Recursively encrypt directories with gpgdir
Recently I wrote an article about Encrypting and decrypting files with GnuPG. This article described how to encrypt single files in with the help of gpg. But what happens if you have a directory full of files? Sure you can tar the directory up and encrypt the files as a single file. But that isn't very practical when you don't want to have to tar and untar a directory all the time. And what if you only want to encrypt certain files within a directory? That is when you need the help of another application.
The application you need is gpgdir. The gpgdir application allows you to recursively encrypt and decrypt directories on your Linux system. It's an easy to use command line tool that can save you a lot of time when you have to do a lot of encryption of files. In this article you will see how to install gpgdir and use it for basic directory encryption/decryption.
Getting and installing
The only drawback is that gpgdir is not installed on your distribution by default, it doesn't come with GnuPG, nor is it included in your repositories. You are going to have to install manually.
If you use an rpm-based distribution you can download the rpm from gpgdir's download page. Once you have that file downloaded you will issue the command:
rpm -ivh gpgdir-XXX.rpm
Where XXX is the release number.
If you are not using an rpm-based distribution you will have to install from source. This is actually quite easy. First download the source file. Once you have that file on your hard drive (let's say it's in ~/Downloads/firefox/) issue the following comands:
cd ~/Downloads/firefox
bunzip2 gpgdir-XXX.tar.bz2
tar -xvf gpgdir-XXX.tar
cd gpgdir-XXX
./install.pl (or sudo ./install.pl)
Where XXX is the release number.
You should now have a working installation of gpgdir.
Using gpgdir
Before you actually run gpgdir you have to have a gpg key generated (The article mentioned at the beginning will describe to you how this is done.) With your gpg key in mind you have to edit a single line in a file before you begin using gpgdir. The file is ~/.gpgdirrc. What you need to do is add your gpg key user name in this file. The line you need to add looks like:
use_key USERNAME
Where USERNAME is your gpg key username (not your Linux system username - although they could be the same). If you're not sure what your gpg key user name is issue the command:
gpg --list-keys
to see the user names of your keys.
Once you have your configuration file edited you are ready to go.
The basic usage of gpgdir is:
gpgdir -e|-d DIRECTORY OPTIONS
Let's create a test directory containing two files. So issue the following commands to create your test environment:
mkdir TEST
echo $USER > TEST/user
data > TEST/data
Now you are ready to see how this works. Let's encrypt the files in our TEST directory.
gpgdir -e TEST
You will be prompted to enter the key's passphrase. Once you do this you will see something like:
[+] Encrypting files in directory: /home/jlwallen/TEST
[+] Building file list...
[+] Encrypting:Â /home/jlwallen/TEST/user
[+] Encrypting:Â /home/jlwallen/TEST/date
[+] Total number of files encrypted: 2
If you look in the TEST directory you will now see the following:
date.gpg
user.gpg
To unencrypt these files issue the following command:
gpgdir -d TEST
You will be prompted for the password again. After gpgdir decrypts the files they will no longer be encrypted.
Excluding files
Say you want to encrypt all files in the TEST directory but the user file. To do this you would issue the command:
gpgdir -e TEST --Exclude user
All files in TEST, except user, will now be encrypted.
Final thoughts
Although you can do more with gpgdir, you now have the fundamental usage of the command.
