Microsoft: Windows 10 hardening against 0-day exploits
One key focus of Microsoft when it comes to promoting the company's latest operating system Windows 10 is to hammer home that Windows 10 is better for security.
The company published a blog post recently on the Microsoft Malware Protection Center blog which exemplified that by analyzing how Windows 10 handled two 0-day exploits, or better, how it protected customer systems from those exploits.
The two 0-day exploits in question are CVE-2016-7255 and CVE-2016-7256, both patched by Microsoft on the November 2016 Patch Tuesday.
CVE-2016-7255, patched by MS16-135, was used in October 2016 in a spear-phishing campaign against a "small number of think tanks and nongovernmental organizations in the United States". The attack used an exploit in Adobe Flash Player, CVE-2016-7855, to gain access to target computers, and then the kernel exploit to gain elevated privileges.
The attack group used the Flash exploit to take advantage of a use-after-free vulnerability and access targeted computers. They then leveraged the type-confusion vulnerability in win32k.sys (CVE-2016-7255) to gain elevated privileges.
CVE-2016-7256, patched by MS16-132, started to appear on the radar in June 2016 as it was used in "low-volume attacks primarily focused on targets in South Korea". A successful attack exploited a flaw in the Windows font library to elevate privileges, and to install a backdoor on target systems called Hankray.
Microsoft's technical blog post goes into great length describing both exploits.
The take away however is that Windows 10 systems that were running the Anniversary Update, were protected against both attacks even prior to being patched by Microsoft's security updates.
In the case of CVE-2016-7255, the exploit was ineffective on devices running the most recent version of Windows 10 because of extra anti-exploit techniques introduced in the Anniversary Update. This caused the attack to be ineffective against those systems, and the worst that happened was the throwing of exceptions and blue screen errors.
