A look at community-powered VPN Penguin Proxy
Penguin Proxy is a community-powered VPN solution for Windows, Mac OS X and Linux, as well as several web browsers, that is free currently.
The service is in beta at the time and the company behind the service plans to charge users a yearly fee for usage once it leaves beta. Whether a free but limited version remains is unclear.
One core difference between Penguin Proxy and commercial VPN solutions such as NordVPN or Private Internet Access, or the free Tor option, is that Penguin Proxy utilizes the bandwidth of connected users and that of its own server network for connectivity purposes.
The default bandwidth contribution per day is set to a limit of 500 MB; users of Penguin Proxy can reduce that to 100 MB or increase it to 2 GB or unlimited. Users who contributed more get faster speeds out of the service according to the service's FAQ.
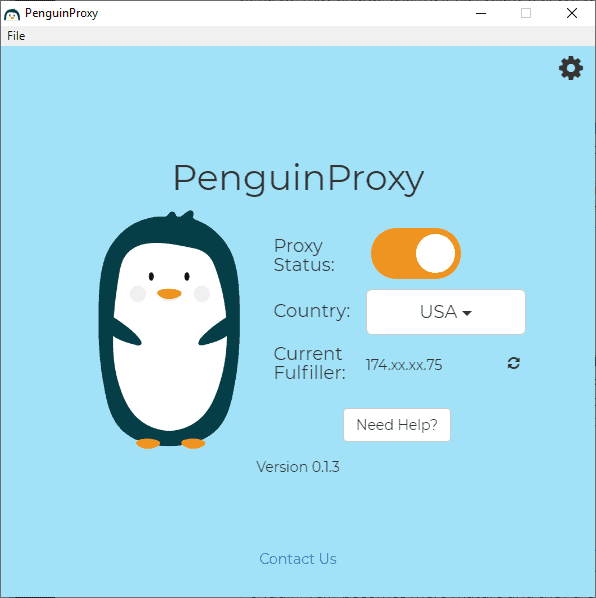
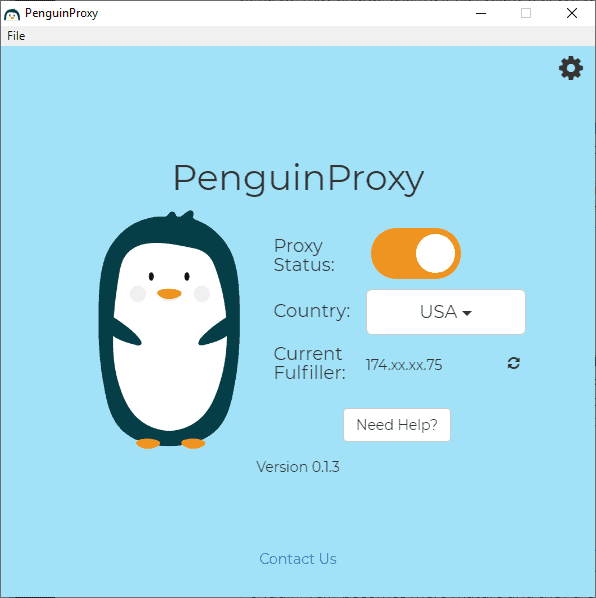
Penguin Proxy is simple to use; just download the application to the local system and run it. The Windows version displays a simple connection dialog on start.
It features a country or region selector, and displays part of the IP address of the VPN server/fulfiller. Penguin Proxy supports a handful of regions only: USA, United Kingdom, Europe, Canada, or China.
A click on the preferences icon displays connection related settings. Users find options to load the proxy on startup, disable the built-in ad-blocking functionality, or enable proxy connections on HTTPS connections only.
Options to add exceptions, reverse the exceptions (to whitelist), enable the use of random IPs on every connect, and to limit bandwidth that is contributed to other users of Penguin Proxy are provided as well.
Penguin Proxy works as expected; users can download and install desktop programs or browser extensions if they prefer to limit functionality to individual browsers.
The connection speed depends on a number of factors. It was not as good compared to non-VPN connection speeds or connections using other VPN services.
Is Penguin Proxy secure and private?
The company behind Penguin Proxy promises that it will never include advertisement in Penguin Proxy or sell user data.
Anonymous logs are kept for 2 weeks during beta phase for debugging purposes but will be disabled "as Penguin Proxy becomes more mature".
Connections are encrypted but they may be forwarded through other users of the service; these devices, at the very least, know the originating IP and the target IP address of the request.