Advertisement


















I just do directory encryption/decryption like this
Encryption
—————–
#1 Encrypt all files in folder “Dokument” that are not already ecrypted
find Dokument/* -type f ! -iname *.gpg | gpg -e -r myname –multifile
#2 delete the non-encrypted copies
find Dokument/* -type f ! -iname *.gpg -exec rm {} \;
Decryption
———————-
#2 find and decrypt all encrypted files
find Dokument/* -type f -iname *.gpg | gpg -d –multifile
#2 delete the encrypted copies
find Dokument/* -type f -iname *.gpg -exec rm {} \;
/Rascarcapackman
Cool, I was working gpg for an year now…. This is cool tips, let me try this
Ramesh
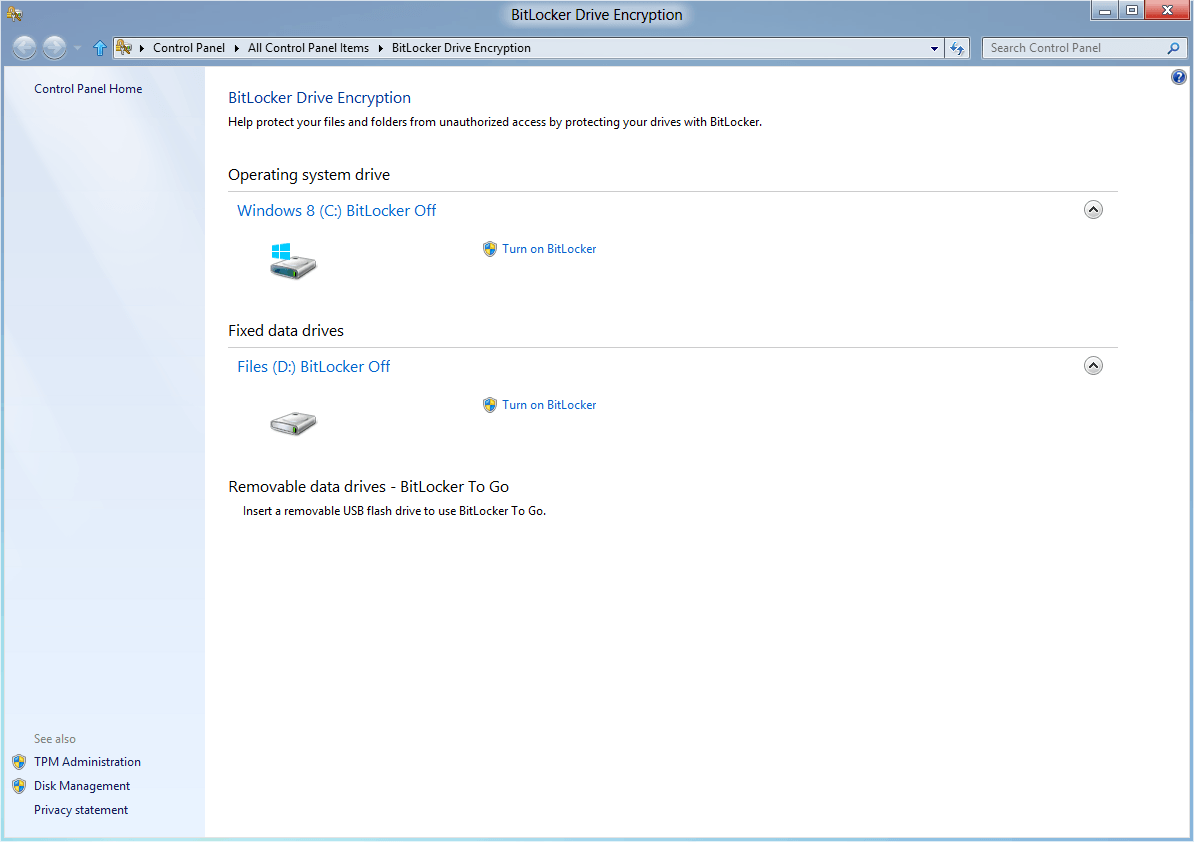
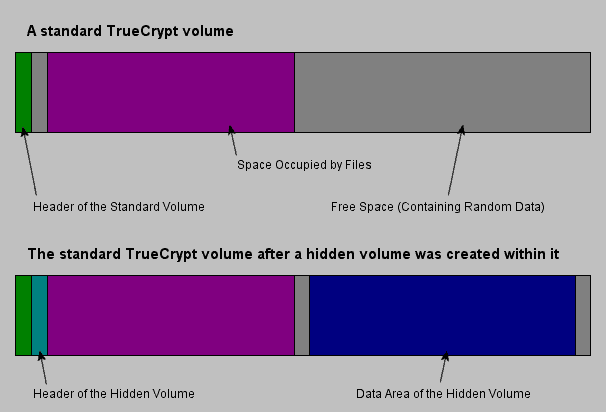
I’m a bit aware of having a file encrypted here, a directory encrypted there, and as many passwords (or not), cumbersome IMO. Either data requires privacy and is stocked in my TrueCrypt safe, either it doesn’t and then I would not bother to get it encrypted in any other way. Just imagining trying to recover an old file encrypted ages ago, with a forgotten password, makes me think twice before closing the flat.