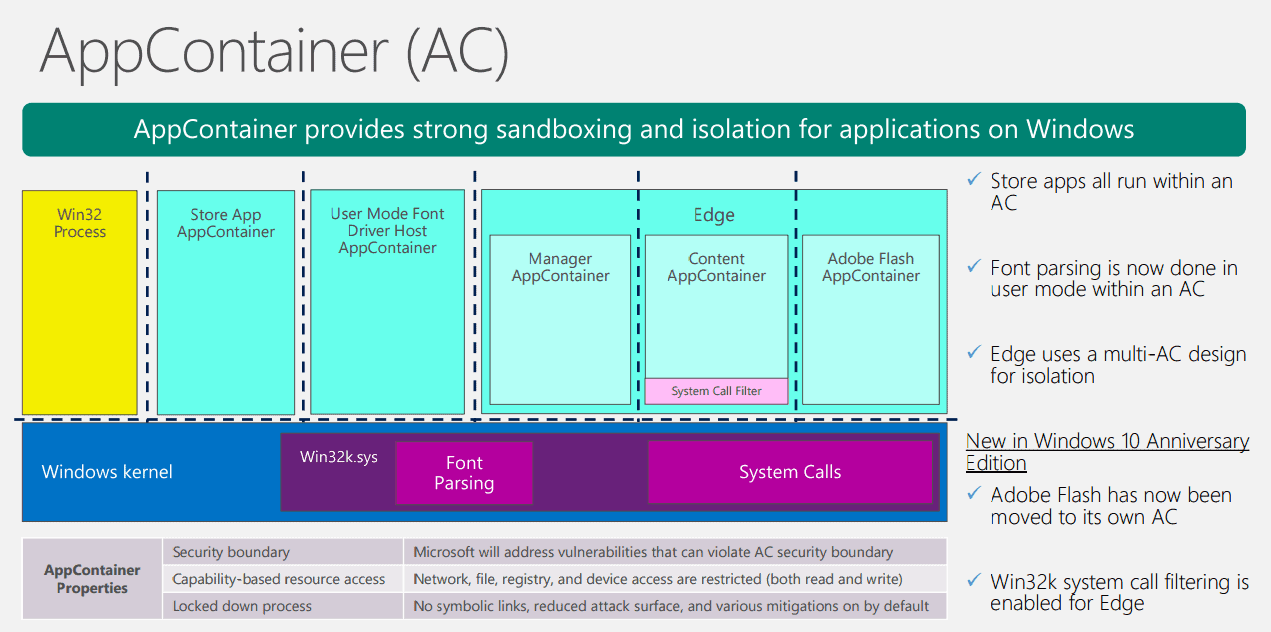
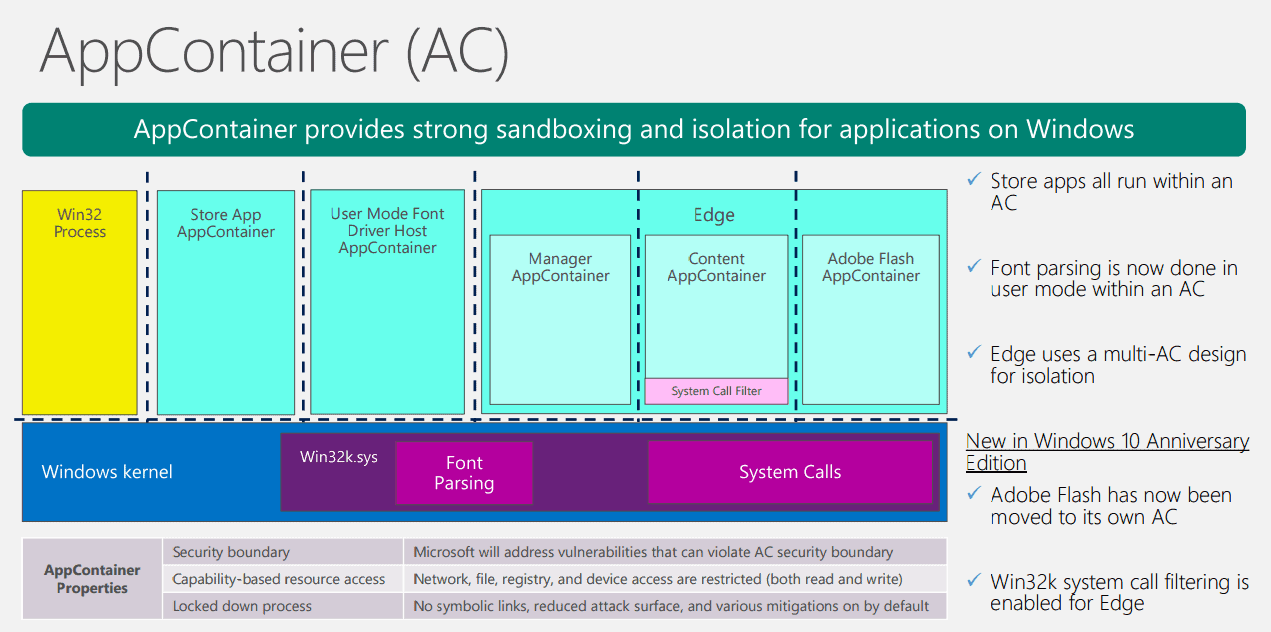
For CVE-2016-7256, AppContainer isolation and additional font parsing validation methods prevented the exploit to work at all on a device running Windows 10 with the Anniversary Update installed.
We saw how exploit mitigation techniques in Windows 10 Anniversary Update, which was released months before these zero-day attacks, managed to neutralize not only the specific exploits but also their exploit methods. As a result, these mitigation techniques are significantly reducing attack surfaces that would have been available to future zero-day exploits.
It needs to be noted that at least one of the exploits, CVE-2016-7256, targets Windows 8 systems and not Windows 10.
Microsoft plans to make further security enhancements to Windows 10 in the coming Creators Update.



















I see it positive, more patches not only means that there were possible holes in the past, it shows they are now faster in fixing stuff which is good (in a security aspect). On the other side they really need to review their own patches to get less problems.
Since the launch of Windows 10 the OS has more security fixes each month than any other older version of Windows.
Which is not that bad after all: https://www.bleepingcomputer.com/news/security/android-was-2016s-most-vulnerable-product/
Good, that means they’re finding them/made aware of them and fixing them.
Also bad, that means they may start getting an edge on security BECAUSE privacy is terrible. In that case, they are exploiting the awfully detailed user data they forcefully grab to improve security. The edge they could get as a result means that…competitors will increase privacy invasion as well.
That’s what happened with behavioral advertising. It works better at converting people into clients so when Google started it, everyone followed.
That gives them too much power and IMO makes them more of a threat than drive-by exploits, which can be reasonably secured without destroying any sense of private space.
better late than never