Penguin Proxy INC., the company that operates the proxy service, states in the FAQ that users of its service should handle the connection as it if would be a public Wi-Fi Hotspot connection; in other words: not very secure by default. Tor is recommended by the company for connections that require the highest security.
Should you use Penguin Proxy?
Penguin Proxy may be attractive to users because it is free to use. The free nature of the service has some disadvantages; you pay with your IP address and bandwidth, and that may lead to a number of issues such as misuse that most users may want to avoid.
Paid VPN service subscriptions start at next to nothing, e.g. a lifetime subscription starts at about $15 on Ghacks Deals. Nord VPN or Private Internet Access subscriptions are available for $3 or $2 per month for a 2-year subscription plan.
There is also some uncertainty when it comes to Penguin Proxy. While the company states that connections are encrypted, it is unclear how secure the encryption is. Additional details about the connection process, encryption, and data that may go through other user devices would be welcome to shed some light.
Lastly, it is unclear what is going to happen when the service exits beta. Will it become paid only? Will users still have to contribute bandwidth even if they provide other users of the service with bandwidth?
Now You: Have you tried Penguin Proxy?



















I have researched in the US for years and someone has stolen all my research! I have notified IC3.gov, filed several complaints, and cannot get the TBI to stop this madness! I am more than disappointed in every agency in TN! How do you stop people from stealing all your hard work?
Disappointed and discouraged in TN!
The settings incorporated into the software aren’t enough to be secure online.
PenguinProxy is only centralized at the moment because that is the thing that we could build the fastest and release a proof-of-concept of. We are working on a decentralized protocol that.
It’s not truly decentralized, I doubt you are ‘working’ on a ‘decentralized protocol’. Why not Blockchain, the makers of Sentinel and Mysterium have huge teams working hard to implement a true decentralized VPN solution, which currently are in early beta and even with their large teams have still ways to go. Yet you are ready to go with your solution, lol.
We are working on a decentralized protocol that.
I bet the tech illiterate eat that up huh. You sound like another VPN service making up stuff to get people to buy into your crap.
Hi Scott, I’m not sure why you took such a negative tone. Can you please elaborate on what settings you think aren’t enough to be secure and what alternative solutions exist that mitigate those issues?
I already explained in my previous response that PenguinProxy is currently centralized and that it’s a huge problem (not just for PenguinProxy, but for every other VPN provider as well). I can’t do anything to convince you that we’re actually working on our new protocol, but if you send us an email at [email protected] I’d be happy to update you when it’s ready.
We’re also rooting for the folks at Mysterium. What they’re doing is both technically feasible and impressive. However, we are of the opinion that being based on Ethereum is a weakness because of how hard it is to onboard a user. A large number of users is critical for such a service to succeed, so we don’t think a successful solution can be based on Ethereum or anything else that is very difficult to install or operate.
Really not fond of the idea that my IP can be misused by others.
The concept of it is great, don’t get me wrong. But there are just far too many people out there that will use this for malicious purposes, and without proper checks in place, then it’s too much of a risk.
Hi Martin, John from PenguinProxy here. I really appreciate you writing this article, just wanted to address some of the concerns raised.
We plan to charge a small yearly fee for extra features to cover development costs, but this fee should be an order of magnitude cheaper than the centralized VPN providers since we don’t have to cover the cost of servers (around $5/year). Our goal is to enable anybody in the world to have free, uncensored access to information, even if you live in a poor country. So PenguinProxy will always have a limited free tier available. The $15 lifetime deals you mention are somewhat deceptive. The way these companies work is they sell a bunch of lifetime deals and then shutter the company, leaving you with no recourse, and certainly no “lifetime” VPN access.
At the moment, connections to your peer go through PenguinProxy’s server and are encrypted by SSL (2048-bit key). Almost every VPN service is centralized in this way, and it’s a huge problem (TOR is the notable exception, but it’s very slow). Any such VPN provider can log, share, transfer, or sell data about your connections despite any claims that they make on their website. There’s nothing actually stopping them from doing it, and it’s very profitable to do so, so it’s a huge security and privacy hole in the traditional VPN model.
PenguinProxy is only centralized at the moment because that is the thing that we could build the fastest and release a proof-of-concept of. We are working on a decentralized protocol that:
a) Allows you to use multi-hop connections so that your peer provably doesn’t know who you are without owning a large part of the network.
b) Enables you to prove that no data is sent to PenguinProxy servers, so it would be impossible for us to log or sell any data about your connections, no matter how tempting the profit from doing so would be.
This protocol will use AES 256-bit encryption, and will make PenguinProxy far more secure and privacy-protecting than any centralized VPN because of the fact that you don’t even have to trust PenguinProxy.
