Computer Virus Effect Remover
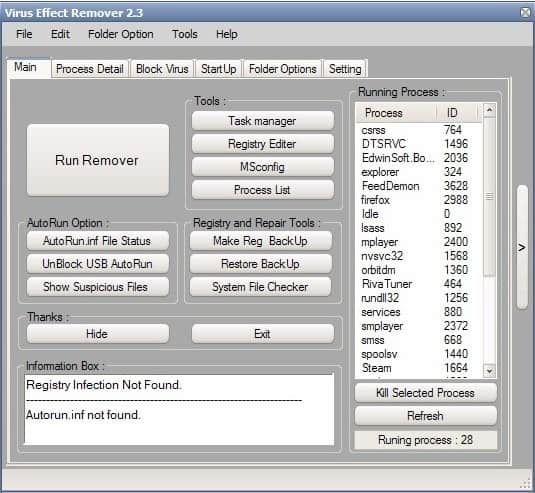
Computer Virus Effect Remover is a helpful software program for the Windows operating system that helps you deal with the aftereffects of an infection with a virus, trojan or other malicious code.
It can be used to remove various changes that malicious programs made on the system. These are often done by malware to make it difficult for the user to remove the malicious program that is running on the system. If you cannot use the Task Manager for example, it becomes difficult to kill the malicious process to stop it.
The Open Source software can aid users in the removal of effects on the Windows file system and the Windows Registry. One of the main features of it is that it can re-enable access to the Windows Task Manager, Registry Editor, MSconfig and the Process List.
Other options include process details that can be used to kill any running process including files that are currently in use by it.
These processes and files can be added to a blacklist so that they will not be executed anymore even if another process attempts to relaunch them right after they have been killed.
The program provides additional options to create or restore a Registry backup, check system files and to repair AutoRun options.
Virus Effect Remover can be a helpful program to remove traces of malicious software.
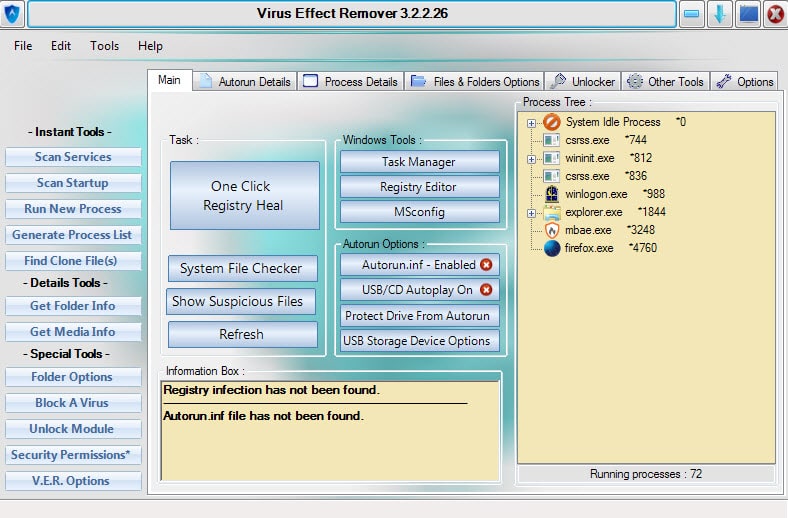
Update: The most recent version of Virus Effect Remover uses a different interface and offers additional functionality on top of what has been mentioned in the review so far.
The interface looks rather messy on first run. You have a bar on the right with access to various tools, and a tabbed interface on the right of it that provides you with access to even more tools.
The tools on the left provide you with direct options. You can use them to scan all startup locations to remove programs from it, to run a new process, get information about files or folders, or to block viruses which allows you to specify files that you don't want executed at any time.
The unlocker is another new tool that you can use to unlock files that you cannot delete or move directly. This is often the case when a file is still in use by a process.
The main issue that you may have with the program is that it is difficult to navigate because it is not immediately clear where you find specific tools. This means that you will have to click through various menus in the beginning to get a feel for the program before you get used to it and start to find tools faster.
With that said, it is an excellent tool that can help you a great deal to recover a system after a successful attack.






















This software really usefull,Download latest,just search google
download 2.6 from
http://sourceforge.net/projects/viruseffectremo/
this will help…
Hi!
Thanks for the Virus Effect Remover. I tried to use it and regards of this, I want to share some errors I encountered as a review for continual development of this Virus Effect Remover.
When I clicked the Task Manager button, an error message appeared saying ERROR OPENING FILE. And I also click the Registry Editor and the same thing happened.
I tried this software because the Task Manager of my computer has been disabled WITHOUT MY NOTICE and the Registry Editor is not accessible. I mean it’s like corrupted software that can’t run!
Please help me regards of this! Thanks…
un virus m,e desbilito el administrador de tareas como hago tego ese virus efecto que esta arriba pero no se utilizarlo ayundenme si
Removes the handcuffs, after it’s up to you to get the place cleaned up. Nice!
Its actually a few batch files/simpel functions of gpedit/registry etc made with a front end
Brian thanks for the information.
I think the best of this is the ability to restore Windows Task Manager and Registry Editor.