Microsoft Security Updates July 2010
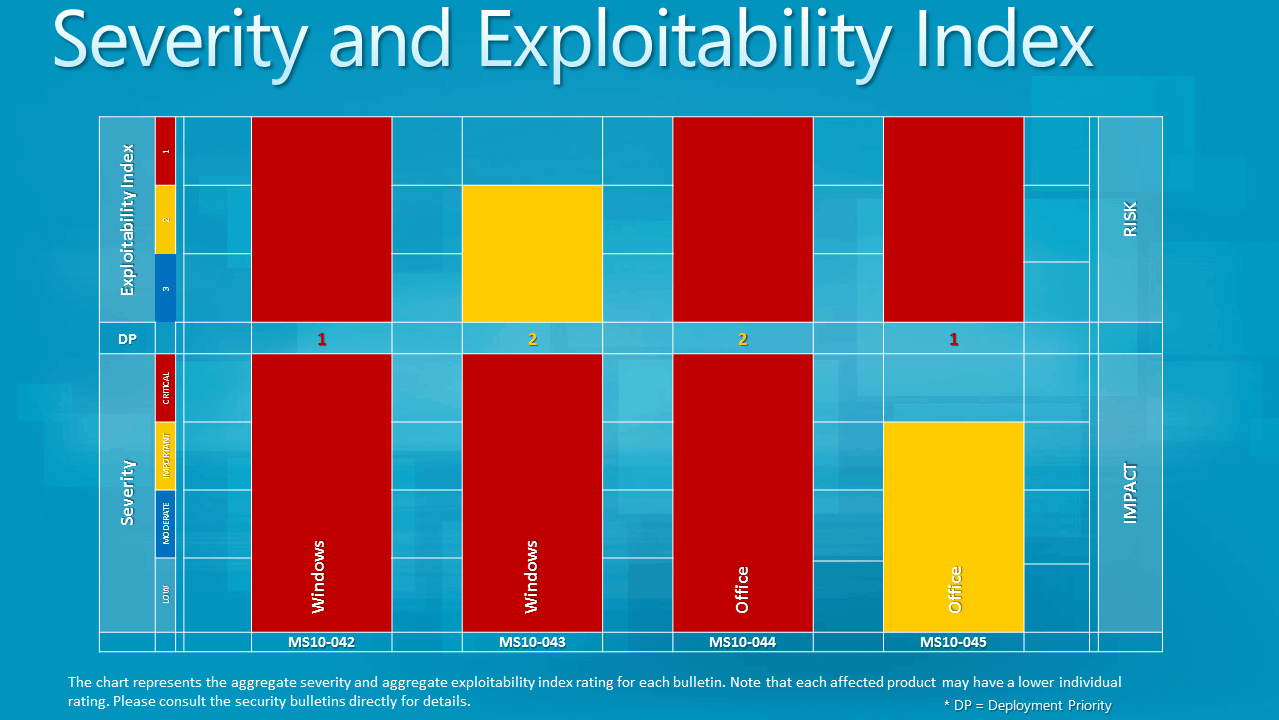
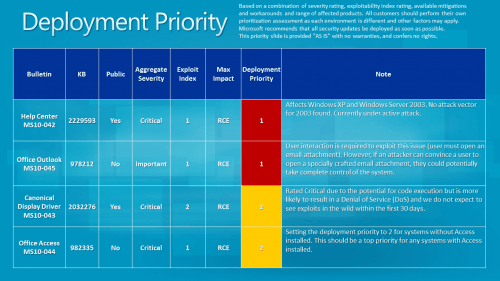
Microsoft has just released four security bulletins on this months' Patch Tuesday fixing vulnerabilities in Microsoft software products. Three of the four bulletins have a maximum severity rating of critical, the highest rated, while one is rated as important.
Affected software includes several Microsoft operating systems and Microsoft Office, take a look at the listing below for additional details on every security bulletin released today.
- Microsoft Security Bulletin MS10-042 - Critical
Vulnerability in Help and Support Center Could Allow Remote Code Execution (2229593) - This security update resolves a publicly disclosed vulnerability in the Windows Help and Support Center feature that is delivered with supported editions of Windows XP and Windows Server 2003. This vulnerability could allow remote code execution if a user views a specially crafted Web page using a Web browser or clicks a specially crafted link in an e-mail message. The vulnerability cannot be exploited automatically through e-mail. For an attack to be successful, a user must click a link listed within an e-mail message. - Microsoft Security Bulletin MS10-043 - Critical
Vulnerability in Canonical Display Driver Could Allow Remote Code Execution (2032276) - This security update resolves a publicly disclosed vulnerability in the Canonical Display Driver (cdd.dll). Although it is possible that the vulnerability could allow code execution, successful code execution is unlikely due to memory randomization. In most scenarios, it is much more likely that an attacker who successfully exploited this vulnerability could cause the affected system to stop responding and automatically restart. - Microsoft Security Bulletin MS10-044 - Critical
Vulnerabilities in Microsoft Office Access ActiveX Controls Could Allow Remote Code Execution - This security update resolves two privately reported vulnerabilities in Microsoft Office Access ActiveX Controls. The vulnerabilities could allow remote code execution if a user opened a specially crafted Office file or viewed a Web page that instantiated Access ActiveX controls. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights. - Microsoft Security Bulletin MS10-045 - Important
Vulnerability in Microsoft Office Outlook Could Allow Remote Code Execution (978212) - This security update resolves a privately reported vulnerability. The vulnerability could allow remote code execution if a user opened an attachment in a specially crafted e-mail message using an affected version of Microsoft Office Outlook. An attacker who successfully exploited this vulnerability could gain the same user rights as the local user. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights
Affected software:
- MS10-042 - Windows XP, Windows XP Pro 64-bit, Windows Server 2003, Windows Server 2003 64-bit
- MS10-043 - Windows 7 for x64-based Systems, Windows Server 2008 R2 for x64-based Systems
- MS10-044 - Microsoft Office 2003 , Microsoft Office 2007
- MS10-045 - Microsoft Office XP, Microsoft Office 2003, Microsoft Office 2007
All vulnerabilities allow remote code execution on compromised systems. Additional information about this months' patches are available at the Technet blog post.
Advertisement



















This information has been released by Microsoft.
http://blogs.technet.com/b/msrc/archive/2010/07/13/july-2010-security-bulletin-release.aspx
And I have linked to it.
Almost everyone is recommending to install the updates, especially if the vulnerabilities are sever and exploitable… Now the question, did anyone of you readers ever become a victim (loose data or have any other problem) from something that could have been avoided if the system were updated???
Somehow I have the feeling that it’s a waste of time to update the operating system all the time…
Crodol, you should always update. The change to become a victim depends on several factors, especially if an exploit is in the wild and how it is targeting computer systems. The worst case is an automated large scale attack. There is obviously a chance that you will never get hit even if you do not update, but then again, I would not want to take that chance.
Hoi Martin thanks a lot for this fairy extensive and greatly helpful explanation of this month MS updates. What i really like are the pictures you implemented, ferry handy that i can open them in a new tab.
You are welcome Paulus ;)