
Microsoft Security Updates November 2009
Microsoft has released six security bulletins today as part of their monthly Tuesday patch day. The six bulletins fix a total of 15 security vulnerabilities in Microsoft Office and Microsoft Windows. The […]
Panda Cloud Antivirus Released: still free
Panda Cloud Antivirus has been released today after months of being available as a beta version. The antivirus software, which has been offered as a public beta since April 2009, received more […]
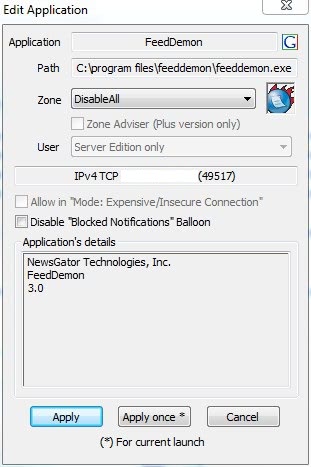
Windows Firewall Control review
Windows Firewall Control is a program for Microsoft Windows devices to add better built-in firewall controls to the operating system. The firewall in Windows 7, Windows 8 and newer versions of Windows […]

PayPal Login: security information
PayPal is a widely used financial service that allows people from all over the world to transfer money to other PayPal users or companies by simply specifying an email address the money […]
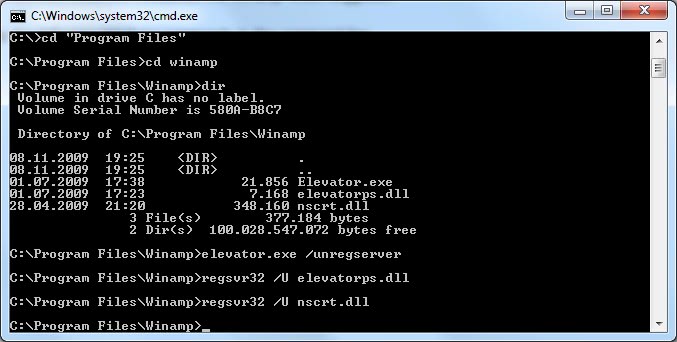
Elevator.exe In Winamp Folder
After dabbling around with several music players on a new Windows 7 PC, I finally decided to stick with AIMP2. The uninstallation of Winamp turned out to be interesting. The uninstaller noted […]

SafeOnline Protects PCs Even If They Are Infected
I have worked for one of the biggest financial organizations in Germany in the past. One of our jobs was to deal with customers who had fallen pray to phishing and other […]
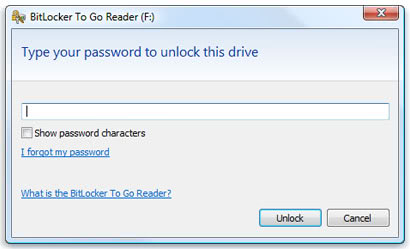
BitLocker To Go Reader
Bitlocker To Go is a program for Windows XP and Windows Vista that allows you to mount FAT Bitlocker volumes in read-only mode. Bitlocker is a data encryption technology that Microsoft implemented […]

Avira Antivir Update Hangs [Fix]
News about an Avira Antivir update have been appearing on the Internet lately by users of the antivirus software Avira Antivir. These users reported that they encountered update problems. The description was […]
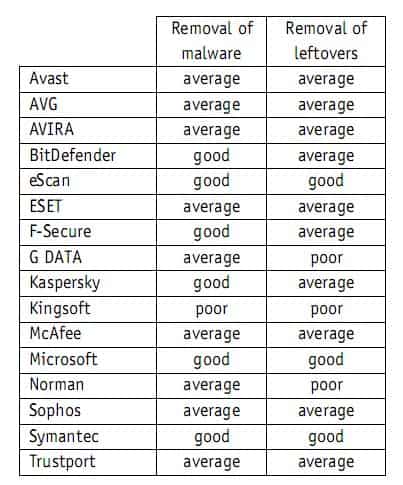
Microsoft Security Essentials Rated Highly In AV-Comparatives Test
Most tech savvy users have their personal favorite when it comes to antivirus software. Be it security software from Kaspersky, Symantec, Trend Micro, AVG, Avira or Avast: everyone seems to have a […]
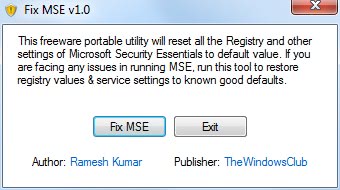
Repair Microsoft Security Essentials
Microsoft's new security software Microsoft Security Essentials has been getting some good reviews since the first public beta version was released by the company to a limited number of beta testers. The […]

