
In a staggering privacy breach, over 21 million images documenting employee activity from a workplace surveillance tool have been leaked. The affected app is called WorkComposer, which is used by IT teams […]

Microsoft Office 2016 and Office 2019 reach end of support on October 14, 2025. That is the last day of support, which means that Microsoft won't release security updates or any other […]

The U.S. Federal Bureau of Investigation (FBI) has issued a nationwide warning about a surge in "smishing" attacks, a form of phishing conducted via SMS messages. These scams are designed to deceive […]
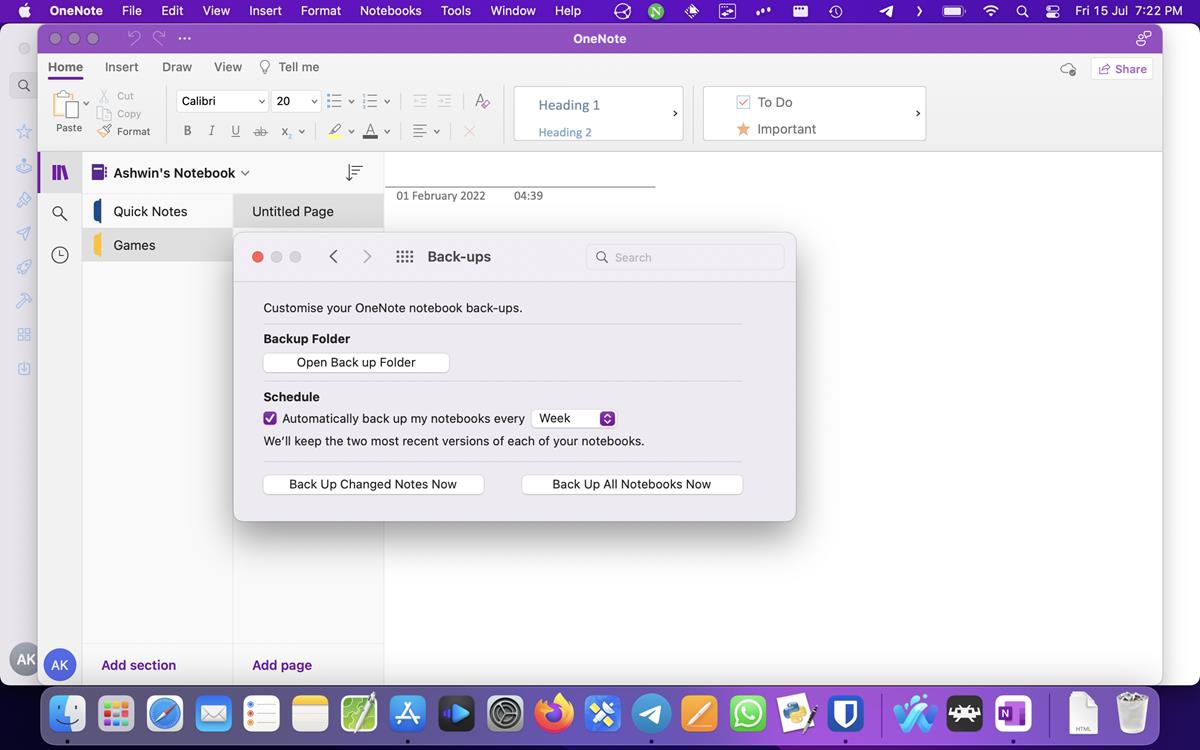
Microsoft has officially announced plans to discontinue support for OneNote for Windows 10, the Universal Windows Platform (UWP) version of its popular note-taking application, in October 2025. This decision is part of […]
If you do use Microsoft Word, you may have noticed the "draft with Copilot" icon that Microsoft added to it. It is displayed whenever you create a new document. Using it, you […]