The speed issues you encountered will be resolved as our network grows bigger and our peering algorithms improve. Right now, we do some very basic checks to see if a peer’s connection is good, and in some cases we get false positives which causes you to match up with a slow peer. You should expect PenguinProxy to match or exceed the speed of centralized VPNs over time.
We will be adding more countries to choose once we have enough users to provide stable connections in each country.
I hope that addresses your concerns. We really believe that it’s possible to give provably secure, uncensored, free or very-low-cost access to information to everybody in the world. I’d be happy to answer any other questions you might have.
You still don’t address the issue of somebody using my IP to commit a crime, nobody likes to have their home raided by cops at 6am regardless of if they charge you with something afterwards or not.
I don’t use free products for a long time, I wouldn’t trust security products which are free, you don’t know what is implemented, because to hold such an infrastructure you have to have some kind of income. I am a user of nordvpn for already a long time, and I wouldn’t recommend anything else, cause it is cheap and you can loose more using something free and unknown.
Hi Danie, we have the opinion that both free and paid VPN services are susceptible to poor security and the temptation to sell user data. It’s not so much free vs paid as much as centralized vs decentralized. If you’re using a centralized VPN, there’s nothing to stop the VPN provider from logging or selling all your data. And if there is a security breach in a centralized service, all the data going through them is instantly centralized. By making a VPN service decentralized, it makes it impossible for the VPN operator to log or sell your data, since your data doesn’t even go through them. PenguinProxy is working on a protocol that makes it possible to prove that we cannot log any of your data.
why does it need ffmpeg.dll? to take screenshots or stream the window? …
The UI of PenguinProxy is built with Electron, which has a dependency on ffmpeg. PenguinProxy does not take screenshots or stream any video of any part of your screen.
Psiphon 3 provides a modicum of privacy. Use SSH and country of choice.
Setting up a SSH server on AWS free tier takes about an hour and PuTTy.
Hoxx and Touch? I don’t know. Nord came out with a browser add-on.
Cocoon or Epic Browsers.
Opera should suffice for most needs.
So Penguin–it still shares one’s IP, from what I gather; the problem is my IP should never be shared, especially by some random computer in cyberspace. P2P proxies–super questionable.
@TeIV–Nice share. I found changing the DNS from Google to some other DNS can cause a super slow down.
How about UltraSurf! [Just kidding.]
@Klaas Vaak:
HOXX VPN/Proxy is horrible — check the online reviews
HOXX boldly states that they log everything you do… and save it forever, share it with anyone, at their discretion
HOXX has many servers, but they are plagued with IP Leaks
Why use a VPN at all if one is unconcerned with privacy?
@Foster what does ‘plagued with IP leaks” mean?
I didn’t know they were planning to charge. Up until this point I was on board with what they were doing, but now I don’t care.
Hi Weilan, the article didn’t make this clear. We plan to charge a small yearly fee for extra features. The fee will be significantly smaller than a typical VPN since we only have to cover the cost of development, and we don’t have any servers to pay for. On the order of $5/year. Our goal is to allow anybody in the world (including in poor countries) to have free access to information, so there will always be a limited free tier.
So…like Hola? Gonna be fun if someone does illegal things with your ip and then you get a swat team into living room.
@Harro Glööckler:
So long as you keep milk and cookies on hand for the SWAT team, I’m sure they’ll listen to your side of the story. Although come to think of it, that didn’t work for the folks who ran a Tor node in Seattle, when they were raided by Seattle police…
Im Very interested in everything mentioned here.
Ive been considering a VPN.
Would be nice to fiddle with some free stuff til I can understand whats going on.
Also interested in switching to FIOS to save some cash & try out freenet &/or I2P.
FIOS would allow me the speed to really help out with my bandwidth.
@supergirl,
Some additional info for you with regard to Tunsafe’s Wireguard servers if you want to experiment with freebee VPNs: https://forum.tunsafe.com/viewtopic.php?id=21
Anyone want to sign up to host a Tor exit node?
No?
It’s fine to help a developer with nascent software but not if it involves allowing users trying to hide their activity to pass through your machine.
No, I won’t try Penguin Proxy, Walrus Wall, Skua Screen or anything else like this.
I’m currently connected to a Tunsafe’s Wireguard VPN server. They have five locations all free and with unlimited usage and no logs. Check it out: https://tunsafe.com/about
I’ve coupled that with Quad9.net’s free DNS servers for additional security (both IPv4 and IPv6): https://www.quad9.net/microsoft/
So no, the Penguin Proxy doesn’t appeal to me at all I’m afraid.
