LastPass suffers another data breach, says customer data was stolen
LastPass has been breached for a second time this year. The cloud-based password manager suffered a data breach in August 2022, which resulted in some source code and proprietary technical information being stolen.
LastPass suffers another data breach
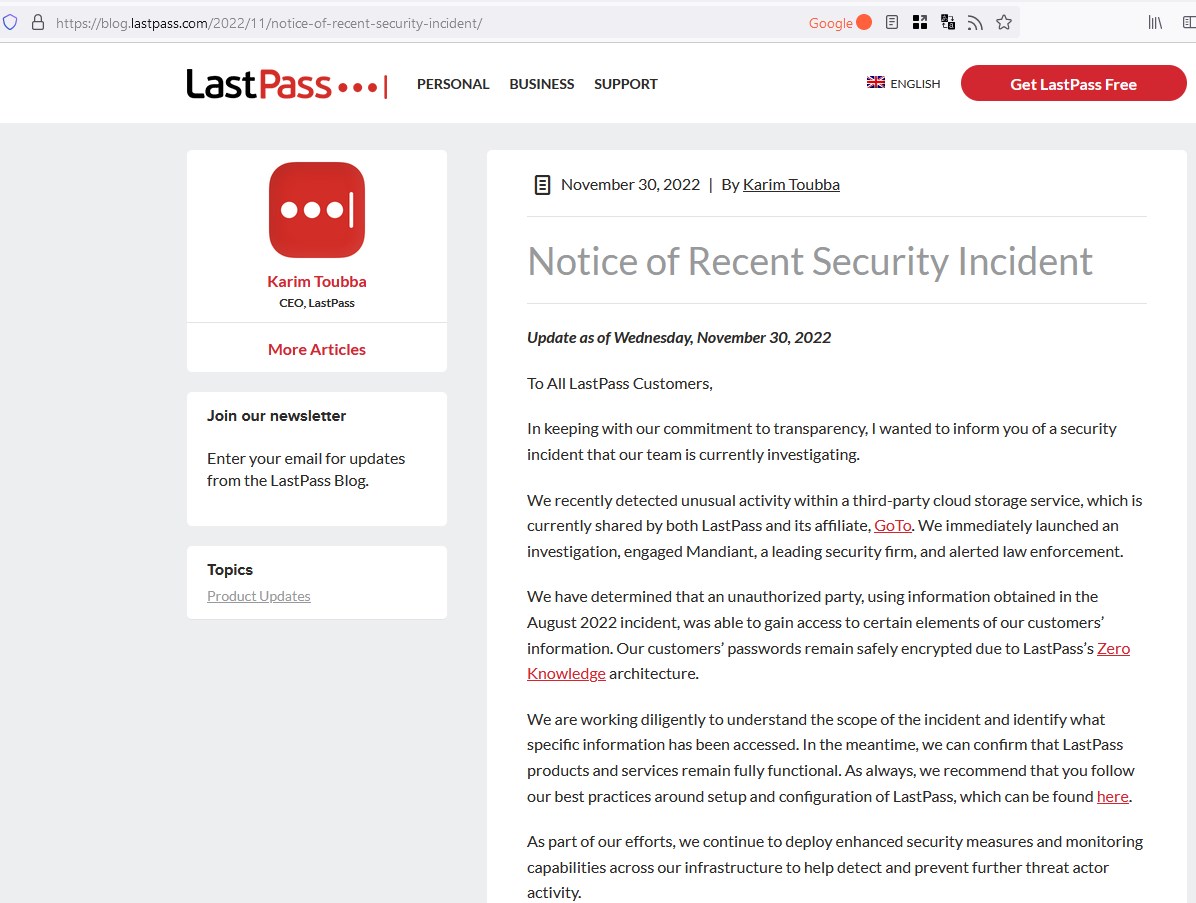
Karim Toubba, the CEO of LastPass has published a notice on the company's blog to inform users about the security incident. The article says that LastPass recently detected some unusual activity within a third-party cloud storage service that it uses. This storage server is shared between LastPass and GoTo (formerly known as LogMeIn).