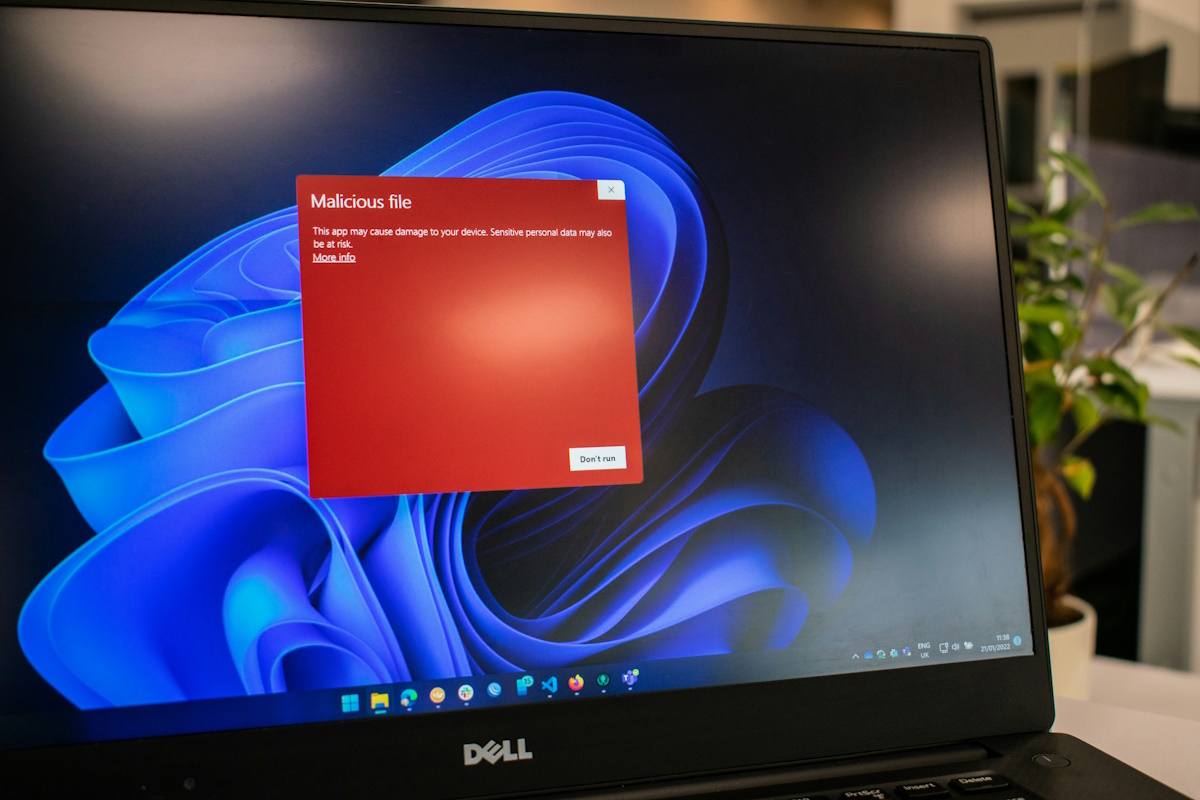
Microsoft is doing a commendable job when it comes to Windows security. Keeping billions of devices secure is no small feat. Sometimes, however, it appears that someone at Microsoft is pushing the […]

Password managers are useful tools. They help users create, store, and manage passwords and other sensitive data. Some offer additional features, like synchronization, two-step authentication, or SSO support. The core functionality remains […]

LibreOffice is a popular open source Office suite that is used by millions of users as an alternative to Microsoft Office. We have followed LibreOffice for almost 15 years here on this […]

OpenAI has expanded access to ChatGPT's Advanced Voice Mode, allowing free users to experience the feature with certain limitations. Previously exclusive to Plus subscribers, this mode enables more natural, real-time conversations by […]

Many PayPal users have seen their fair share of phishing emails ever since they signed up for the service. Being a financial service, PayPal is a high value target for criminal organizations. […]

Microsoft has announced a significant enhancement to its Copilot feature in Excel, enabling users to reference and extract data from Word, PowerPoint, and PDF files within their organizational data. This update aims […]

Lexmark has published several security warnings about recently disclosed vulnerabilities in Lexmark print software and firmware. Patches are provided and customers are asked to update their devices and software immediately to protect […]
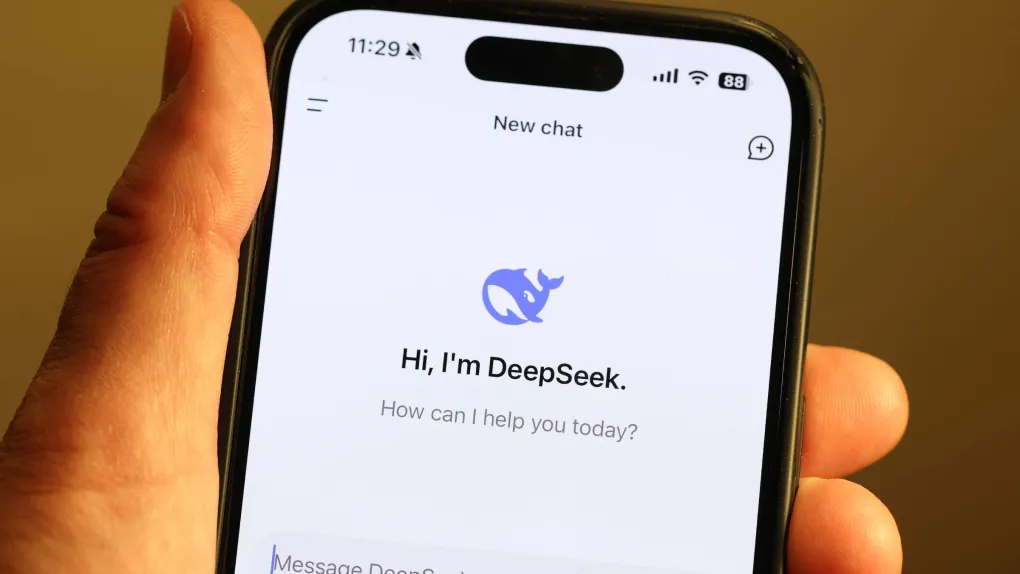
Recent security analyses have revealed that the iOS version of DeepSeek, a widely-used AI chatbot developed by a Chinese company, transmits user data unencrypted to servers controlled by ByteDance. This practice exposes […]