Four Options To Deal With Flash Cookies
Flash Cookies, which are also known as super cookies or Local Shared Objects, should not be confused with normal cookies that are placed by websites. Normal cookies can easily be deleted from […]

Panda Internet Security 2010 [free]
Seems that some security companies and software developers are going crazy on the launch day of Microsoft's new operating system Windows 7. Panda Security is the latest security software developer that will […]

Kaspersky Asks For Internet Police And Passports
In an interview with Vivian Yeo of Zdnet Asia, Eugen Kaspersky stated that he would like to change the design of the Internet after being asked what he would change if he […]

Remove Fake Antivirus Software Programs
Fake antivirus software programs, also called rogue security software, are programs that seem to be antivirus programs when in fact they are not. They either are disguised viruses, trojans or try to […]

Microsoft Silently Installing Windows Presentation Foundation Plugin For Firefox
If you have recently opened your Firefox web browser you may have noticed a notification from the web browser that the Windows Presentation Foundation plugin was disabled to protect the user and […]

After Cyborg Beetles We Now Have Sniffer Bees
Next time you visit an airport, there’s a chance of you being sniffed by, not dogs, but bees. Yes, they are now down to training bees to sniff and apparently it is […]

Zonealarm Pro Firewall 2010 Promotion
Update: The promotion is over and there is currently no new promotion that is offering free access to Zonealarm products. Remember last year? Zonealarm ran a promotion in November where users could […]

Leaked Hotmail Password Data Analysis
Remember back then when AOL decided to provide downloads of an anonymized snapshot of search engine log files? One of the first things that Internet Marketers did was analyze the data to […]

Phishing Protection Tips
It is time to update the phishing protection article that we published some time ago (see Phishing explained) with the recent news that thousands of Hotmail users (and apparently Gmail users as […]

Hotmail Phishing Attack: Time To Change Passwords
Microsoft confirmed recently that thousands of Windows Live Hotmail customer's credentials were exposed on a third-party website. According to Neowin, the account information was posted by an anonymous user at the Pastebin […]
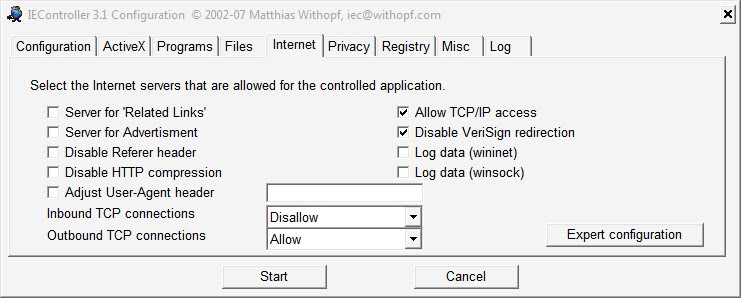
Secure Internet Explorer With IEController
Microsoft's Internet Explorer web browser is tightly integrated into the Windows operating system. This makes it an important software program even if the users of the system do not use it as […]

How To Download Microsoft Security Essentials
Some of you may wonder why I'm writing about the topic again after having published two articles Microsoft Security Essentials Final Announced and Microsoft Security Essentials Final Available about it recently. The […]

