Tor Browser 8.0.9 update resolves add-on signing issue
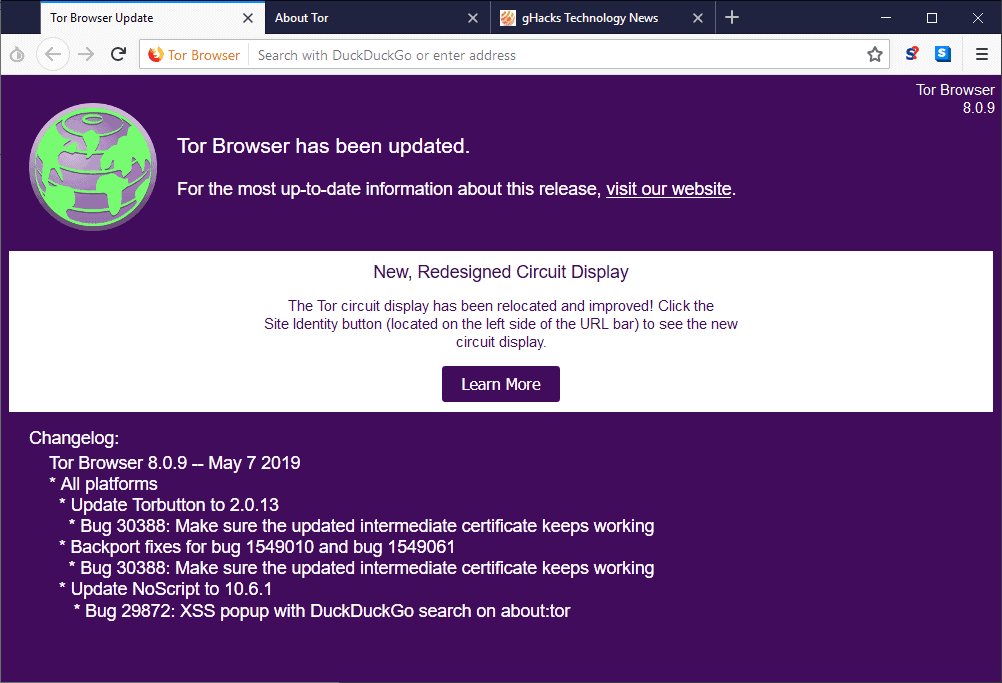
Tor Browser 8.0.9 was released on May 7, 2019 to the public. The new version addresses a major issue in Mozilla's add-on signing platform that caused verification to fail.
Tor Browser is based on Firefox ESR code, and since Firefox ESR, and any other version of Firefox, was affected by the issue, so was Tor Browser.
The privacy-focused browser comes with several add-ons installed that improve privacy. One notable extension is NoScript as it blocks all (or most) JavaScript from execution. Scripts may serve legitimate purposes, e.g. provide functionality on websites, but they may also be used for fingerprinting, tracking, the serving of advertisement, and even malicious attacks or the distribution of malware.
The Tor project informed users of the browser about the issue on its website
Tor users found the add-ons NoScript, HTTPS Everywhere, Torbutton, and TorLauncher disabled, and marked as legacy extensions. The same happened to Firefox users worldwide who all lost access to their installed extensions.
Mozilla fixed the issue in the meantime in Firefox (including Firefox ESR), and Tor Browser 8.0.9 does the same. Means, add-ons should show up as installed again after Tor Browser is updated to the new version or installed anew.
Note: The Brave browser supports Tor as well; it was not affected by the issue.
Tor Browser 8.0.9
Tor users and admins can download the latest version of the web browser from the official project website. It is available for the desktop operating systems Windows, Mac OS and Linux, and the mobile operating system Android.
You may run an update check by opening Menu > Help > About Tor Browser.
Tor users who use the built-in extensions or others are encouraged to update to the new version to fix the issue. Add-ons should return to the enabled state automatically after the update.
The entire changelog:
Update Torbutton to 2.0.13
Bug 30388: Make sure the updated intermediate certificate keeps working
Backport fixes for bug 1549010 and bug 1549061 *
Bug 30388: Make sure the updated intermediate certificate keeps working *
Update NoScript to 10.6.1
Bug 29872: XSS popup with DuckDuckGo search on about:tor
Tor users who disabled add-on signing in the browser to fix the issue temporarily may want to consider enabling it again. This is done by loading about:config in the browser's address bar, searching for xpinstall.signatures.required and setting the preference to True.
True means that Firefox will verify the certificate of installed extensions and extensions that are about to be installed in the browser. Extensions without valid certificate cannot be installed or used if the setting is enabled (with some exceptions, e.g. temporary add-ons). (via Born)














Seems to work!
I still haven’t found a fix that works for a portable install of Tor Browser 7.5.6 I was keeping on hand for a small number legacy extensions. (I know it’s potentially insecure to install additional extensions in Tor Browser, and to use older versions of Tor Browser itself, but when the primary concern is to evade interference from my ISP, I figure a less-than-perfect Tor Browser is good enough. I don’t need it often enough to warrant paying for a VPN.)
I too like to keep my privacy with my ISP. As I’m sure you know, in the USA they can now collect and sell our traffic data and such (old news).. The Privacy Statement from my ISP says they still don’t sell my data, but they likely still collect it. And they can always legitimately sell our data later, with a simple change to their Privacy Statement.. And they keep data going back many years.
