Web Fingerprinting Gets Frighteningly Good: Sees Through VPNs and Incognito Mode

Web fingerprinting is not a new technique to identify visitors on the Internet, but it is a technique that has become frighteningly good in recent time.
Fingerprinting describes a set of methods that sites and advertisers use to track users across the Internet. These methods do not rely on cookies and other common forms of tracking, which mostly rely on storing data on user devices, but use device parameters and other information to compute a fingerprint.
It should not come as a surprise that some browsers, mostly those focused on privacy, have implemented anti-fingerprinting protections in recent years. Brave Browser introduced language and font fingerprinting protections in 2022, and Mozilla's Firefox web browser anti-fingerprinting protections as part of the browser's Tracking Protection feature.
While some web browser makers have upgraded defenses to protect against fingerprinting, developers of fingerprinting solutions have also made advancements. Take Fingerprint as an example; the web service promises that its commercial solution has a 99.5% accuracy. In other words: it can identify 995 out of 1000 returning visitors correctly, even if these visitors clear browsing data, use a VPN connection or switch to private browsing modes.
The company advertises it as a solution against fraud, account takeovers and spam, and it can very well be used for that.
Local tests done in several web browsers confirmed the accuracy. The website identified three visits using Firefox, Firefox with private browsing mode and Firefox with private browsing mode and a VPN connection, as coming from the same user.
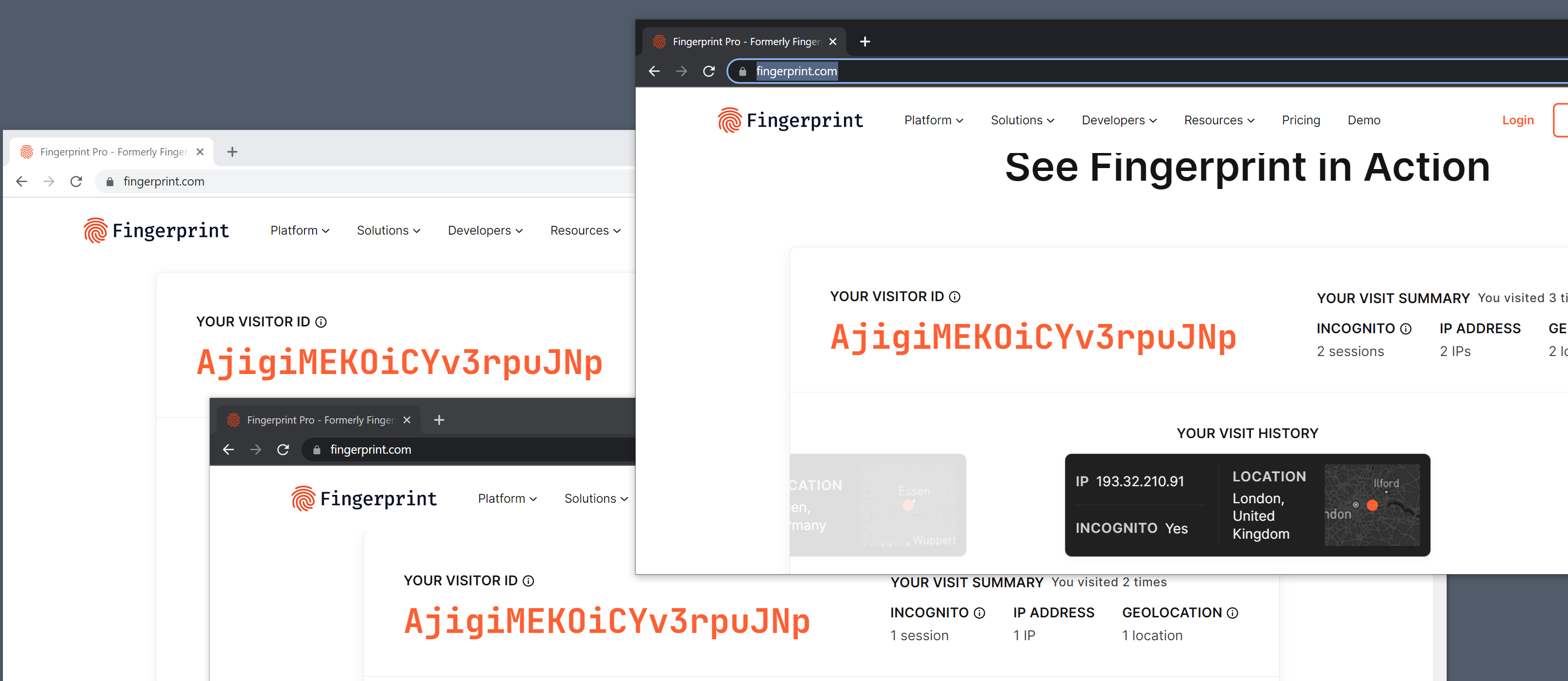
Similarly, it identified the same user correctly in Brave, Google Chrome and Microsoft Edge. The only browser that it could not detect correctly was Tor Browser. Firefox users who have enabled fingerprinting protection in the browser manually are also not identified as a single user by the site's script.