Trend Micro RootkitBuster
Most security software programs that are available these days provide protection against rootkits as well. There are on the other hand a few security programs that deal solely with rootkits. One of […]
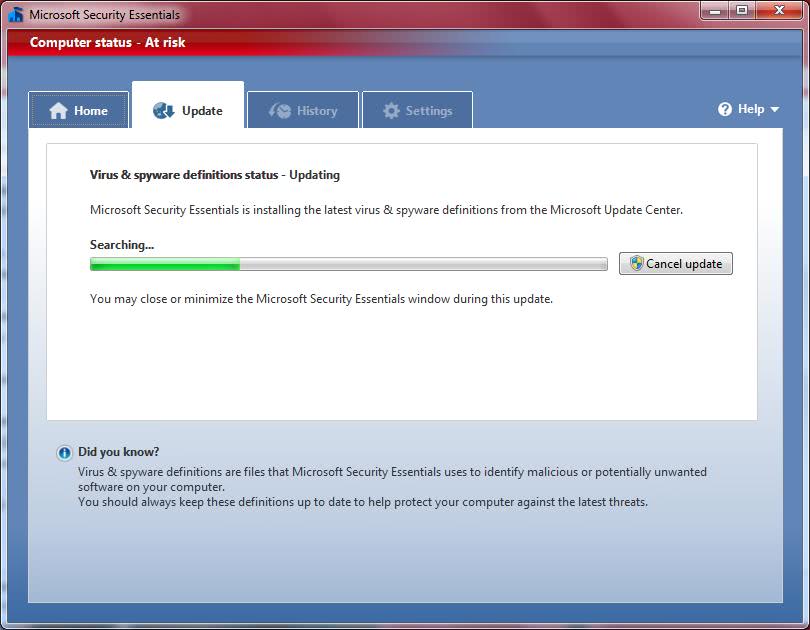
Microsoft Security Essentials Final Available
Microsoft has released the final version of their security software program Microsoft Security Essentials to the public. The software, which the company released to a limited amount of beta testers earlier this […]
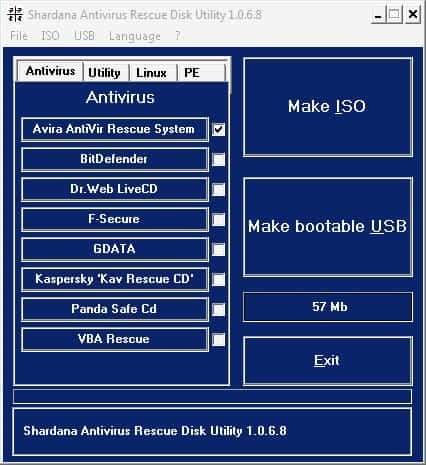
Shardana Antivirus Rescue Disk Utility
Many antivirus developers offer bootable rescue ISO images of their antivirus software programs so that users can use them to scan the computer system without having to boot into the installed operating […]

How To Run Commercial Antivirus Software Without Paying For It
This article is not about illegal methods to obtain software products without paying money for them. But read on if you are interested in how you can protect your computer with the […]

F-Secure Health Check 2.0 Beta Ditches ActiveX
F-Secure Health Check is a web application that can perform a health check of a local Microsoft Windows operating system. A health check is basically divided into three areas of interest that […]
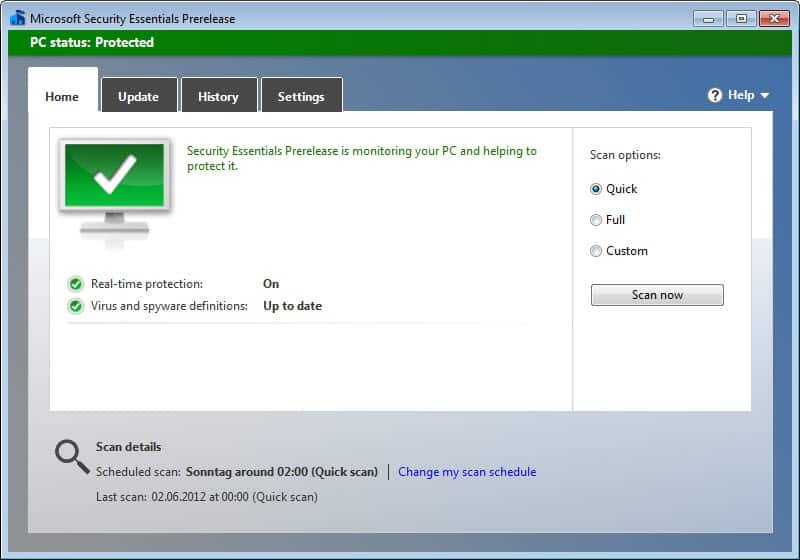
Microsoft Security Essentials - Microsoft Software Program
Microsoft Security Essentials is a free security software that is developed by Microsoft. The security software was released as a limited beta to users in the United States, Brazil and China. It […]

