Firefox 72 may block fingerprinters by default
Firefox 72, an upcoming version of the web browser, may block so-called fingerprinters by default. Mozilla started to integrate and push Tracking Protection in the Firefox web browser in 2019. Designed to reduce tracking on the Internet, Tracking Protection blocks known trackers (e.g. social media trackers), cross-site tracking cookies, and other tracking related or undesirable content.
Standard tracking protection functionality is enabled in Firefox by default. Users of the web browser may adjust the protective feature by setting it to strict or custom. Strict and custom, the two other available presets, include protection against fingerprinters already.
Starting in Firefox 72, Firefox may block fingerprinters by default as well as part of the standard preset.
Mozilla added the blocking of fingerprinters to Firefox 72 Nightly and plans to test the integration. Based on the outcome of the test, fingerprinting protection may become a standard blocking feature in Firefox 72 Stable or be reverted.
Compatibility issues play a big part in the assessment of the feature. Some, legitimate, sites may break or functionality on legitimate sites may break, if fingerprinting is enabled. If the breakage is too severe, Mozilla may revert the decision.
Fingerprinting refers to methods that use data that is provided by the browser or user activity for tracking. All web browser reveal some information when sites are loaded. Information may include the user's location in the world, language settings, screen resolution, and other data. Sites may run scripts to gather more data. The main idea behind the data gathering is to generate a fingerprint based on the data to identify the user when the same or other sites are visited.
Mozilla explains the concept on its wiki website:
Fingerprinting is used to identify a user or user agent by the set of properties of the browser, the device, or the network, rather than by setting state on the device. For example, a party which infers the set of fonts a user has installed on their device and collects this information alongside other device information would be considered to participate in browser fingerprinting.
Tip: check out our master list of privacy tests that you may run to find out what your browser reveals about you.
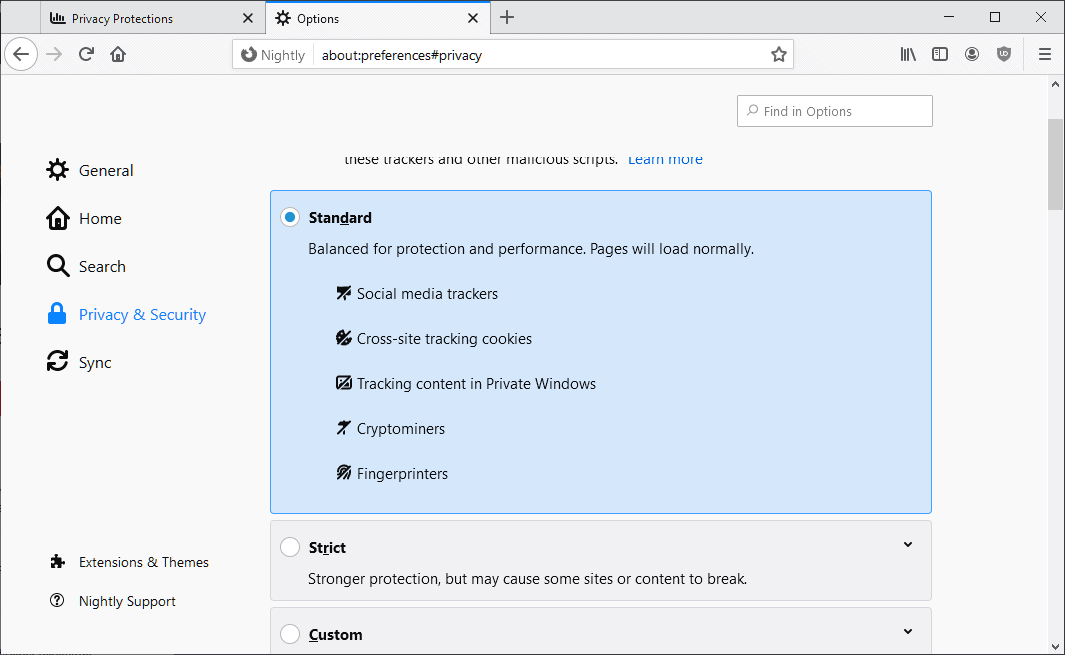
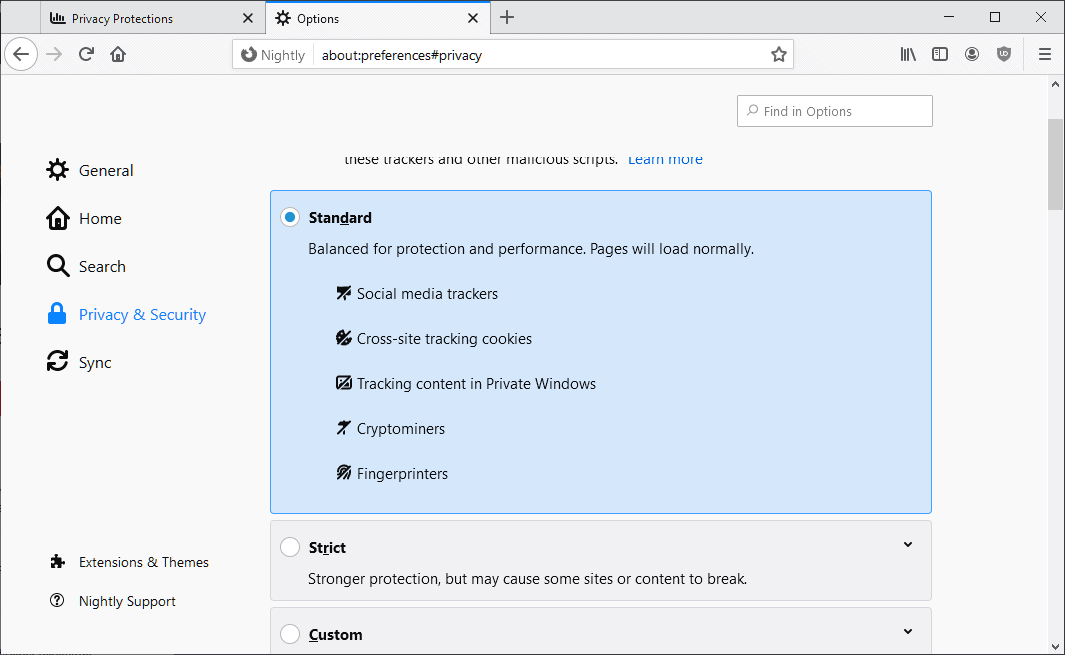
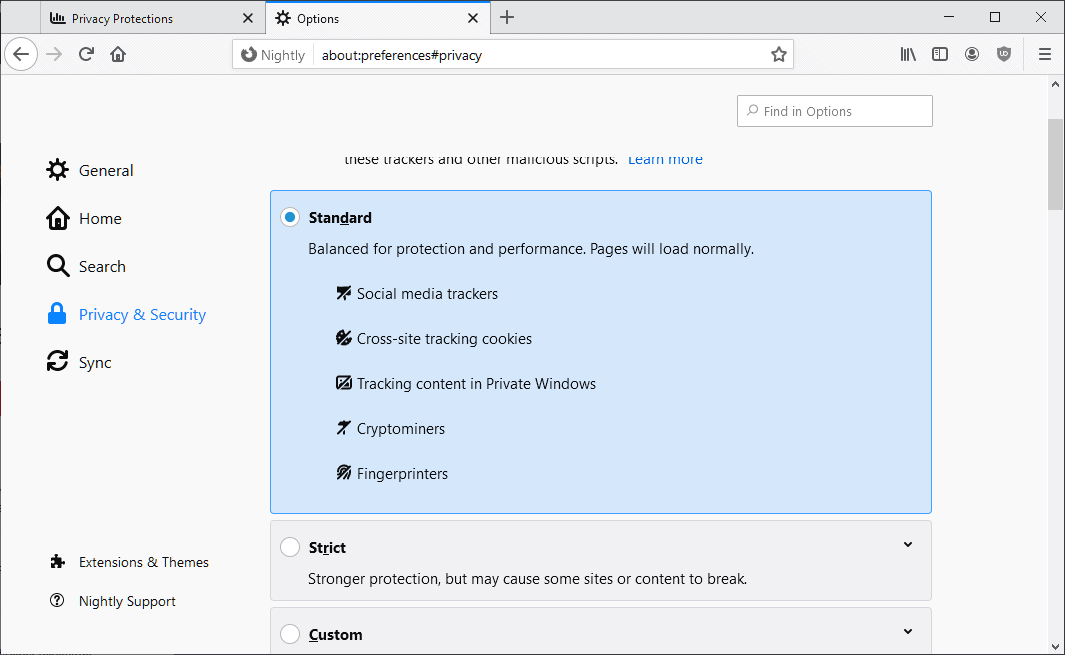
Firefox users may control the browser's tracking protection feature in the following way:
- Load about:preferences#privacy in the browser's address bar.