Once it noticed the security breach, LastPass alerted law enforcement about it. The company also began an investigation of its own, again in partnership with a security firm called Mandiant to discover the origin of the attack, and trace its scope. Its investigation has led the company to believe that the new security incident is directly related to the August 2022 data breach. To recall the incident, hackers had gained access to LastPass' development environment for 4 days. But the forensic report published by the password manager service had claimed that no user data had been stolen during that attack.
This time, however, LastPass mentions that the threat actors exploited the information from the previous hack to gain access to some elements of LastPass' customer data. But the company says that the hackers did not steal the passwords of its users, because of LastPass' Zero Knowledge, i.e. the technology that it employs to encrypt user data. The service does not store its decryption keys on its servers, these are saved on the end user's device, the vault is end-to-end encrypted. Since LastPass itself does not have access to the encryption key, this likely means that the contents of the password vault are safe.
If that is the case, and I'm purely speculating here, if the passwords are safe, what else could the hackers have stolen? The only other data that LastPass could have has got to be related to customer's personal information which is related to their subscription details, e.g. stuff that you would find on an invoice. I'd still advise users to keep an eye on their mail inbox to check if any unauthorized login attempts have been made, it's the logical thing to do.
LastPass has not disclosed further details about the breach. It is still investigating the scope of the incident to determine what user data was accessed. We can expect another update from the company that explains more about the hack, and how it affects users.
Meanwhile, Toubba has confirmed that the company's services are fully functional. He also reassured LastPass users that they are monitoring the situation to detect and prevent further malicious activity by the hackers.
Security incidents like these are the reason why some people prefer to use offline password managers like KeePass, because the only person who has access to your vault is you. You can't blame them for that, though one could argue that any website and service is open to attacks, it is the strength and quality of the security protocols that they use that actually matters. That said, if you have enabled 2-factor authentication for the accounts that you have stored in the cloud-based password manager, you should be relatively safe from attacks.
Do you use LastPass?

















LastPass is a very big target. Bitwarden might be targetted too in the future. As long as hackers can’t find the backdoor these companies provide to western intelligence, general users should be safe.
Chrome, has a nice password keeper, even reminds you when etc. data maybe stolen..
Why to trust those third – party tools ? …
“which resulted in some source code and proprietary technical information being stolen”
It’s not free software ? What a pity.
Bitwarden if you need an easy-to-use cloud-based solution, KeePass (regular or XC) for probably-more-secure self-hosted.
LastPass was best-in-class for a while, but not these days. There are plenty of free open-source solutions.
I have no sympathy for anyone who continues to use these terrible cloud services.
Sticky Password has a feature that allows the user to sync (passwords and all other information kept inside the vault) between devices only using local WiFi.
When activated, synchronization can be made over your local WiFi — your data never leaves your devices. You control the devices and the network your data is synced over.
For LastPass users:
It would be highly recommended
that, after Login,
LastPass would show:
– date/time of most recent previous login
– IP, country,… etc.
This would immediately alert
the LP user.
LP, are you listening?…
===============
Storing one’s passwords somewhere in the cloud has always been an inherently unwise decision. And in spite of the assurances of any cloud-based password managers, this will never be a really safe way to handle passwords. I myself use KeePass with its encrypted locally-stored database file, and have always felt more happy with that.
Can anyone give recommendations for alternative to Lastpas? Tried some, but nothing works as well as lastpass does.
The best alternative is to remember passwords in your memory.
If a service is breached, you are compromised. If a service is down, you can’t log in, because you don’t remember your password.
If you remember your passwords, the two scenarios above don’t apply to you.
@Chris
I already gave one half an hour before your post.
@web
@semce
I also gave an alternative to self host.
I migrated from LastPass to Bitwarden a couple years ago and I am very happy with Bitwarden.
Others just come close or surpasses them in other ways, like bitwarden but have their own host of disadvantages.
You are trading security for convenience, just by using this kind of services
Useless shameless garbage.
Garbage
Especially when you can self-host your own password manager instance like:
[https://github.com/dani-garcia/vaultwarden]
Is there anyone sane anymore who trusts “the cloud” in the float year 2022.91781