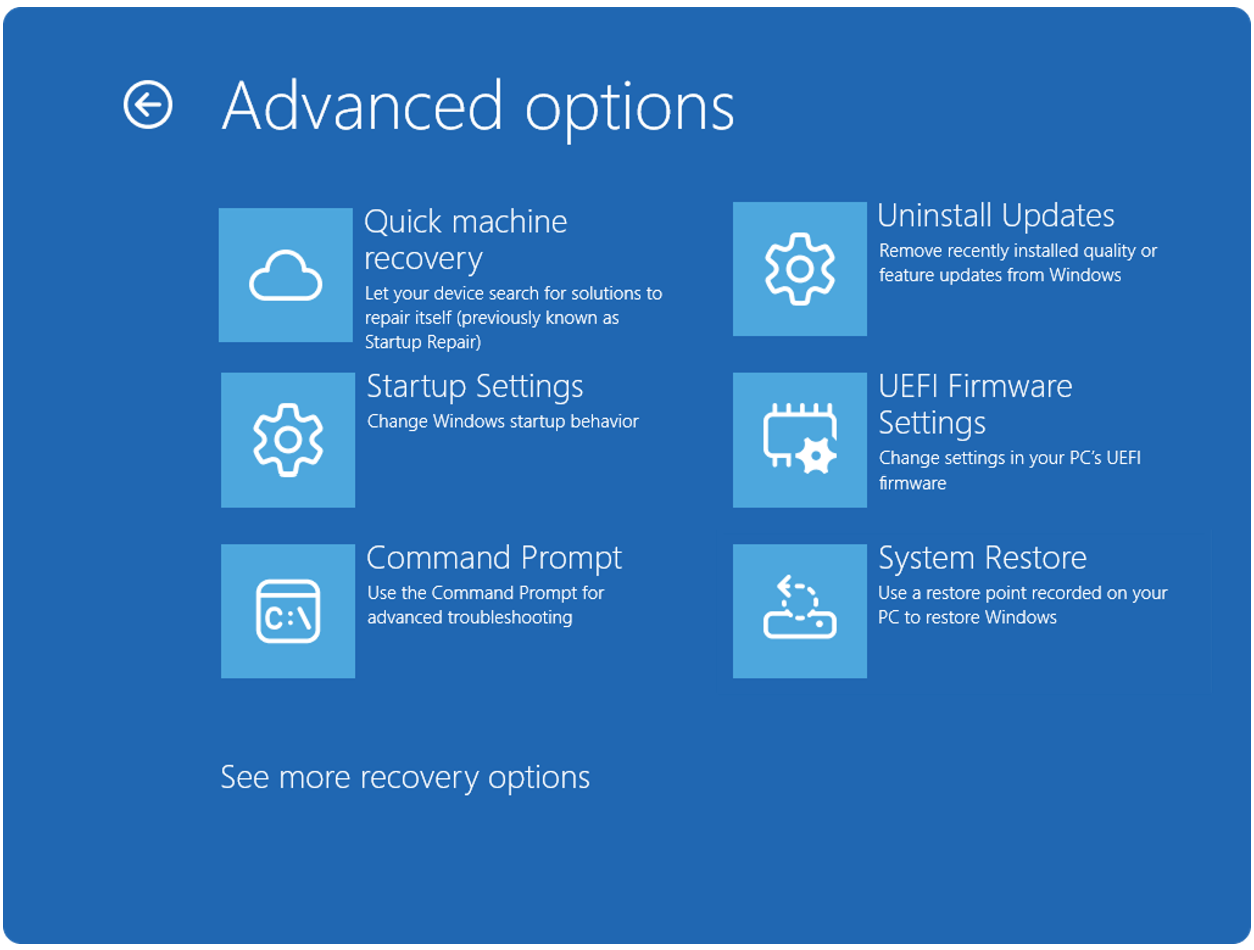
It is necessary to set the preference privacy.resistFingerprinting to TRUE on about:config. Please note that doing so may result in some usability issues when using the browser.
The script did not connect visits across different web browsers, only when the same browser was used.
Fingerprint offers an open source version of the script, which is less accurate, as it lacks some advanced features, and a commercial script, which uses machine learning and additional techniques to improve the accuracy significantly.
How to protect against fingerprinting
Internet users have two main options when it comes to protections against fingerprinting-based tracking. Either use a browser with proper protections against these types of tracking, Tor Browser or Firefox with privacy.resistFingerprinting set to TRUE are two valid options, or use different web browsers for different tasks.
