Fake Chrome apps highlight why automated scans are not enough
While Mozilla is still in the process of setting up add-on signing for its Firefox web browser, Google uses the system already for apps and extensions for its Chrome web browser.
Mozilla's add-on signing efforts have been criticized as ineffective recently, and the same can be said for the automated scans that Google runs to filter out malicious extensions or apps before they are listed in the official Chrome Web Store.
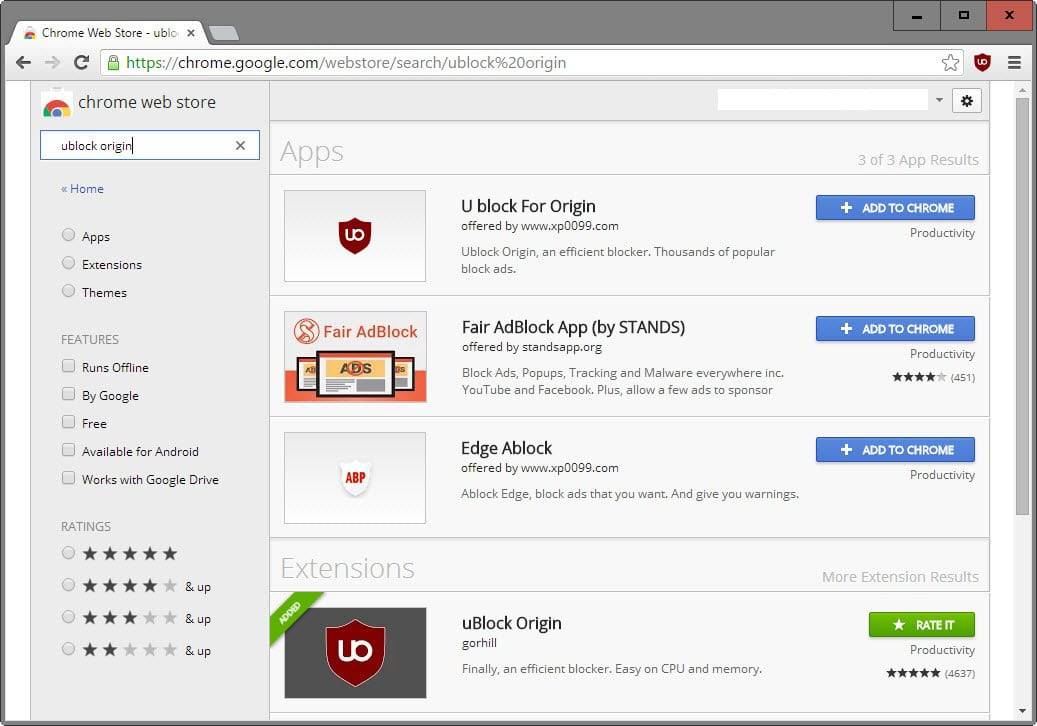
A user on Reddit noticed yesterday that the Chrome Web Store would return an app called U block for Origin as the first result for the search term ublock origin.
As you can see on the screenshot below, it is the first result returned on the search results page, and while it is clearly marked as an application, will get user clicks just because of its position in the results.
The "real" uBlock Origin application is listed as the first entry under Extensions, way below the fake entry.
The description and icons the fake apps use are taken directly from uBlock Origin as well.
Experienced computer users will spot the fake right away, but inexperienced users may not.
Further investigation revealed that the same developer has added a whole batch of fake apps to the store posing as TunnelBear, AdGuard, Browsec VPN, Easy Proxy, Hola and more.
The only purpose of the apps seems to be to lure users to a website that displays advertisement for monetization.
Each faked application has its own page on that website with a short description and a link back to the Chrome Web Store or the developer website.
It seems right now as if the sole purpose of those fake apps was to drive traffic to the website to drive up ad revenue. While that is the case, similar sites might contain attack code on top of that.
Google's automatic scan failed to realize that the apps were fake. A simple icon/description check would have resulted in a hit for instance, and while that is easy to bypass by adjusting the description and changing icons, it might prevent at least some incidents in the future.
This is not enough though to prevent this from happening again in the future and it seems likely that incidents like these will happen again unless Google changes the vetting process significantly.
Mozilla's situation is different from Google's. All extensions get reviewed manually before they are allowed in the Mozilla Add-ons Store. This is however not the case for add-ons that are submitted for signing only. While developers need to submit add-ons for signing so that Firefox Stable and Beta users can install them once add-on signing becomes mandatory, they may offer signed add-ons on third-party sites exclusively.
This means that these add-ons won't be reviewed manually by Mozilla.
Now You: What's your Chrome Store experience?










Chrome extension Chrome extension source viewer https://goo.gl/rvBFs4
If I have a doubt with a Firefox add-on I download the xpi file, unzip it (it’s a plain zip file) and start searching for external calls (search for http in the code). I also have a look at included javascripts. Not being an expert makes it tougher and longer sometimes, but it’s worth it, even if surprises may be only discovered by skilled techies as they had been found several years ago with the NoScript add-on (explained and fixed later on). No idea with Google’s Chrome apps and extensions. Are they downloadable, “unzip-able”?
For browser efficiency and safety, I’ve always felt running with as few extensions as you can tolerate is the best practice.
U Block For Origin is no longer there.
That’s good. Looks like my report went through as I and another user notice this first.