- Switch between standard, strict and custom enhanced tracking protection levels. Custom allows users to configure protective features individually.
Firefox 72 is scheduled to be released on January 7, 2020.
Closing Words
Fingerprinting protection is a welcome addition to Firefox's arsenal of tracking protections. Users can enable the protection already in Firefox 70 Stable, e.g. by switching to custom protections and enabling the option.
Now You: What would you like to see next added to Firefox's Tracking Protection feature? (via Techdows)





















> What would you like to see next added to Firefox’s Tracking Protection feature?
Simple: bundle Ublock Origin like LibreWolf instead of this shameful half baked content blocker with “acceptable ads” betrayal, planned user tracking, and deliberately lame blocking abilities (no cosmetic filtering, no scriptlets, no ability to add non Mozilla filter lists, and so on). Or at least use more decent filter lists. And stop disabling adblockers by default in private browsing like Google Chrome, Mozpricks.
LibreWolf,
It seems to be Firefox’s new fork browser that has just been developed recently.
The platform is the latest “Firefox release”.
It is developed and supported through the open source project hosting site “GitLabâ€.
LibreWolf Browser | A fork of Firefox, focused on privacy, security and freedom.
https://librewolf-community.gitlab.io/
LibreWolf Browser | Docs
https://librewolf-community.gitlab.io/docs/
The following is a reprint from the official homepage:
This project is an independent fork of Firefox, with the primary goals of privacy security and user freedom. It is the community run successor to LibreFox
LibreWolf uses more than 500 privacy/security/performance settings, patches, LibreWolf-Addons (optional) and is designed to minimize data collection and telemetry as much as possible (updater, crashreporter and Firefox’s integrated addons that don’t respect privacy are removed).
LibreWolf is NOT associated with Mozilla or its products.
Features
â— Latest Version of Firefox: LibreWolf is compiled directly from the latest build of Firefox Stable. You will have the the latest features, and security updates.
â— Completely Independent Build: LibreWolf uses a completely independent build from Firefox and has its own settings, profile folder and installation path. As a result, it can be installed alongside Firefox or any other browser.
â— Extensions firewall: limit internet access for extensions.
â— IJWY (I Just Want You To Shut Up): embedded server links and other calling home functions are removed. In other words, zero unauthorized or background connections by default.
â— User settings updates: gHacks/pyllyukko base is kept up to date.
â— Settings protection: important settings are enforced/locked within librewolf.cfg and policies.json, those settings cannot be changed by addons/updates/LibreWolf itself or unwanted/accidental manipulation; To change those settings you can easily do it by editing librewolf.cfg and policies.json.
â— LibreWolf-addons: set of optional LibreWolf extensions
â— Statistics disabled: telemetry and similar functions are disabled
â— Tested settings: settings are performance aware
â— Multi-platform (Windows/Linux/Mac/and soon Android)
â— Dark theme (classic and advanced)
â— Recommended and code reviewed addons list
â— Community-Driven
◠And much more…
Roadmap
See https://gitlab.com/librewolf-community/librewolf/issues
It’s childsplay to enable an extension.
Are you really that triggered anon???
BTW, no one uses LibreWolf (I’ve never even heard of it), LOL.
How do you know that no one uses LibreWolf, when you haven’t heard of it? Now you have heard of it.
There are worldwide browser marketshare statistics from multiple sources, none list LibreWolf.
LibreWolf is not even listed, because no one uses it.
I haven’t heard of you and you don’t exist? It is a strange conclusion.
for the privacy conciseness, i personally recommend disabling fingerprint, tracking and cryptomining protection in Firefox and using the much more comprehensive uBlock Origin add-on along with the appropriate filter lists
That’s what I do as well, perhaps motivated more by efficiency (and lack of redundancy) than by privacy awareness. Whatever, Firefox’s built-in privacy & security settings remain a better than nothing first base for users who run the browser out of the box, I guess… and I think they are a majority.
‘uBlock Origin’ (“Origin”, not pale copies) is definitely the first extension to add to Firefox.
You can use both Firefox’s privacy protections AND uBlock Origin.
We don’t live in the 1980’s, computers can easily handle running both.