PC Security: Tips To Make Your PC More Secure
A friend recently asked me a bunch of questions about PC security. How dangerous email was, how people could attack a website and so forth. The answers to his questions led to […]
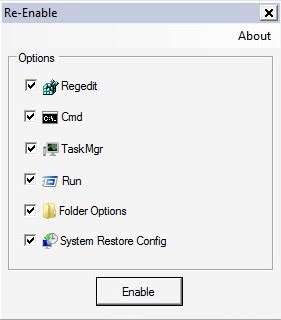
Computer Virus Effect Remover Re-Enable Portable
Malicious attacks on a computer system can sometimes have undesired side effects that make it harder for the computer user to remove the computer virus or malware effectively. This includes a disabled […]

New Security Vulnerability Affects Windows Operating Systems
Microsoft released a security advisory yesterday that describes a new security vulnerability affecting several Microsoft operating systems. The article, which was posted only a few hours after the release of security patches […]

Microsoft Security Patches September 2009
Microsoft has released two charts that show the severity and exploitable index and the deployment priority. The former interesting for all users while the latter probably only for network administrators.

Computer Worm Attacks Not Updated WordPress Blogs
A computer worm is currently in the wild that is attacking unpatched WordPress blogs. Unpatched meaning blogs that have not been updated by their administrators to the latest version of the popular […]
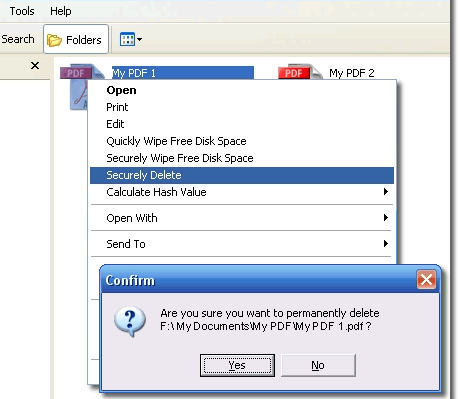
Secure File Deletion and Data Shredding
One of the many misconceptions about file deletion is the fact that files can be recovered even if they are deleted on the computer system by the user. Deleting files normally moves […]

Help the fight against phishing with Phishtank
For anti-phishing tools to work, phishing sites must be recognized, analyzed and then added to a database so that users who use programs that work with the database are warned about it. […]

F-Secure Exploit Shield Protects Against 0-Day Web Browser Exploits
One of the major security threats that computer users face in the past couple of years are web browser exploits. These exploits use 0-day vulnerabilities (and often also older known vulnerabilities) to […]
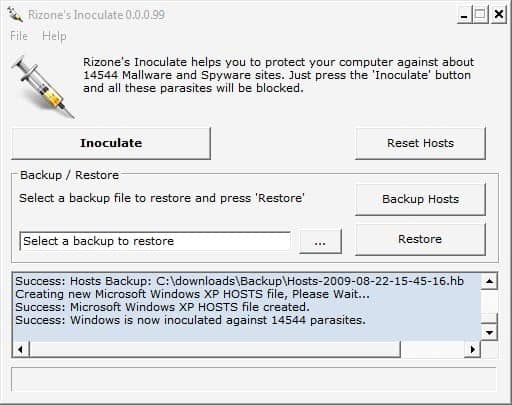
Block Spyware Websites With Inoculate
Many spyware infections happen on specifically prepared websites. These websites might exploit web browser vulnerabilities or offer software and files for download that infect a computer system once they are executed on […]

Microsoft Security Updates August 2009
Microsoft has released its monthly set of security patches yesterday which patch several security vulnerabilities in Microsoft software programs including Microsoft operating systems and Microsoft Office. A summary of the patches can […]

Microsoft Internet Explorer Security Update
Microsoft has released a critical security fix for its Internet Explorer web browsers. The vulnerability, actually its more than one that is patched by the cumulative update, affect most Internet Explorer versions […]

Amazon Deletes a user's Kindle Books Without Consent
If you ever needed another reason not to purchase hardware, software or media with DRM then this latest story may convince you that DRM is utterly bad for consumers in general. Amazon […]