So, you use an old version of Tor Browser with legacy FF add-ons? Hmm. I guess that’s okay, as long as you run it in a VM, in a sandbox, on a dedicated PC, with a dedicated router. Hmm.
Have you considered the Basilisk browser?
It supports several legacy FF add-ons, such as DTA. It’s “experimental” but it’s updated with a large user base.
I use Basilisk in a VM, in a sandbox, with the free VPN service from Proton VPN.
I don’t do torrents, but Proton works good for me with DDLs and streaming.
The free Proton VPN service uses these servers:
2 servers in USA that use TOR.
2 servers in the Netherlands that support P2P traffic.
3 servers in Japan.
They sometimes temporarily add more servers, but not often. Most servers average around 80% load, thus with slower speeds.
All the user traffic is often using up much of the bandwidth, but it still works fine for me, by jumping to less used servers as need be.
Proton VPN also has a VPN Kill Switch, and DNS Leak Protection.
Beyond that, as you may know, Cloudflare is planning to provide a free VPN for desktops as well.
Also, for just browsing the web, VPN Gate works okay and is free. But I find most of the connections are too slow for streaming video and such.
For those that back up the .mozilla directory be aware that Firefox 67.0 beta 9 will upgrade this directory to a NEW format, and once you have updated the new version of Firefox your old .mozilla directory back up can no longer be used – it will fail to restore. You will have to make a new back up of this directory after upgrading Firefox, which can be restored with the newer versions. Mozilla is pushing for you to use Sync to do this – to be honest if I wanted to use Sync then I would just use Chrome.
Time to move TBB to Chromium, I think. The mozilla ship is sinking ;)
The NSA had a big enough window to gather lots of information while users were unaware that the Tor Browser security was crippled. Nice!
I guess if the giant red full screen width banner was ignored.
Well, the update worked.
I’m still calling bullshit,
FF on Android was affected as well, temporarily, and the problem vanished with no update to the app.
I’m also still on FF 66.0.3 on the dessktop and all my extensions are working fine.
(With studies disabled) and (After doing a refresh and reinstalling all my extensions)
What exactly is in this update they claim i need?
is it to…
#!/bin/bash ?
I love firefox and waterfox, palemoon and liked the now terminated cyberfox…
Firefox = choice – where not many others do ?
If you can call chromium derivatives choice, then I may have eat humble pie…
This should always come with the disclaimer that Brave’s developer himself said that users should rely on Tor Browser for real anonymity. Brave’s support also says:
Browsing with tor isn’t secure with Chromium or most other apps. In the distant future, it is hoped to make it more modulable but right now it has to be used through Tor Browser, although the step towards a Tor+Firefox combo is already more than half made.
Browsing with Tor is not secure with Brave either. Tor is all about being well hid in a crowd, the relays. Tor inside a real VPN is quite secure but not completely.
Let the Firefox bashing begin again…..
Poor snowflake Firefox. Saying a program is bad, and a company not be be trusted, is “bashing”. You should not “bash”, and you should not “hate”.
I mean, you should not “bash” things, or people that “anti-bashers” like. It’s perfectly right to “bash” things they don’t like. Such as Firefox competitors. Or people not liking Firefox. Or Mozilla.
That’s the right sort of hate. That’s not “hating”. It’s just stating what’s right and good. Hate haters don’t hate. They are just morally superior to you. Like Firefox fanboys, Firefox devs and Mozilla employees.
Those are your masters, and you should defer to them.
@Clairvaux Indeed.
I was a FF user since it was pre-version 1.0 and had a different name. But even I saw the writing on the wall years ago and had to jump ship.
Since then, Mozilla has just driven FF deeper into the ground, while taking a dump on the small percentage of users that continue to stick with them and yet people like ‘Bobby Phoenix’ thinks that it is “Firefox bashing” to point out that Mozilla royally fucked up (again) and this time, even left security conscious users affected with the TOR Browser!
Isn’t the snowflake the person who suddenly feels morally inferior because he was told he’s acting like an ass ?
@ Sup
If you read my comment correctly, you will see it’s a thing I called a snowflake, not a person. That thing is a software program called Firefox.
Yes, it is absurd, but I was only drawing the obvious conclusion from an absurd (and trollish) comment, in order to demonstrate its absurdity.
As for your own statement, it’s wrong, irrelevant and offensive to the millions of users who have been trapped by Mozilla in that trainwreck of epic proportions.
“Tor users found the add-ons NoScript, HTTPS Everywhere, Torbutton, and TorLauncher disabled, and marked as legacy extensions.”
Not HTTPS Eerywhere for me, if memory serves right. Only No Script was affected. I did not see any other warning.
What are Tor Button and Tor Launcher ?
Still can’t believe how such a important certificate was allowed to expired which broke so many extensions in Tor and Firefox. You have to figure some sort of notifications of expiration were provided. Has to be some person or group that would keep track of this. Some of Mozilla’s responses early seem clueless about what was happening. They seemed surprised as any of the users. Which makes this a even problematic issue, because they clearly had no knowledge of this expiring certificate. It did convince me to be done with Firefox and I uninstalled it from all my PC’s.