total Uploader Update
Virus Total Uploader is the official desktop program for Windows of the Virus Total service to have files scanned directly from Windows. Virus Total offers a great service for users who want […]

Christmas Giveaway A-squared Anti-Malware
Security software like A-squared Anti-Malware protect the computer system from threats and attacks not only on the Internet but also locally. Update: Please note that A-Squared Anti-Malware is now known as Emsisoft […]
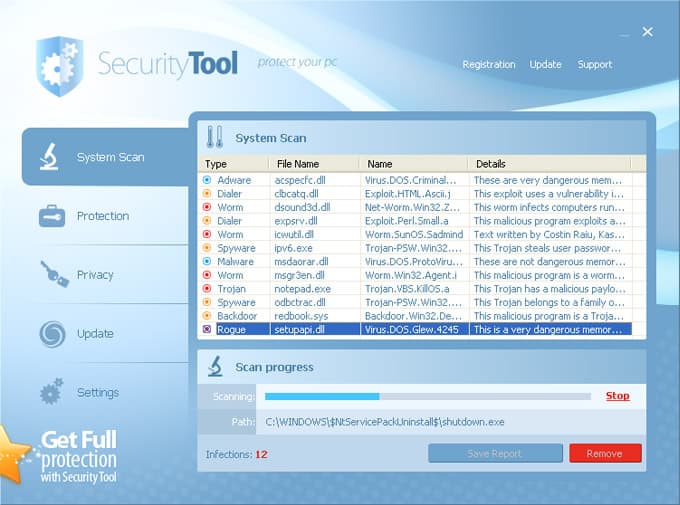
Security Tool Removal Instructions
Security Tool is a so-called rogue antivirus software that is distributed by various means including malicious software like trojans. It is also distributed through popups on the Internet which display a fake […]

Microsoft Security Updates December 2009
Microsoft has released a new batch of security updates on this month's Patch Tuesday which patch various security vulnerabilities in Microsoft software products. The vulnerabilities are affecting several popular Microsoft products including […]
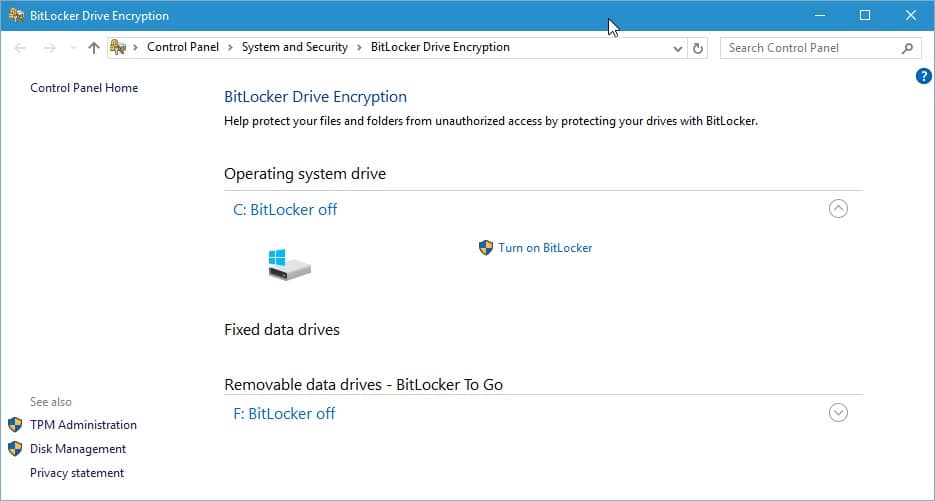
Bitlocker Encryption Not 100% Secure After All
Earlier this year a method to get access to data encrypted with the Open Source software True Crypt was published by security researchers. It involved physical access to the protected computer system. […]
Zonealarm 9.1 Firewall Free Windows 7 Released
Update: ZoneAlarm released new versions of its firewall product. You can download the most recent version from the official website where it is still available for free. The free version is compatible […]
MocoSpace Login
MocoSpace is a so called mobile social networking website. What this means is that it is primarily designed for mobile access and not computer desktop access. Another interesting aspect of MocoSpace is […]
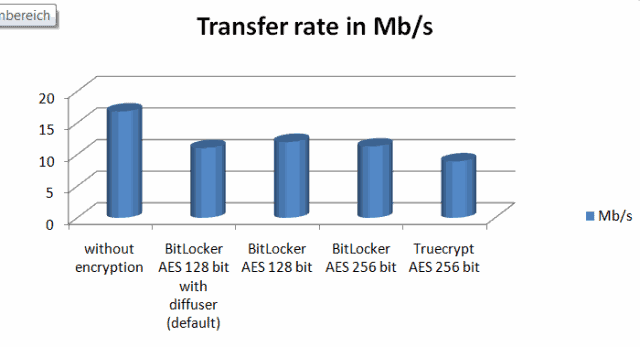
Bitlocker Versus True Crypt Performance
Alexander over at 4Sysops ran a benchmark comparison test of the encryption software programs Bitlocker and True Crypt on netbooks. Bitlocker is the encryption software that ships with Windows 7 Ultimate and […]
Antivir Maker Avira Changes Update System
We ran a post in the beginning of this month (read: Avira Antivir Update Hangs) in which we mentioned a growing problem that users of Avira Antivir experienced. The problem that users […]