Cancel the Quad9 part of my post please. I just read their privacy policy which states (among other things):
“When you use Quad9 DNS Services, here is the full list of items that are included in our logs:
* Request domain name, e.g. example.net
* Record type of requested domain, e.g. A, AAAA, NS, MX, TXT, etc.
* Transport protocol on which the request arrived, i.e. TCP, UDP, and encryption status of the protocol
* Origin IP general geolocation information: i.e. geocode, region ID, city ID, and metro code
* Protocol version IP address – IPv4, or IPv6
* Response code sent, e.g. SUCCESS, SERVFAIL, NXDOMAIN, etc.
* Absolute arrival time
* Name of the Quad9-operated machine that processed this request
* Quad9 target IP to which this request was addressed (no relation to the user’s IP address)”
Yet they say elsewhere that they don’t keep logs…..
Quad9 is basically run by police. It was never a good choice. If you need a fast and okish dns stick to 1.1.1.1 by cloudfare. Yes they are still a US corporation and thus not very trustable but at least it’s not a police and their offer ia not filtered internet as what quad9 does.
Better choice is peobably a service like the dns offered by Chaos Computer Club or similar organisation. Not as fast but a lot more reliable.
@AxMi-24,
I’ve gone back to using my VPN’s DNS even though it’s a bit on the slow side: https://www.azirevpn.com/docs/servers
I tried Cloudflare, but it seems even slower maybe because I’m not located in the US.
grc.com has a DNS Benchmark tool but it’s focused on the US so doesn’t help much. I’ll have a look on the CCC site though. Thanks for the tip.
@Ax-Mi 24:
I’ve read that DNS.Watch is even more “private” than Cloudflare. DNS.Watch supposedly doesn’t keep any logs at all. I mean, I’m sure they have to keep *some* logs for a while, for diagnostic purposes, but they *claim* not to keep any.
Cloudflare supposedly dumps all logs after 24 hours … *after* sharing all DNS query data — ostensibly without originating IP addresses — with APNIC Labs, and who knows how long *APNIC Labs* keeps it or what they do with it.
Quad9 keeps *extensive* logs. It supposedly don’t keep records of originating IP addresses, but the other data kept is so extensive (geolocation, type of originating machine, time of day, and more) that it would facilitate individual identification *considerably*.
Unlike Quad9 and Google DNS, neither DNS.Watch nor Cloudflare blacklists “malicious” sites. (Put another way, both are neutral and uncensored.)
Cloudflare is supposedly the speed champion, followed closely by Quad9.
OpenDNS supposedly keeps logs for a year by default, although you can apparently configure to a degree what kind of information it keeps on you. When I used OpenDNS a while back, the servers changed a couple of times, meaning I had to temporarily use either my ISP’s DNS servers or Google’s (which are easy to remember) in order to search for OpenDNS’s *new* IP addresses. I got tired of that and stopped using it.
Off-Topic Remark # 1: I’m going to have to figure out whether I can bypass my (effing) Netgear router and install DNScrypt on my computer. From what I’ve read, DNScrypt can be installed only on routers running OpenWrt or Tomato. I’ve been eyeing an inexpensive MikroTik router for the high Ethernet throughput. (I have gigabit d/l service and the “gigabit-capable” Netgear is cutting the modem’s d/l speed in half.) Users have been clamoring for MikroTik to support DNScrypt, and more recently DNS over TLS, in its RouterOS for *three years*, but … bupkis!
Off-Topic Remark # 2: I’m just going to go ahead and assume that any DNS service located in the UK is hosted directly at GCHQ, to cut out the middleman. Similarly, I’m going to assume that any DNS service located in the US is going to cough up whatever the NSA, CIA, FBI, or any other alphabet agency asks for, probable cause or not, warrant or not.
So if someone does dodgy things with my IP, i get in trouble. This service won’t have much success.
“..the company behind the service plans to charge users a yearly fee for usage..”
Should they PAY the users for using their bandwidth ?
The article didn’t make that clear. We plan to charge a small yearly fee to cover development cost. The fee will be far lower than a typical VPN since it only covers development costs, and there are no servers to pay for. On the order of $5/year. And there will still be a limited free tier available.
For a free proxy with unlimited bandwidth and a much longer list of countries try Hoxx. I have not experienced any throttling nor a crash in the 6 months I have been using it. It is an extension on the Mozilla site, don’t know about Chrome.
Sounds half-assed to me. Wouldn’t waste my time. I’ll stick with my Private Internet Access VPN for $7 a month.