Extensions that block the execution of scripts on websites may also protect against fingerprinting. Browser users may check out NoScript for that, which may be configured to block scripts by default. The popular uBlock Origin extension may also be configured to block all JavaScript by default.
Now You: do you use protection against fingerprinting? (via Bitestring)

















“Web Fingerprinting Gets Frighteningly Good: Sees Through VPNs and Incognito Mode”
“The website identified three visits using Firefox, Firefox with private browsing mode and Firefox with private browsing mode and a VPN connection, as coming from the same user.”
A VPN only hides the IP address and private browsing mode is not either supposed to do anything against fingerprinting (because Firefox’s anti-fingerprinting which is part of tracking protection, which blocks some fingerprinting scripts, is already enabled when not in private browsing mode, while the more advanced privacy.resistFingerprinting that does like Tor Browser by trying to look average is not enabled either by default nor in private browsing).
So the actual information is rather that this default anti-fingerprinting protection in Firefox is defeated.
By the way, Mozilla has made the deliberate choice of not blocking many fingerprinting scripts with their default tool as long as they’re considered not to be there for tracking, as defined by them. As long as the site claims that taking our fingerprint is only to protect them from fraud or denial of service attacks for example, it won’t be blocked.
And considering the way Firefox’s default anti-fingerprinting works, by blocking requests, it’s not better for that than what a nuisance blocker like ublock origin does. uBO may have the same limitations regarding allowed fingerprinting but this time not deliberately, considering that it does not have the same power as Google and Mozilla to choose to block this practice unilaterally so as to enforce that policy on sites. However uBO can’t be expected to have unethical limitations that it is responsible for, like for every other nuisance category that it blocks better than Firefox, so it can be expected to be superior. Google’s billions invested in Mozilla have also been proved not to make Firefox’s default tracking protection better than ublock origin’s one with its zero budget, and in fact inferior. Which reminds that this is all not only about having lots of resources, but also about ethical use of those.
Blocking JavaScript is not a solution, it’s a problem. It will break way too many things, it’s not practical at all.
Fingerprints no more…
brave://flags > fingerprinting
Enable dark mode blocking fingerprinting protection – Enabled
Enable navigator.connection attribute – Disabled
Block screen fingerprinting – Enabled
After closing my browser each time, FP Pro reports 1 visit with different
visitor ID each time
And no effect on logging into my banking webpage.
Hmmm…what does this mean for torrents?
It’s not about the cookies anymore. Hundreds of Id points are collected like how you hold the device and the combination of gpu/cpu/etc that has been seen on a network of sites before.. if you are able to complete a purchase at a major retailer, chances are high you are IDd across multiple sites.
“Firefox users who have enabled fingerprinting protection in the browser manually are also not identified as a single user by the site’s script”
Firefox wins again….That’s why I always use it. It’s the best privacy browser.
It’s interesting that “privacy.resistFingerprinting” defaults to False, but “privacy.trackingprotection.fingerprinting.enabled” to True, since they sound pretty similar.
I found using Firefox with the extension “CanvasBlocker” (default settings) prevented fingerprinting with this fingerprint web service
Thanks. I’ll give it a try. I’m sick of being fingered so much.
Quoting the article,
> […] the web service promises that its commercial solution has a 99.5% accuracy.
I presume, given the link, that the web service is [fingerprint.com]
Demo/test page : [https://fingerprint.com/demo/]
Cookies are not blocked (set to block only 3rd-party), but that parameter is superfluous given the use of the ‘Cookie Autodelete’ extension mentioned hereafter).
The visitorID which appears on that page is NOT, in my case, fixed :
– If I reload the page, visitorID remains the same (of course);
– If I exit the site, reopen it (without having cleaned FF’ cache), the visitorID has changed.
I’m using Cookie Autodelete, Canvasblocker, Privacy Possum, ETag Stoppa Firefox extensions. All 4 are required to escape the visitorID’s relevance (not sure for Privacy Possum given Etag Stoppa may be enough).
Looks like having a configured device correctly set enables it to be among the happy few 0.05%
Let advertisers and their fingerprint obsession go to hell.
I’ve been using different browsers for different tasks for years.
When your accessing your bank, you want to be fingerprinted and tracked. When your accessing your porn, not so much ;)
Understanding that a browser sends 20 or 25 pieces of data to a website, if what their sw does is catalog points of data that a browser sends, what if a single or several variabales are changed, something simple like a using a user-agent switcher, screen size or VPN location change?
More corporate product hype: Promise everything, deliver nothing.
i do not think you understand what this is. it is more like a couple of thousand pieces of data, in well under a second (you wouldn’t even know) – a user agent switcher will not save you and only makes you paradoxical to your detriment