Malicious applications that are uploaded to Google's Play Store or Apple's App Store continue to be a problem for users worldwide. Google said that it blocked more than 2.3 million risky Android […]

One of the largest data leaks in recent history has exposed a staggering 1.5 billion records, affecting major Chinese platforms, financial institutions, and even government-related entities. The unprotected dataset, discovered by Cybernews […]

Microsoft has announced that it will be shutting down the VPN feature in Microsoft Defender for Microsoft 365 Personal and Family subscribers later this month. The decision comes just days after Microsoft […]

A recent study conducted by Searchlight Cyber in collaboration with Marsh McLennan Cyber Risk Intelligence Center has revealed a stark correlation between exposure on the dark web and heightened risks of cybersecurity […]

Bitwarden is a popular open source password management solution that we have mentioned several times in the past. It is one of our recommended password managers. Bitwarden announced recently that it is […]

A pair of hackers, Sam Curry and Shubham Shah, have exposed alarming security vulnerabilities within Subaru’s Starlink-connected infotainment system, enabling them to remotely take control of a Subaru Impreza. The duo gained […]

OpenAI has unveiled "Operator," an advanced AI agent designed for autonomous online task execution, currently available as a research preview for ChatGPT Pro subscribers in the United States. This innovative tool represents […]

December 2024 saw an unprecedented surge in ransomware attacks, registering 574 incidents—the highest monthly total recorded since 2021. This spike came as shocking news, particularly as December typically experiences a decline in […]

In a significant security alert, cybersecurity firm CloudSek has unveiled a sophisticated phishing campaign linked to the Lumma Stealer malware, targeting Windows users. This approach leverages deceptive human verification pages that mimic […]
Perplexity, the AI conversational search engine, is making a significant leap into the mobile arena with the integration of Perplexity Assistant in its free Android app. This new feature enables users to […]

Microsoft is implementing a significant change to its account authentication system starting February 2025. Under the new system, users stay signed in across sessions unless they sign out explicitly. To better understand […]

The first update of 2025 for the open source encryption software VeraCrypt is now available. VeraCrypt 1.26.18 is a security update that is also introducing a number of fixes and other changes, […]

Bitwarden is an open source password management solution that we have mentioned and recommended several times here on this site in the past. The developers have released the first major update of […]

Security experts at iVerify have developed a solution to detect traces of the spyware Pegasus on mobile devices. Pegasus is marketed as a solution to fight terrorism and crime, but governments all […]

For decades, tape storage has formed the backbone of data archiving, finding its application in financial records, compliance, large-scale backup, and much more. Tapes proved to be a reliable, cost-effective solution for […]

OpenAI has released the official ChatGPT app for Windows for all users. The company had released the desktop app for macOS in June 2024, before following it up with a Windows version […]

Weak passwords continue to be a problem on today's Internet. It seems that many users continue to pick weak passwords that were weak 20 years ago and continue to be the weakest […]

VMware Workstation and VMware Fusion are now free for all users. Didn't Broadcom make them free already in March 2024? Yes, the products had been transitioned to a free for personal use […]

The Internet Archive has been hacked. The data breach has resulted in the theft of credentials of 31 million users. Good to know: The Internet Archive is a non-profit organization that aims […]

Adobe announced new Adobe Elements 2025 Family releases this week. The two products, Adobe Photoshop Elements 2025 and Adobe Premiere Elements 2025, come with "Ai magic" according to Adobe and several other […]
Microsoft released a new non-subscription version of Microsoft Office for home users and businesses. This one differs from the subscription-based Microsoft 365 version of Office in several meaningful ways. The following paragraphs […]
Kaspersky users in the US have discovered that their antivirus has been replaced by UltraAV. That doesn't seem like it would do wonders for a company's PR image. For those unaware, the […]
Tor is an important service on the Internet when it comes to anonymity. It is free and can be used by anyone to hide information such as a device's public IP address. […]
Microsoft Exchange Servers play an important role in corporate communications. They are also not immune from issues such as accidental or intentional mailbox deletions, which can lead to a significant amount of […]

One of the most important advices when it comes to the security of electronic devices is to make sure that they are up to date. A security researcher discovered a new attack […]

Malicious actors have managed to steal more than 33 million phone numbers used by users of the two-factor authentication service Authy. Authy is a popular security application to manage authentication codes for […]
The United States are banning Kaspersky products. Starting July 20, Kaspersky is no longer allowed to sell its products to new customers. Software updates remain available until September 29, 2024. Customers who […]