Toshiba Self-Encrypting Hard Drives With Host Authorization
The best way to protect data on one of your storage devices is to encrypt it. There are several free solutions out there, for instance by using the Open Source encryption software True Crypt, to protect data from unauthorized access.
While it is not a problem for tech savvy users like you and me to encrypt a disk drive with encryption software, it may very well be one for normal computer users.
But even with encryption there is the chance that third parties may find ways to access the data on the hard drive, for instance by brute forcing the password or placing a trojan or other malicious code on a system.
Toshiba recently announced a new generation of self-encrypting drives with several advanced features that offer more than hardware data encryption.
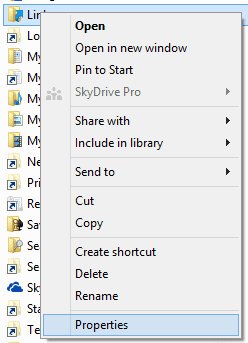
The drives can be configured to only work on known host systems. Any attempt to connect them to an unknown host would automatically render the data on the drives useless.
The drives have been specifically designed to "address the increasing need for IT departments to comply with privacy laws and regulations governing data security" and are "ideally suited for PC, copier and multi-function printer, and point of sale systems used in government, financial, medial or similar environments".
Drives can be configured to deny access or erase sensitive data if the authentication process fails. This would for instance be the case if someone connected the hard drive to an unauthorized computer system.
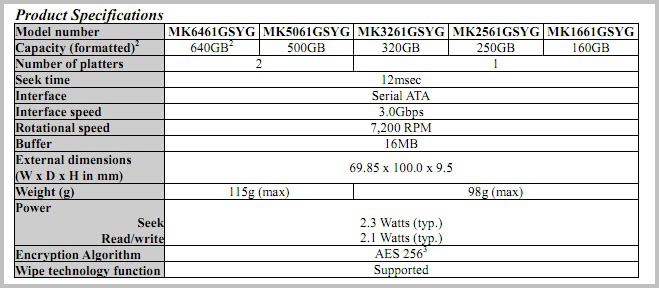
The hard drives will be offered with capacities between 160 Gigabytes and 640 Gigabytes, 7200 RPM, 16 Megabyte buffer and a Serial ATA 3,0 Gbps interface. All drives use the AES 256 encryption algorithm to protect data from unauthorized access.
The drives will be made available in the coming months, and will be first made available to OEMs and ISVs. The press release is available here.
Advertisement




















Annoy the hell out of your colleague: grab his disk and plug it into any non-autorized computer…. :)
Not SSD, only 16mb cache, and only SATA 3GB/s.
Yuck! No thanks.
Yes that’s right. SSD are in the workings.